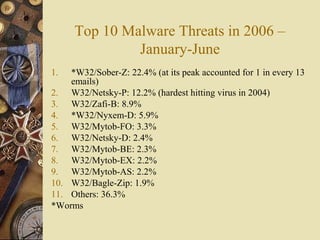
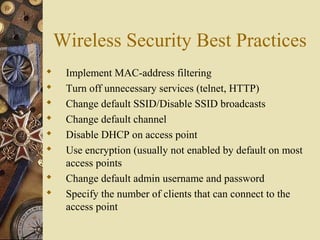
The document provides an overview of information security, outlining its importance, challenges, and best practices to protect digital assets. It highlights trends such as identity theft, malware, and the need for continual patch management, while emphasizing the growing demand for skilled information security professionals. Various preventive measures are suggested, including the use of antivirus and anti-spyware software, maintaining system updates, and implementing wireless security practices.