Embed presentation
Download as PDF, PPTX
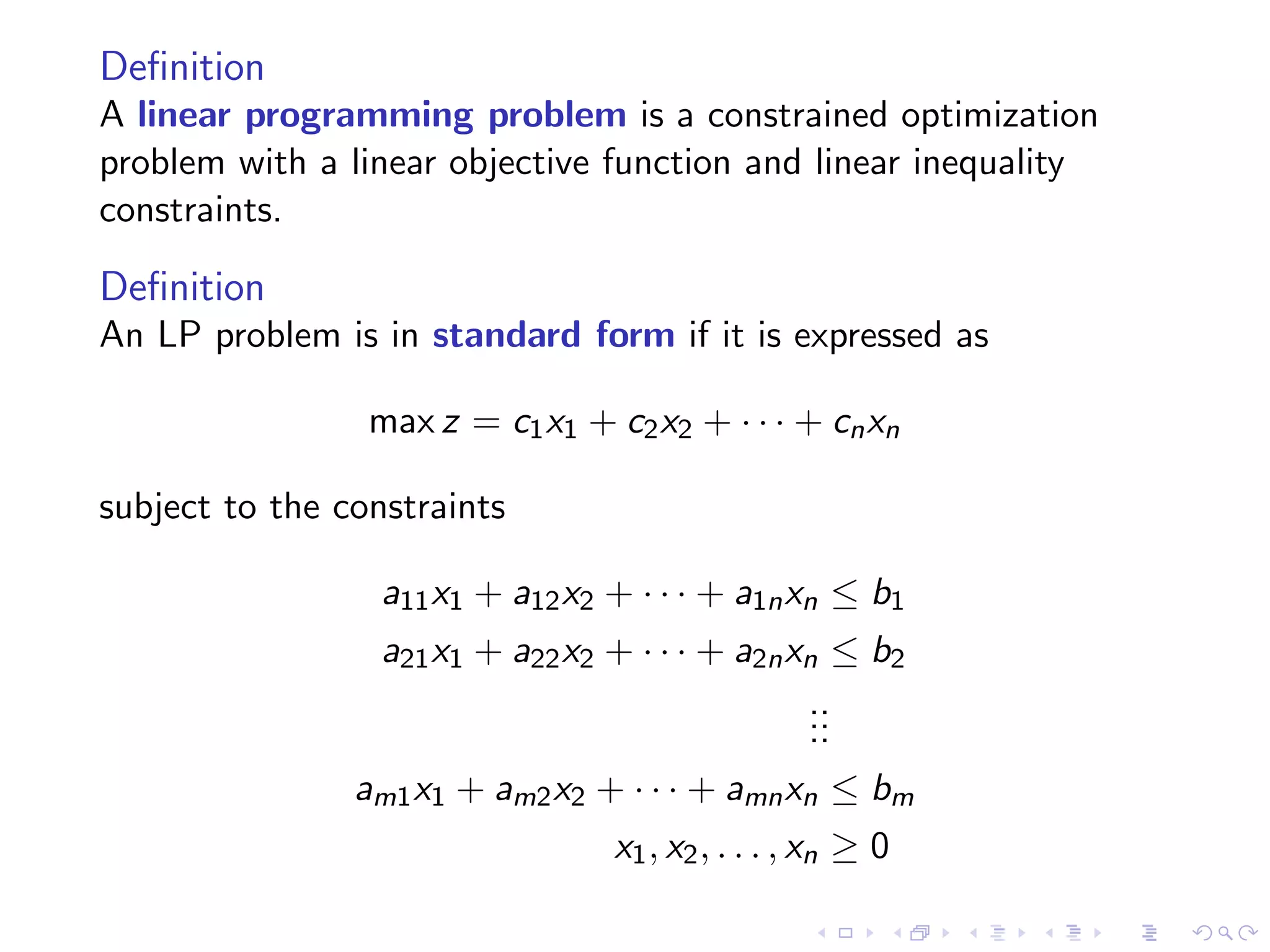
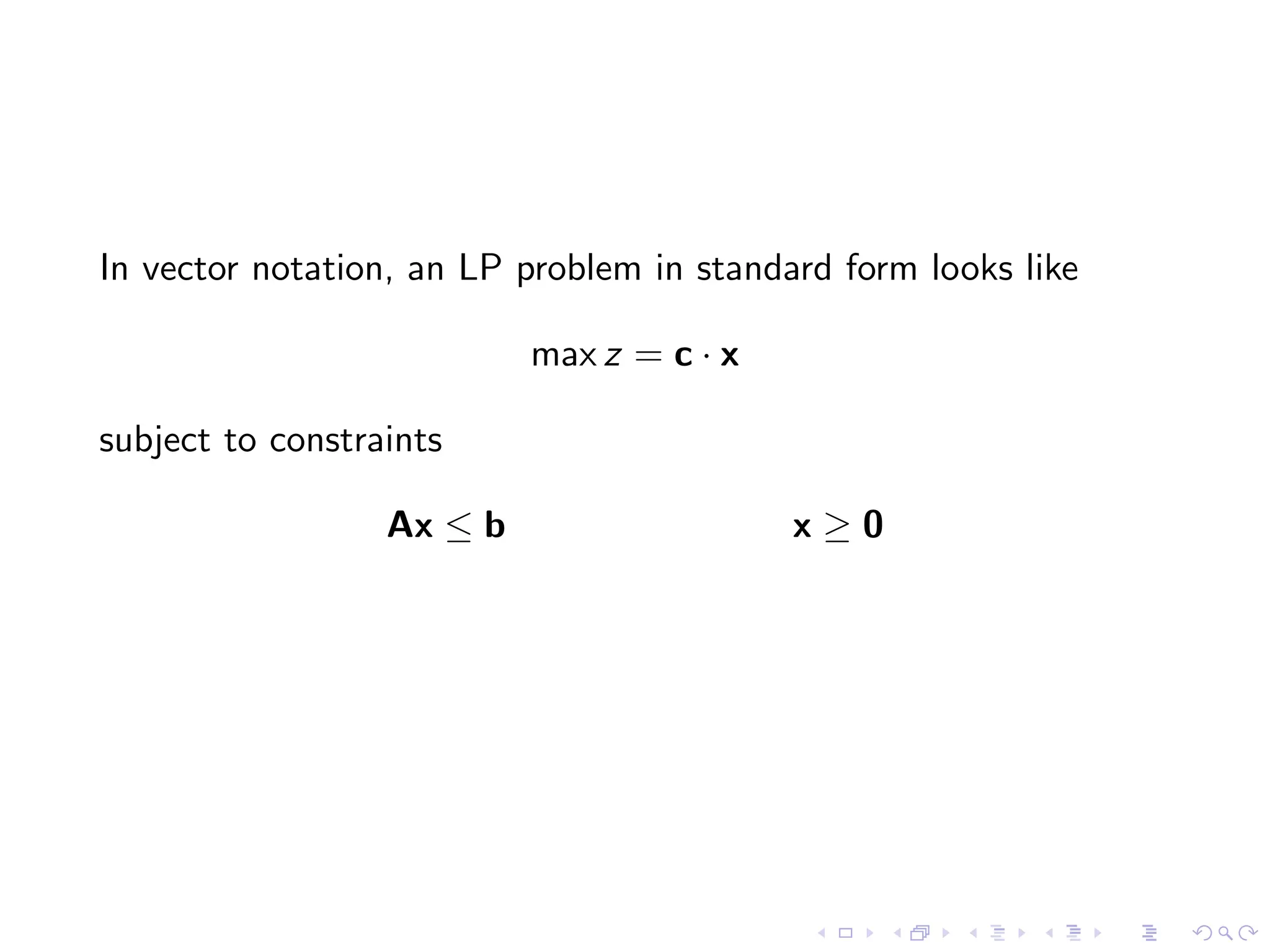
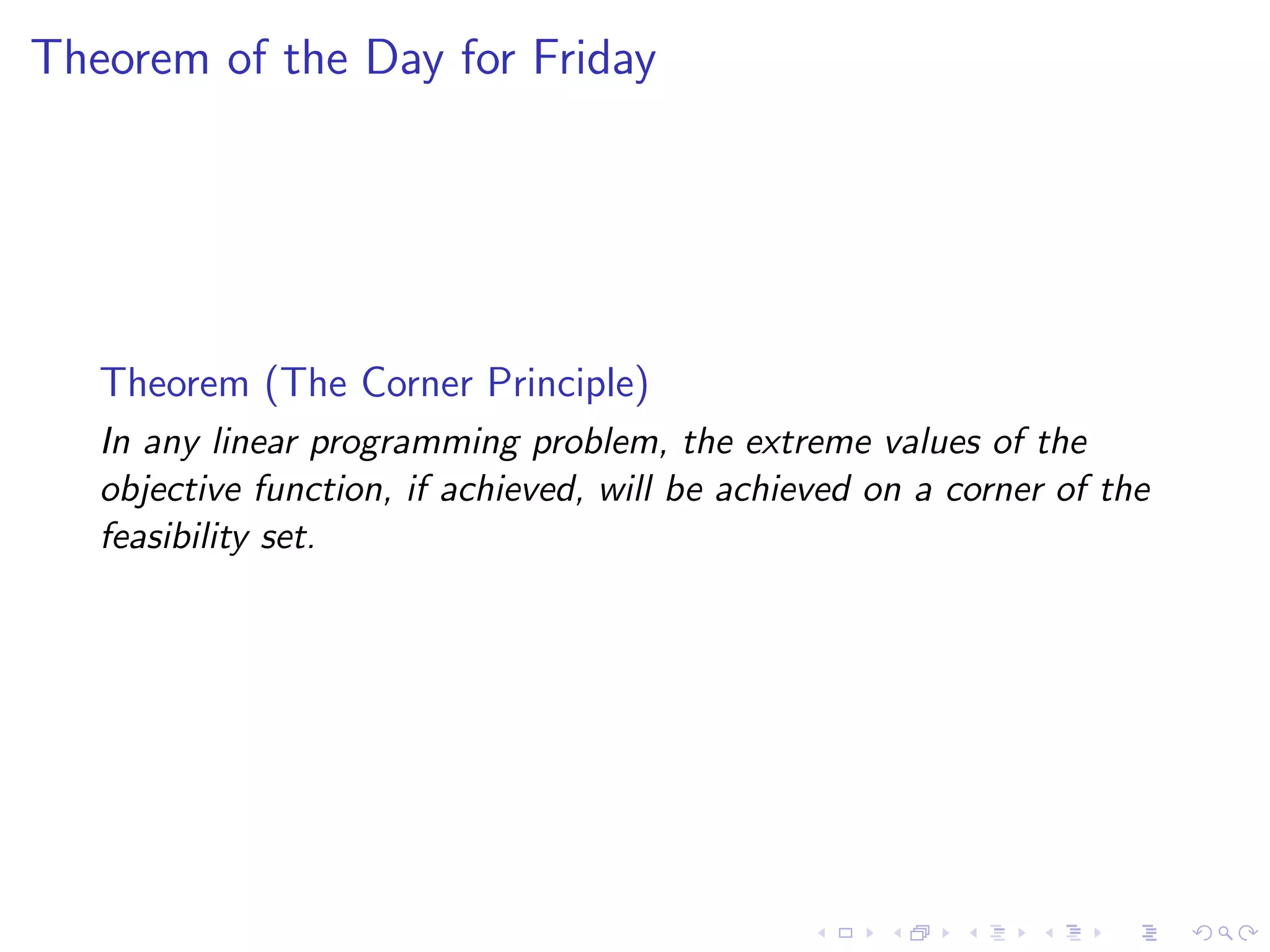
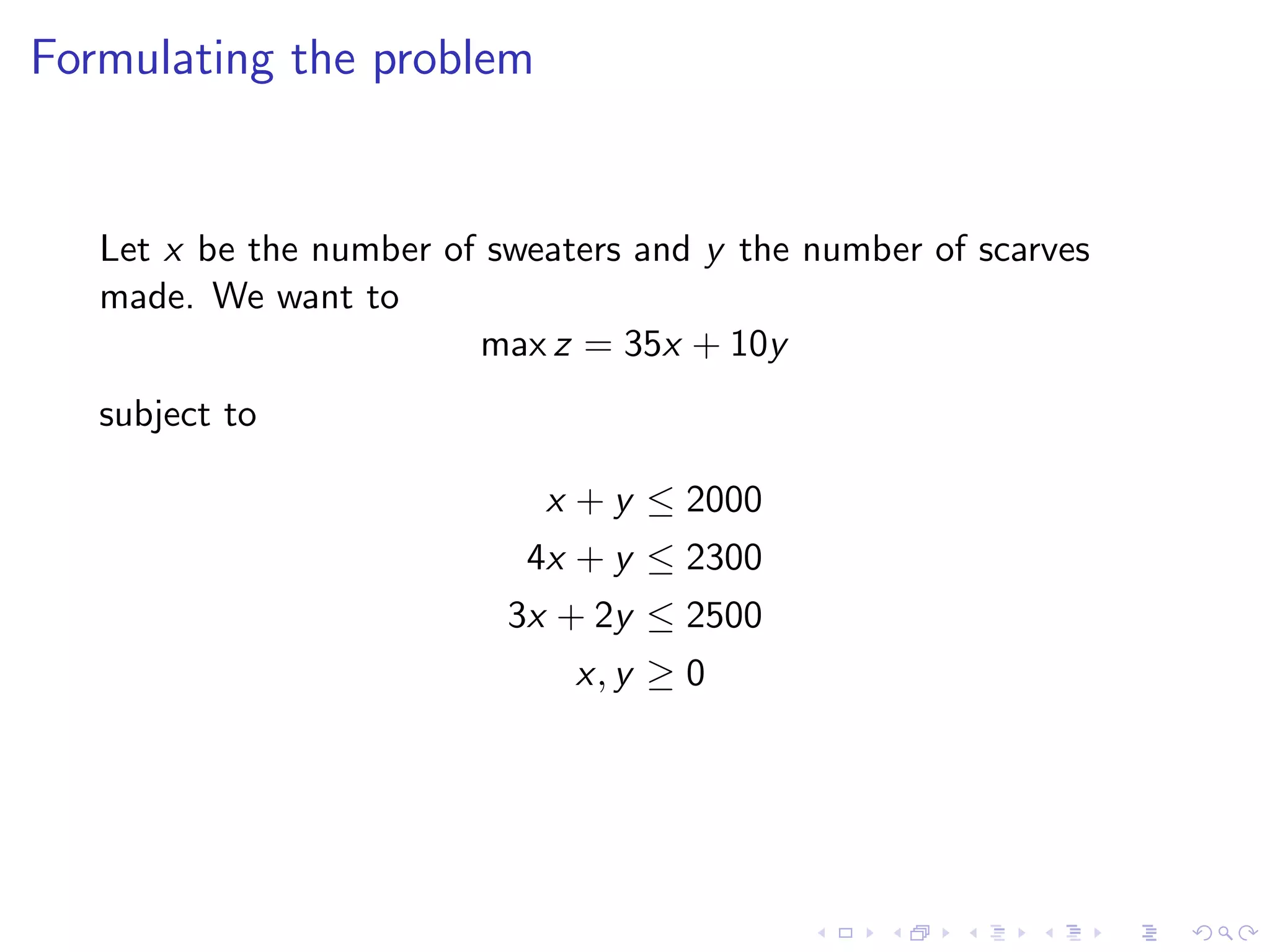
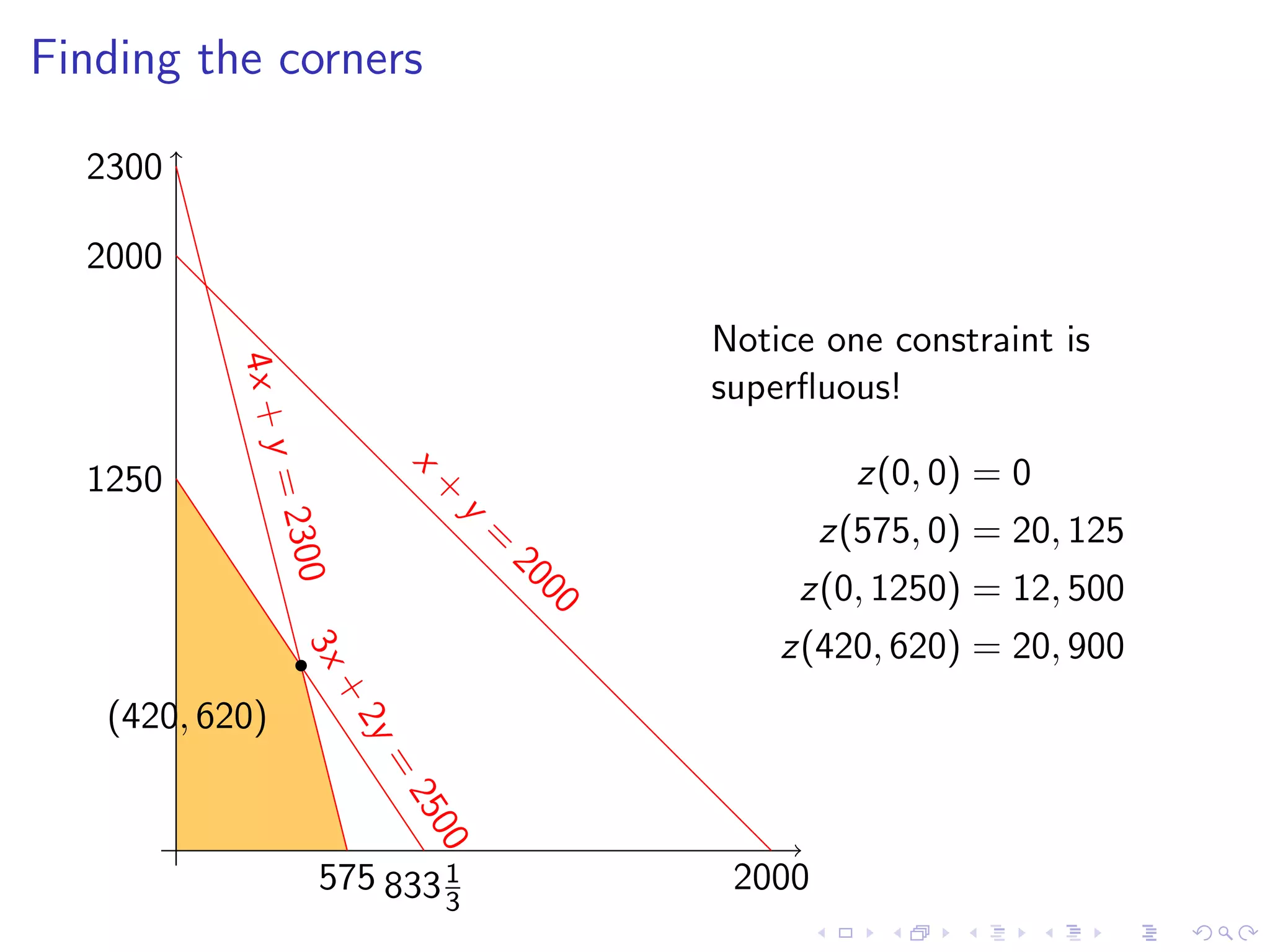
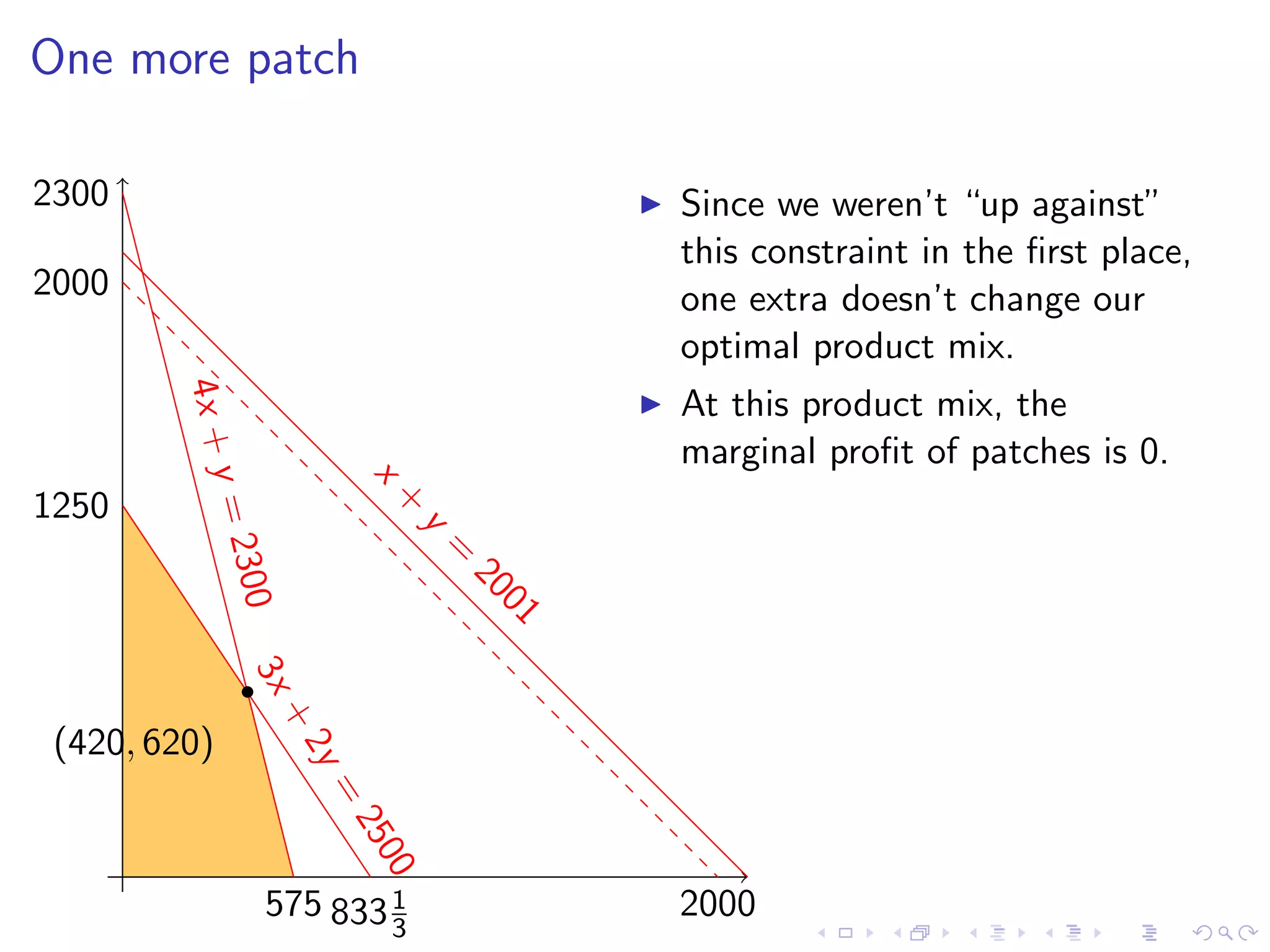
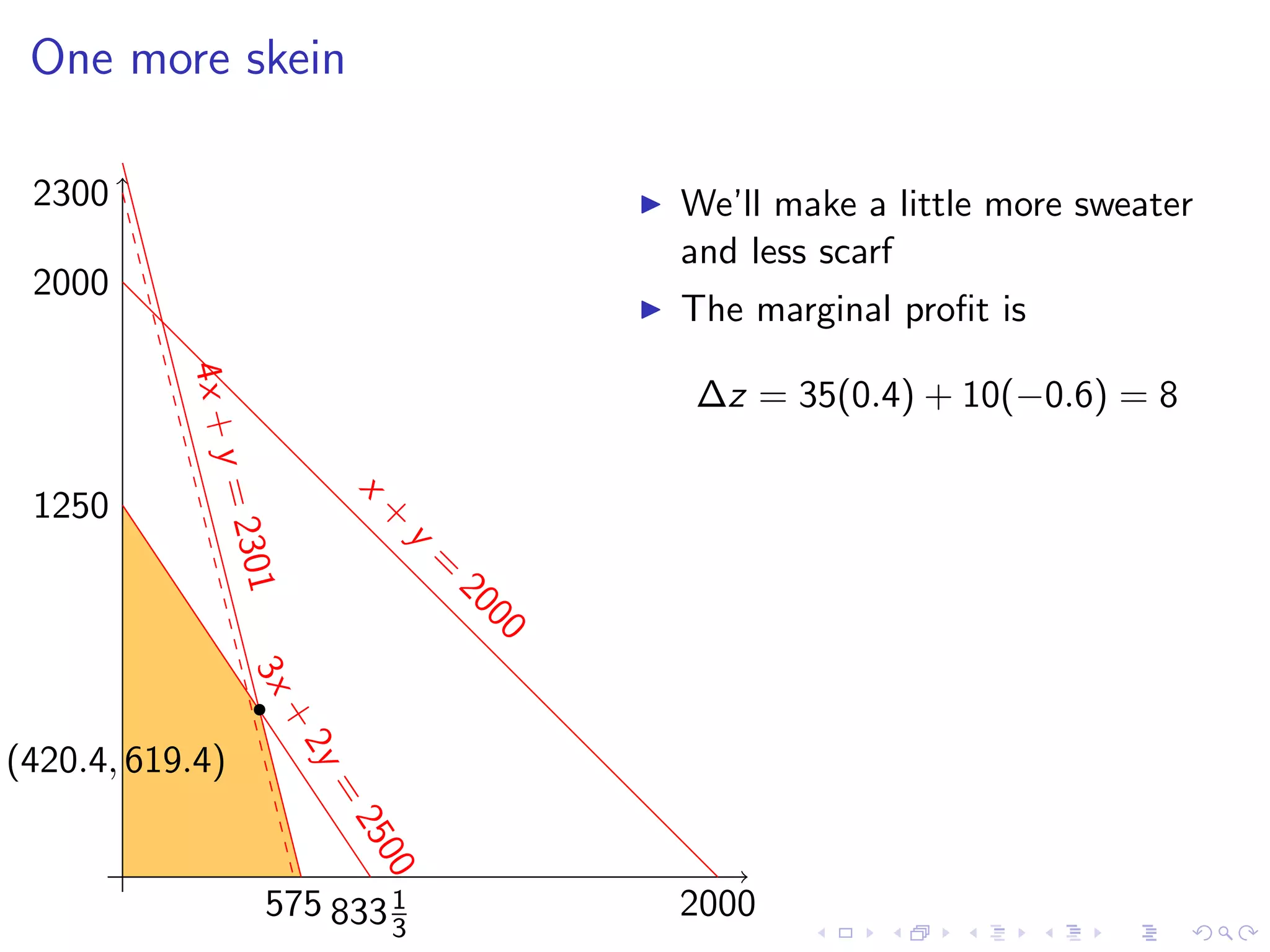
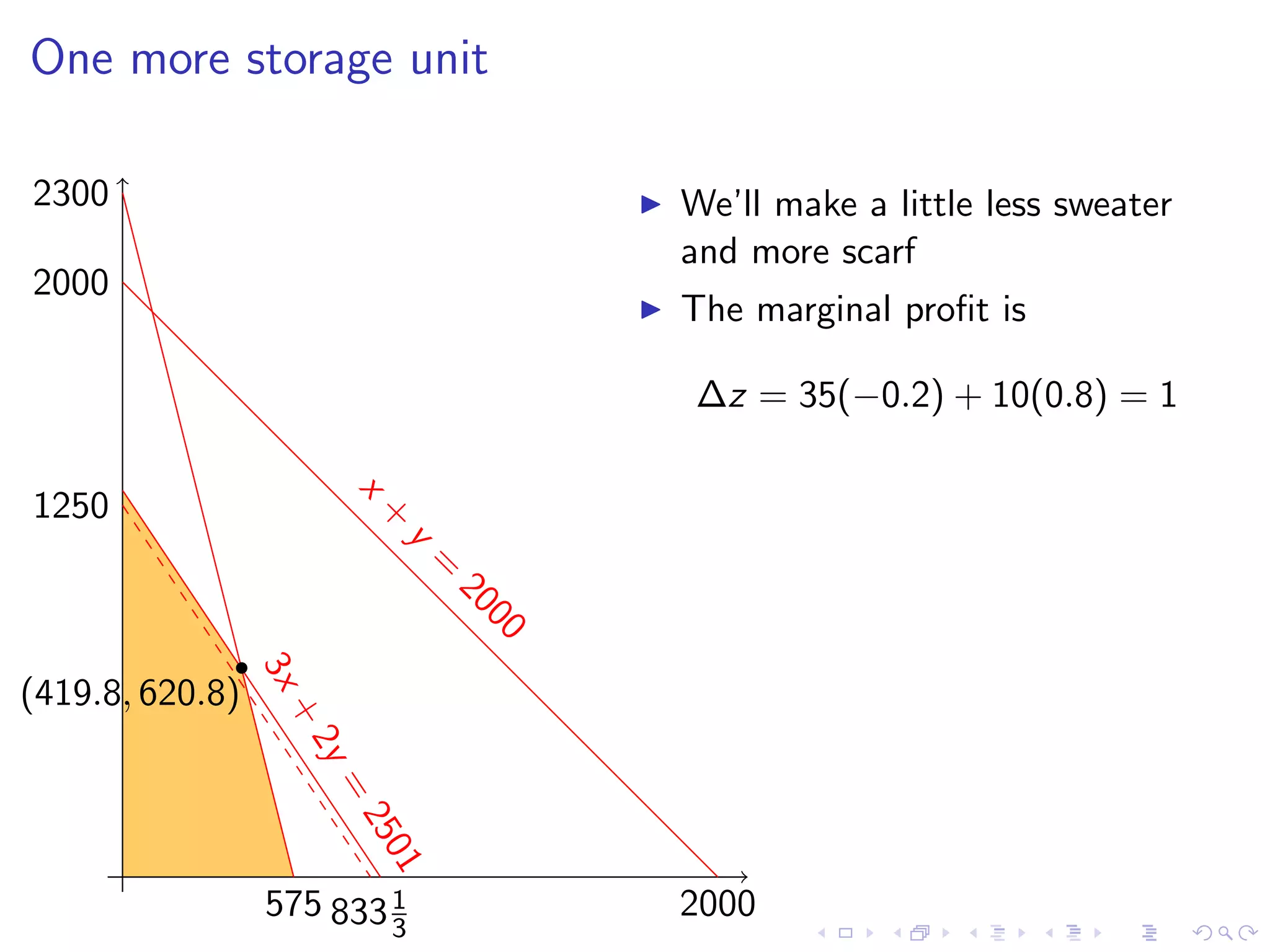
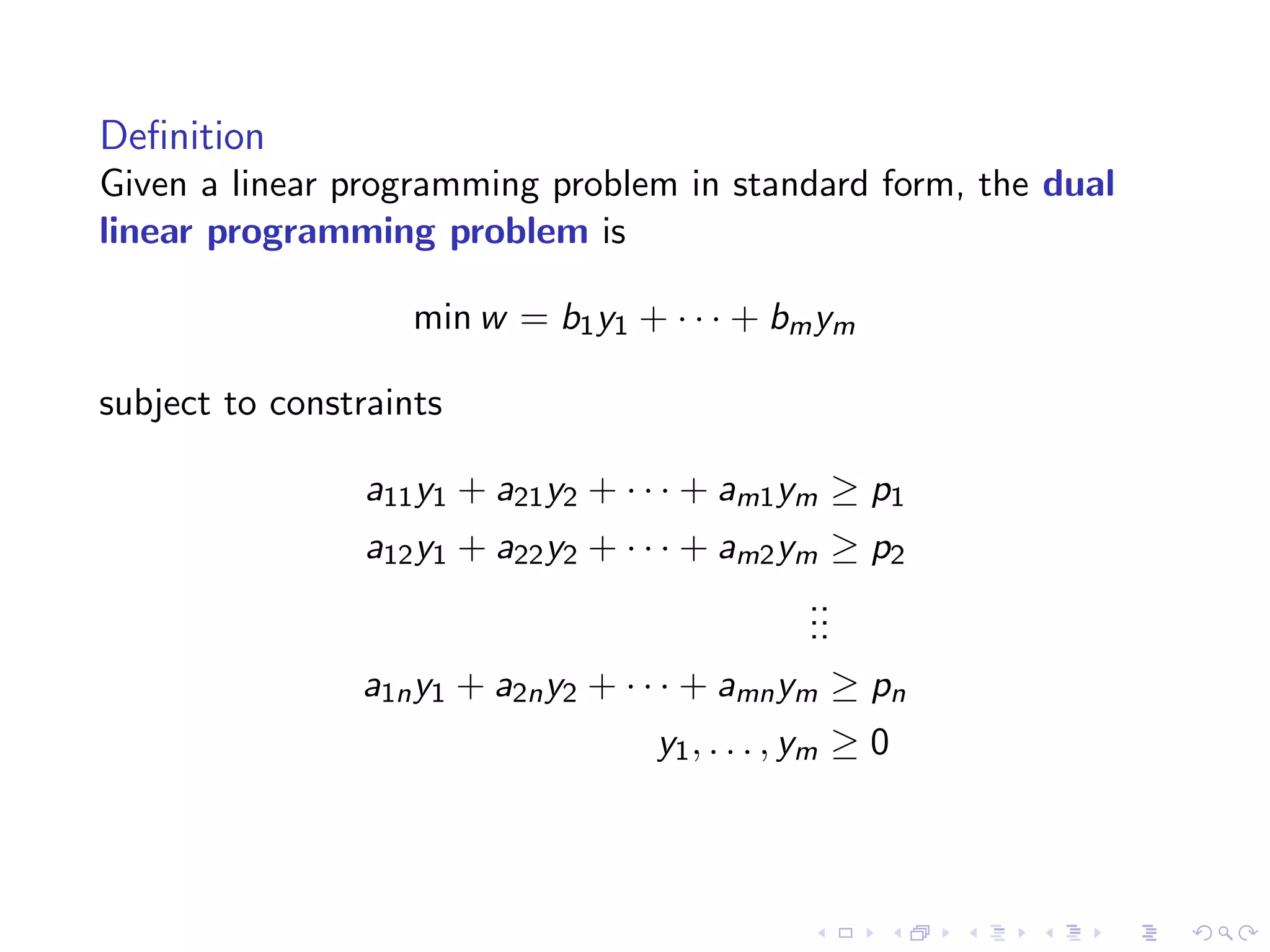
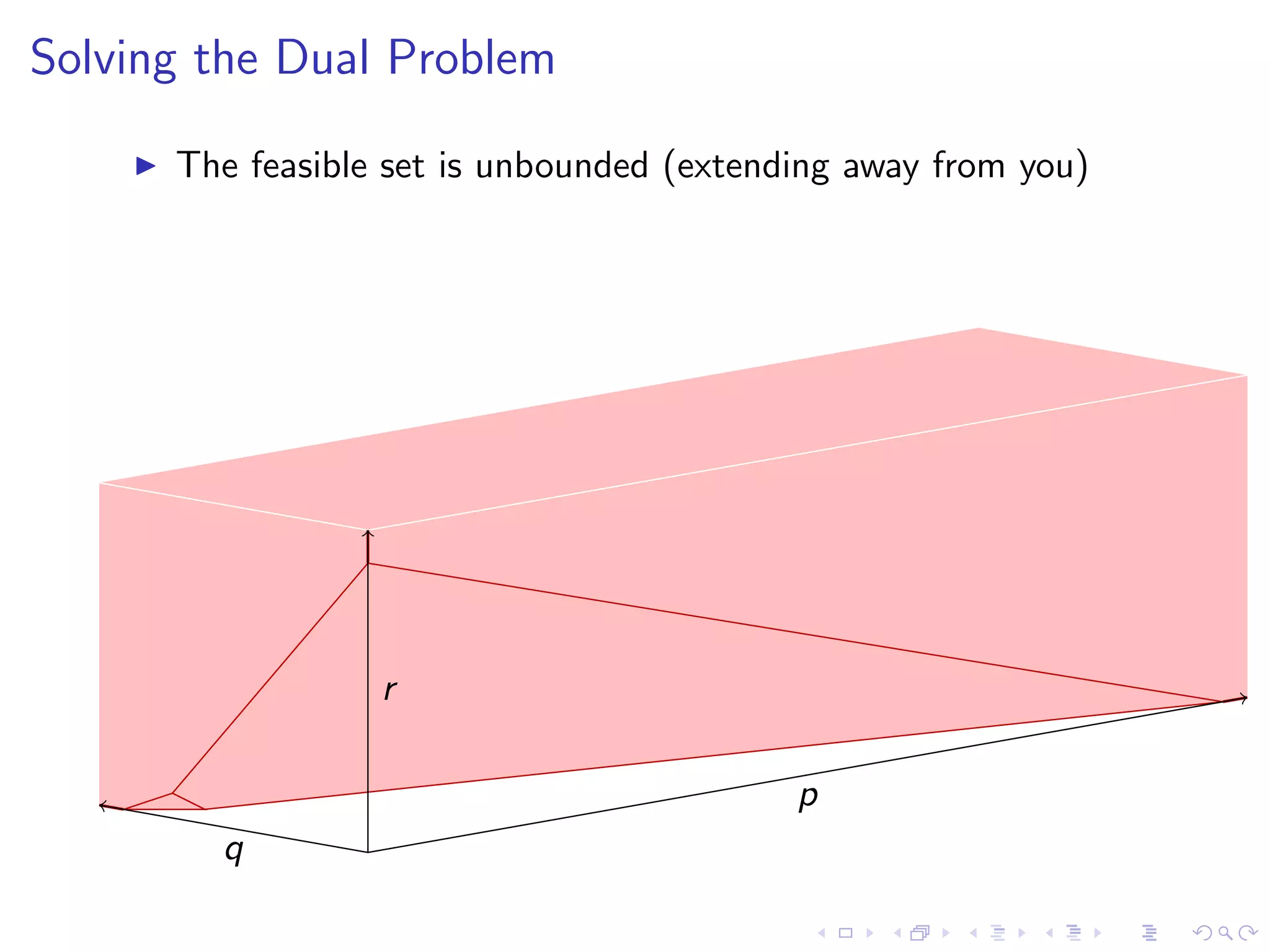
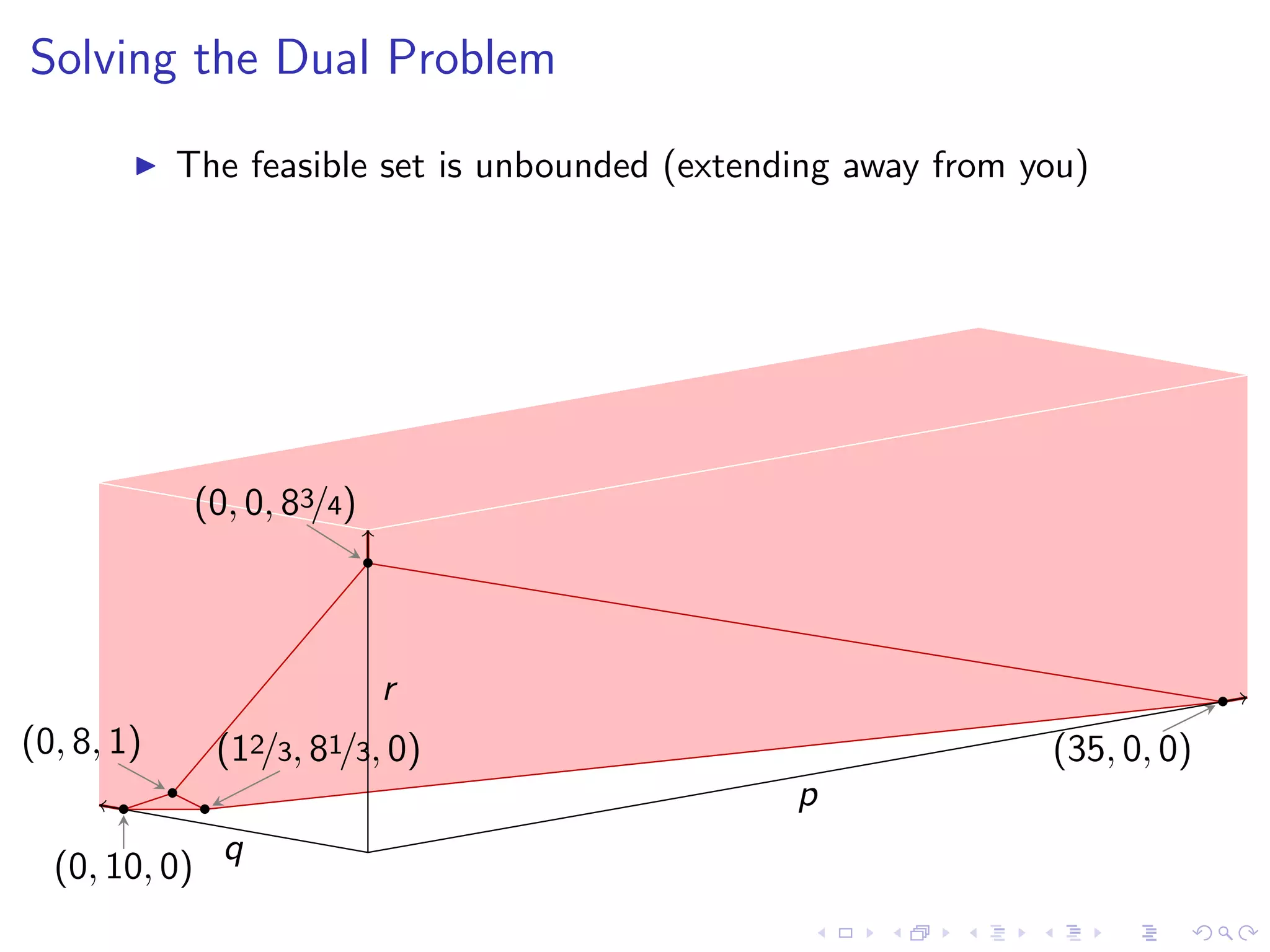
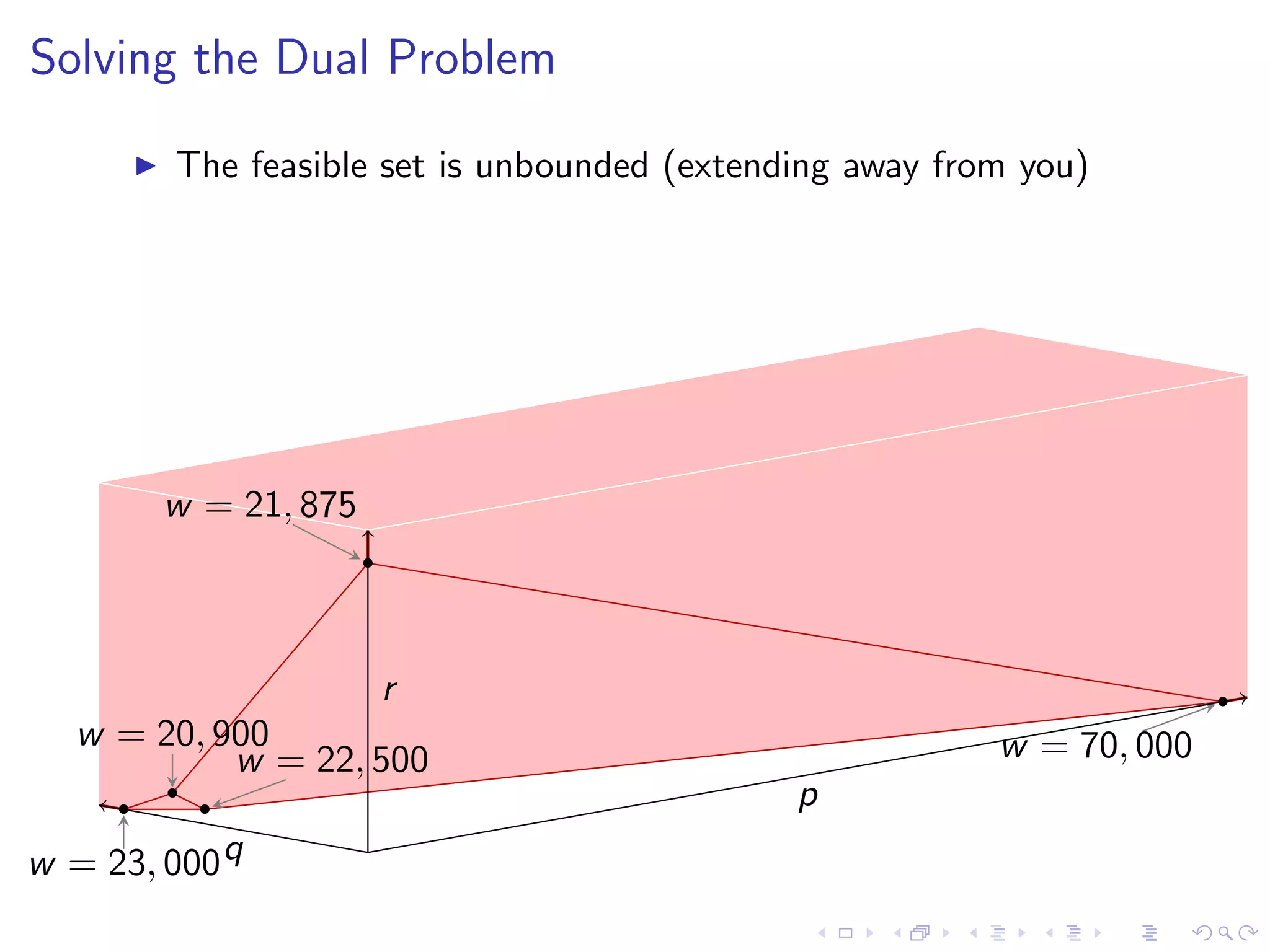
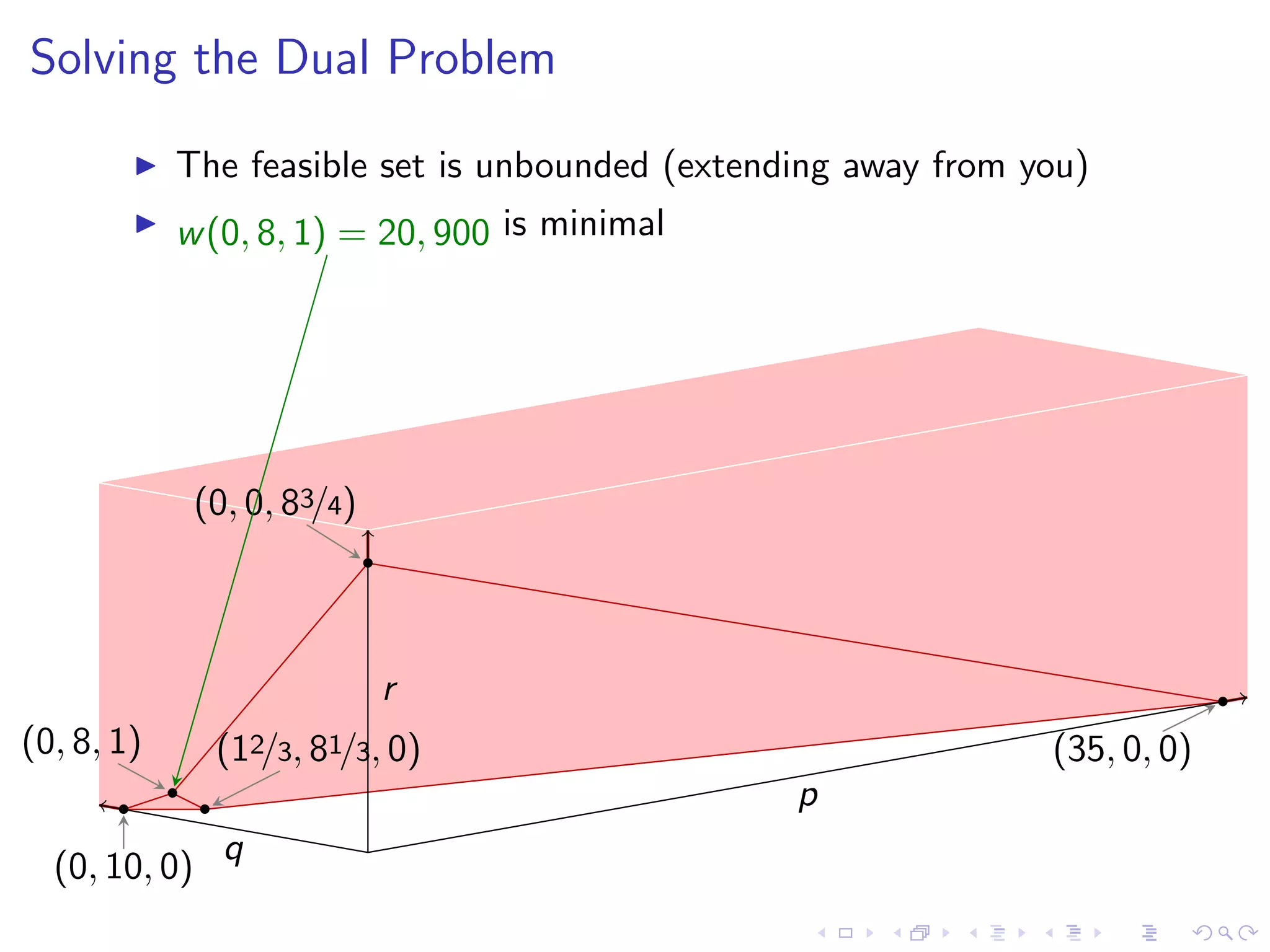

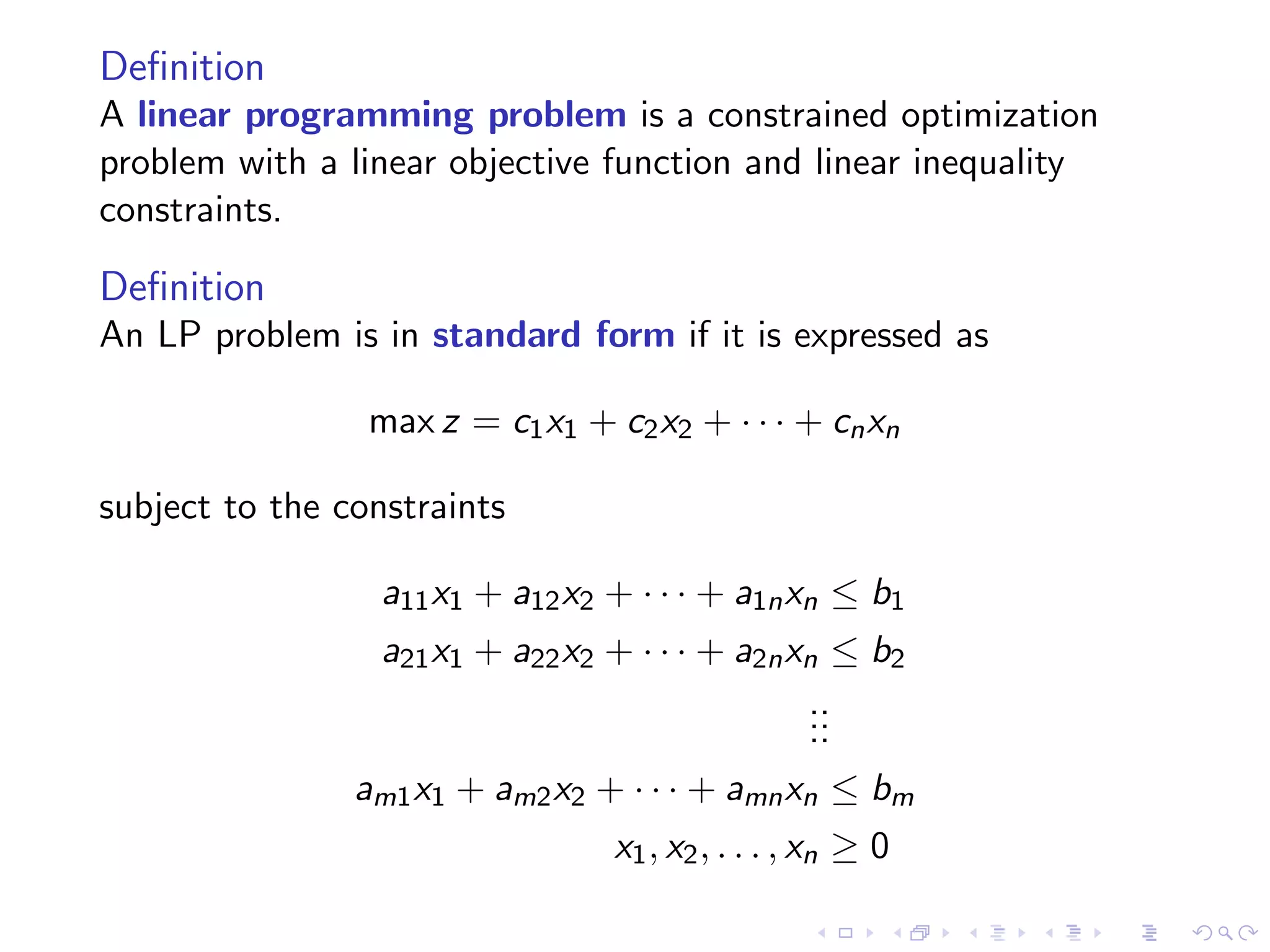
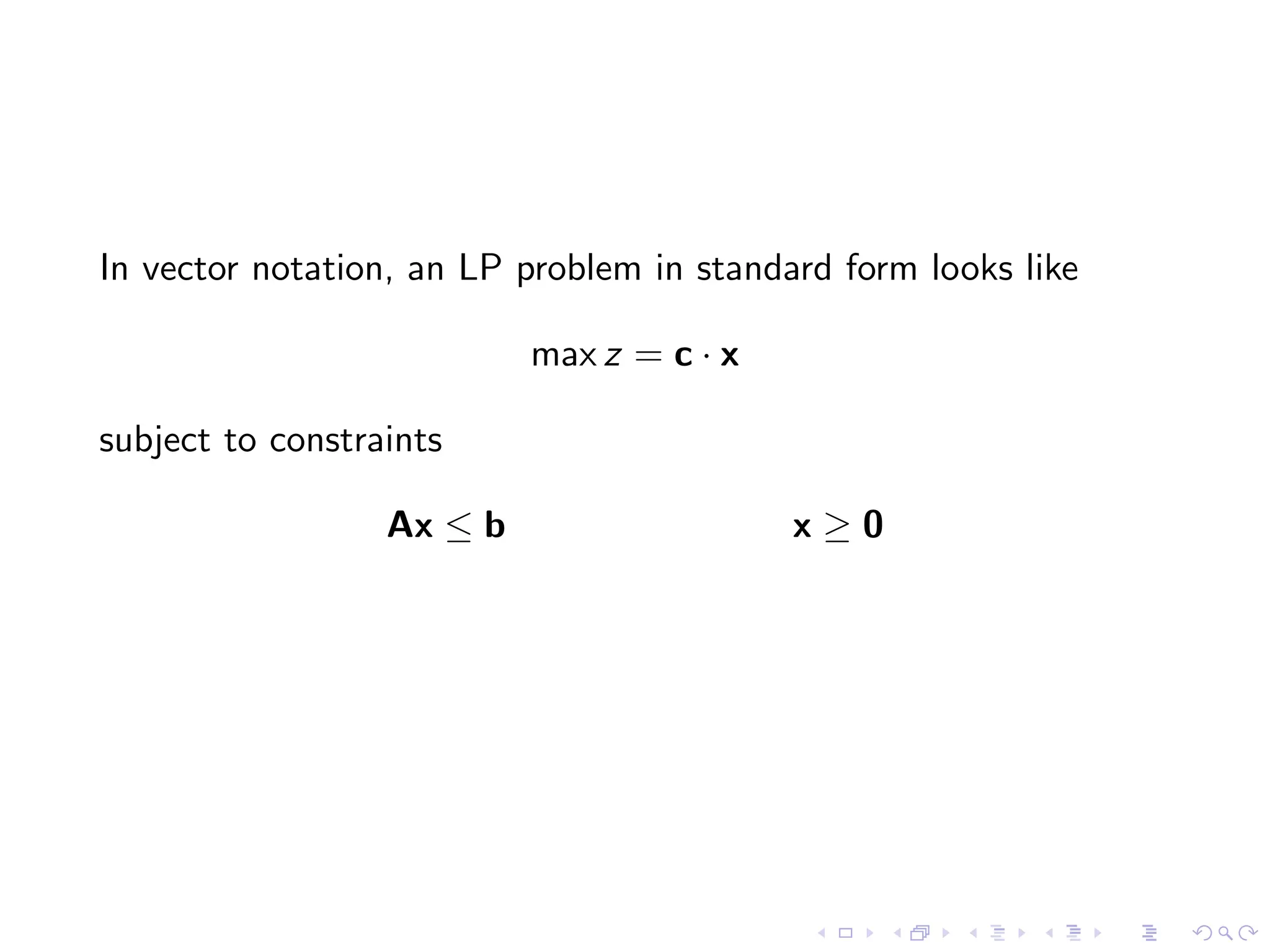
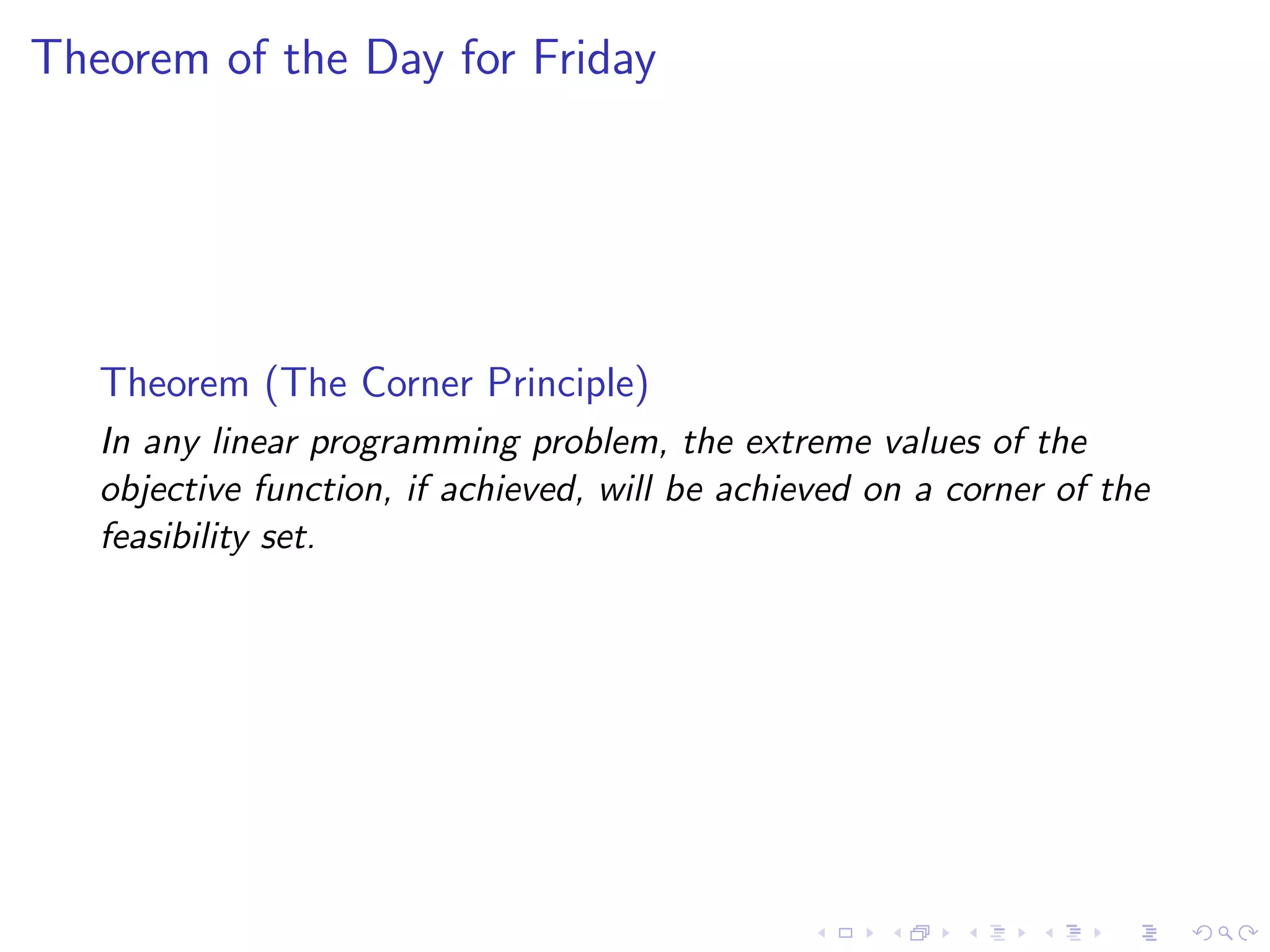
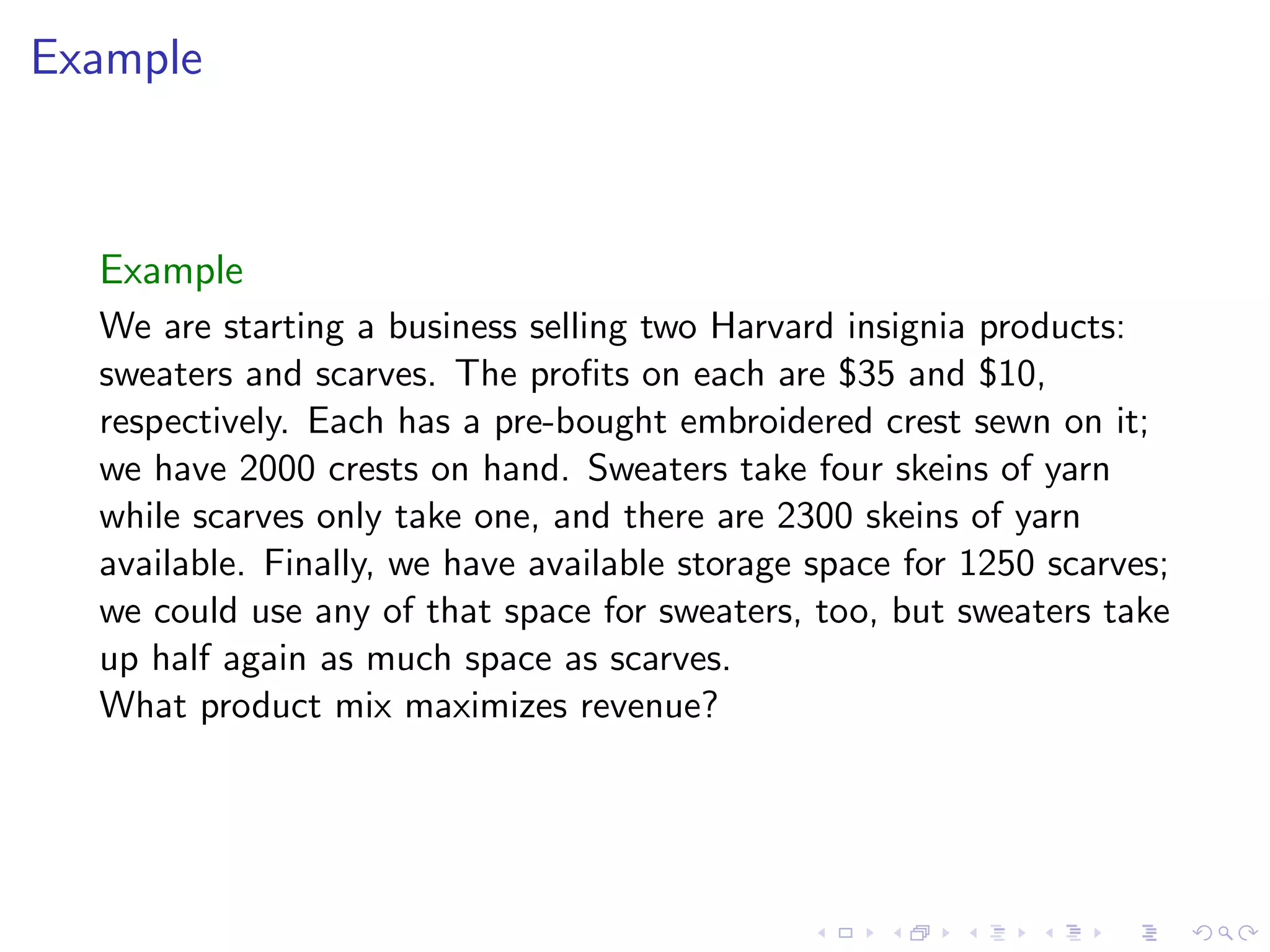
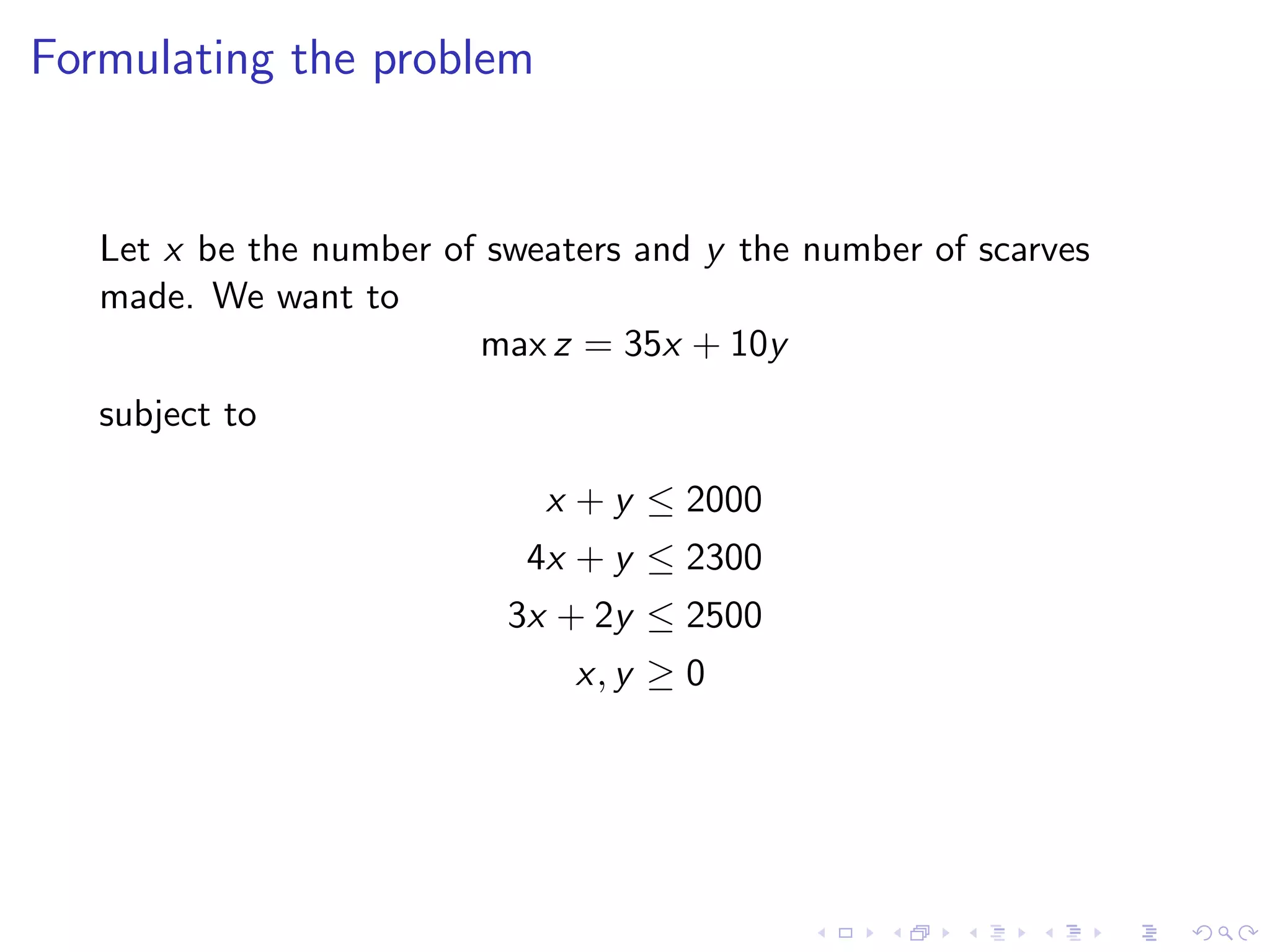
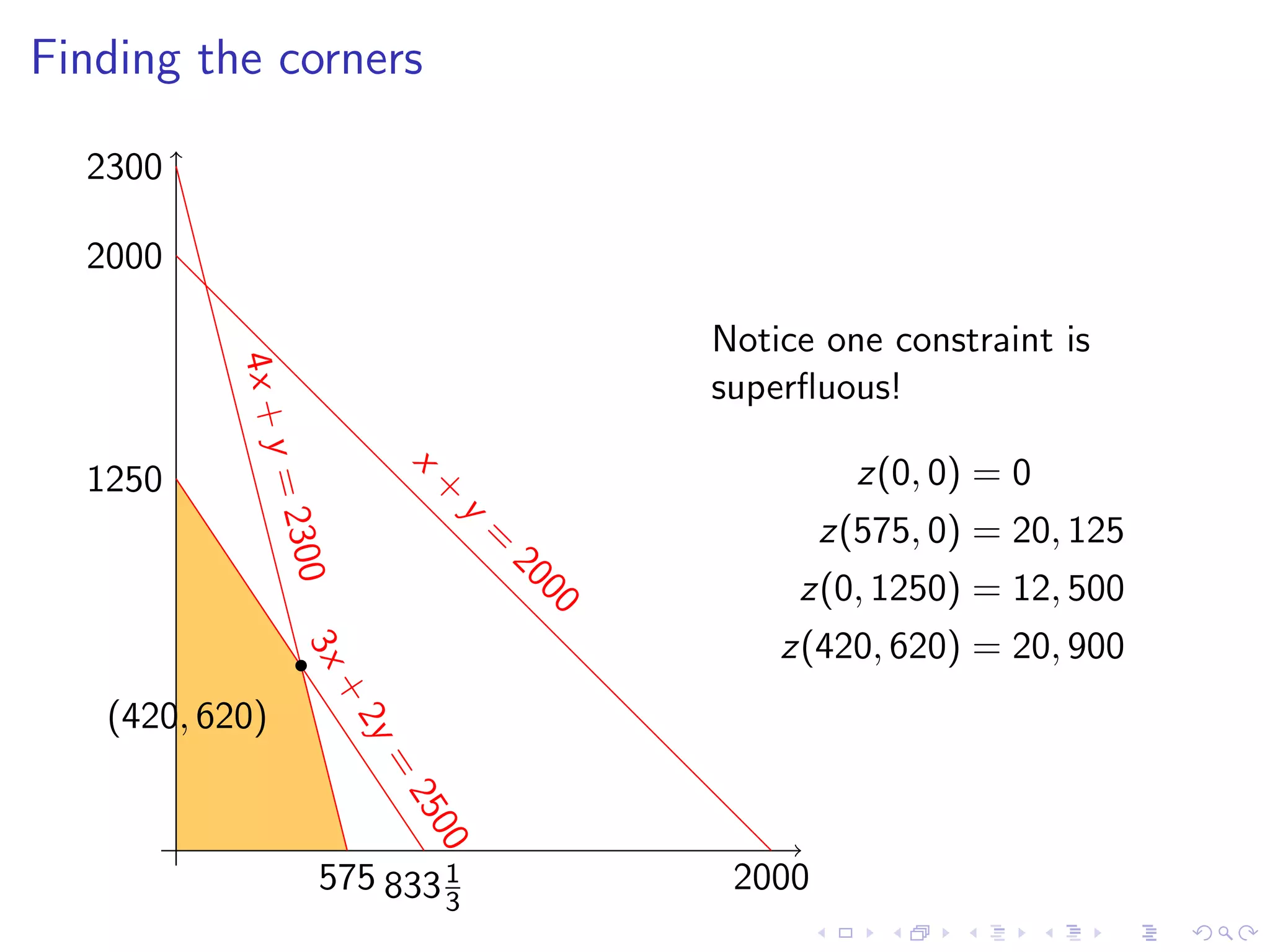
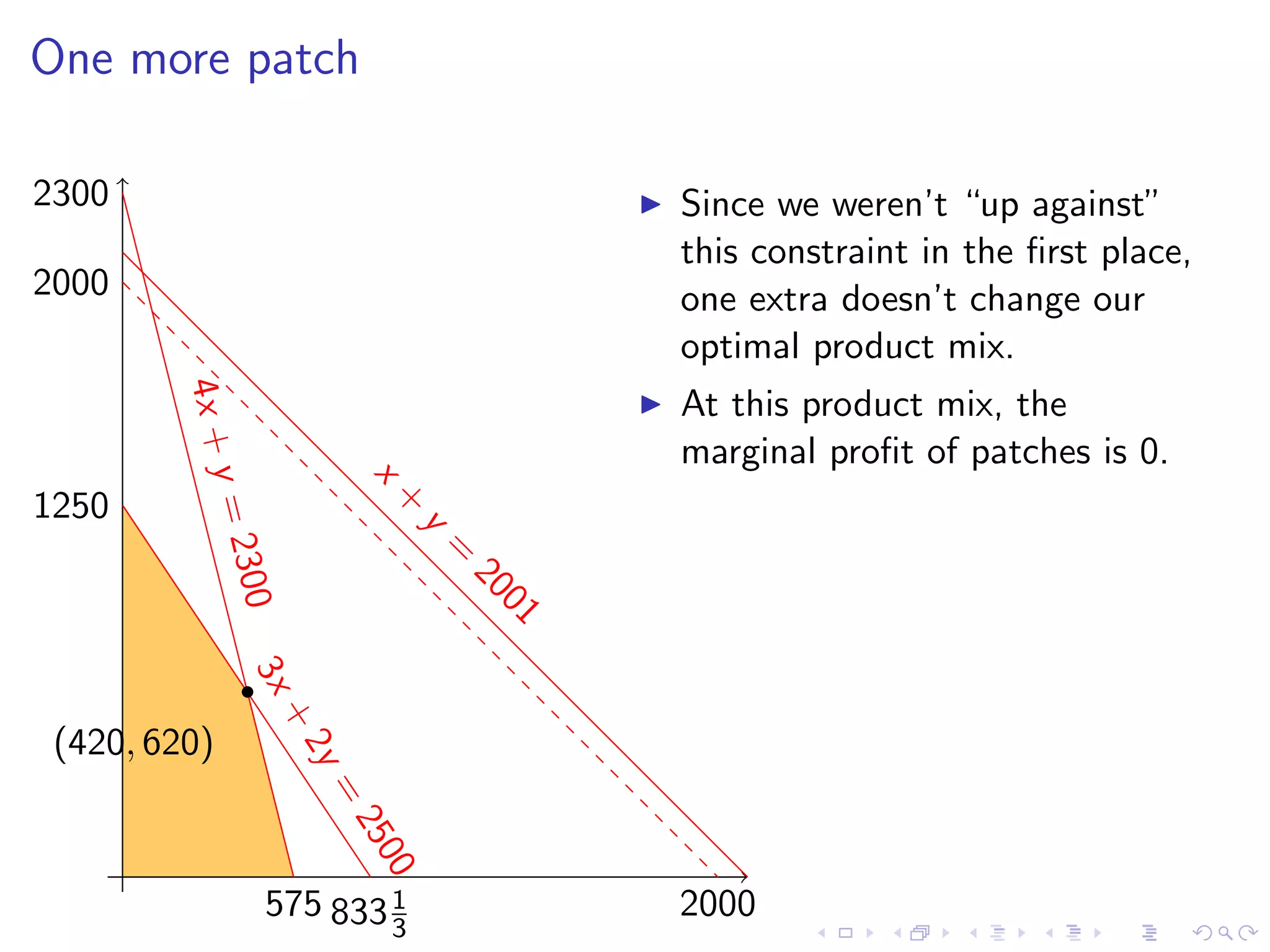
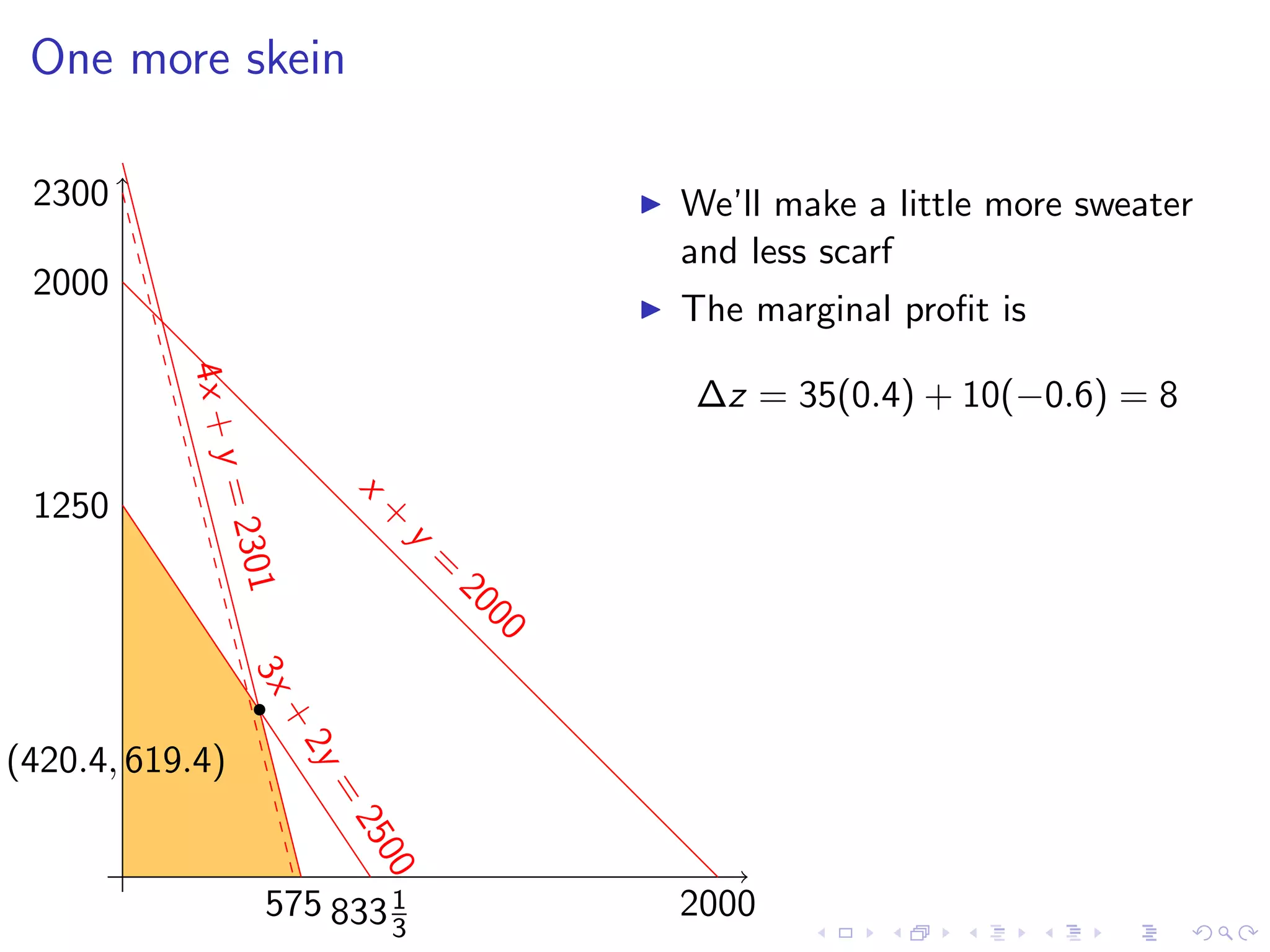
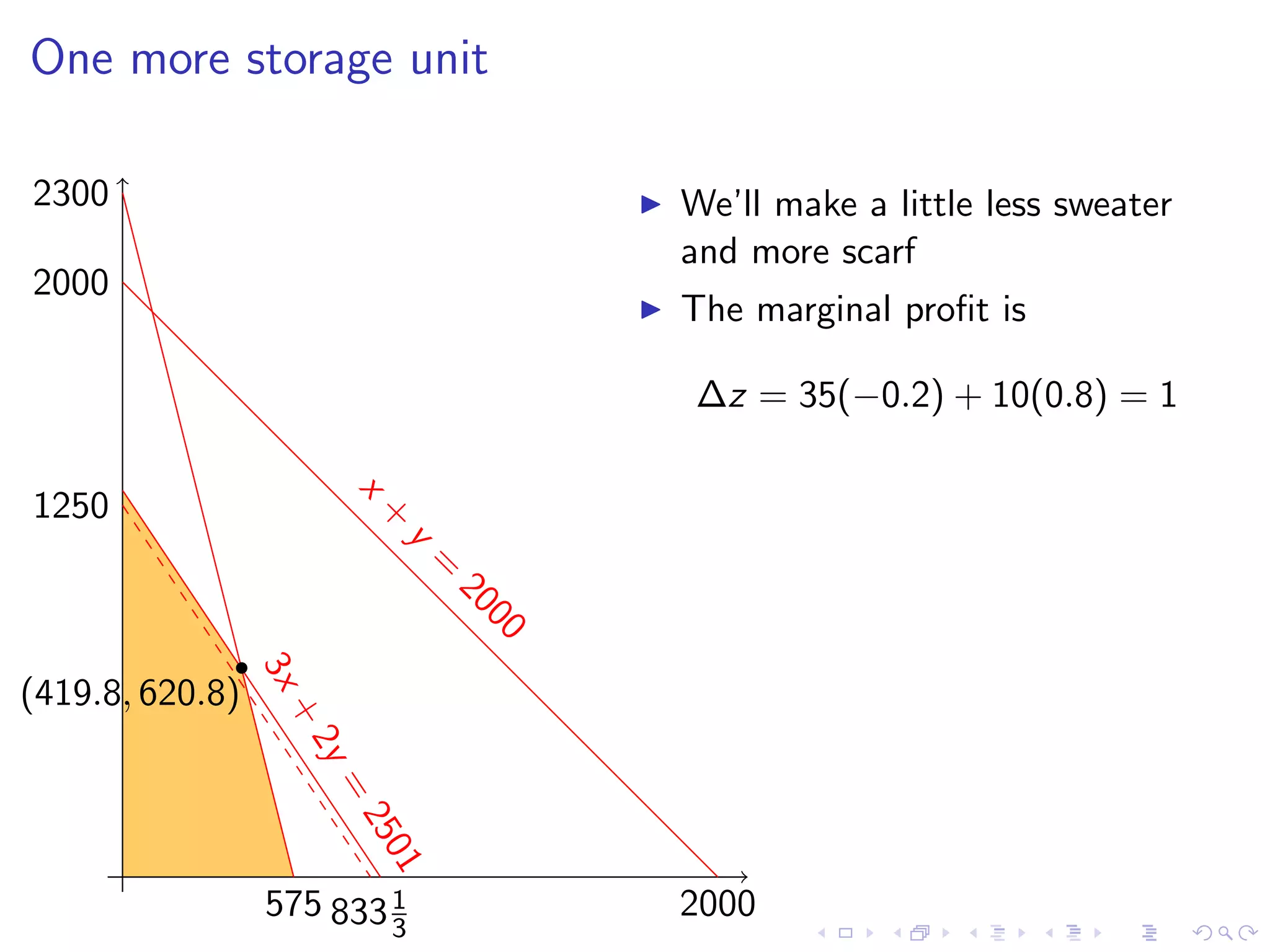
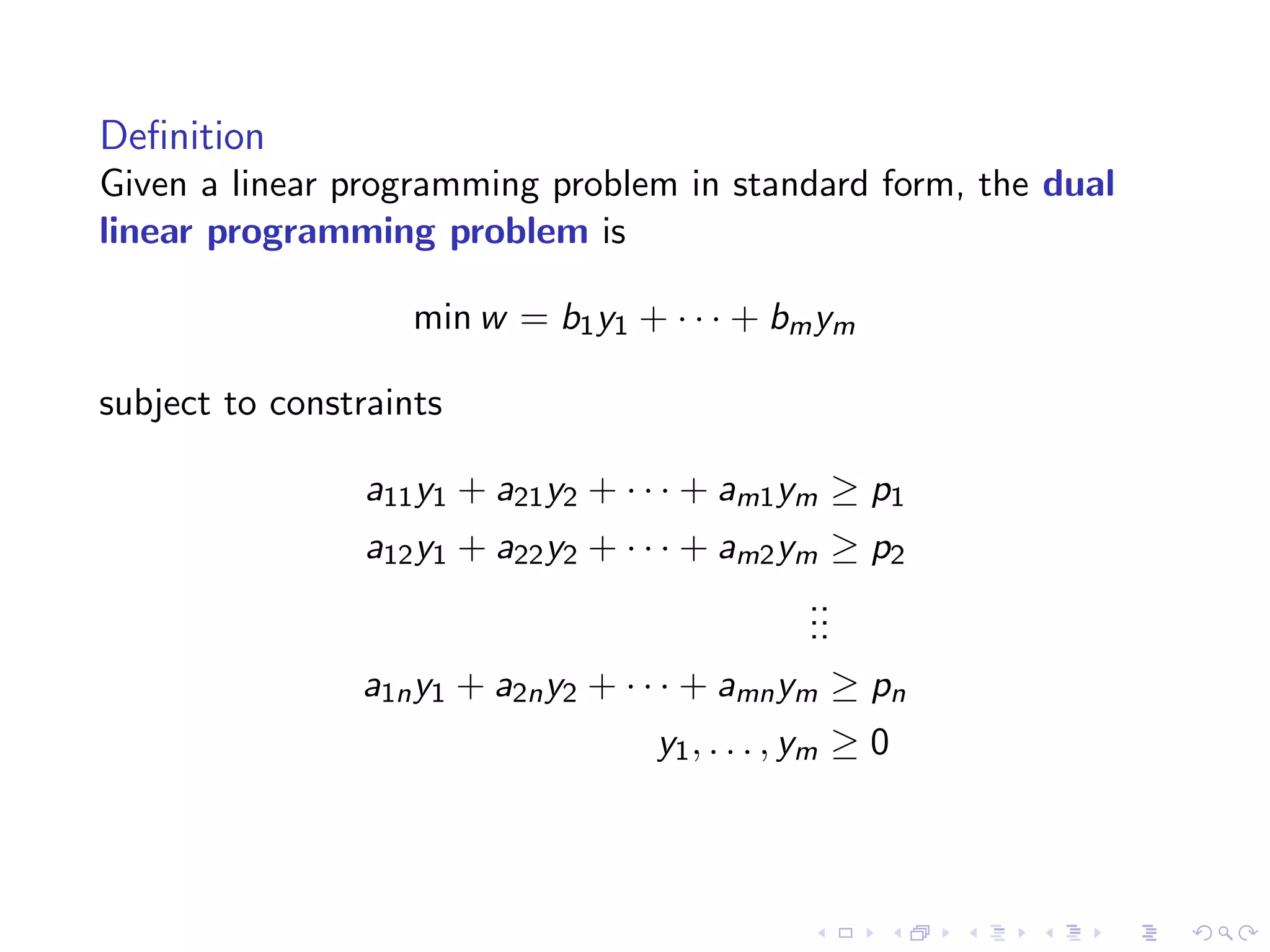
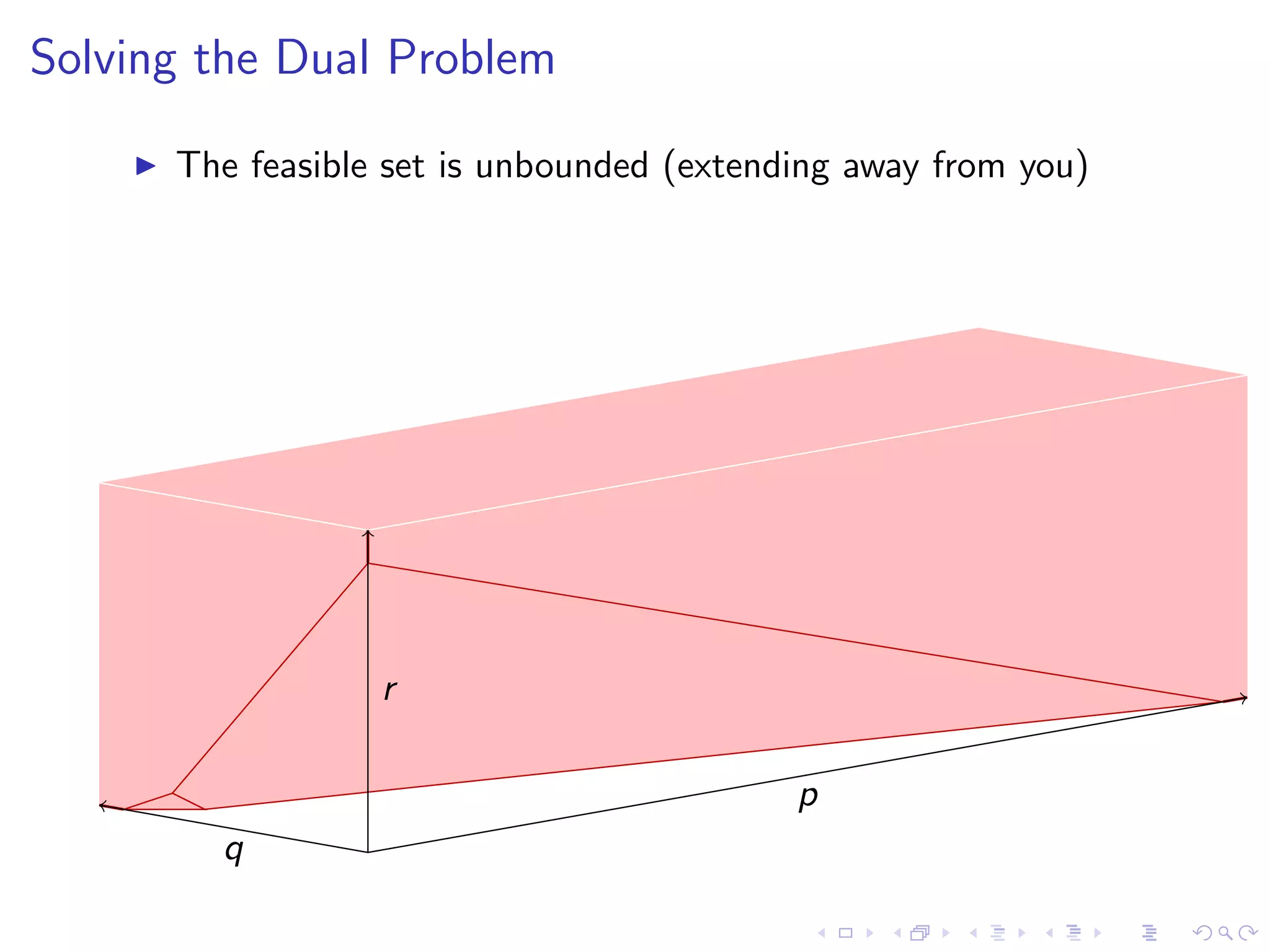
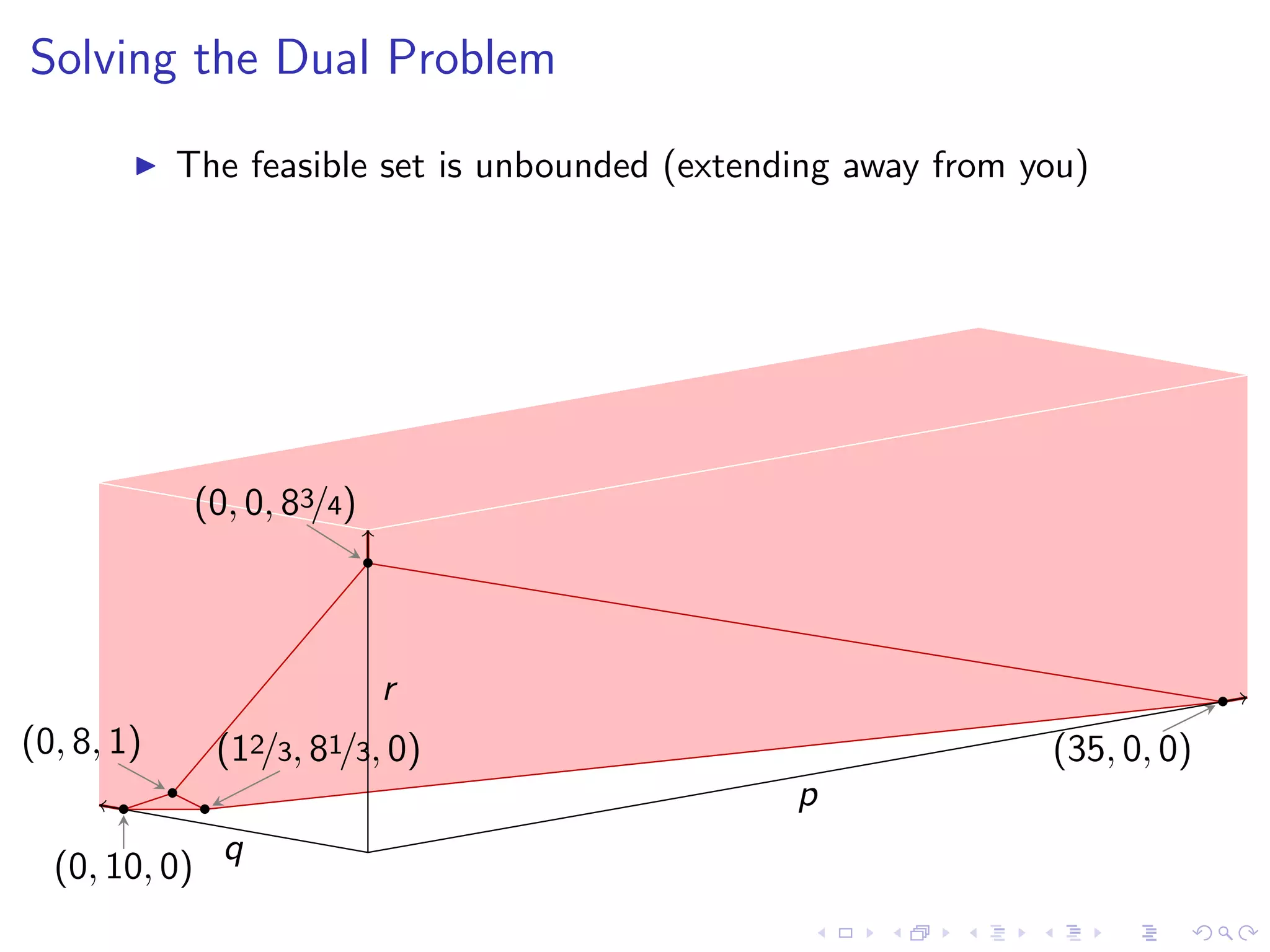
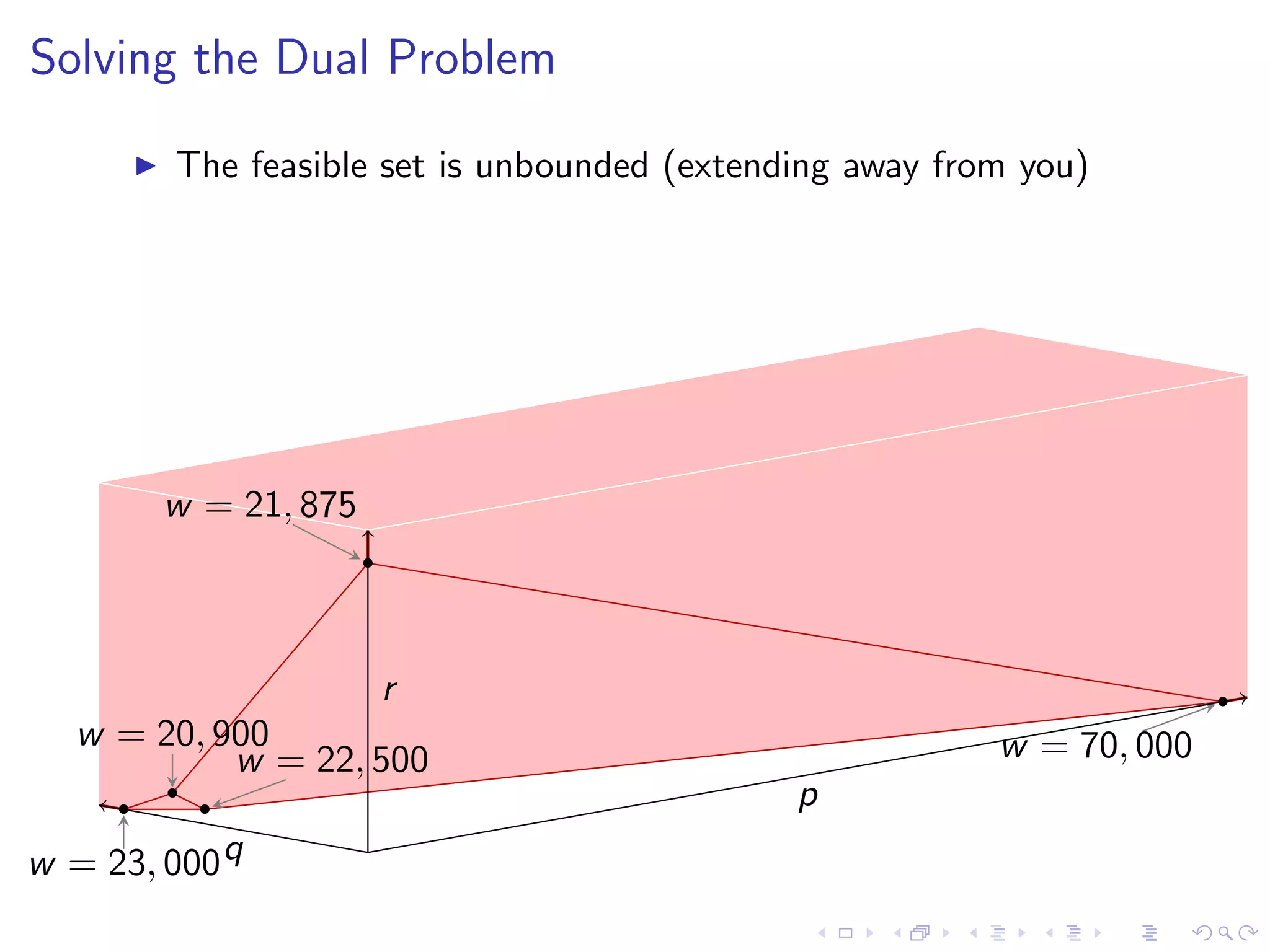
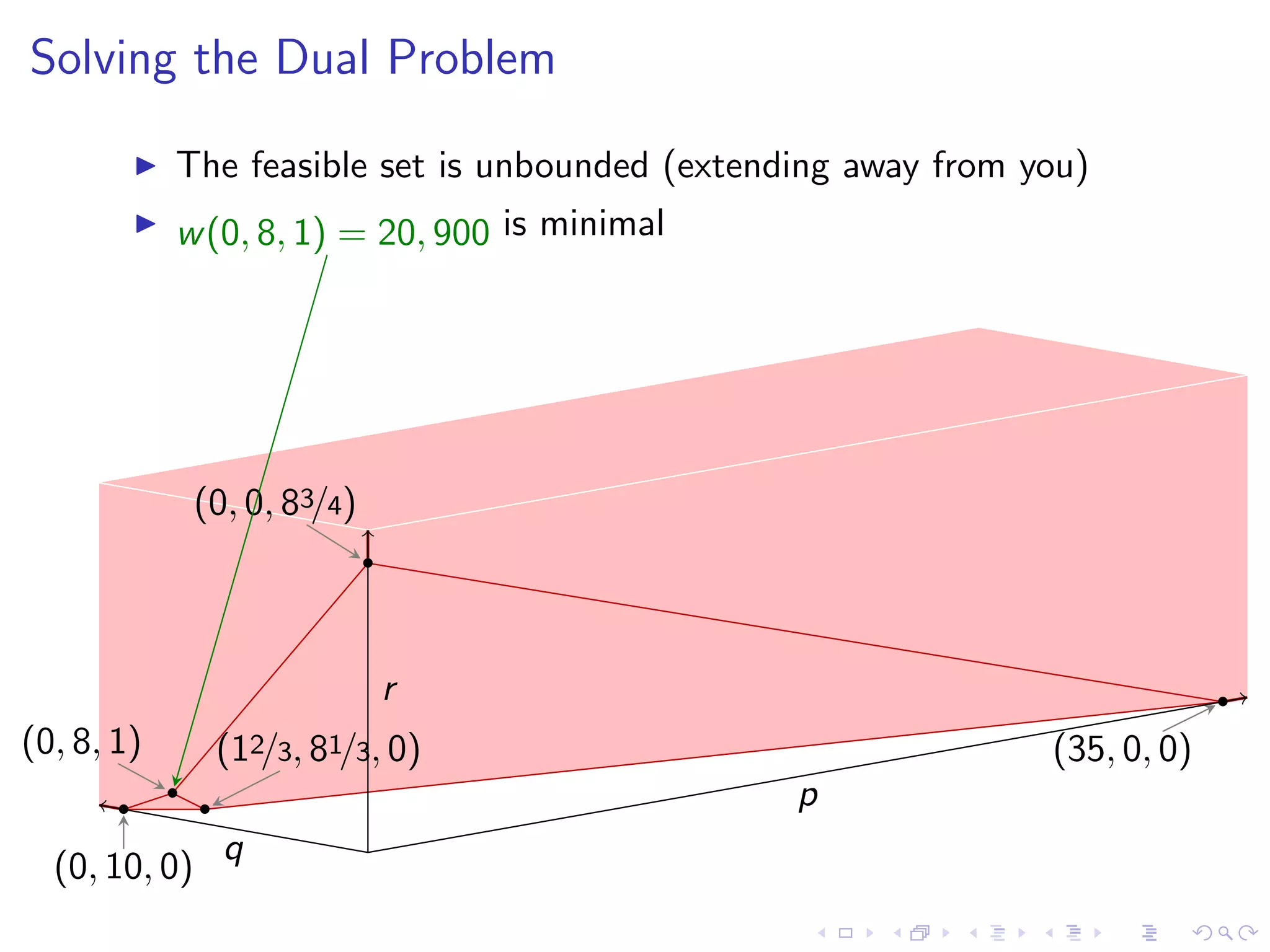
This document discusses duality in linear programming, outlining key concepts such as the standard form of linear programming problems, the corner principle, and shadow prices. It provides a practical example involving product mix optimization for a business selling sweaters and scarves, detailing the constraints and profit calculations. The document also introduces the dual problem associated with resource pricing for an entrepreneur interested in purchasing the business's resources.