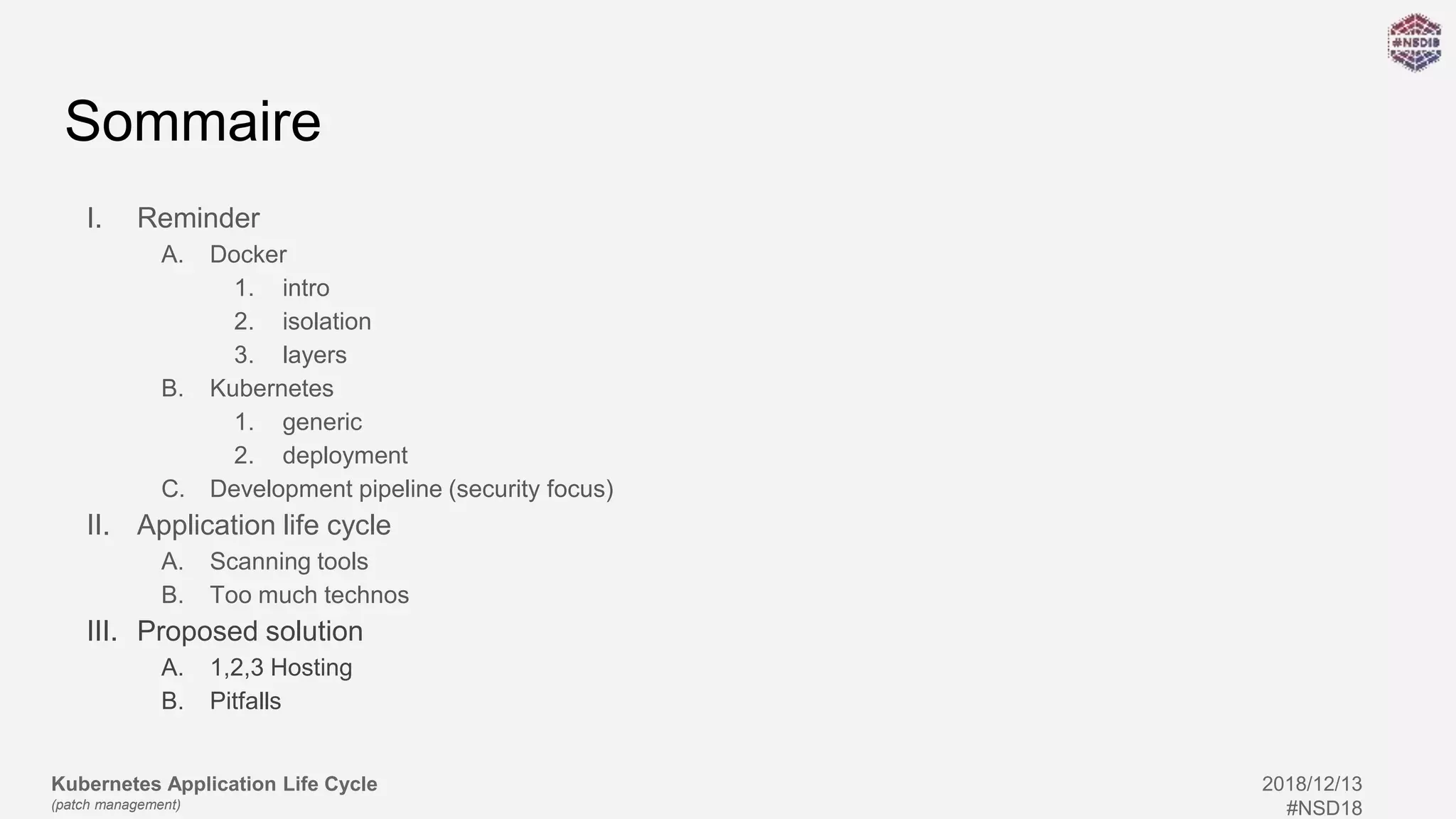
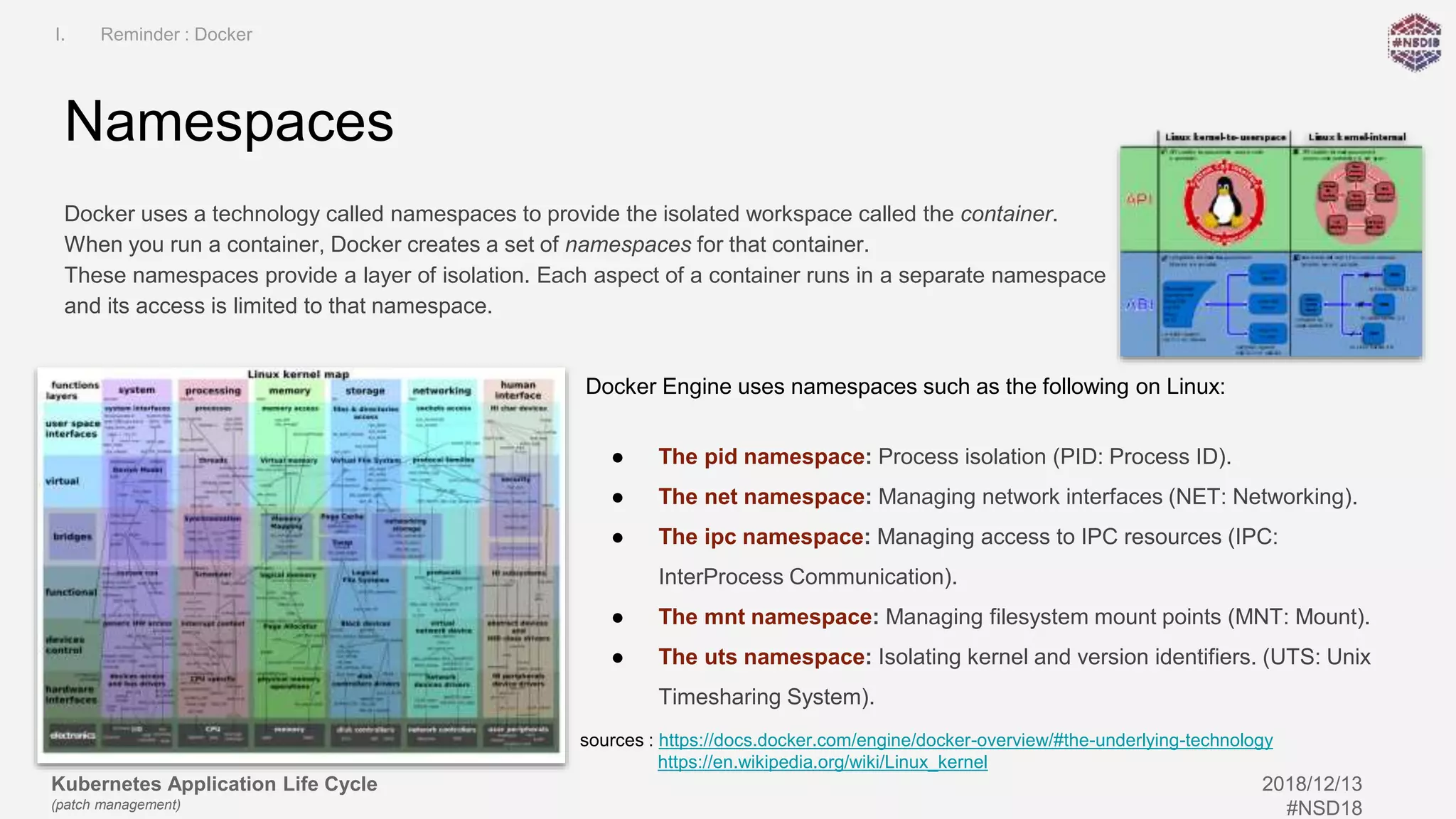
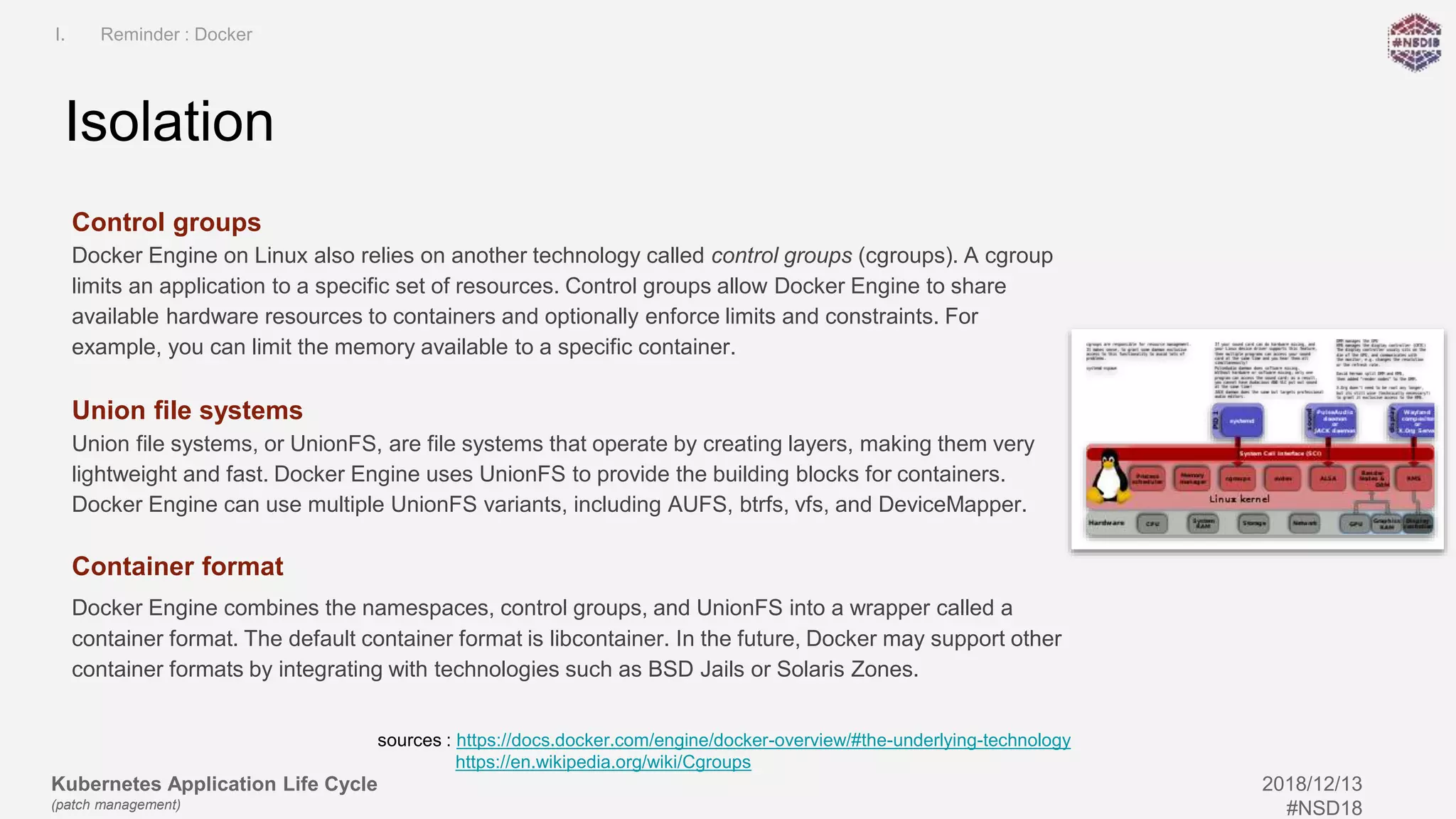
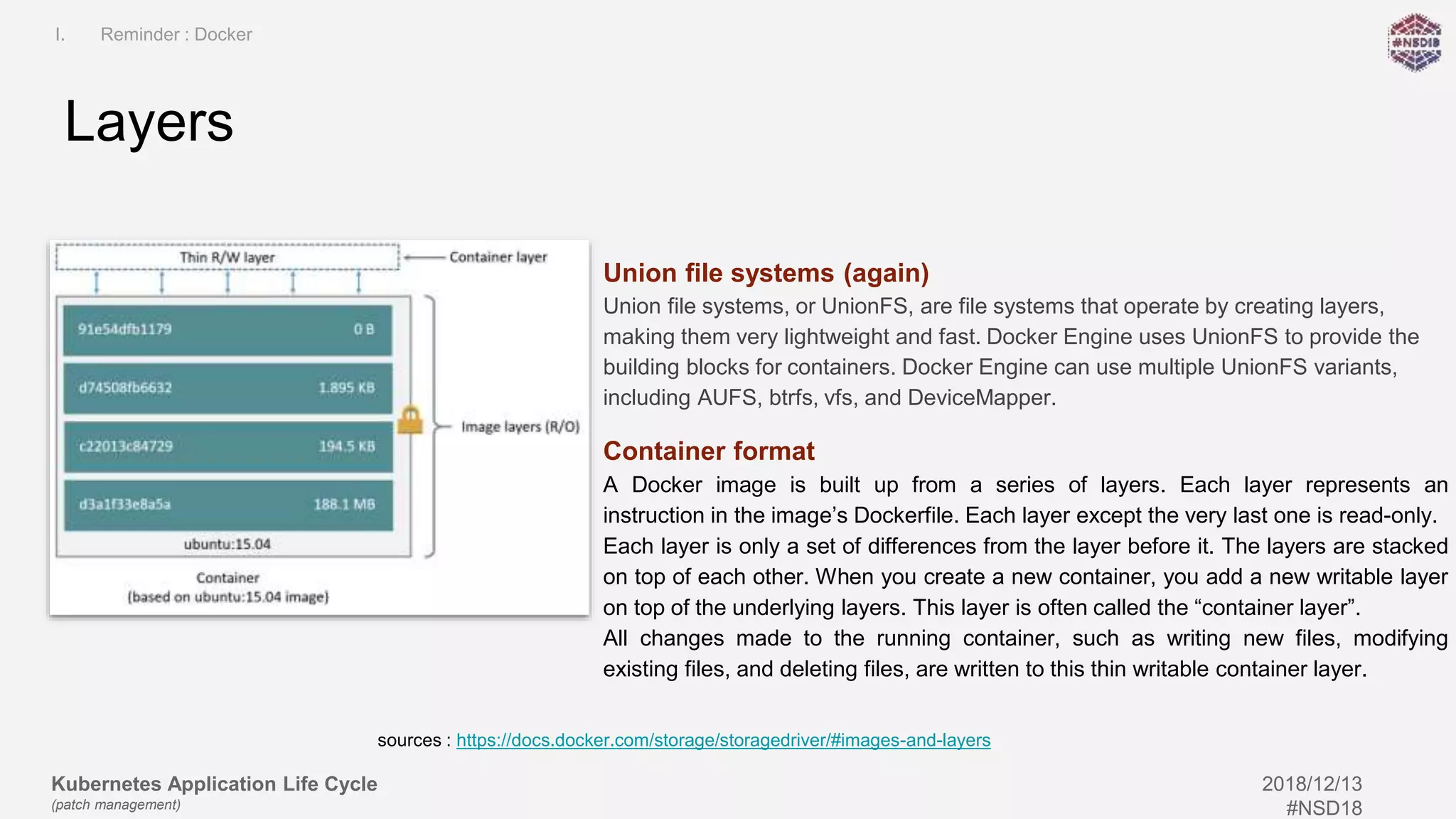
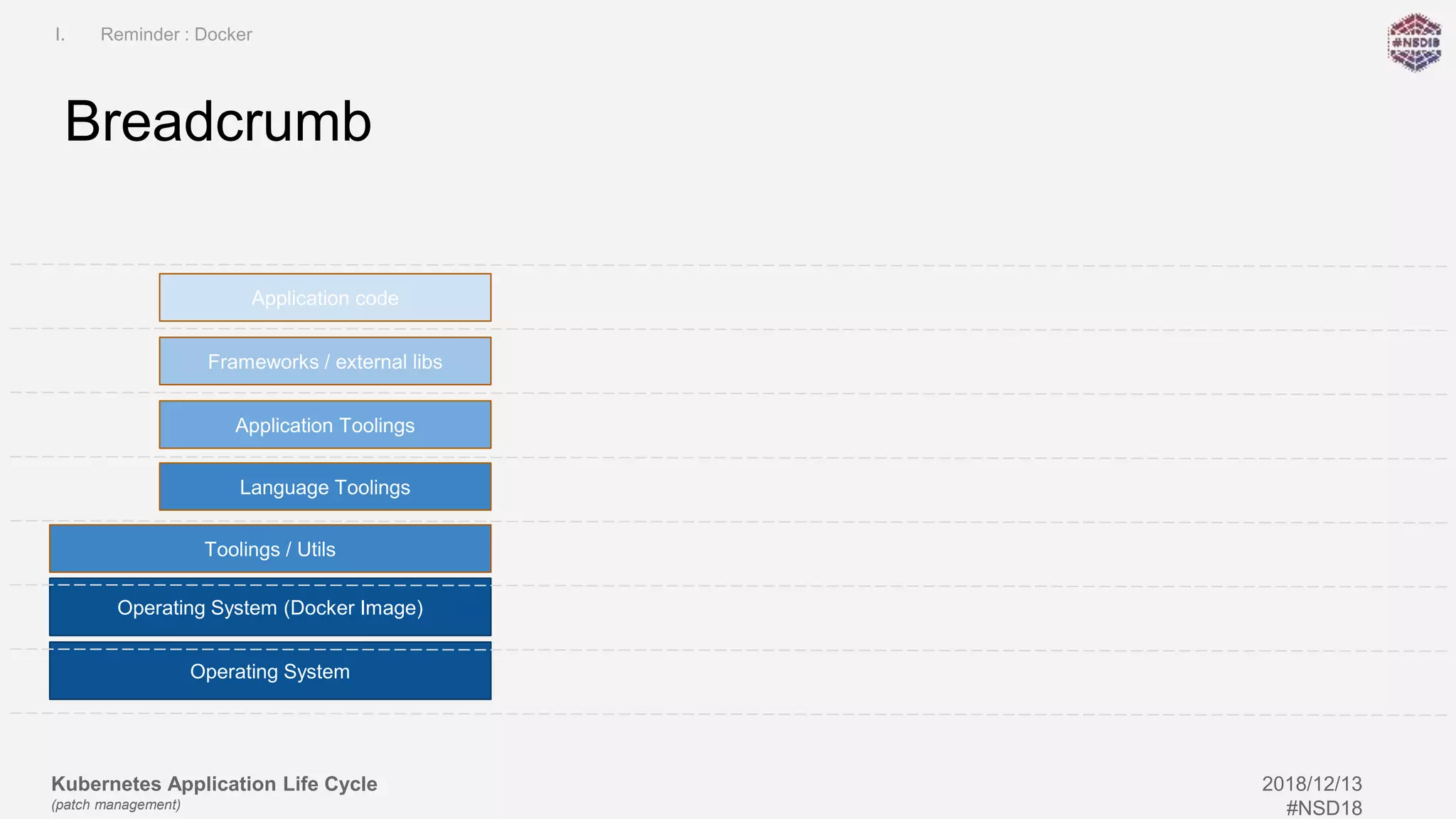
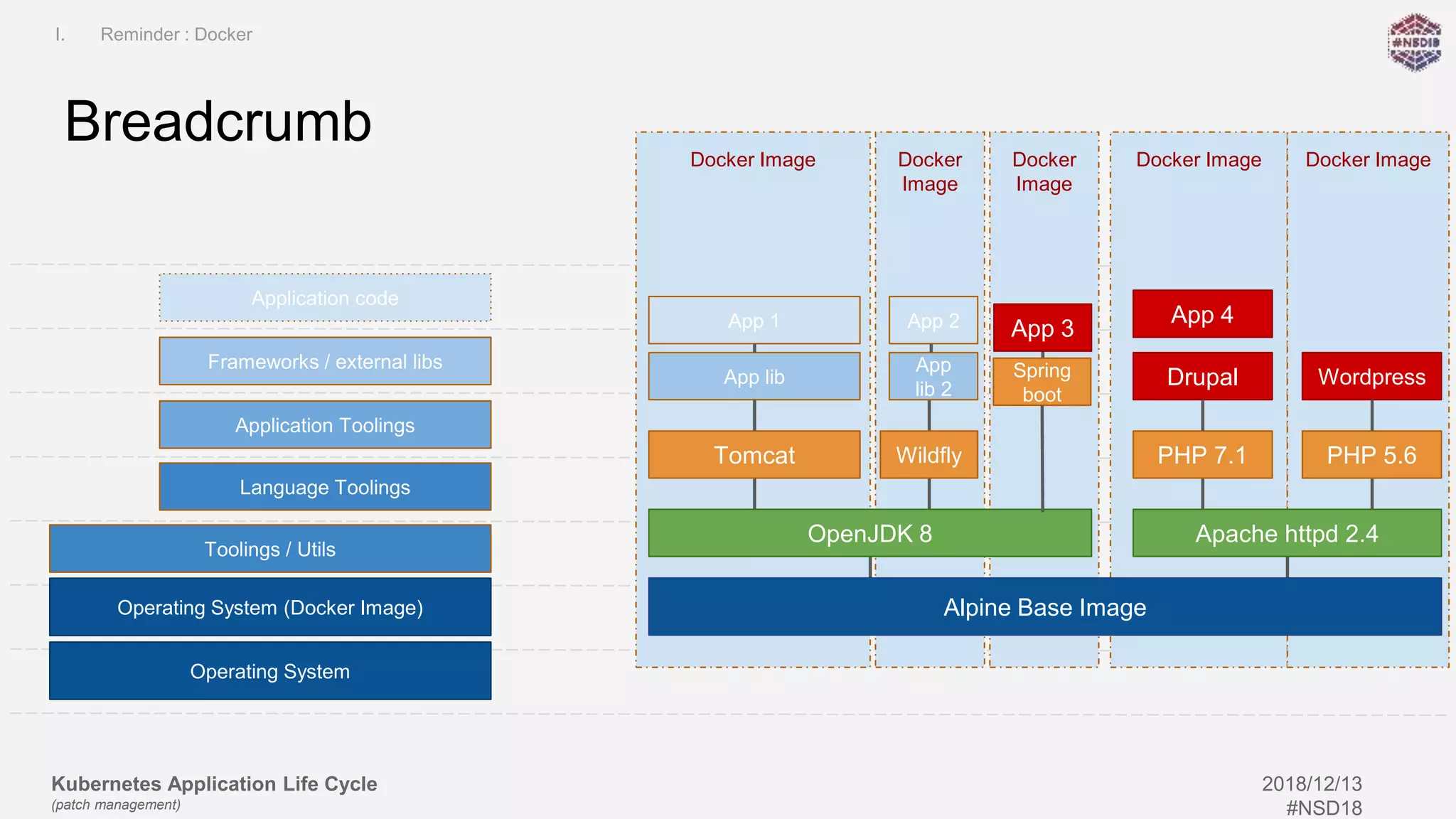
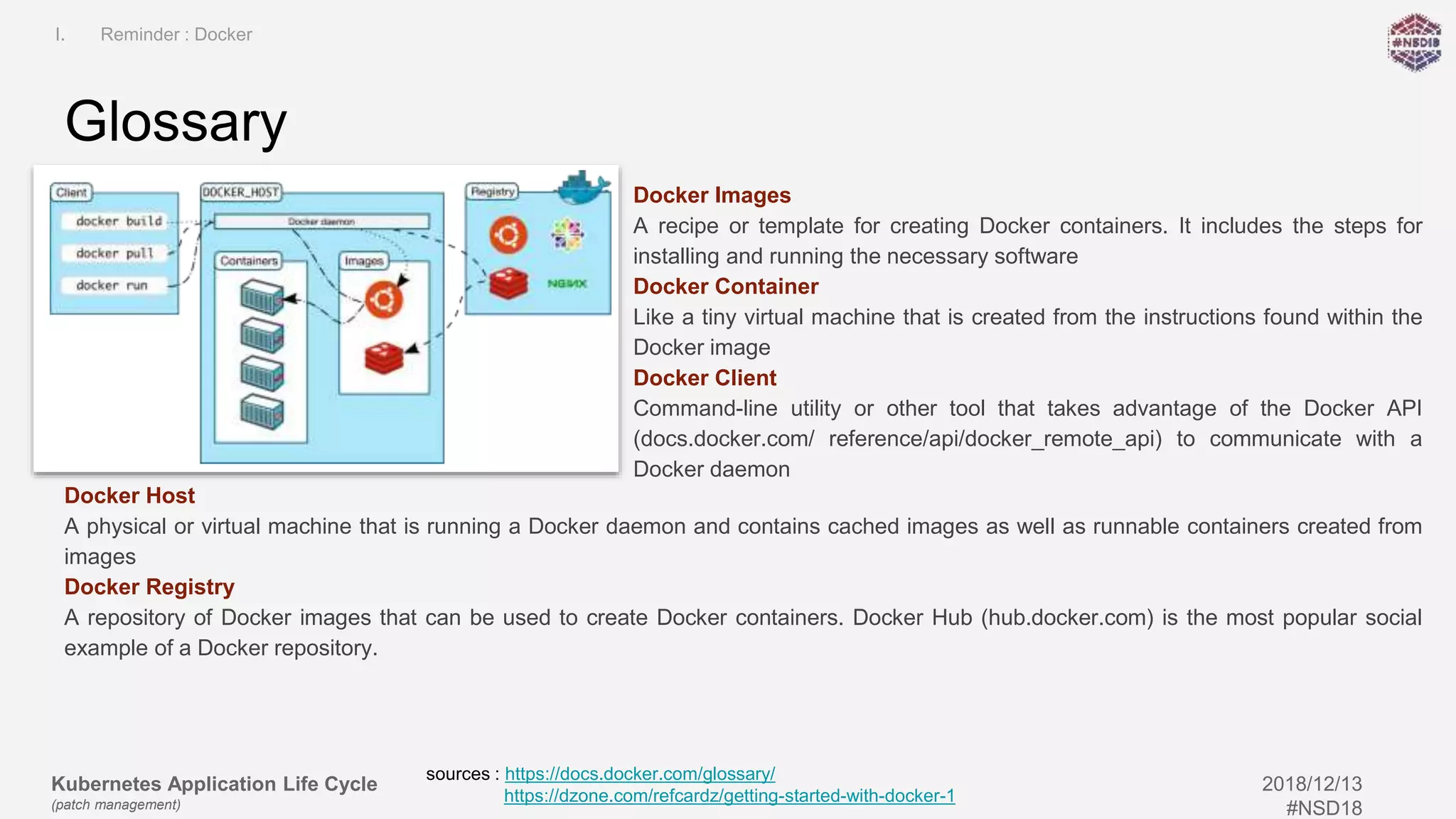
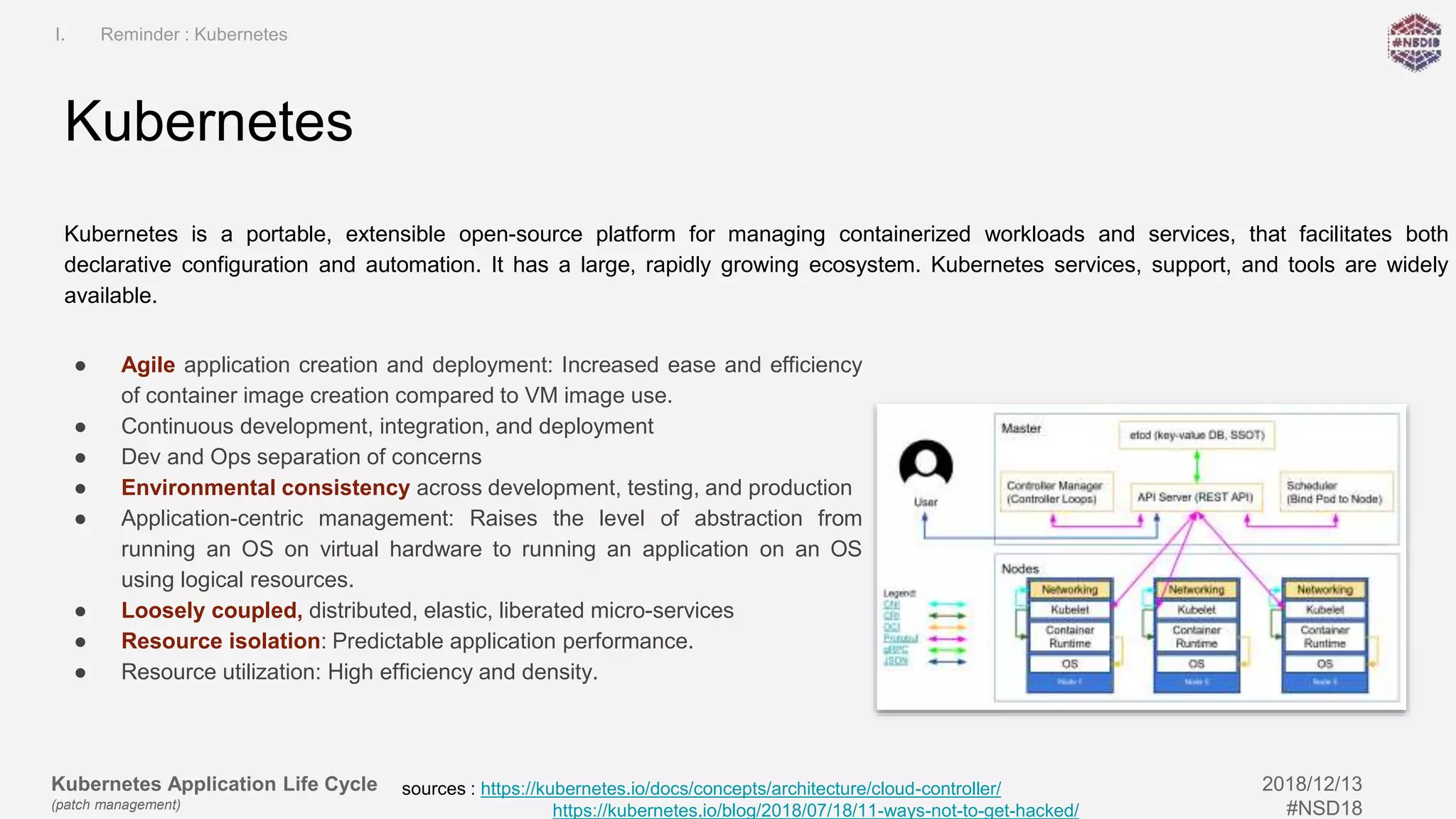
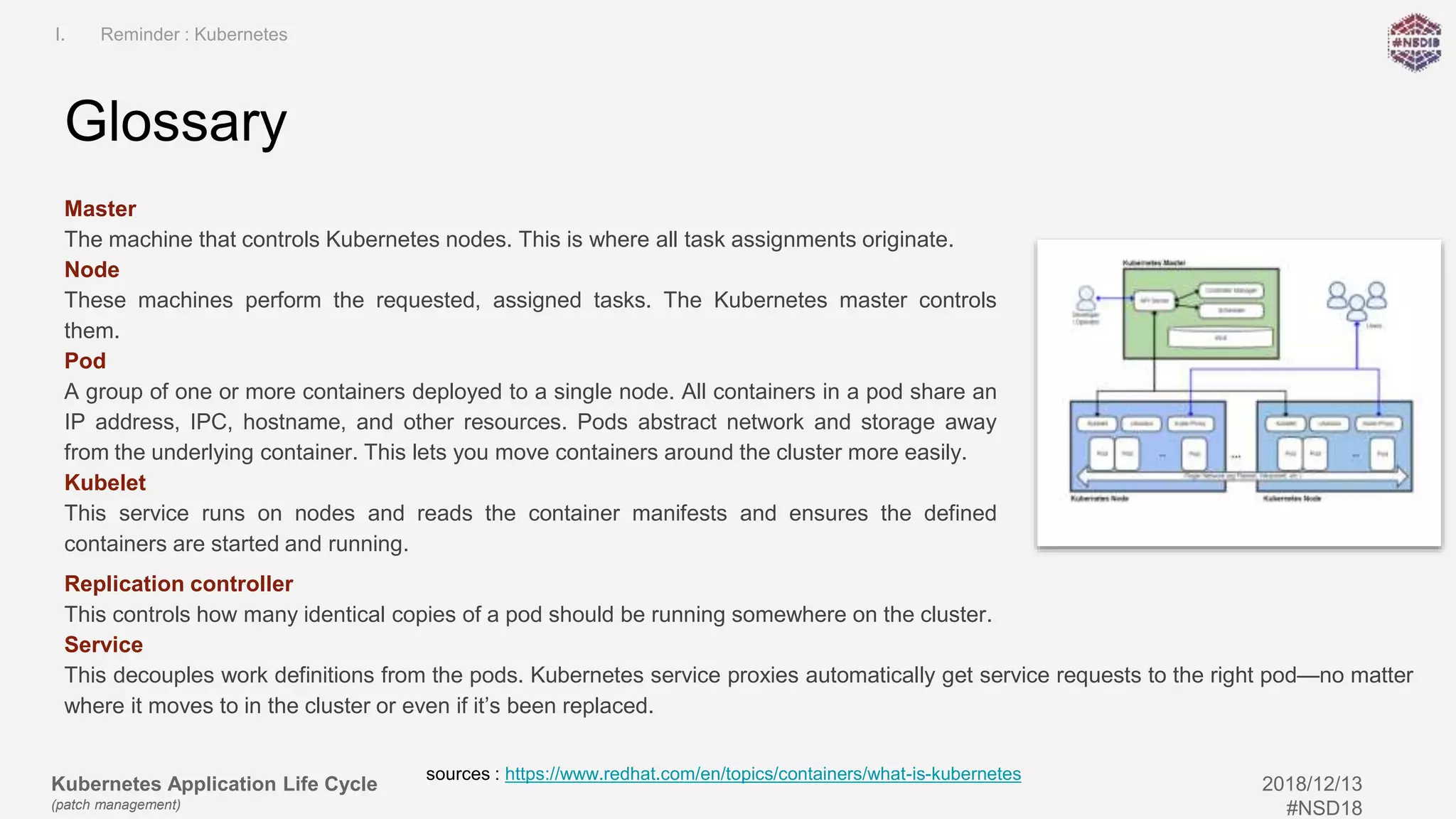
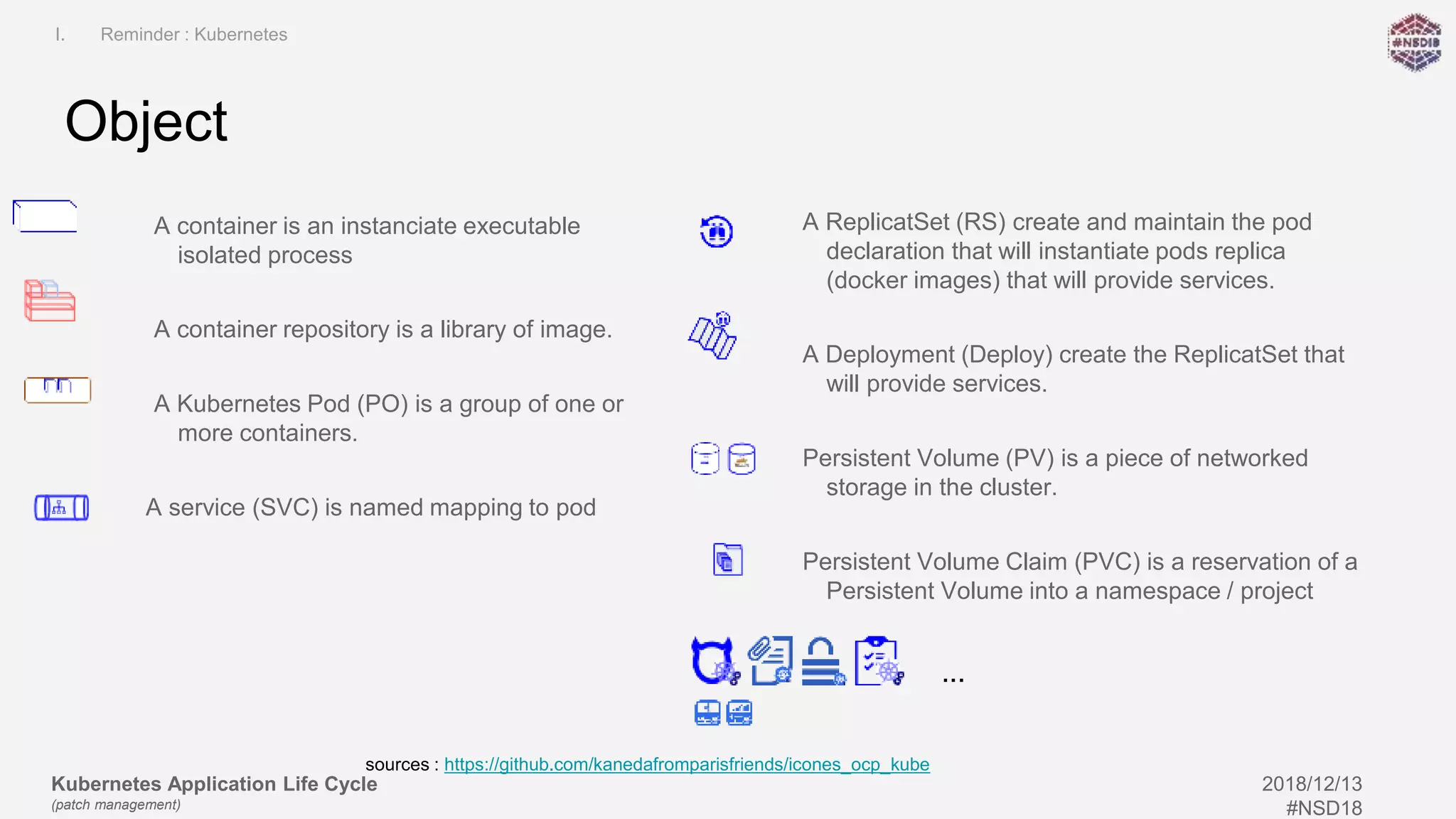
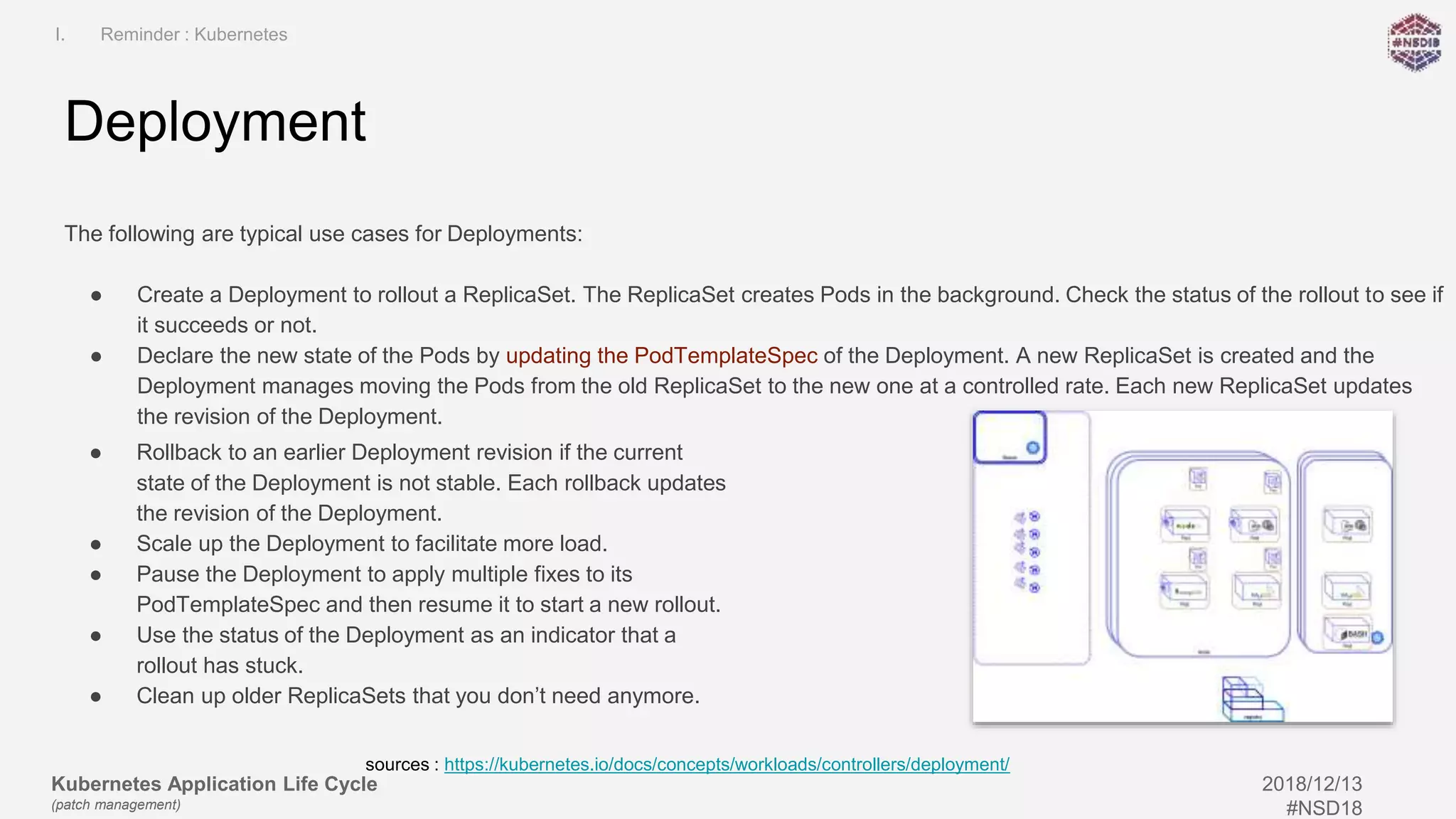
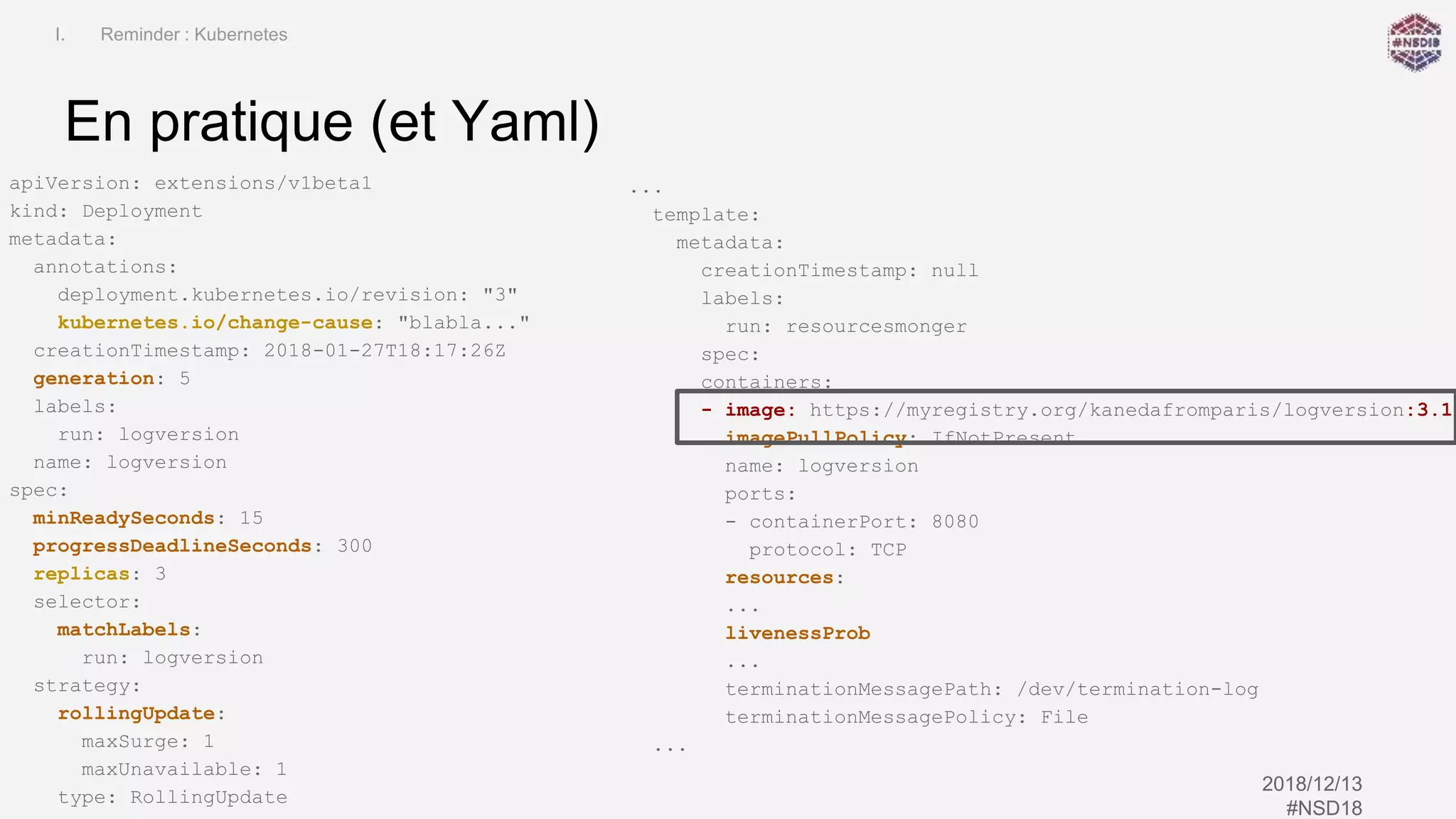
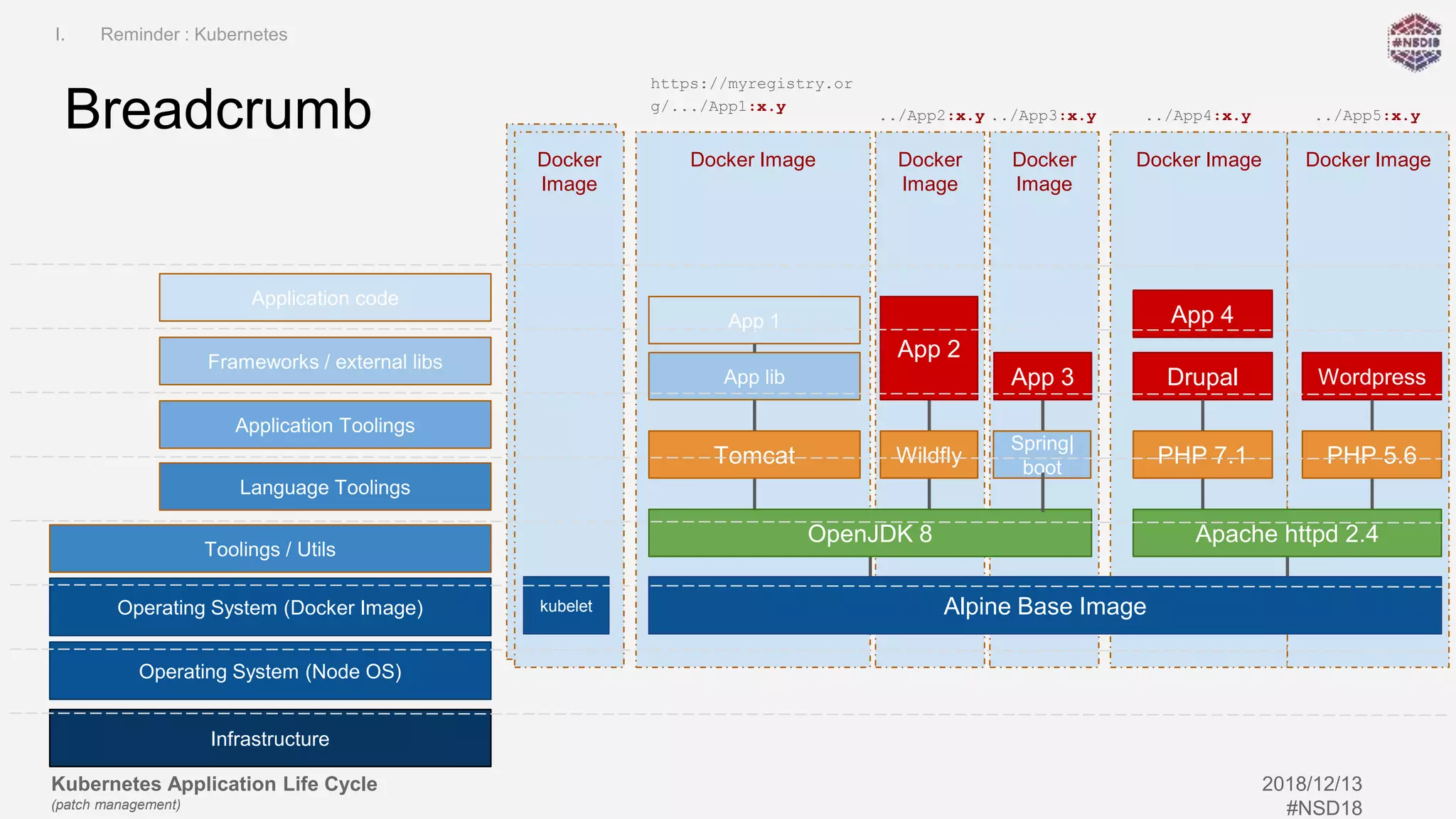
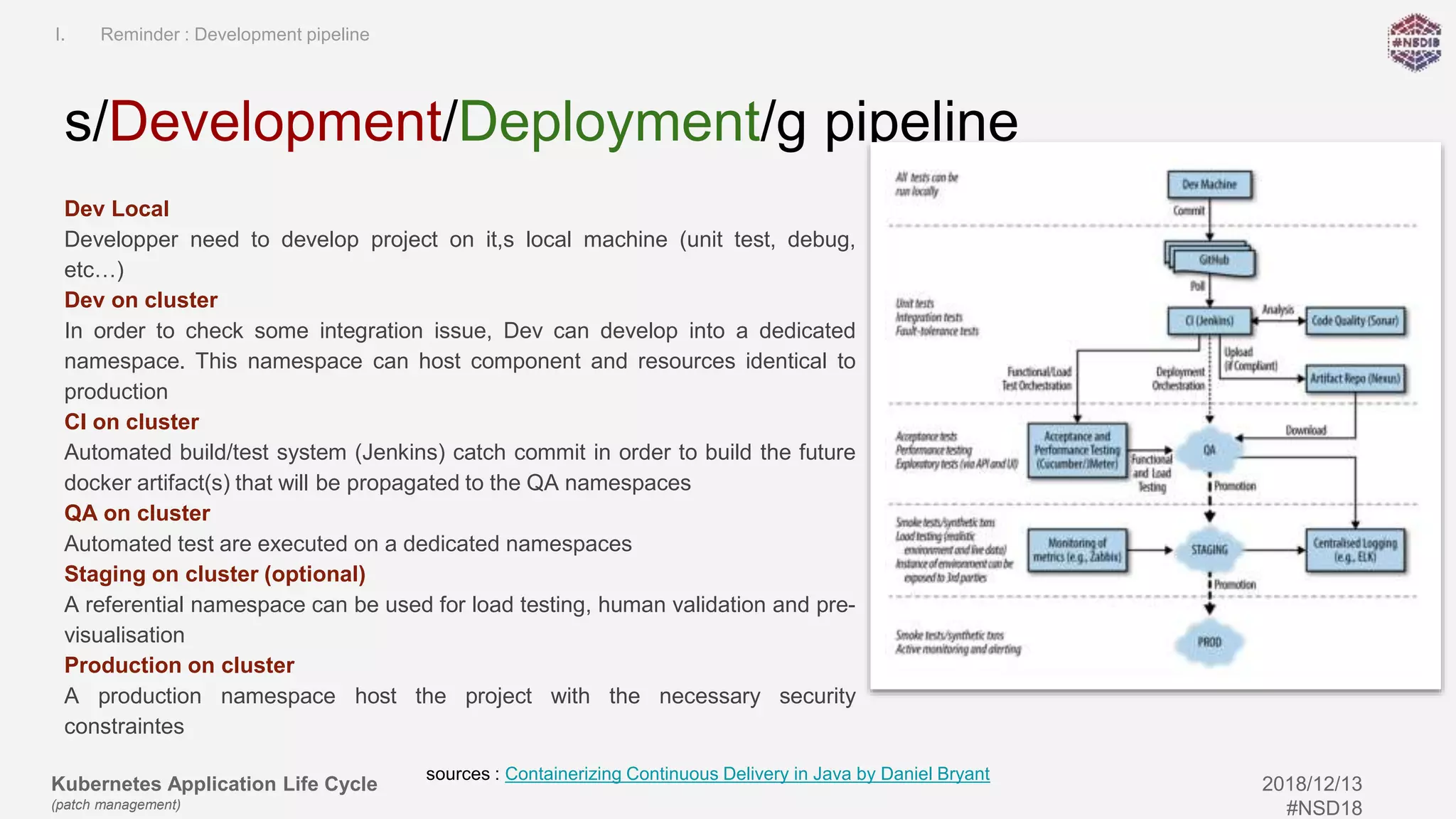
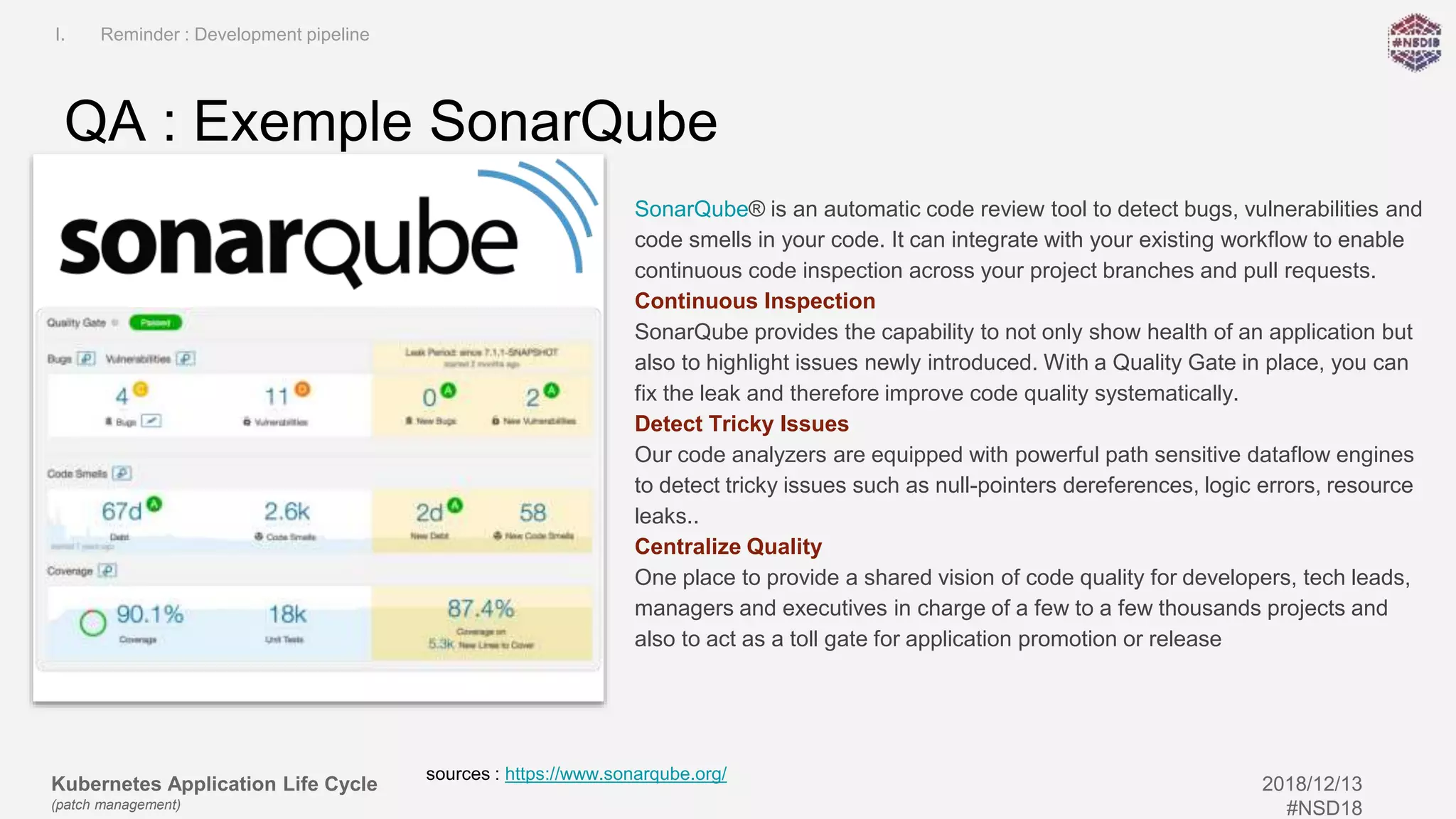
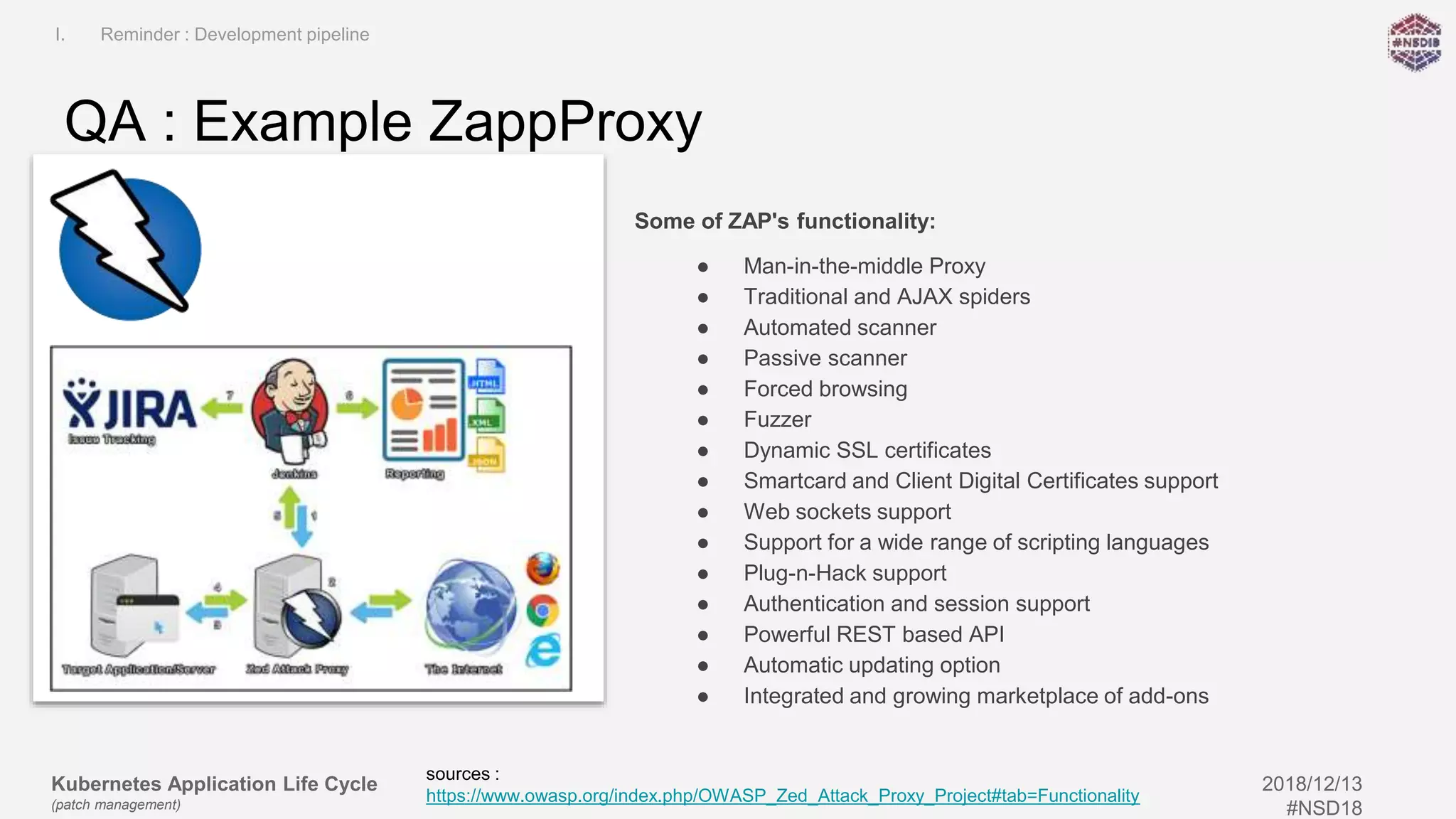
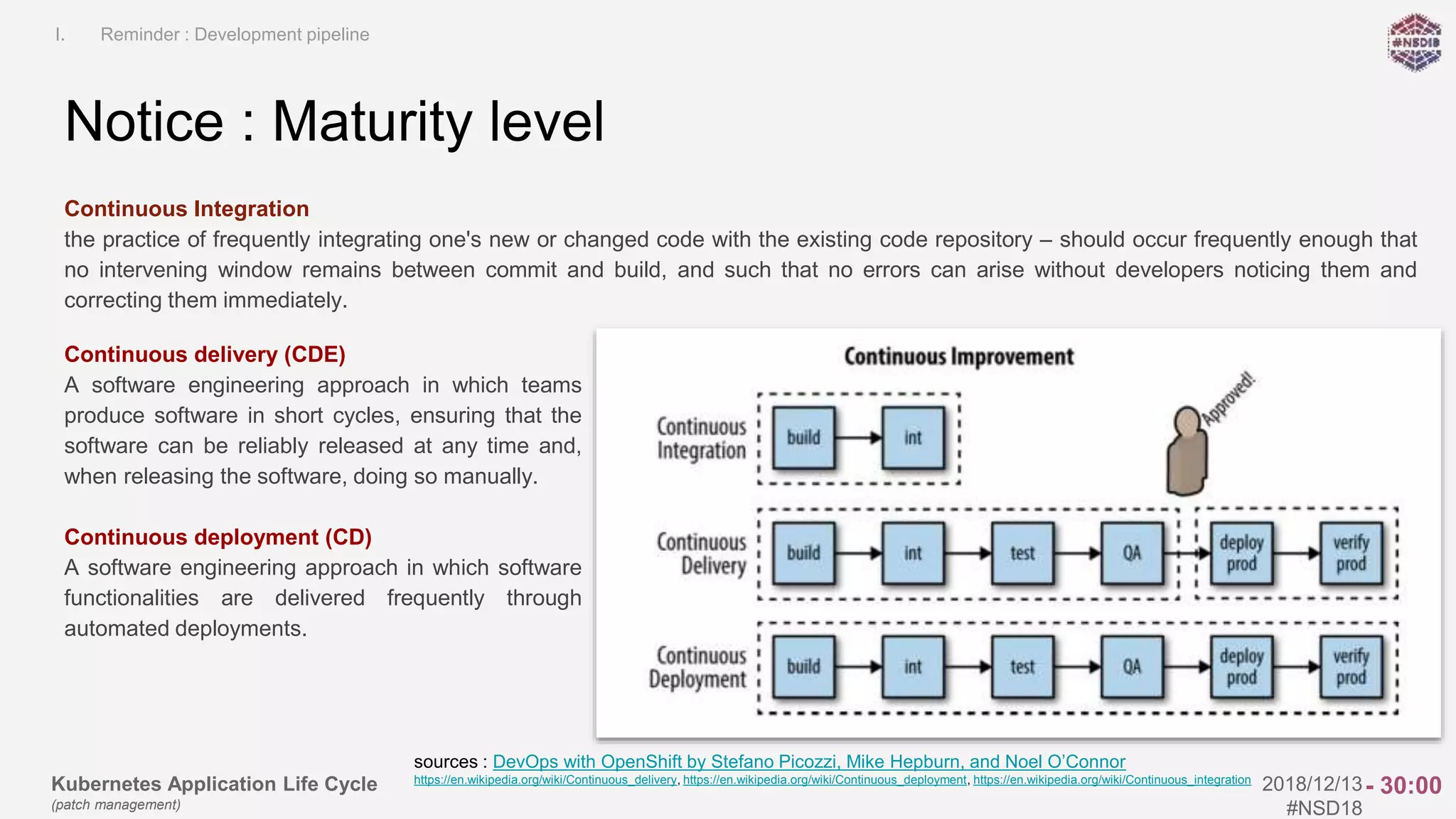
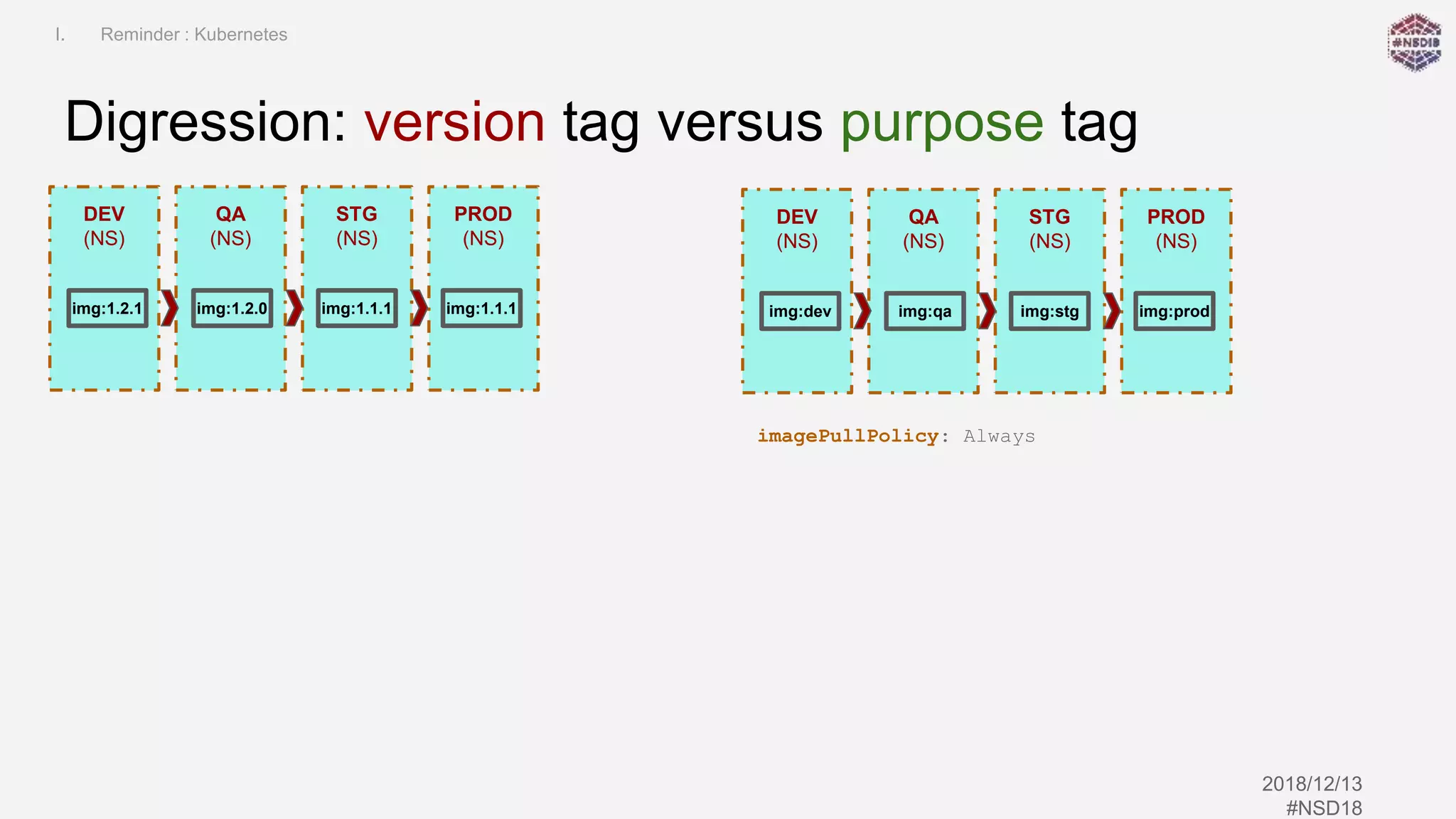
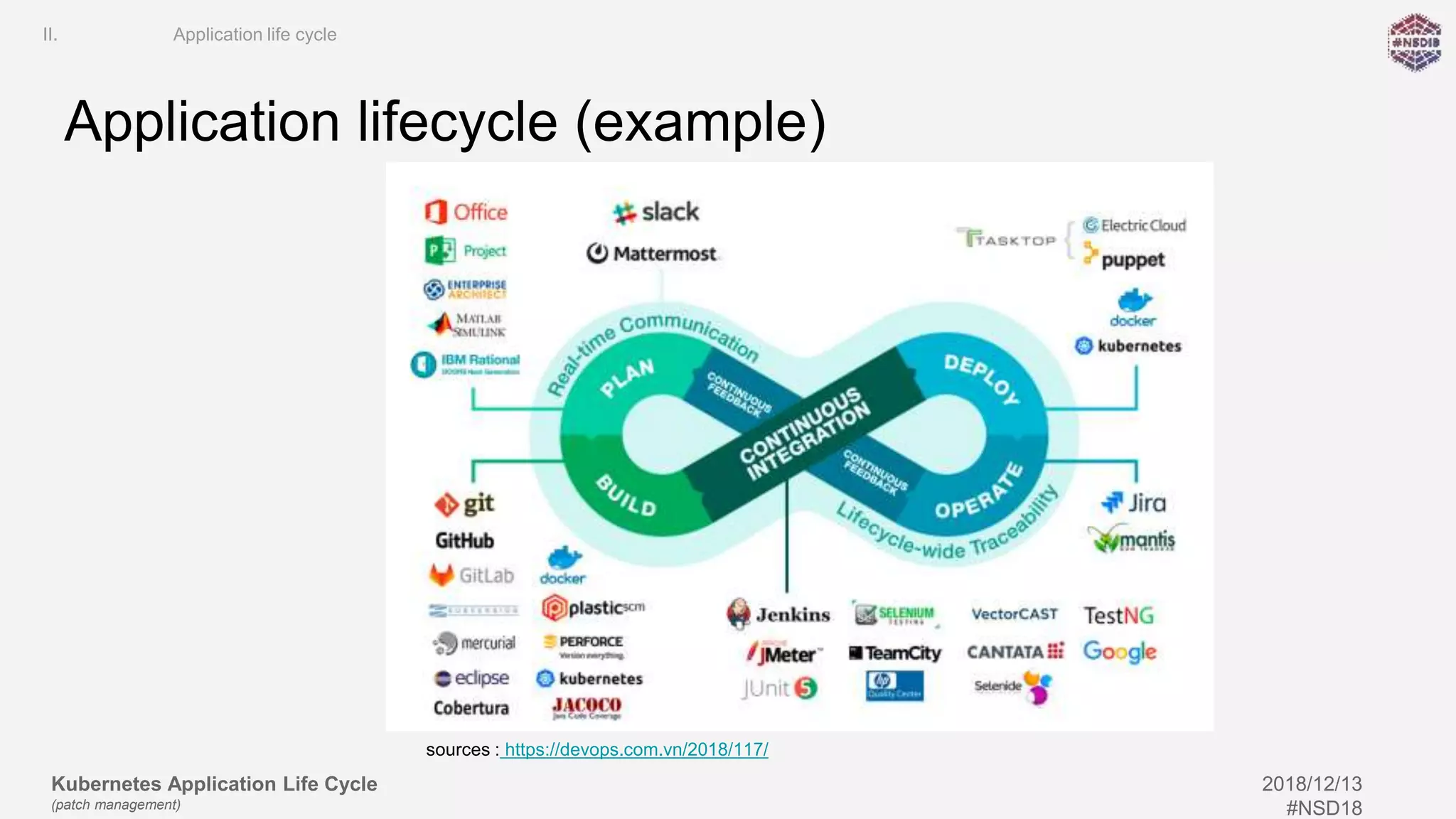
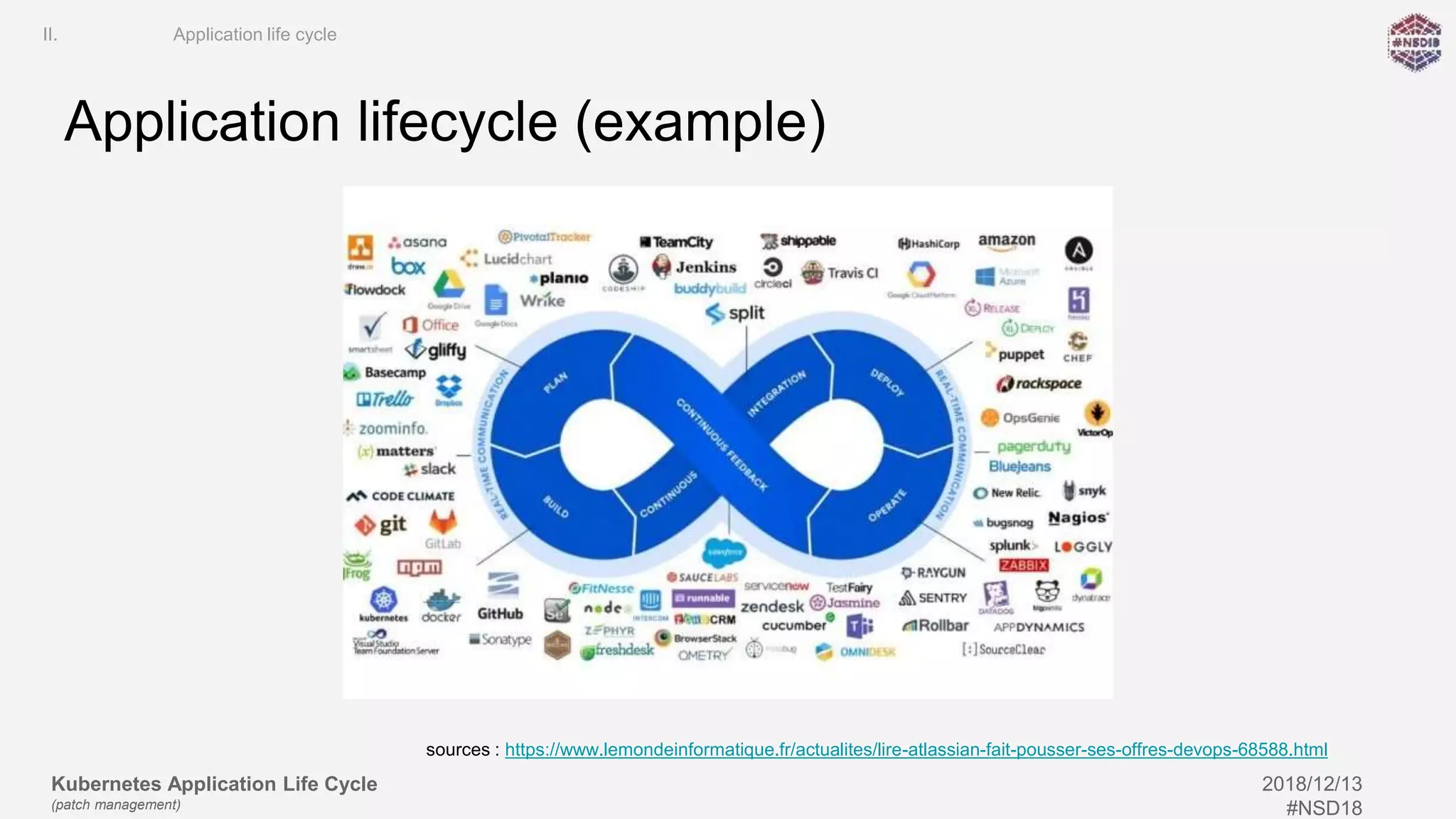
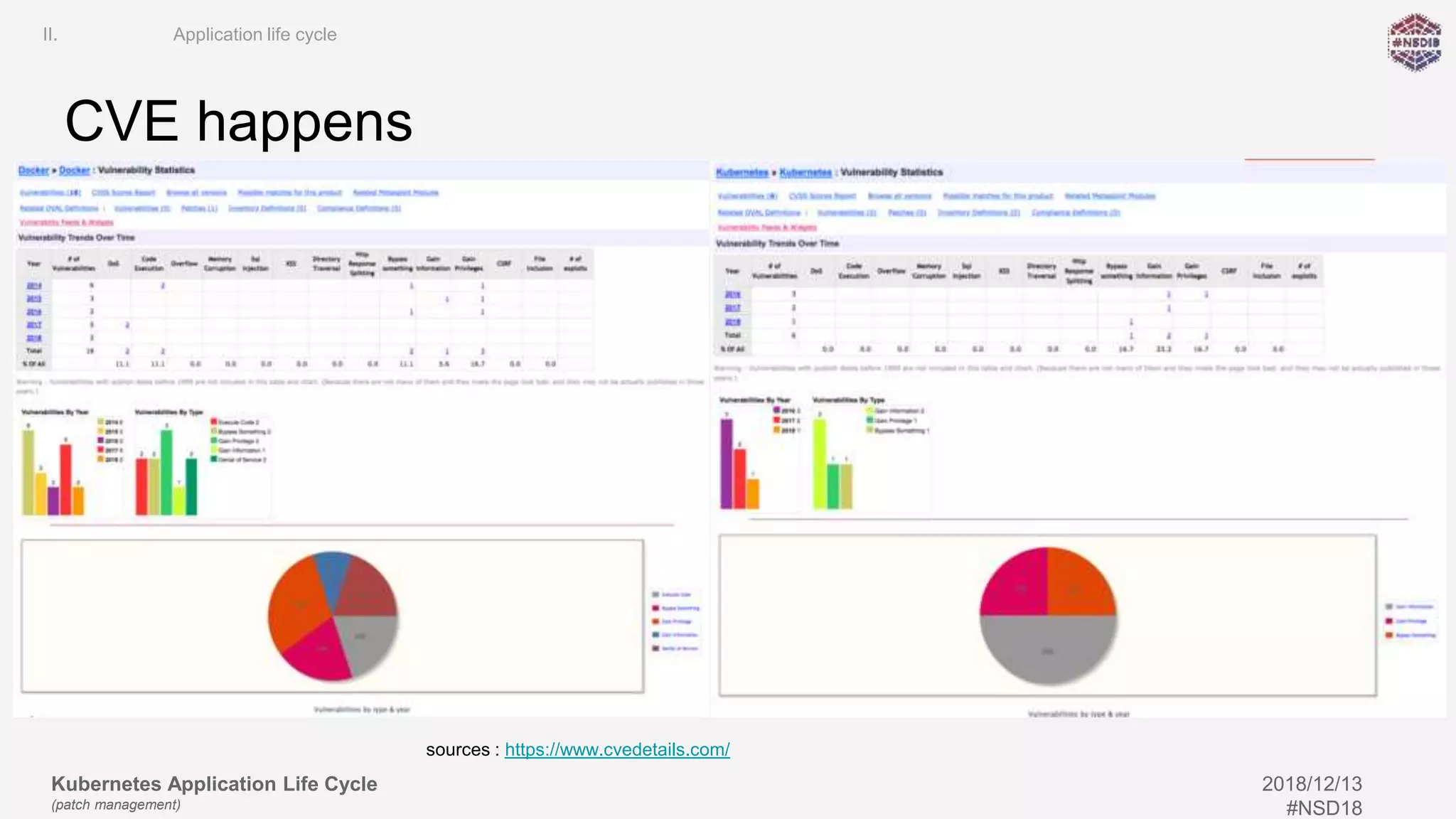
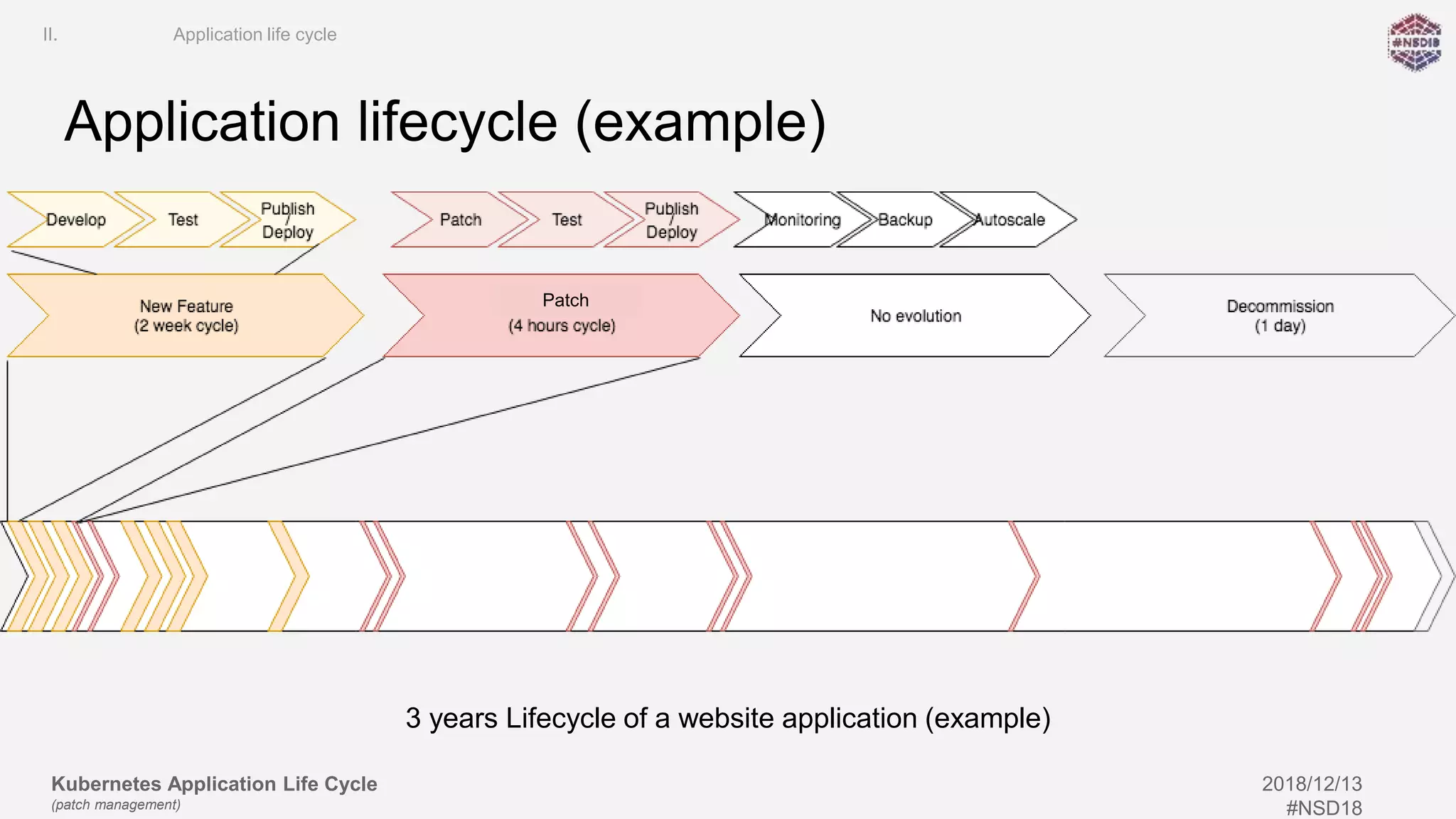
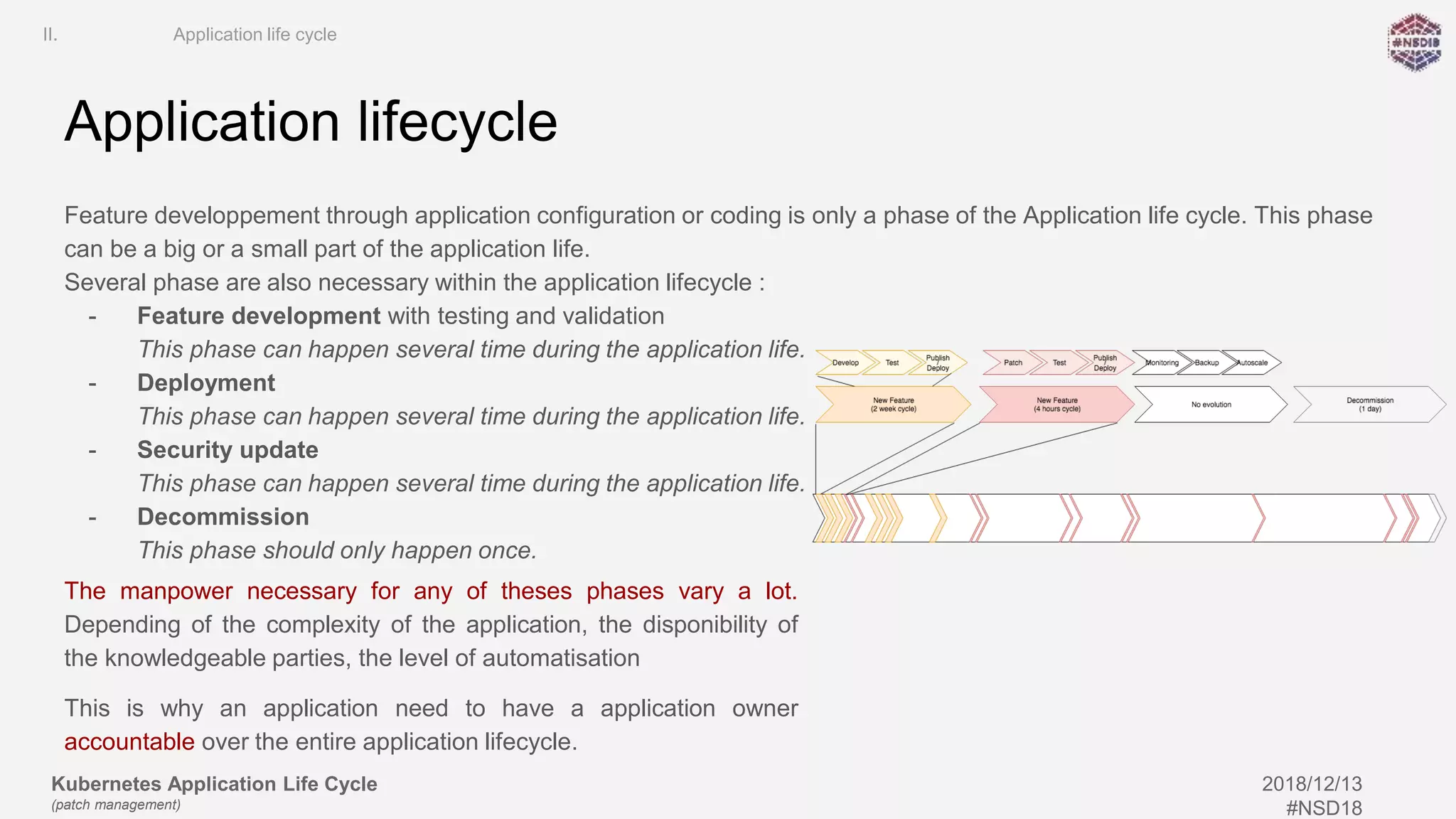
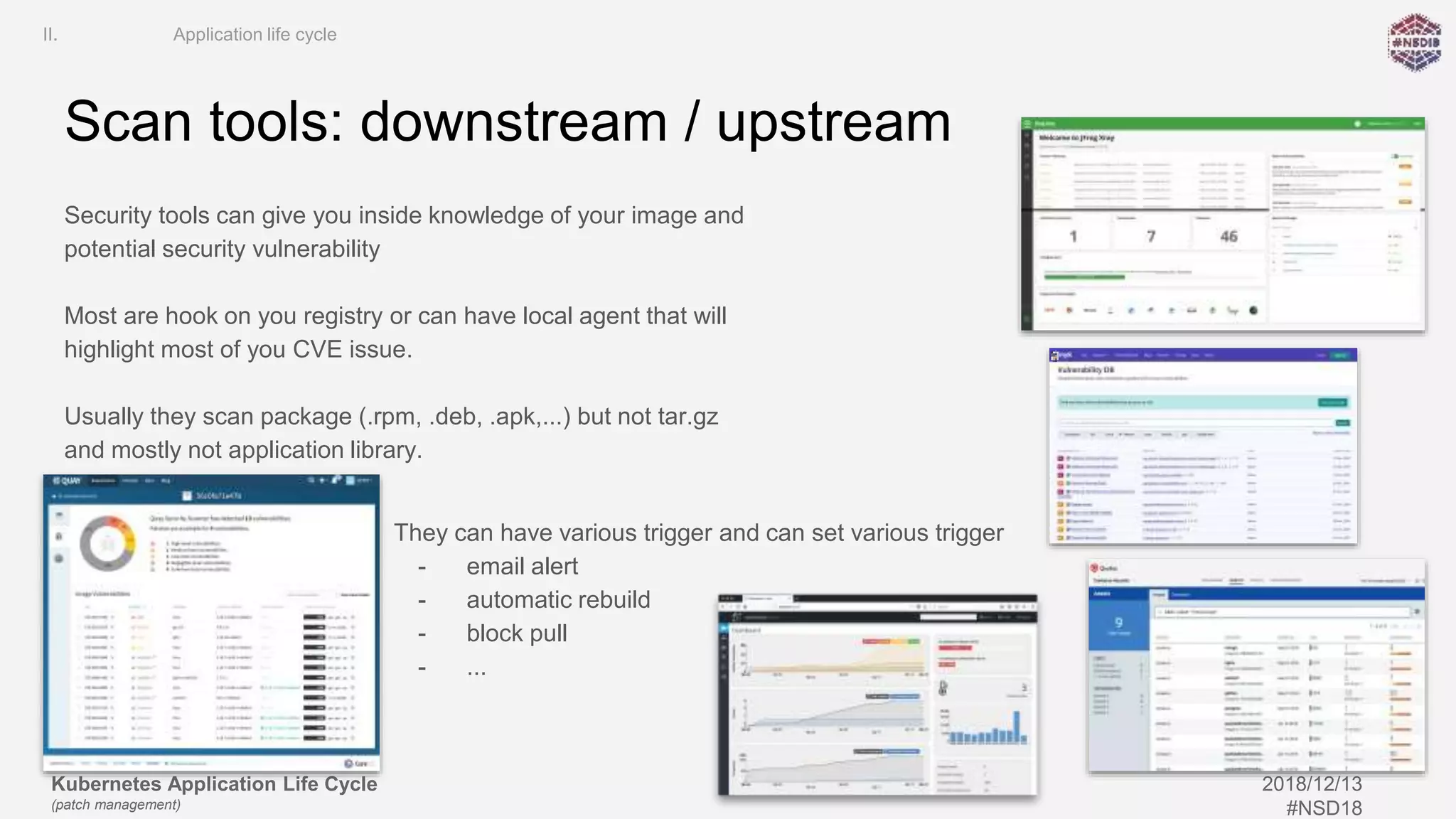
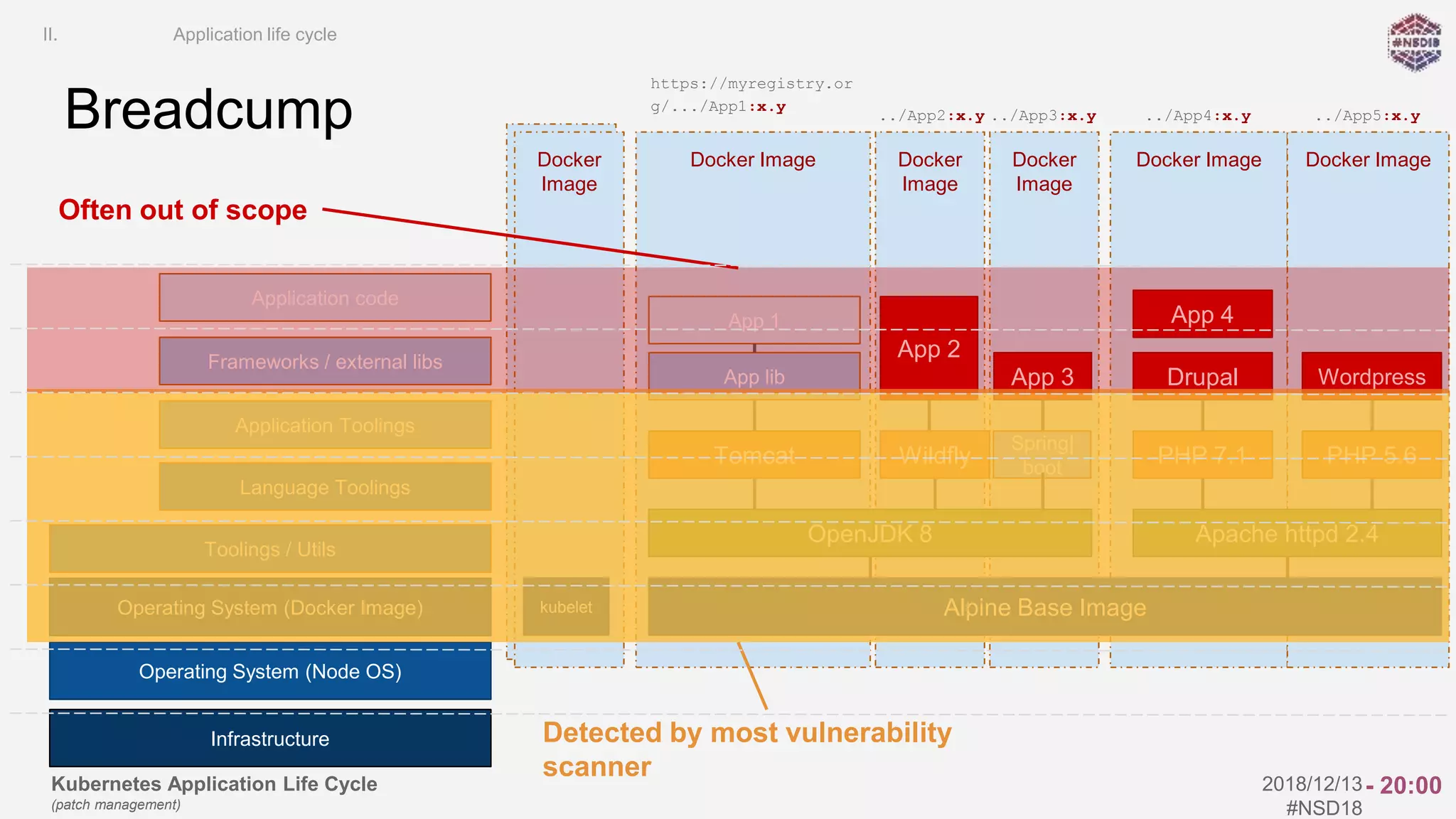
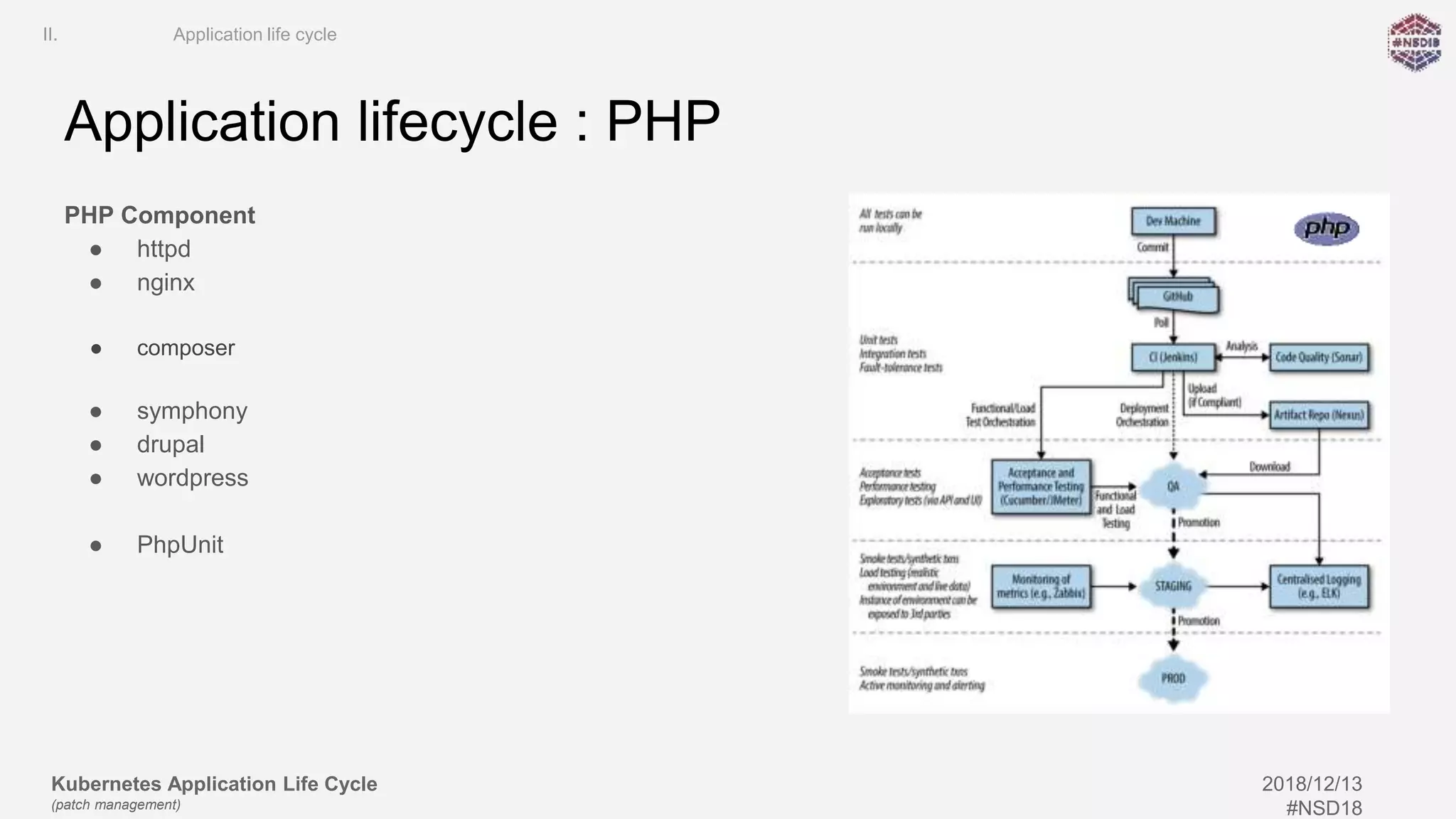
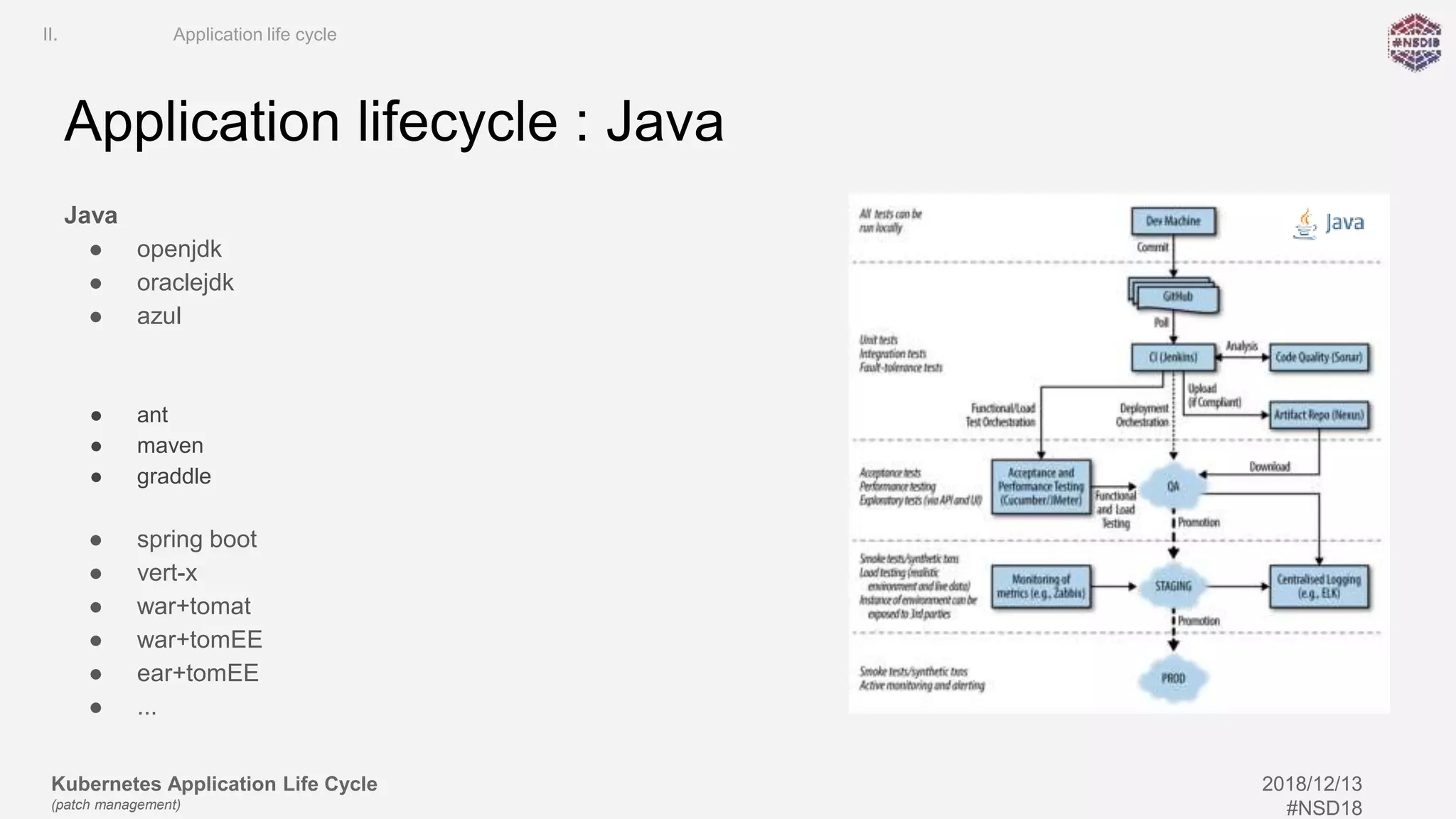
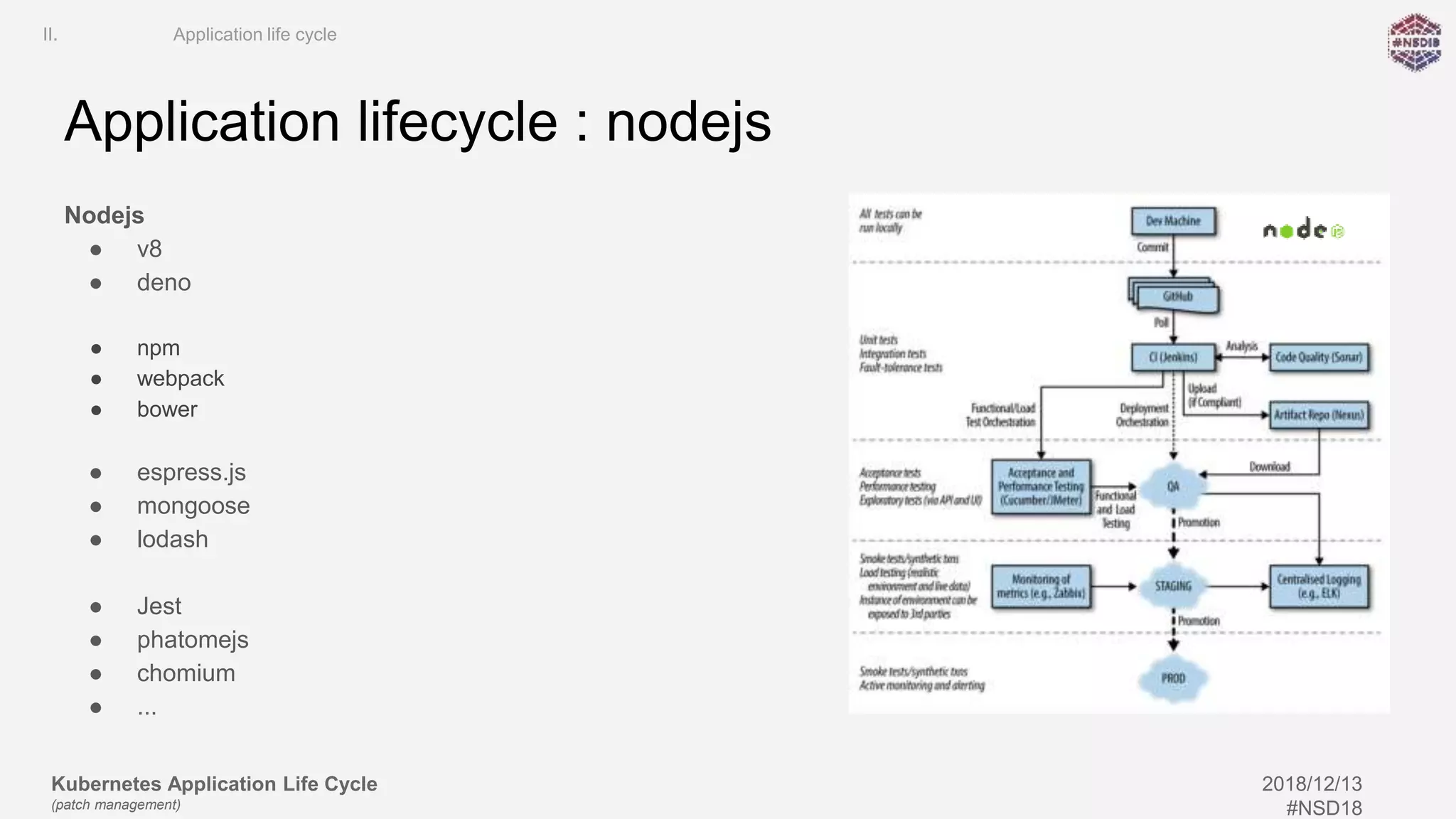
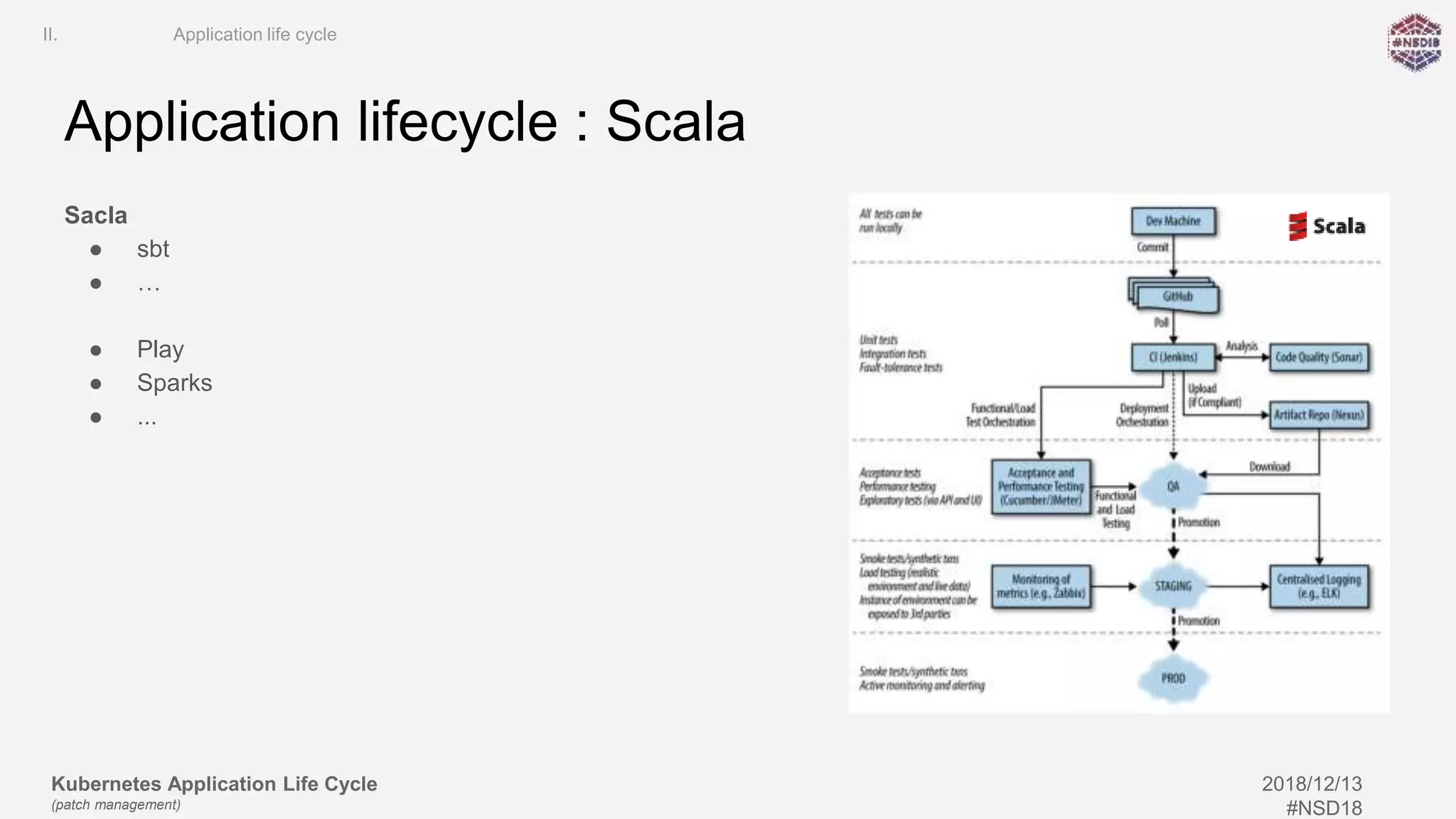
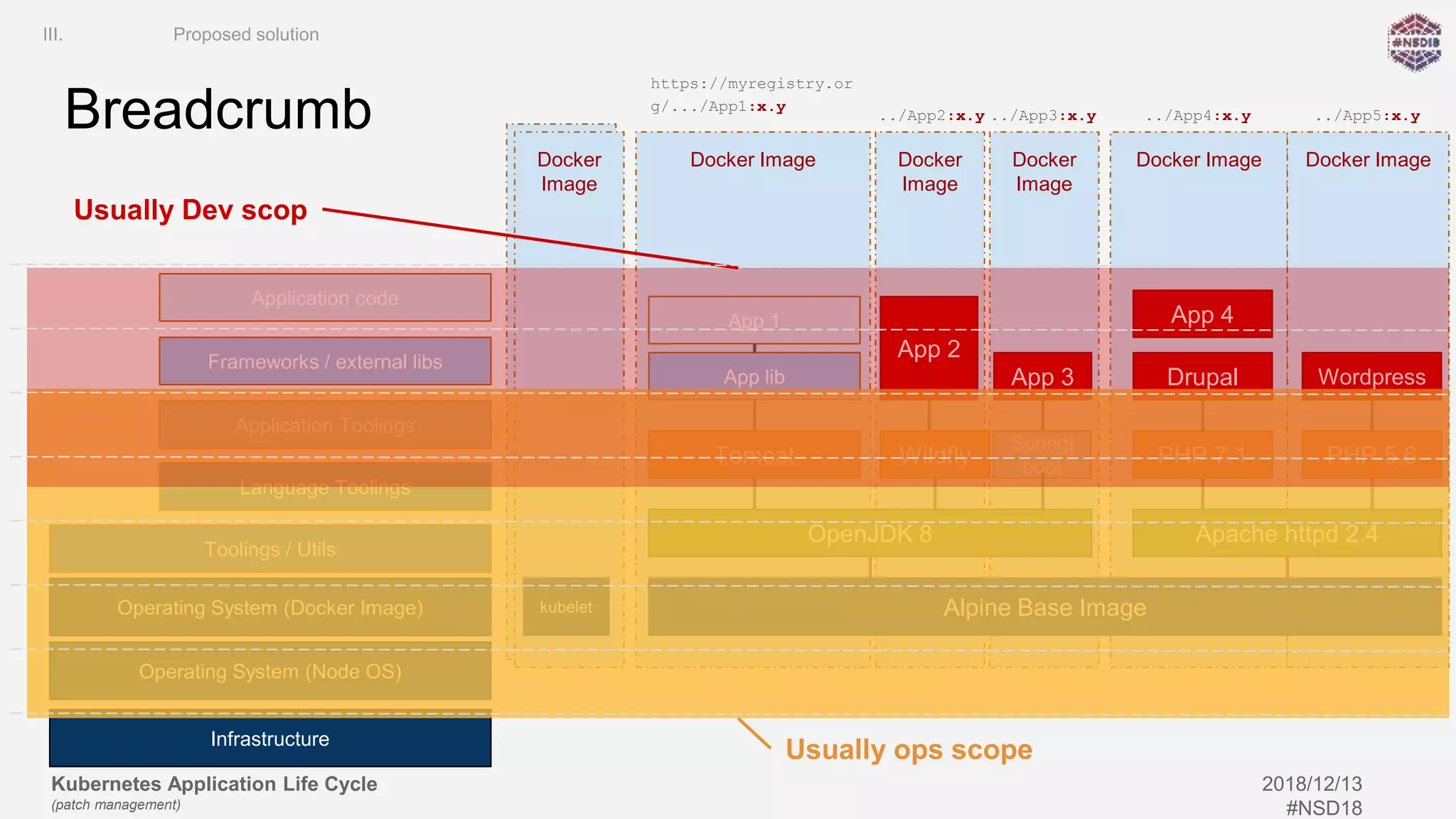
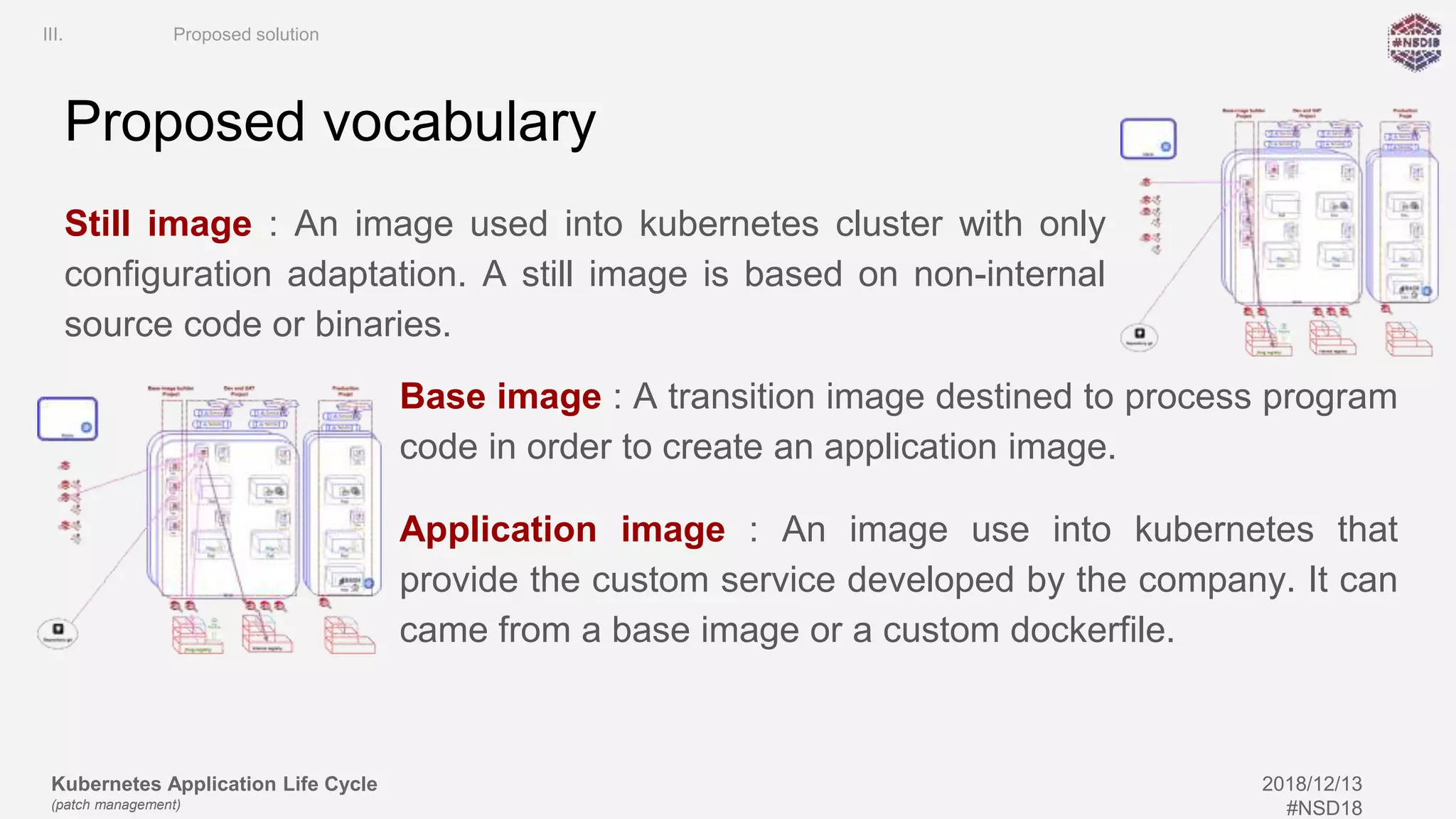
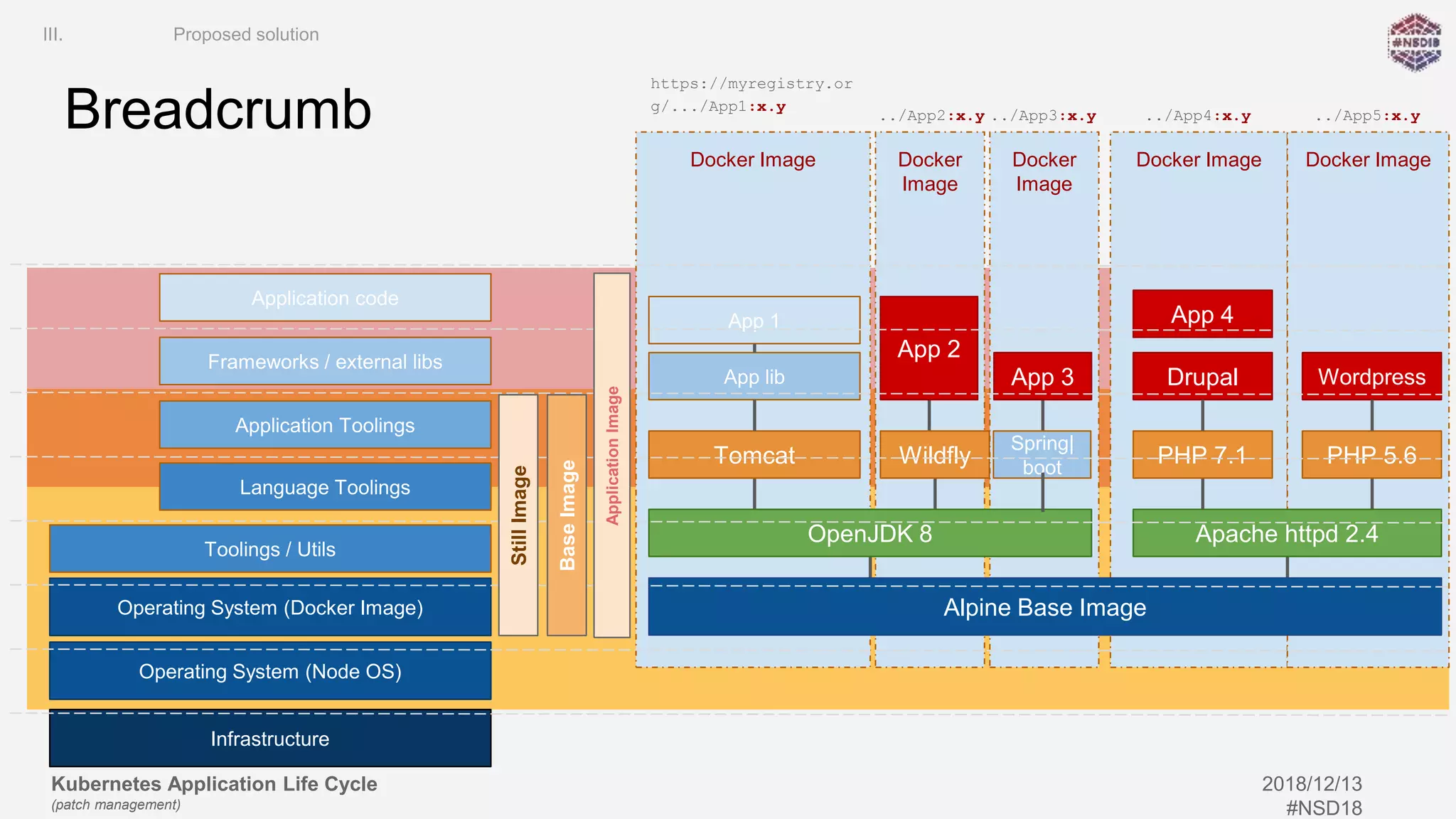
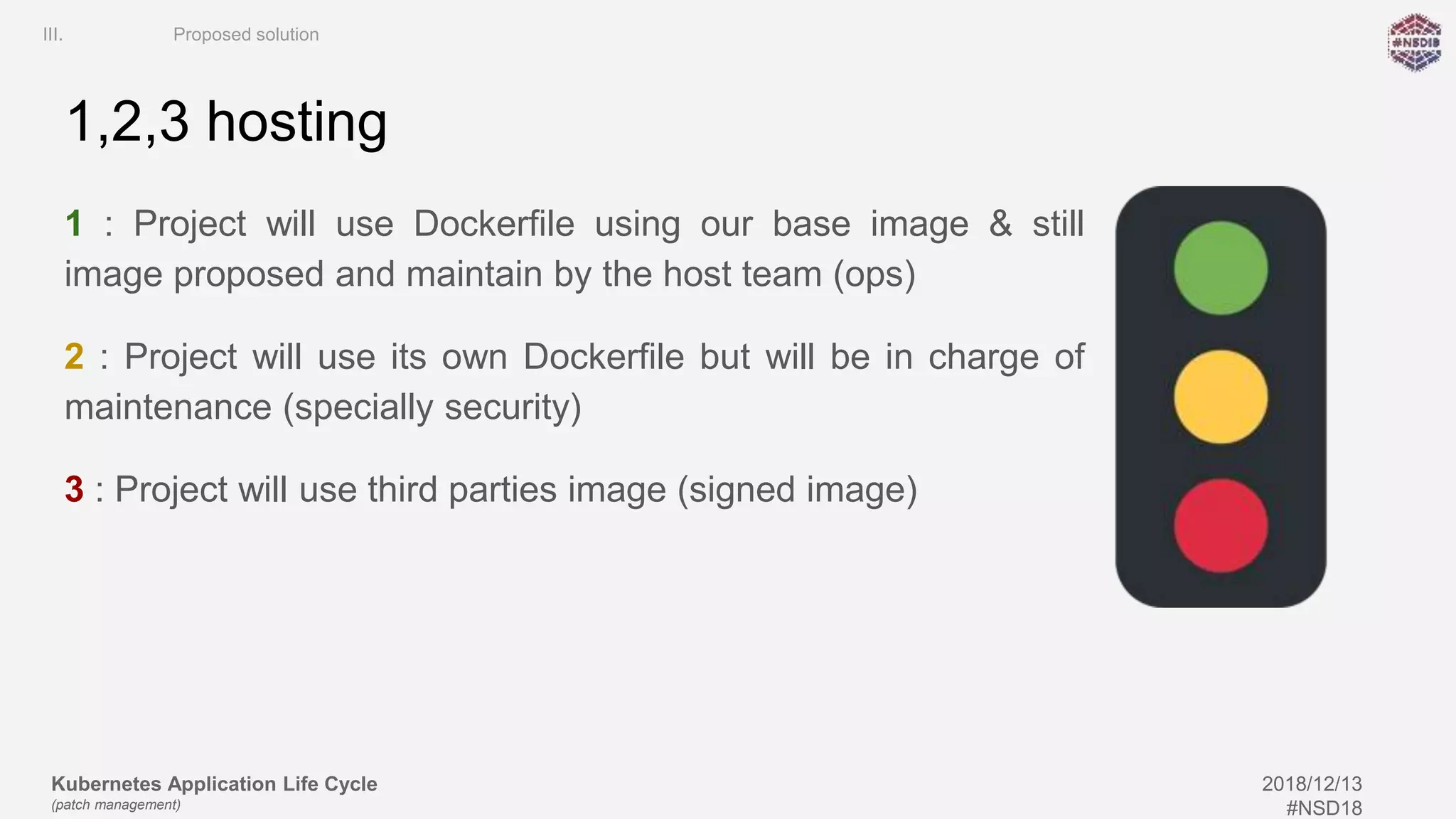
The document outlines the Kubernetes application lifecycle with a focus on patch management, integrating Docker concepts such as images, containers, namespaces, and control groups. It discusses the workflow for continuous development, integration, and deployment along with tools like SonarQube for code quality and ZAP for security testing. Additionally, it presents a proposed solution for managing technical challenges associated with application lifecycle management.