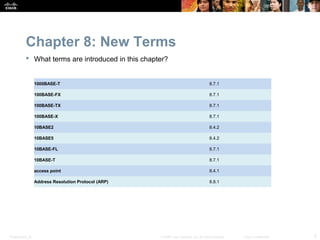
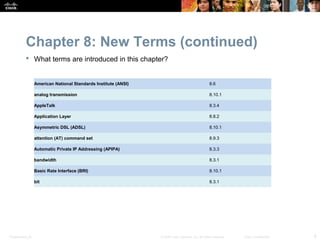
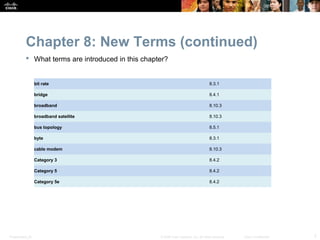
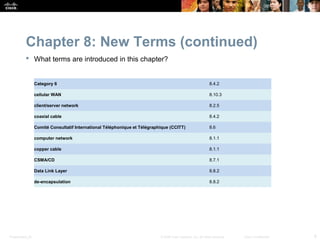
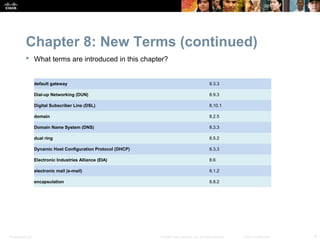
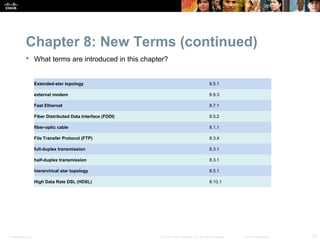
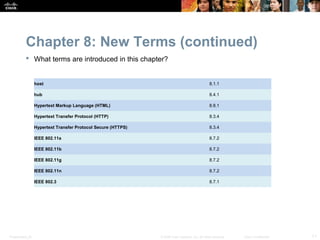
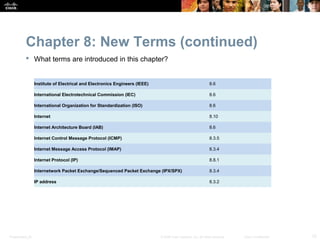
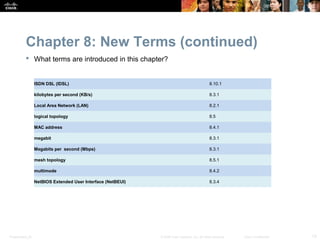
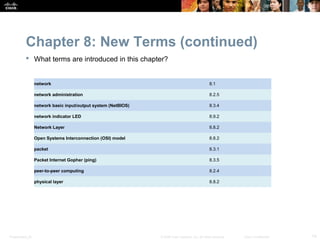
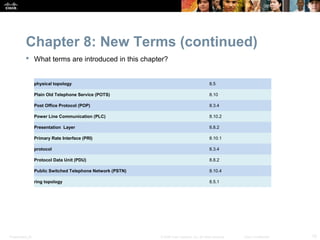
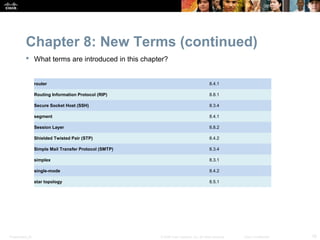
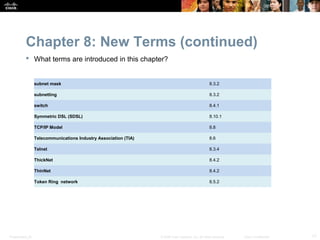
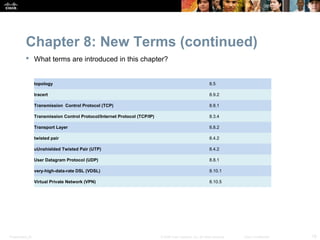
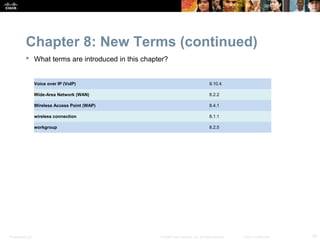
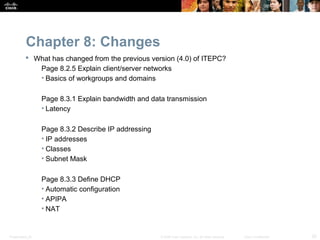
This chapter introduces fundamental networking concepts including networking principles, types of networks, networking components, LAN topologies, standards organizations, Ethernet standards, the OSI and TCP/IP models, configuring network interfaces, and network troubleshooting. It aims to provide students with the knowledge needed to install devices on a network and understand basic networking concepts. The chapter covers various networking terms and technologies and includes worksheets, labs, and Packet Tracer activities for students.