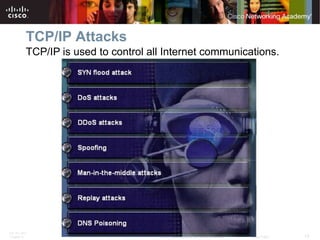
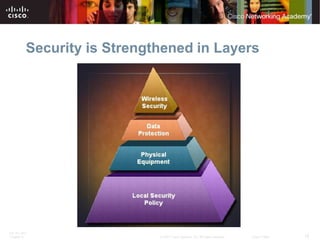
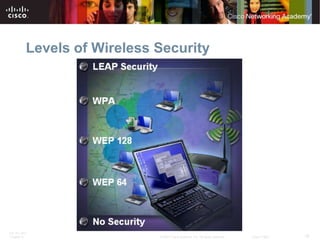
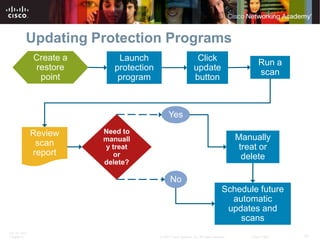
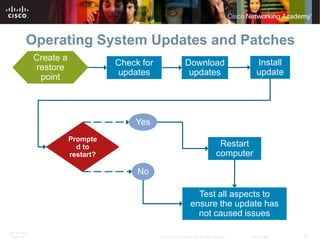
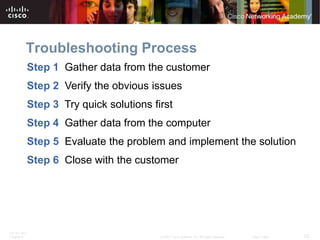
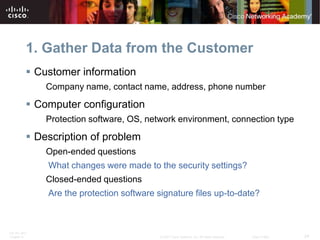
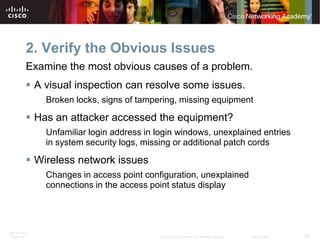
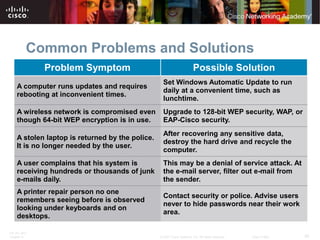
The document provides an overview of the content covered in Chapter 9 of the IT Essentials textbook, which includes explaining the importance of security, describing common security threats, identifying security procedures, preventative maintenance techniques, and how to troubleshoot security issues. It summarizes the learning objectives, lists the worksheets and activities, and previews the key topics covered in each section of the chapter such as viruses, firewalls, wireless security, and installing updates.