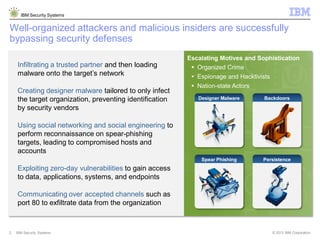
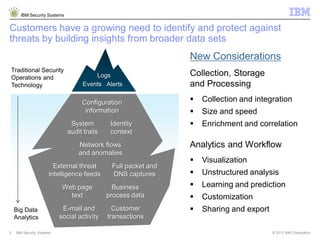
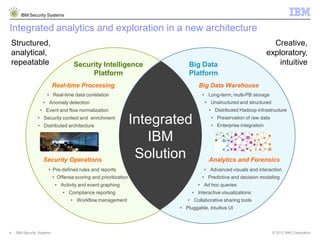
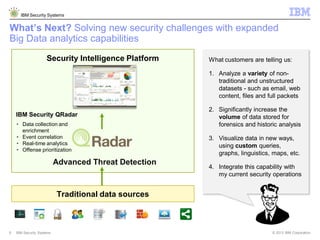
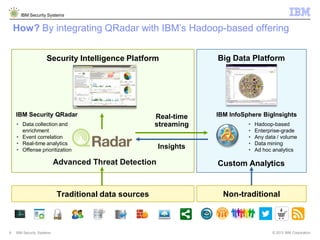
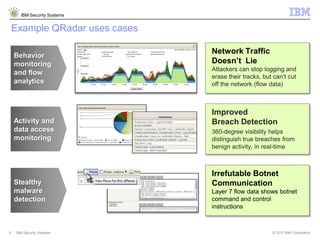
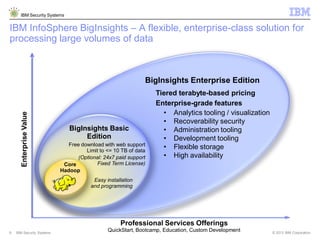
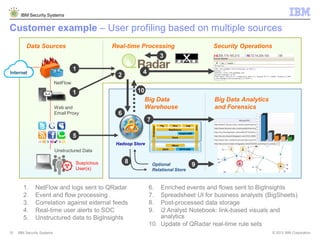
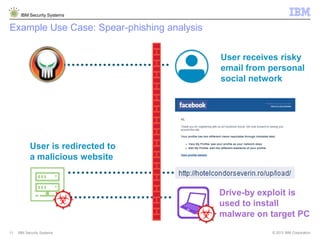
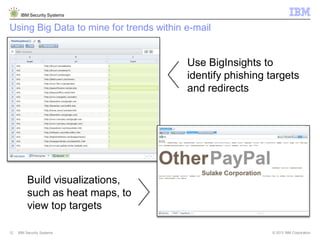
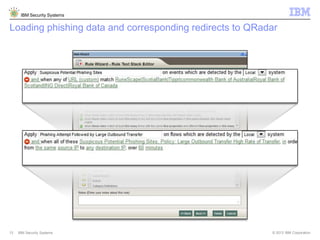
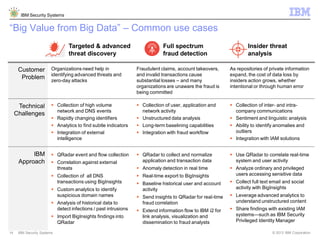
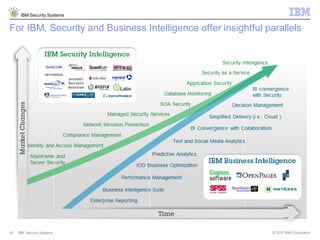
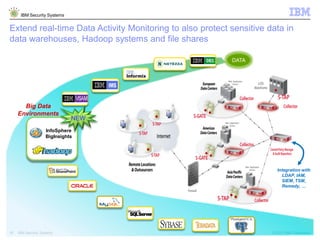
IBM's security systems highlight the importance of leveraging big data to enhance threat detection and analysis, addressing challenges posed by advanced cyber threats, including malware and zero-day attacks. By integrating various data sources, IBM's solutions aim to provide real-time insights and enable organizations to effectively monitor and protect sensitive data. Customers express a need for advanced analytics capabilities for unstructured data to improve security operations and threat response.