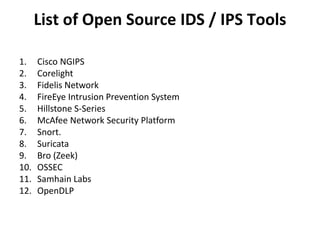
This document discusses intrusion detection systems (IDS), including the different types and methods they use. It describes signature-based detection which looks for known threats, and anomaly-based detection which identifies deviations from a network's normal behavior profile. It also covers stateful protocol analysis which compares traffic to protocol specifications. The document outlines host-based IDS for monitoring individual systems, network-based IDS for capturing network traffic, and intrusion prevention systems (IPS) which can detect and block threats in real-time. Finally, it lists some popular open source IDS and IPS tools.