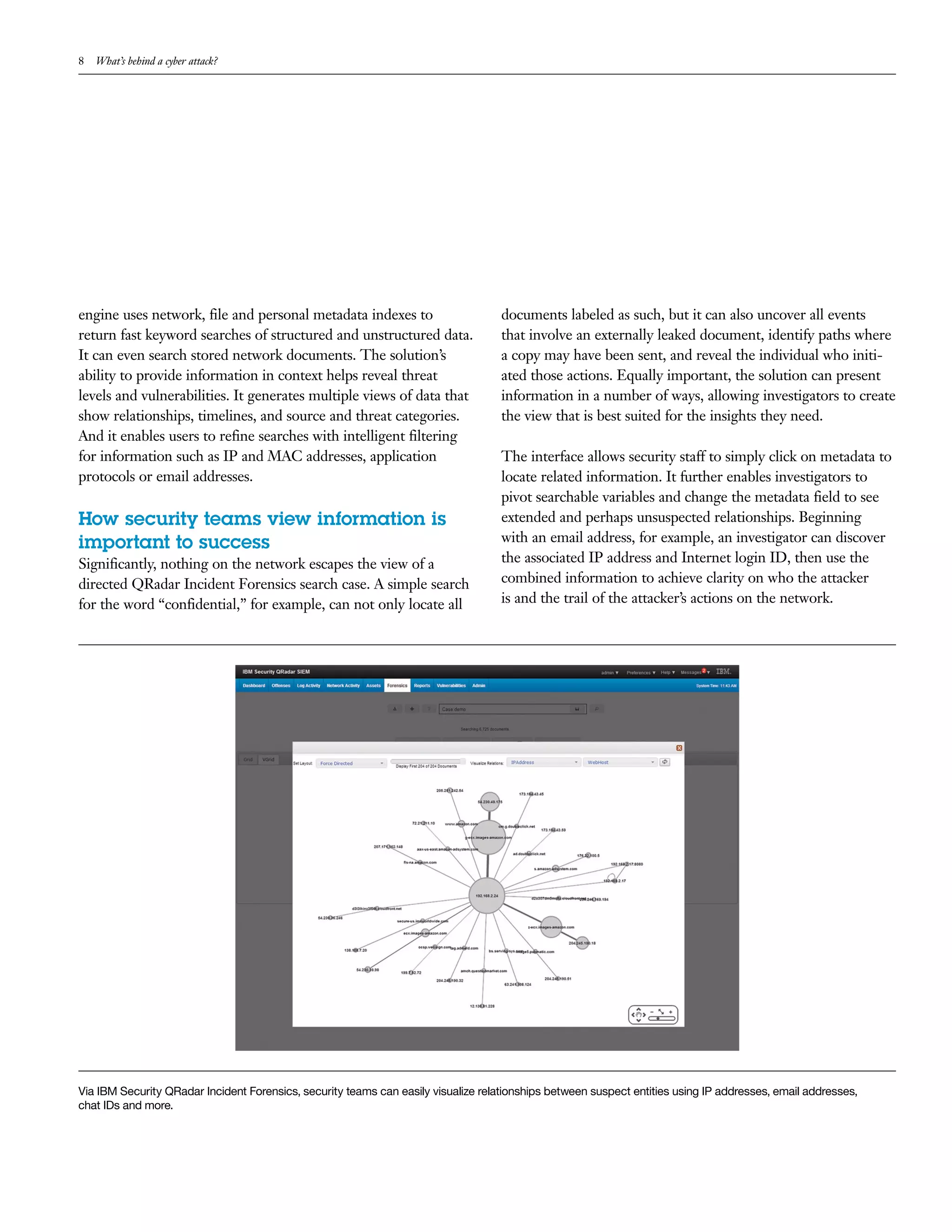
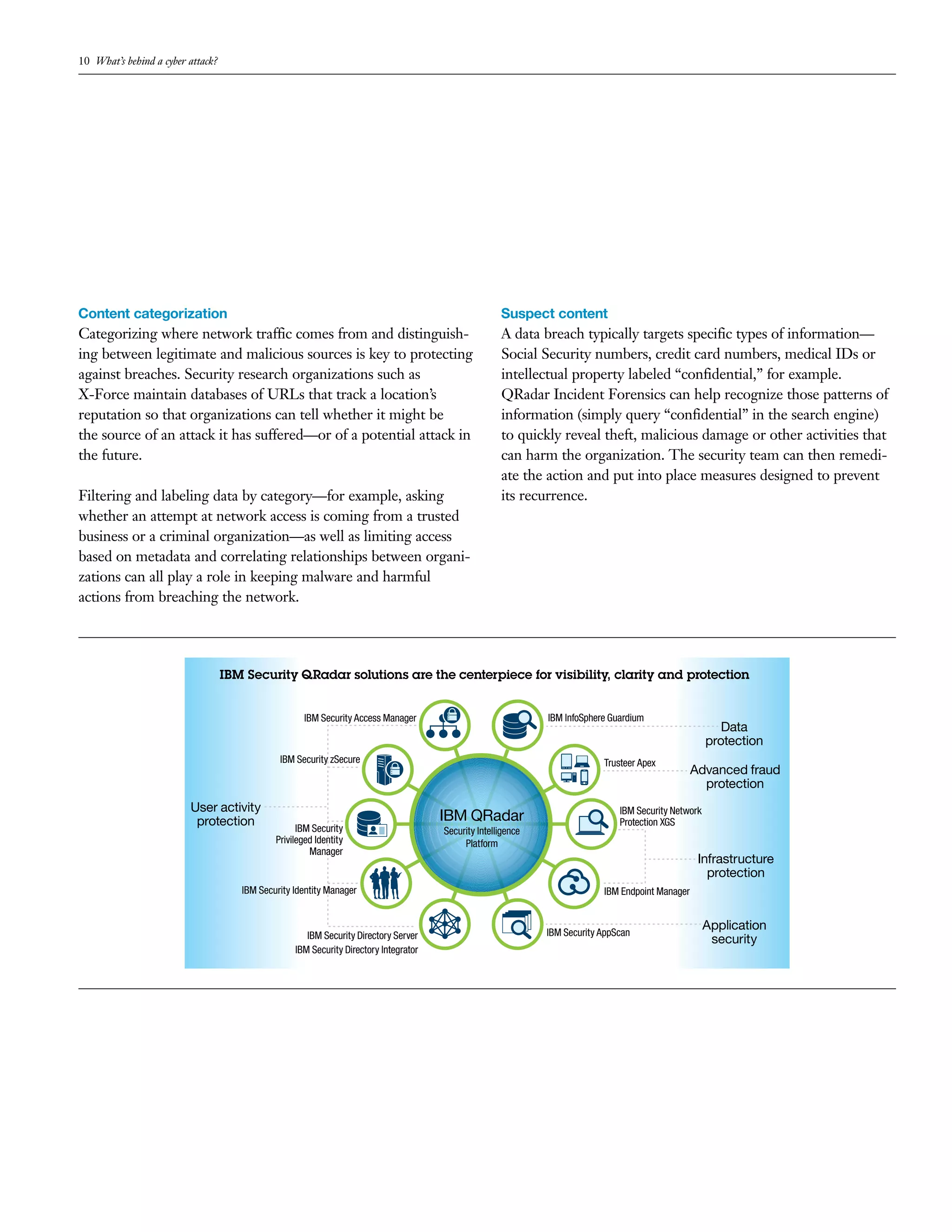
This document discusses how advanced network forensics can help security teams investigate cyber attacks more effectively. It describes how IBM's QRadar Incident Forensics solution allows organizations to (1) retrace an attacker's steps through raw packet data reconstruction, (2) speed up investigations by indexing network activity into searchable information, and (3) give security teams better visibility into security incidents through a simplified search interface.