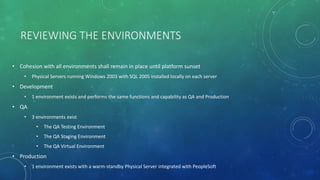
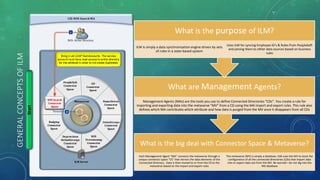
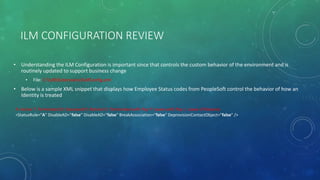
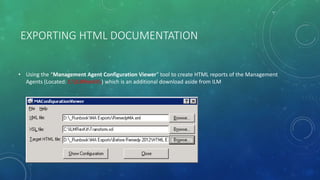
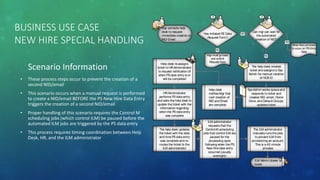
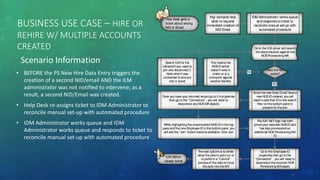
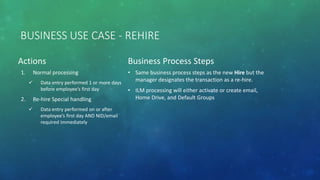
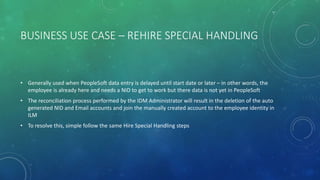
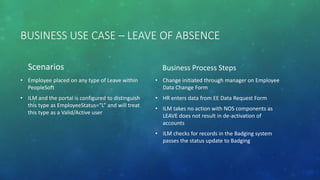
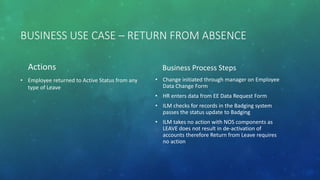
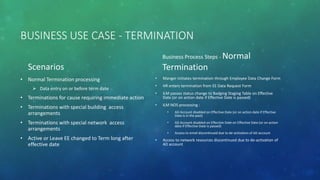
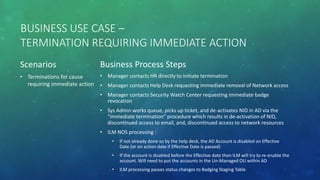
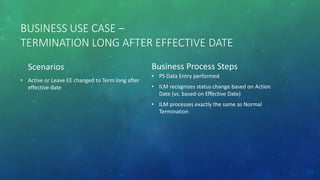
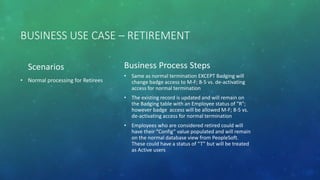
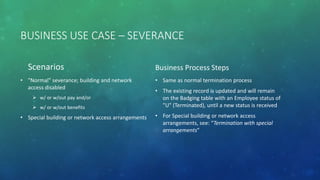
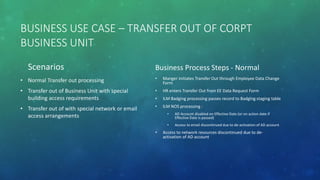
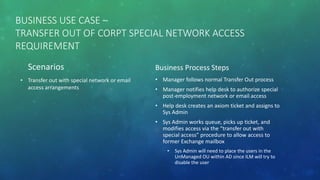
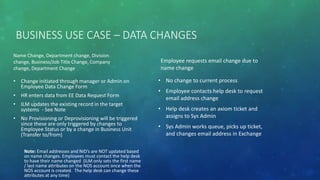
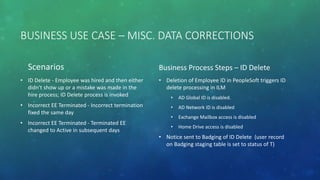
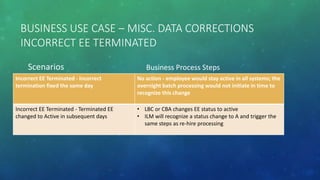
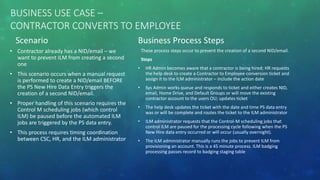
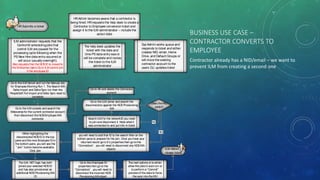
The document is a knowledge transfer presentation on the Microsoft Identity Lifecycle Manager (ILM) provided by Mike Reams, covering its core concepts, history, and operational procedures over two days. It outlines the agenda, objectives, and critical use cases in managing employee identity provisioning and access management. The presentation also discusses the technical environment, data sources, and specific scenarios related to hiring, rehiring, and terminations, detailing step-by-step business processes associated with each case.