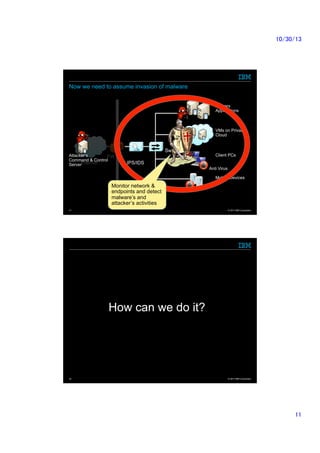
The document discusses the need for advanced security technologies in response to evolving cyber threats and the limitations of traditional defense methods. It highlights the importance of integrating security information and event management (SIEM) and analytics for enhanced threat detection and response. Additionally, it details the collaborative roles within IBM and the Information Processing Society of Japan, emphasizing their contributions to technology and security advancements.