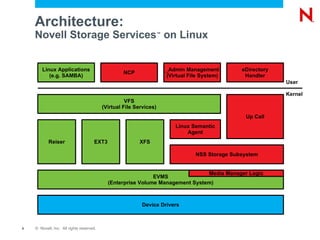
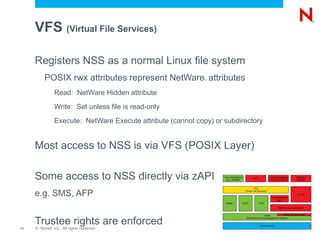
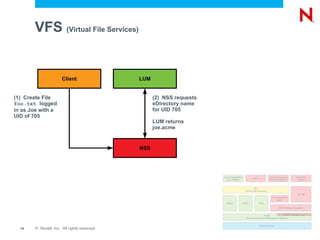
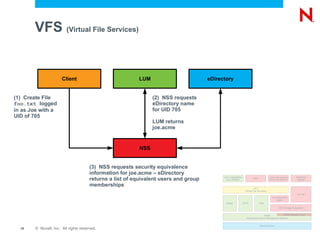
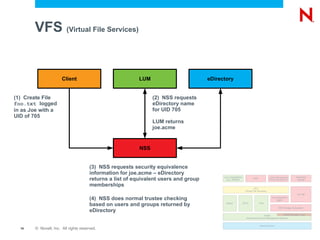
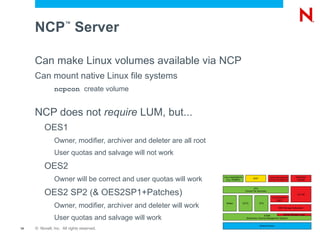
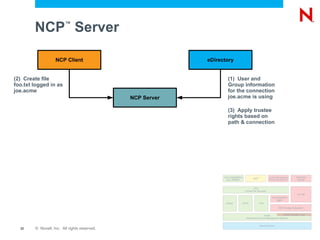
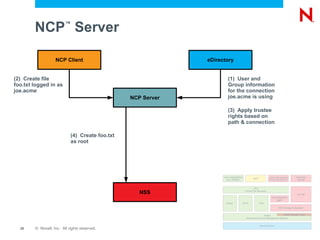
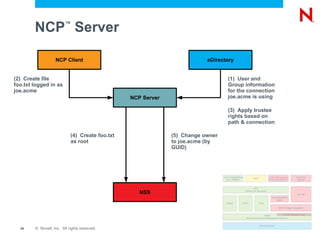
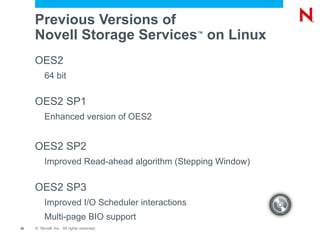
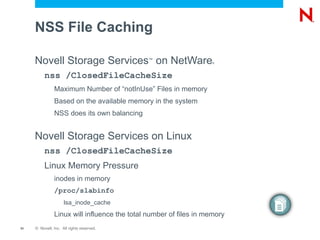
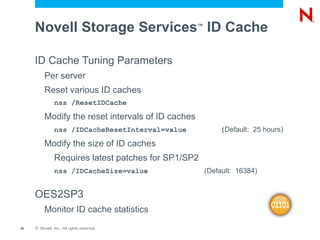
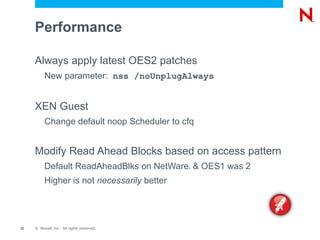
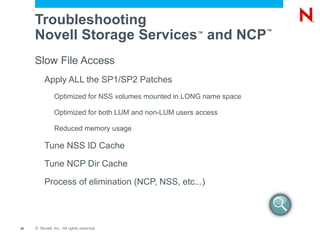
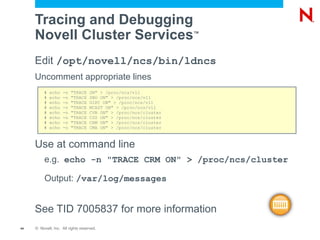
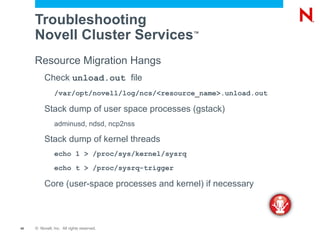
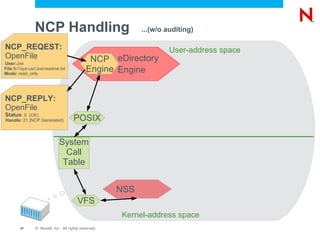
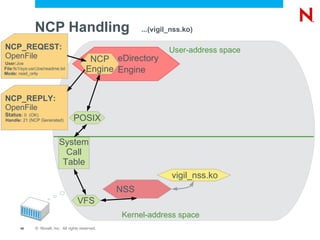
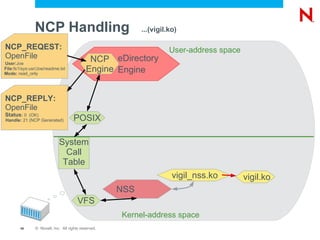
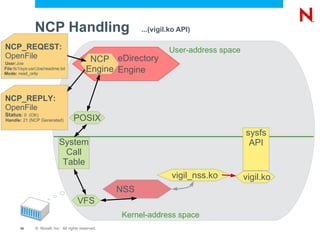
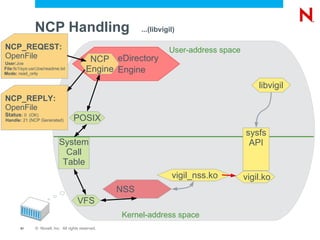
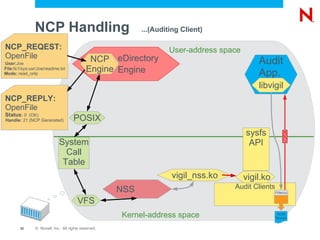
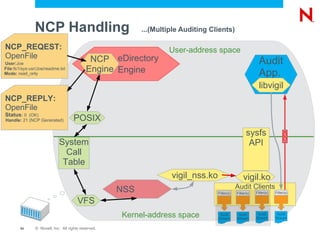
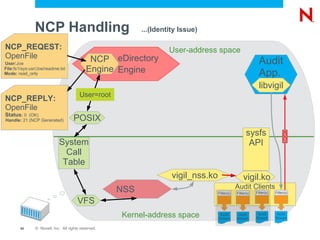
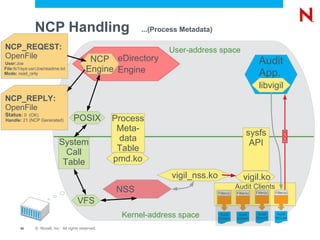
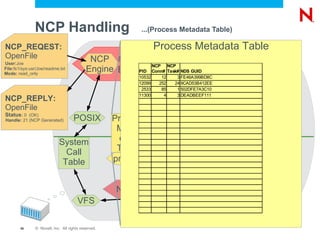
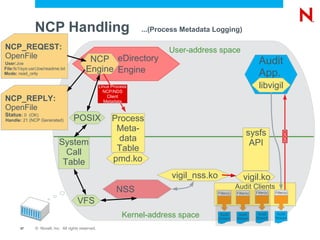
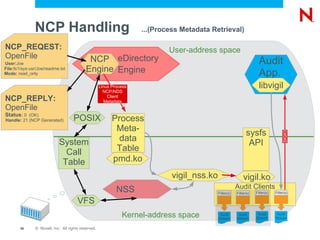
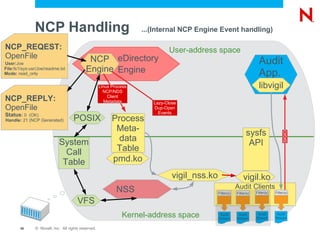
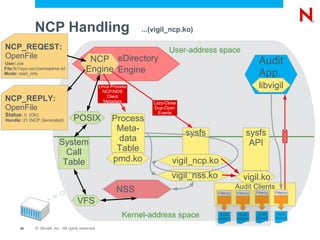
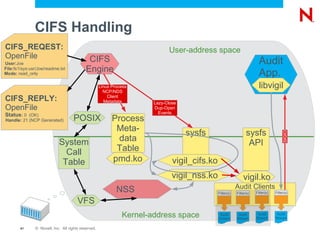
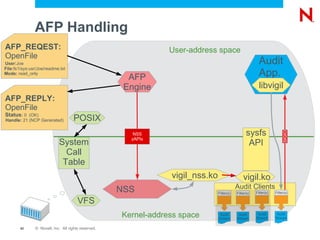
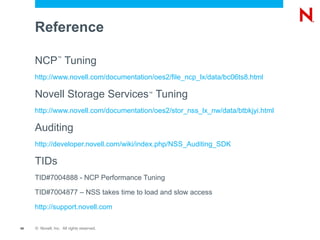
The document provides an overview of Novell Storage Services features and architecture when implemented on Linux using Novell Open Enterprise Server. It discusses features such as trustee models, quotas, compression. It describes the architecture which uses components like EVMS, NSS storage subsystem, NCP server, and VFS. It also covers tuning, troubleshooting, and clustering aspects of Novell Storage Services on Linux.
![Novell Storage Services ™ File System Performance, Clustering and Auditing in Novell ® Open Enterprise Server on Linux Marcus Gould Premium Support Engineer Novell, Inc. [email_address] Bart Schoofs WorldWide Support Engineer Novell, Inc. [email_address] Adam Jerome Senior Software Engineer Novell, Inc. [email_address] Vijai Babu Madhavan Filesystem Engineer Novell, Inc. [email_address]](https://image.slidesharecdn.com/cl309-101204115335-phpapp02/75/Cl309-1-2048.jpg)