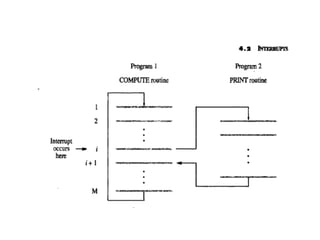
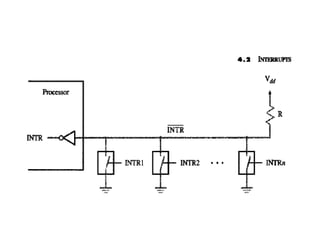
Interrupts allow input/output devices to alert the processor when they are ready. When an interrupt request occurs, the processor saves its context and jumps to an interrupt service routine. It then acknowledges the interrupt and restores its context before returning to the original instruction. Processors have mechanisms for prioritizing interrupts and enabling/disabling them to avoid infinite loops or unintended requests.