This paper presents a method for detecting copy-move forgery in digital images through the use of discrete wavelet transform (DWT) and lexicographical sorting. The proposed technique involves converting images to grayscale, dividing them into blocks, and calculating feature vectors to identify duplicated regions. Experimental results indicate that the method demonstrates high accuracy in detecting forgery even under various image manipulations.
![International Journal of Collaborative Research in Engineering Sciences(2348-9707)
Volume I Issue 2, April, 2014
1
ISSN: 2348-9707© IJCRES | ijcres.com
FORGERY (COPY-MOVE) DETECTION IN DIGITAL
IMAGES USING BLOCK METHOD
AKHILESH KUMAR YADAV, DEENBANDHU SINGH, VIVEK KUMAR
Department of Computer Science and Engineering
Babu Banarasi Das University, Lucknow
akhi2232232@gmail.com, deenbandhusingh85@gmail.com, vivek.kumar0091@gmail.com
ABSTRACT- Digital images can be easily modified using powerful image editing software. Determining whether a
manipulation is innocent of sharpening from those which are malicious, such as removing or adding parts to an
image is the topic of this paper. In this paper we focus on detection of a special type of forgery-the Copy-Move
forgery, in this part of the original image is copied moved to desired location in the same image and pasted. The
proposed method compress images using DWT (discrete wavelet transform) and divided into blocks and choose
blocks than perform feature vector calculation and lexicographical sorting and duplicated blocks are identified
after sorting. This method is good at some manipulation/attack likes scaling, rotation, Gaussian noise, smoothing,
JPEG compression etc.
INDEX TERMS- Copy-Move forgery, Wavelet Transform, Lexicographical Sorting, Region Duplication Detection.
— — — — — — — — — — — — — — — — — — — —
1. INTRODUCTION
Now a day, it is easy task to create digital image forgeries
from the advanced digital cameras. Some of the tools
found in the editor are: cropping, resizing an image,
selecting part of a (lasso tool), removing rotating objects,
unwanted part of an image, merging pictures together.
Therefore it’s become a challenging task to verify the
originality of an image.
Digital image forgery detection methods are classified into
two approaches, which are active and passive approach. In
active approaches, the digital images require signatures,
watermarking etc. which are pre-processing. Passive
approach is different from active approaches; passive
approach does not need any watermark embedded in
advance.
The copy-move forgery is one of the difficult types of
forgery. In this forgery one portion of an image are copied
and then select the desired location for pasting in same
image. The target of this type of forgery is to hide or add
some main feature in same image. A reduced dimension
representation is proposed to A.C. Popescu [2], in this
image blocks are given by PCA (principal component
analysis). After that to get duplicated regions we performed
lexicographically sorting into every block. H. Huang [3]
first calculates SIFT descriptors of an image, which are not
depending on rotation and illumination etc. For detecting
copy-move forgery in the image, all these descriptors are
matched with each other.
2. PROPOSED METHOD
In our proposed method first we take an input image and
then check image is in RGB or Gray. If image is not in
gray scales, convert the image into gray scale image, then
following the step hich are shown in figure-1.
Figure-1 Flow Chart of Proposed Method
Gray Scale Conversion
Block Creation
Feature Extraction
Exact Match
Shift Vector Calculation
Detection Result
Input Image](https://image.slidesharecdn.com/fdd0431201403-140526090453-phpapp02/75/FORGERY-COPY-MOVE-DETECTION-IN-DIGITAL-IMAGES-USING-BLOCK-METHOD-1-2048.jpg)
![International Journal of Collaborative Research in Engineering Sciences(2348-9707)
Volume I Issue 2, April, 2014
2
ISSN: 2348-9707© IJCRES | ijcres.com
2.1 Discrete Wavelet Transform
A discrete wavelet transforms (DWT) is wavelet
transforms for which the wavelets are discretely sampled.
The basic idea of discrete wavelet transform is to reduce at
each level for the size of the image.
The haar wavelet transforms is the simplest of the all
wavelet transform. In this simply input value 2n
, sorting the
difference and passing the sum. This process is repeated
recursively, pairing up the sums to provide the next scale:
finally resulting in 2n
-1 differences and one final sum.
Figure 2
Figure 3 Type [2] an example of the 2D DWT
2.2 Block Creation
Figure 1 depicts the flow chart of proposed methods. The
input image of size x×y is divided into ‘a’ blocks of size
b×b pixels by moving the block point to point on the
image[1]. Each block of the image is iteratively compared
to every other block. The adjacent neighbors of the marked
blocks are compared, in copy-move forgery.
2.3 Exact Match
So that, every block contains nine feature vectors V = v1s,
v2, v3, v4, v5, v6, v7, v8. We contain an array a, all these
block is sorted into it. The starting pixel of this block will
contain in array of row and column indices with features of
block. It means, this array has contained d [M – b + 1] *[N
– b + rows] and [9+2] columns. In sorting, first nine
columns may be used. Since, radix sort is sufficient method
for the integers of normalization by features [4].
Alphabetical order or lexicographical product is
generalization of the way the alphabetical order of words is
based on the alphabetical order of their component letters.
So that, the highest priority is given by serial, first priority
is given to v1 to v5 and left for the other vectors features
v6 to v9. One pixel is containing information which is
contributing to two different sub blocks. Strongly
correlated features are given by it [5].
2.4 Feature Extraction
Formally, the positions are let be consider as [j1, j2] and
[k1, k2]. Between the two matching blocks, the shift vector
s is calculated as-
s = [s1, s2] = [j1 – k1, j2 – k2].
So that, the same shift is corresponding to the shift vector s
and –s, the normalization is done for shift vectors s.
If necessary, we get s1≥0 by multiplying by -1. So that for
every pair of block matching, the normalized shift vector
counter C is incremented by one:
C (s1, s2) = C (s1, s2) + 1.
The sorted matrix A contains the counter C incrementation
for every pair of consecutive matching’s rows. Before the
algorithm starts, the shift vector is initialized zero. At the
end of the matching process, different normalized shift
vectors occur by the counter C indicates the frequencies.
Then the entire normalized shift vectors s (1), s (2)… s (K)
find by the algorithm, whose occurrence exceeds an user-
specified threshold T: C(s(r)) > T for all r = 1… K.
The matching blocks that contributed to that specific shift
vector are colored with the same color and thus identified
with segments that might have been moved and copied; it
is for all normalized shift vectors [6].
2.5 Detection of Duplicated Region
The algorithm identified the size of the smallest segment
which is related to the value of the threshold T. The
algorithm may miss some not-so-closely matching blocks
of large value. While too many false matches may
introduce to too small value of T. We repeat that the Q
factor Controls the sensitivity of the algorithm to the
degree of matching between blocks, while the block size B
and threshold T control the minimal size of the segment
that can be detected.
We perform erosion for removing such false matches
followed by dilation. Before one or two erosions, the
boundaries are shrunk from erosion of the matched block.
Unwanted blocks are removing from it for the small
blocks. For getting forged region for the original shape, we
performed dilation of same numbers of time [5].
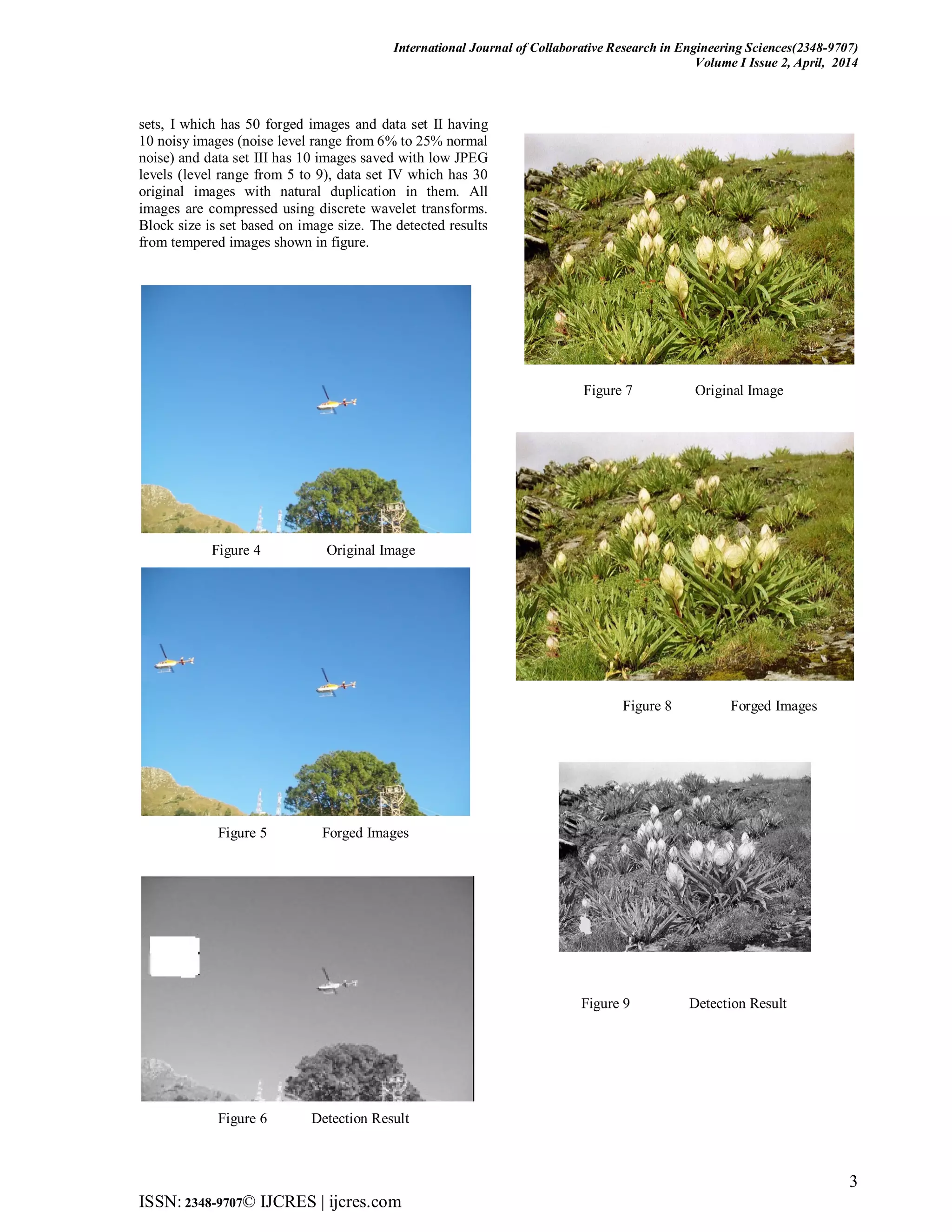
3. Experimental Result
In the experiments carried out for the detection process,
several images are tempered by copying and pasting one
image block over another, in the same image using
malicious tools. The whole process was implemented in
MATLAB (R2011a) and executed on a computer of CPU
2.0 GHz with secondary storage memory of 320 GB and
main memory 3 GB. Experimental data set consists of data](https://image.slidesharecdn.com/fdd0431201403-140526090453-phpapp02/75/FORGERY-COPY-MOVE-DETECTION-IN-DIGITAL-IMAGES-USING-BLOCK-METHOD-2-2048.jpg)
![International Journal of Collaborative Research in Engineering Sciences(2348-9707)
Volume I Issue 2, April, 2014
4
ISSN: 2348-9707© IJCRES | ijcres.com
Figure 10 Original Image
Figure 11 Forged Images
Figure 12 Detection Result
Comparison result of propose approach with other existing
methods [1] [5].
Table 1 Comparison
Algorithm False Detection Right Detection
[1] 0.222 0.643
[2] 0.721 0.8771
Proposed
Method
0.822 0.9633
CONCLUSION
In this paper an algorithm for detecting copy move forgery
using wavelet transform is proposed. Our method of stand
to in the original images for detecting duplicated region
attacked by way of rotation (up to some extent), JPEG
compression and Gaussian noise.
REFERENCES
[1] Tehseen Shahid, Atif Bin Mansoor,” copy-move forgery detection
algorithm for a digital images and a new accuracy metric”, in
international journal of recent trends in engineering, Vol 2, No. 2,
November 2009.
[2] A.C. Popescu and H. Farid,” Exposing digital forgeries by detecting
duplicated image regions”, Technical Report TR2004-515,
Dartmouth College, Aug. 2004.
[3] H. Huang, W. Guo, and Y. Zhang, “Detection of Copy-Move
Forgery in Digital Images Using SIFT Algorithm,” in Proceedings
of IEEE Pacific-Asia Workshop on Computational Intelligence and
Industrial Application, Vol. 2, 2008, pp. 272-276.
[4] Hwei-Jen Lin, Chun-Wei Wang, Yang-Ta Kao, “Fast Copy-Move
Forgery Detection,” WSEAS TRANSACTIONS on SIGNAL
PROCESSING, Issue 5, Volume 5, May 2009, pp. 188-197.
[5] Vivek Kumar Singh and R.C. Tripathi,” Fast and Efficient Region
Duplication Detection in Digital Images Using Sub-Blocking
Methods”, in international journal of advanced science and
technology, Vol. 35, October, 2011.
[6] Jessica Fridrich, David Soukal, and Jan Lukáš,” Detection of Copy-
Move Forgery in Digital Images”.
[7] Shinfeng D. Lin and Tszan Wu,” An Integrated Technique for
Splicing and Copy Move forgery Image Detection”, in 2011 4th
International Confress on Image and Signal Processing.
[8] Saiqa Khan, Arun Kulkarni,” Robust Method for Detection of Copy-
Move Forgery in Digital Images”, in IEEE 2010.
AUTHORS
First Author – Akhilesh Kumar Yadav, M.tech. Babu
Banarasi Das University, Lucknow, Uttar Pradesh, India.
akhi2232232@gmail.com
Second Author – Deenbandhu Singh, M.tech. Babu
Banarasi Das University, Lucknow, Uttar Pradesh, India
deenbandhusingh85@gmail.com
Third Author – Vivek Kumar, Sr. Lecturer Computer
Science Department, Babu Banarasi Das University,
Lucknow, Uttar Pradesh, India.
vivek.kumar0091@gmail.com](https://image.slidesharecdn.com/fdd0431201403-140526090453-phpapp02/75/FORGERY-COPY-MOVE-DETECTION-IN-DIGITAL-IMAGES-USING-BLOCK-METHOD-4-2048.jpg)