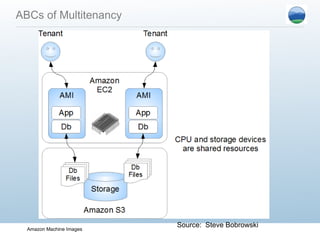
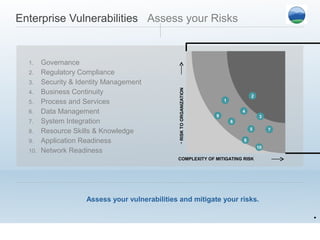
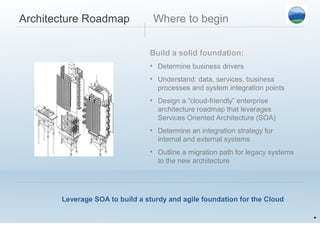
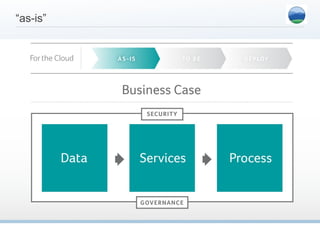
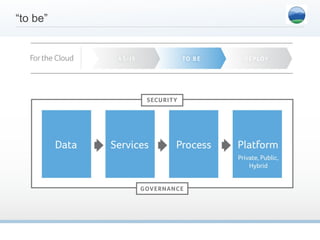
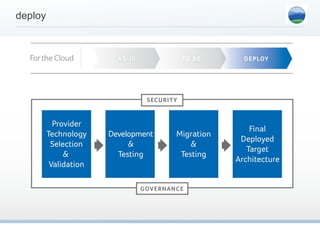
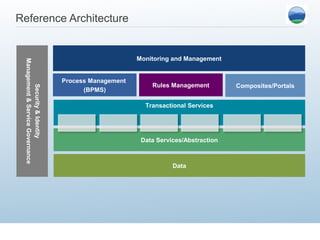
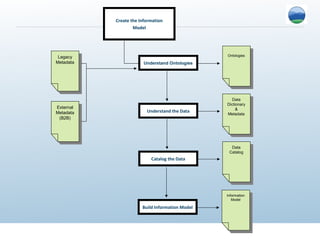
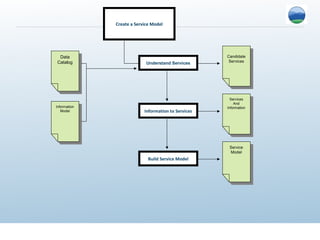
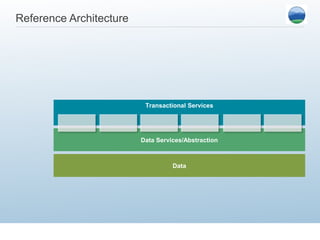
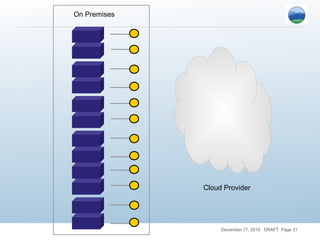
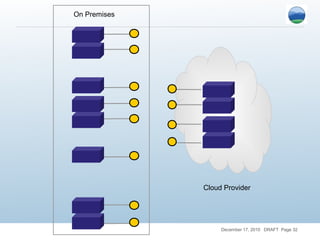
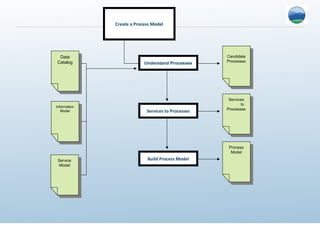
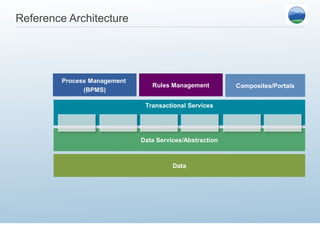
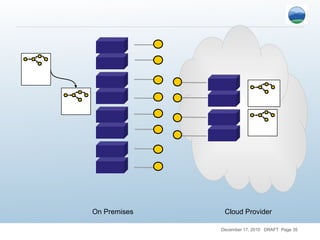
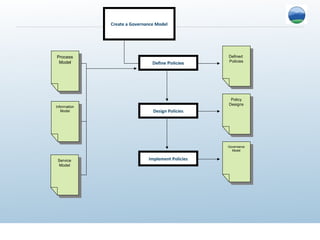
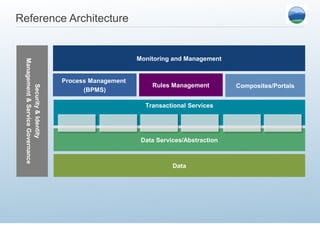
This document discusses best practices for designing cloud architectures. It recommends focusing on primitives like data, transaction, and utility services and building for tenants rather than individual users. The document also warns that security and governance must be addressed systematically. It provides an example reference architecture for migrating an existing business system to the cloud by breaking it into component services and redesigning the database.