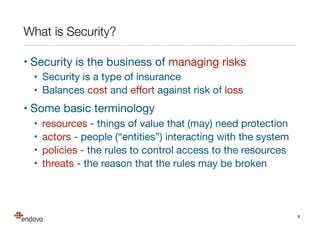
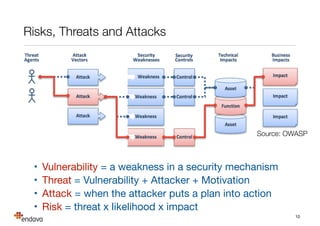
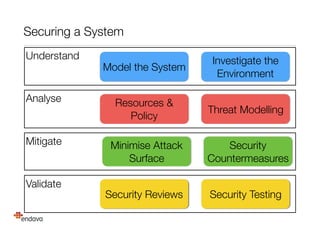
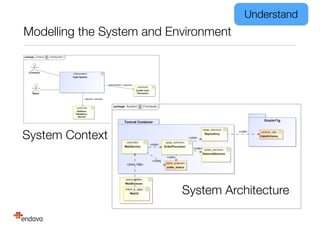
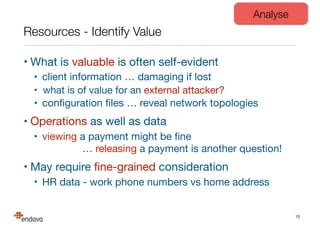
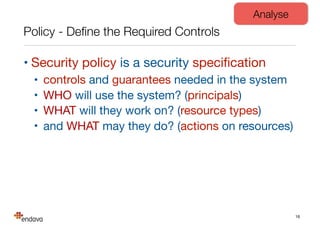
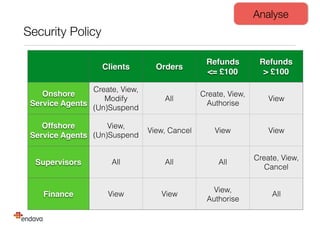
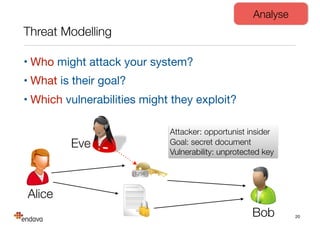
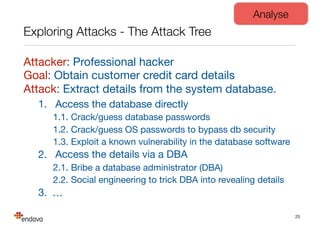
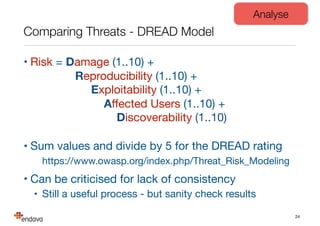
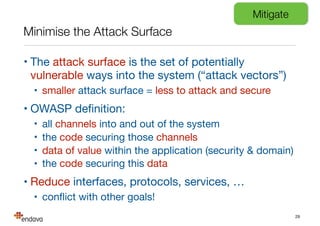
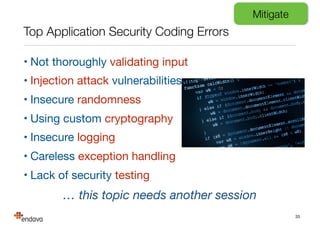
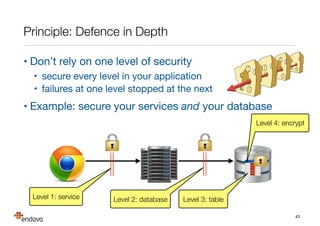
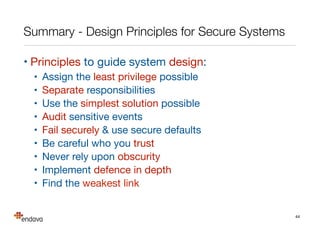
The document discusses the importance of understanding security based on risks rather than technology, emphasizing that proper security requires a blend of people, processes, and technology. It outlines methods for mitigating risks, including threat modeling, minimizing attack surfaces, and implementing security measures while recognizing that weaknesses often come from human error. Finally, it stresses the need for continuous improvement in security practices and the involvement of security specialists for significant risks.