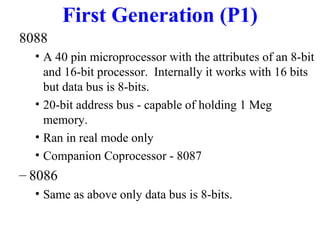
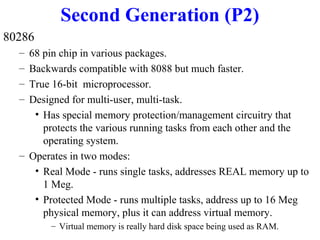
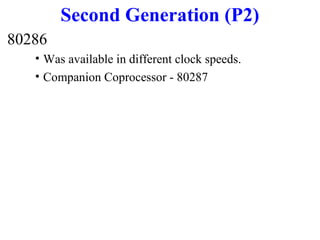
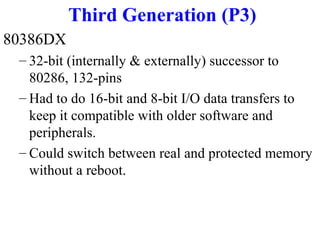
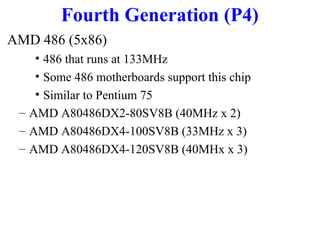
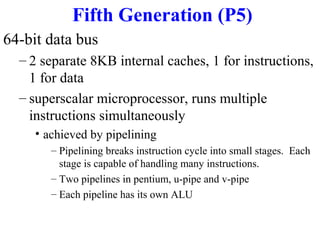
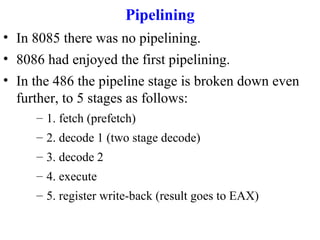
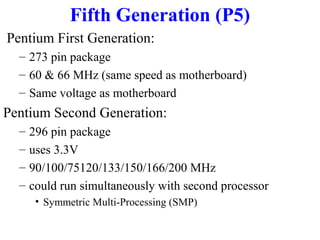
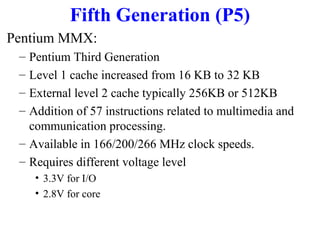
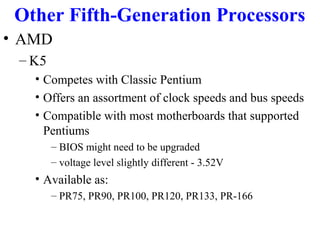
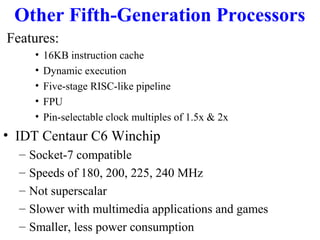
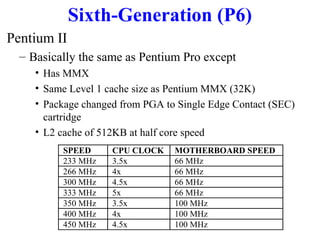
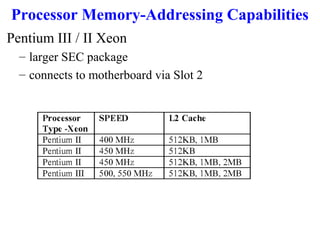
This document summarizes the history and generations of microprocessors from the early 1970s to the 2000s. It describes the key features and specifications of important processors like the Intel 4004, 8088, 286, 386, 486, Pentium, Pentium Pro, Pentium II, Pentium III, Pentium 4 and Itanium. Each generation brought performance improvements through higher clock speeds, increased transistor counts, cache memory, pipelining and other architectural enhancements. The document also discusses competing processors from AMD, Cyrix and others.