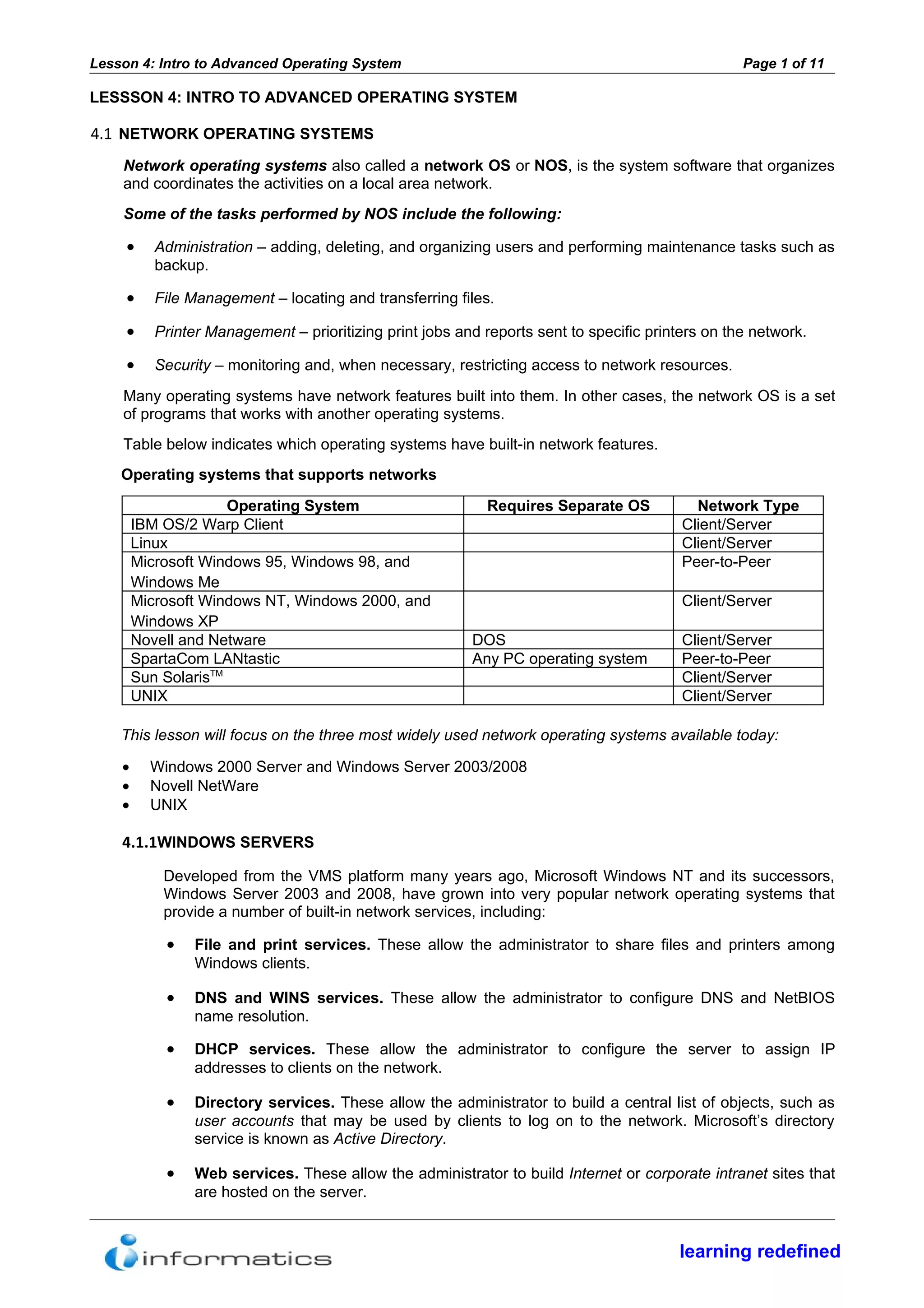
This document provides an introduction to advanced operating systems, focusing on network operating systems (NOS). It discusses the main functions of NOS including administration, file/printer management, security, and more. The most widely used NOS are then described in more detail: Windows servers, Novell NetWare, and UNIX. For Windows servers and NetWare, the core network services, supported clients, and directory services (Active Directory and eDirectory) are outlined. The document provides high-level information on the key features and roles of different network operating systems.