The document outlines a research thesis on video inpainting detection, aiming to restore lost video parts and detect forged regions using optical flow analysis. It critiques existing detection techniques for failing to address newer methods and proposes a novel algorithm that effectively identifies multiple inpainting techniques. Experimental results demonstrate the algorithm's superior performance compared to previous methods, although it has limitations in handling camera motion and multiple object removals.
![Related Work
Hsu et al. [1] Proposed approach to locate forged regions in an inpainted video
using correlation of noise residue.
Zhang et al. [2] Performs inpainting forgery detection based on ghost shadow
artifacts.
Das et al.[3] Proposed a blind detection method based on zero-connectivity feature
and fuzzy membership function to detect video inpainting forgery.
Lin et al. [4] Proposed spatio-temporal coherance based approach for video
inpainting detection and localization.
9](https://image.slidesharecdn.com/shobhitamtechthesispresentation-150809125735-lva1-app6892/75/Video-Inpainting-detection-using-inconsistencies-in-optical-Flow-9-2048.jpg)
![Targeted Inpainting Techniques
14
This algorithm performs on two variants of Temporal Copy Paste (TCP) inpainting.
They are as follows :
Conventional TCP – one of the first and most popular inpainting techniques
proposed by Patwardhan et al [5] in 2007. Handles relatively simple motion
types in videos for inpainting.
Complex TCP – one of the state-of-the-art inpainting techniques proposed by
Alasdair et al [6] in 2014. Handles relatively complex motions in videos to
performing inpainting.](https://image.slidesharecdn.com/shobhitamtechthesispresentation-150809125735-lva1-app6892/75/Video-Inpainting-detection-using-inconsistencies-in-optical-Flow-14-2048.jpg)
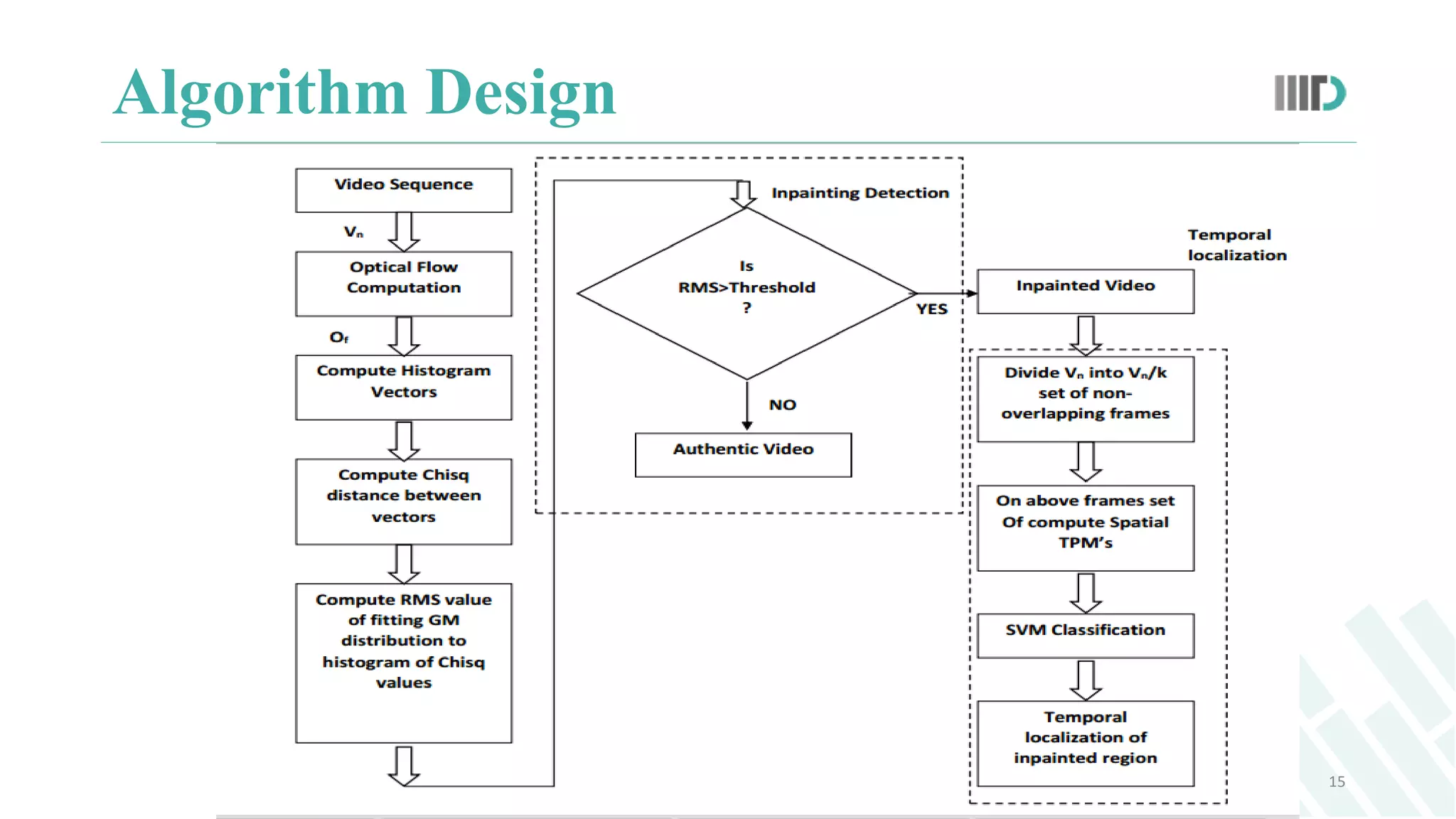
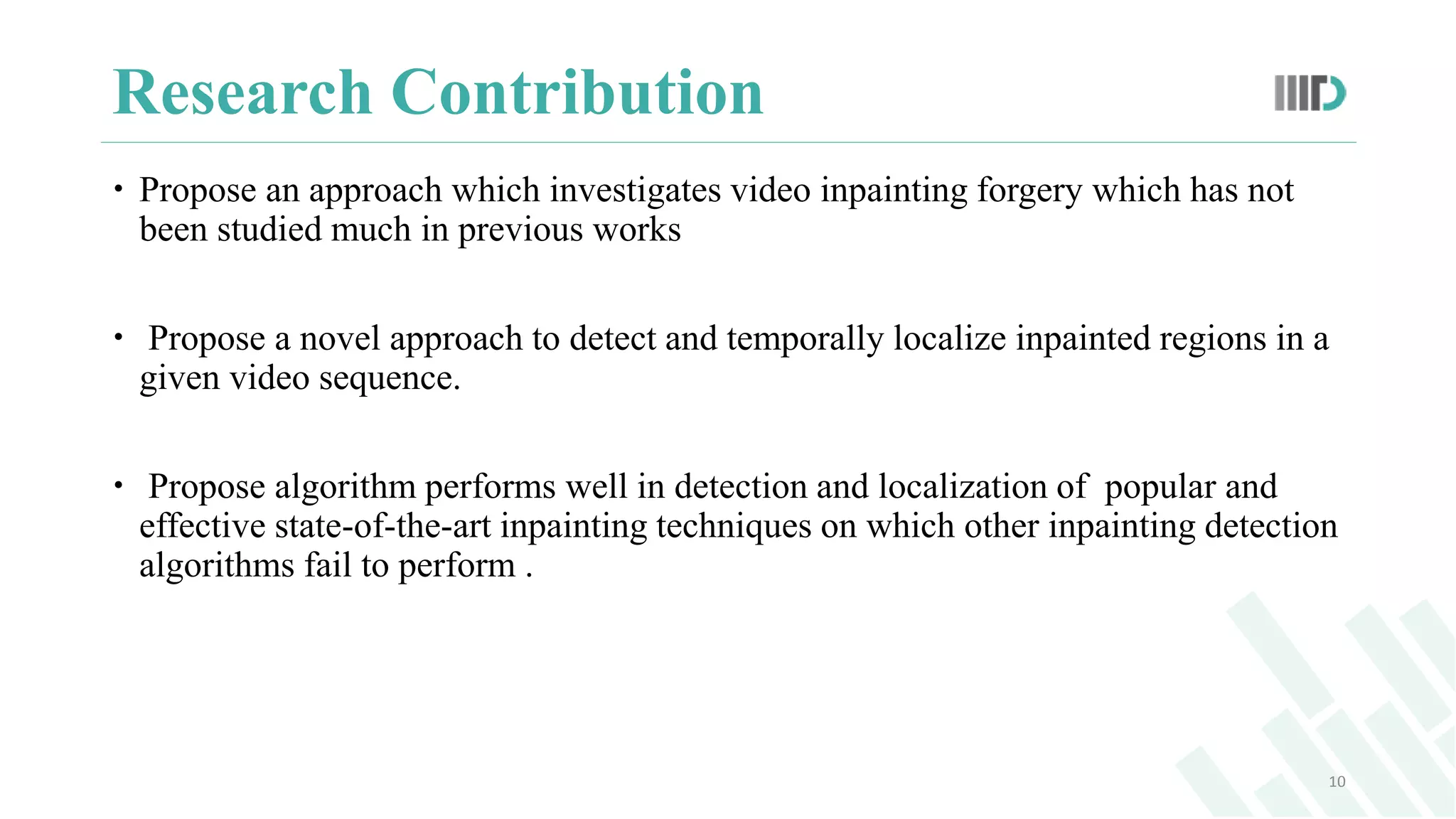
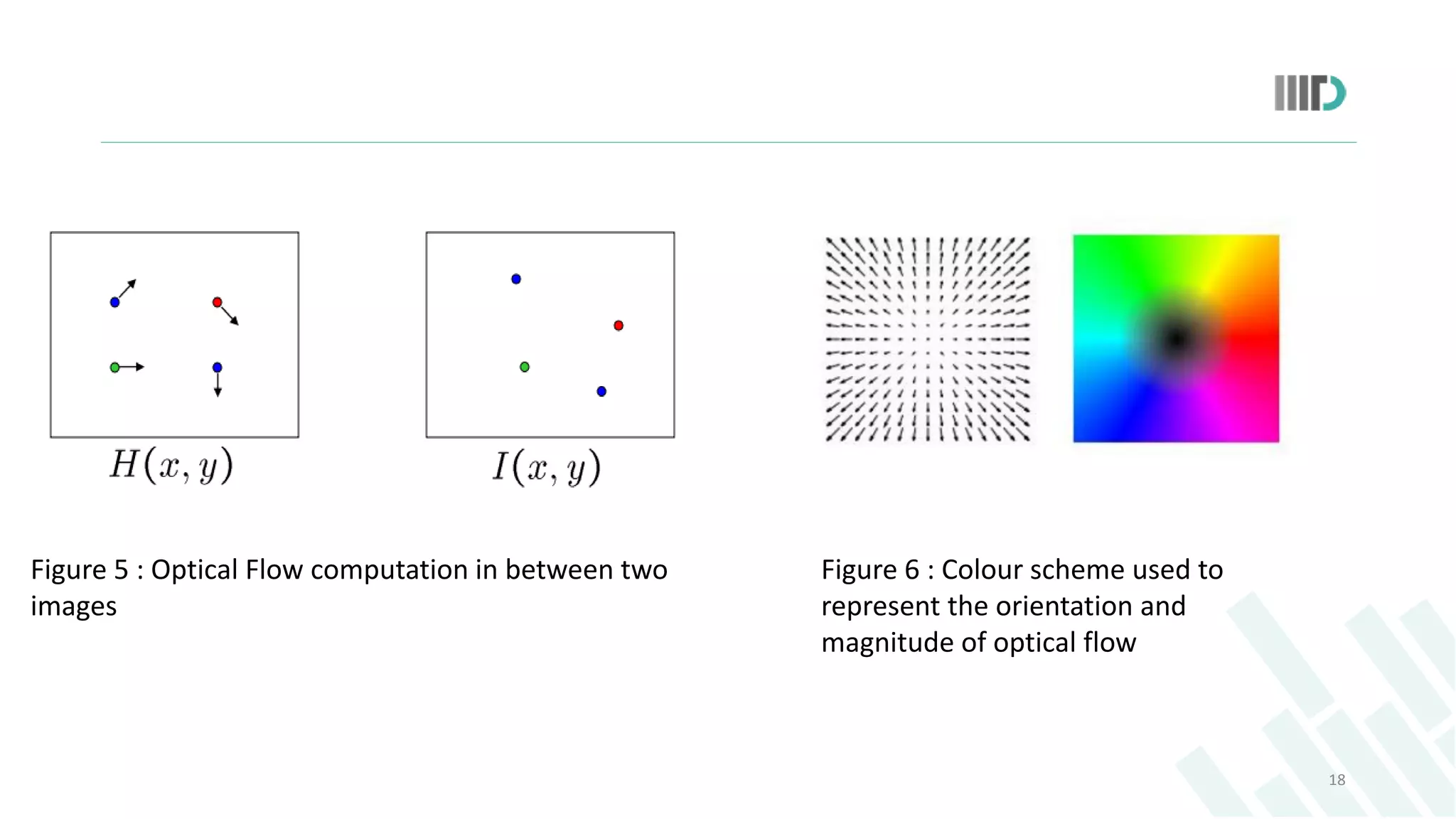
![Optical Flow
16
Optical Flow (Of) characterizes
the motion of every pixel in one
image to its corresponding
location in next image[7].
Performs motion estimation in
between video frames .
It is best applied to video frames
as these are sequence of time
ordered images.
Figure 3 : (a,b) mouth regions of two consecutive
images of a person speaking . (c) Flow field
estimated using optical flow.](https://image.slidesharecdn.com/shobhitamtechthesispresentation-150809125735-lva1-app6892/75/Video-Inpainting-detection-using-inconsistencies-in-optical-Flow-16-2048.jpg)
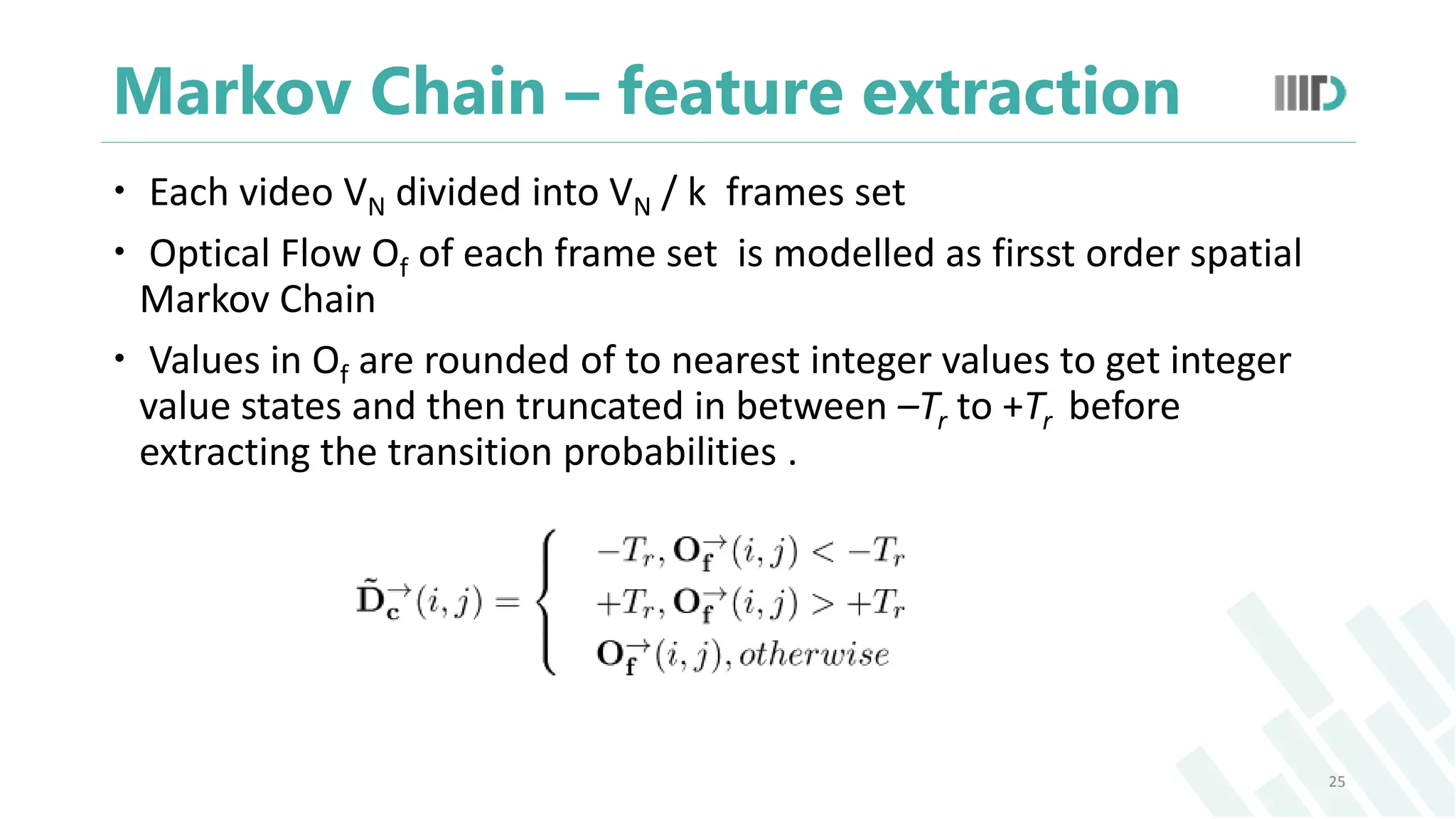
![ Number of states to model a markov chain = (2Tr+1)
For each matrix, number of Transition Probabilities = (2Tr+1) * (2Tr+1)
TPM is constructed as :
where, u,v ϵ [-Tr , Tr] , and u,v ϵ Z.
Similarly, probabilities can be estimated for other directions.
Perform SVM classification on above obtained TPMs.
26](https://image.slidesharecdn.com/shobhitamtechthesispresentation-150809125735-lva1-app6892/75/Video-Inpainting-detection-using-inconsistencies-in-optical-Flow-26-2048.jpg)
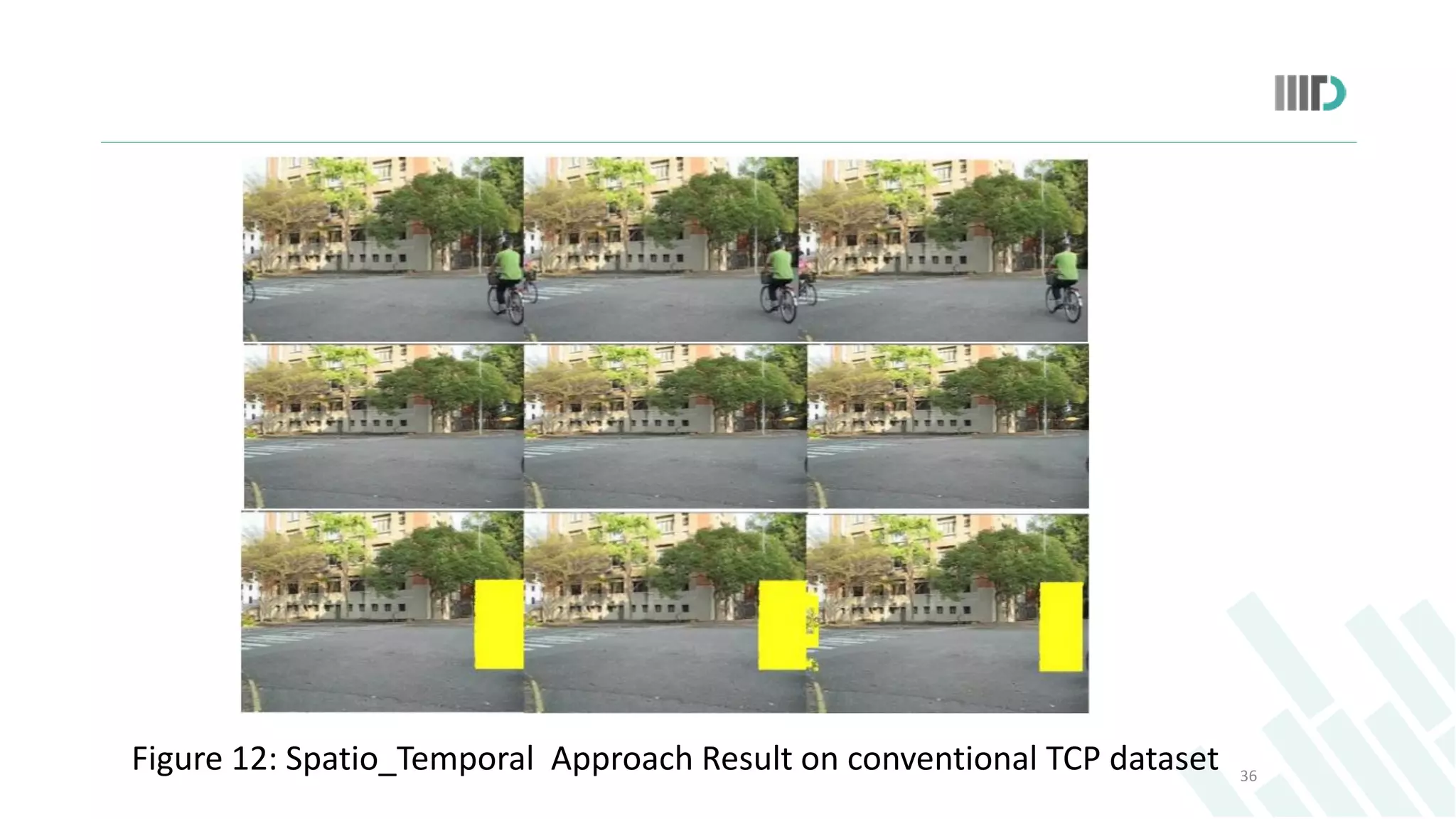
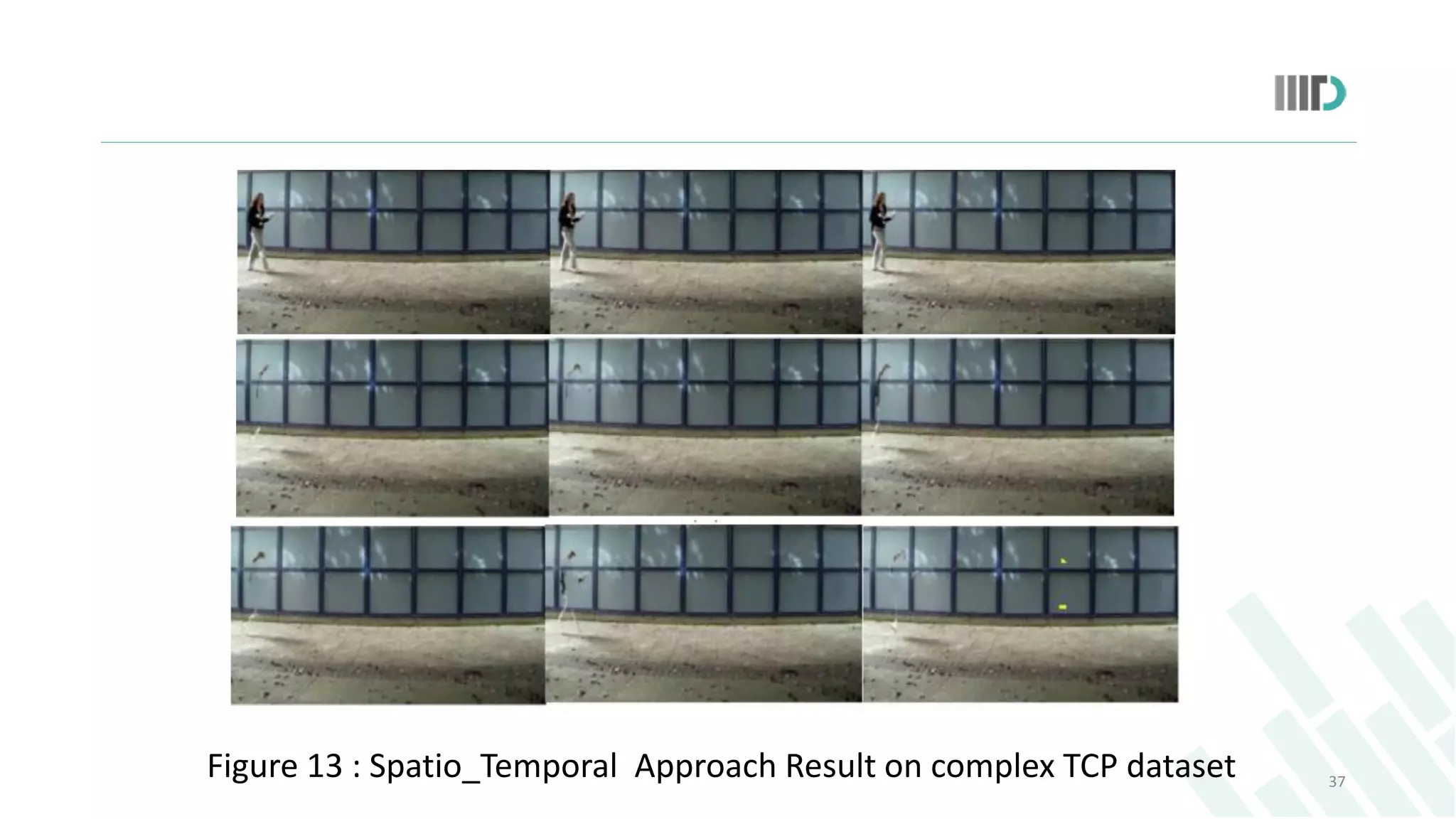
![Comparison
Proposed approach is compared with spatio-temporal coherence
based technique proposed by Lin et al [4]for inpainting detection and
localization .
Spatio- Temporal coherence based approach fails to perform on
complex TCP inpainting dataset.
35](https://image.slidesharecdn.com/shobhitamtechthesispresentation-150809125735-lva1-app6892/75/Video-Inpainting-detection-using-inconsistencies-in-optical-Flow-35-2048.jpg)