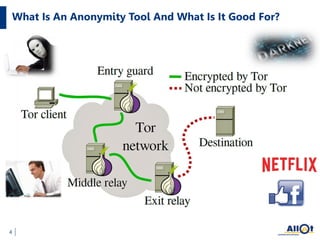
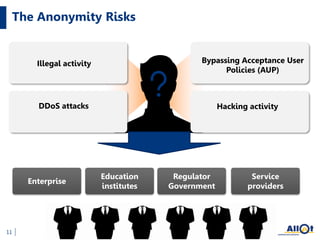
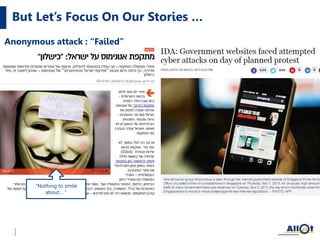
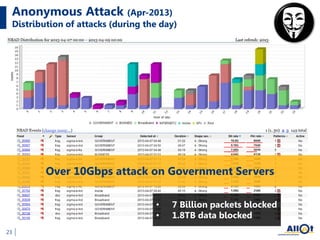
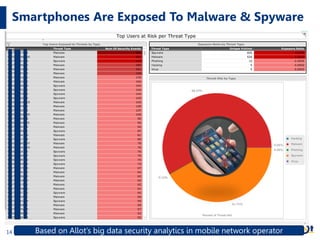
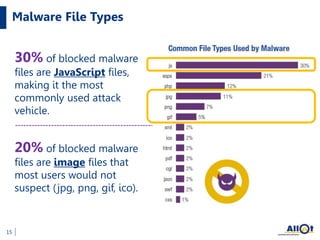
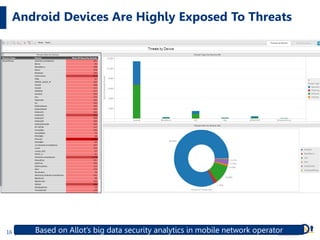
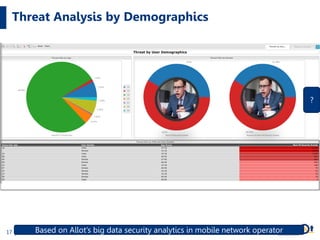
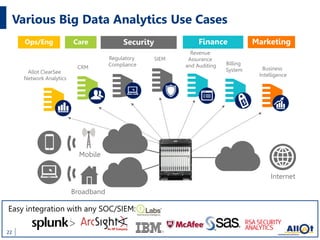
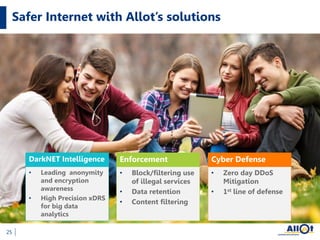
The document discusses trends and risks in network security, emphasizing the challenges posed by anonymity tools like Tor and Telegram, which are used for illegal activities and DDoS attacks. It highlights the prevalence of malware targeting mobile devices and the significance of big data analytics in enhancing security measures across various sectors. Additionally, it outlines the offerings of Allot Communications in providing security solutions and insights for a safer internet environment.