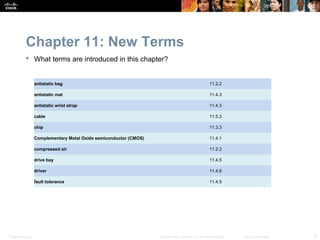
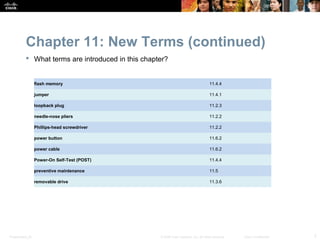
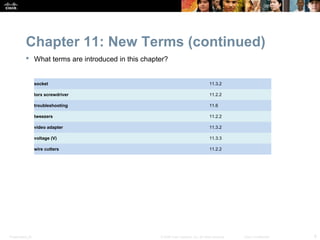
This chapter of the IT Essentials PC Hardware and Software 4.1 instructional resource provides an overview of advanced personal computer technician jobs and safe lab procedures. It describes situations requiring computer component replacement and teaches how to upgrade, configure, troubleshoot and perform preventative maintenance on personal computer components and peripherals. The chapter objectives and activities, new terms, and changes from the previous version are outlined.