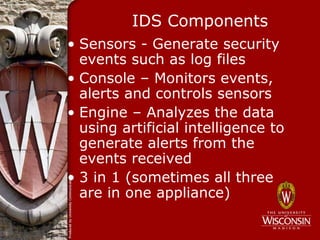
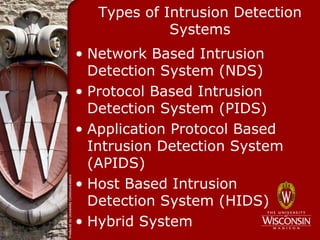
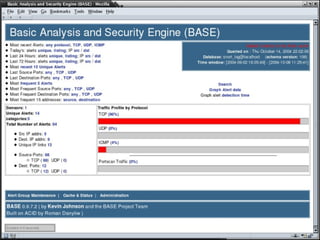
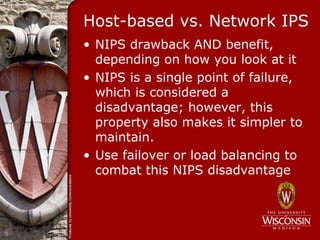
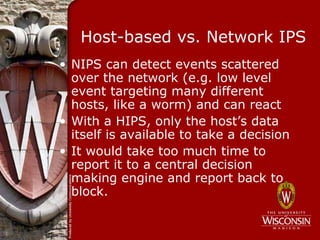
The document discusses intrusion detection and prevention systems (IDS/IPS). It describes what an IDS is, the components of an IDS, and different types of IDS including network-based, host-based, and hybrid systems. It also covers the differences between passive and reactive IDS, as well as techniques attackers use to evade detection like fragmentation and small packets. The document concludes by discussing intrusion prevention systems and how they differ from IDS in their ability to block threats in real-time.