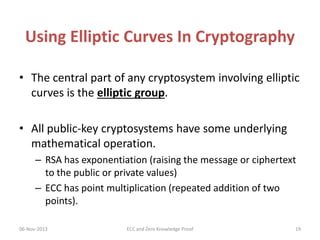
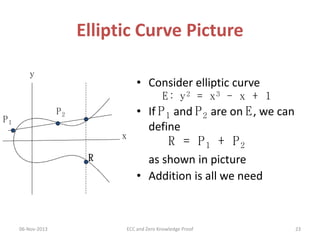
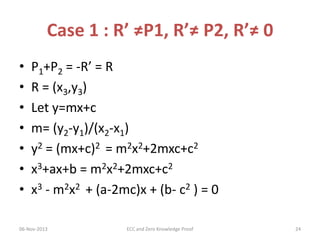
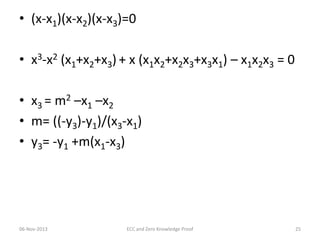
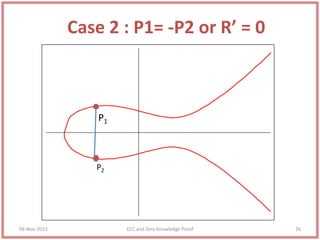
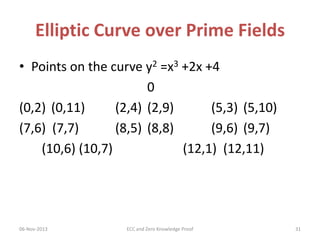
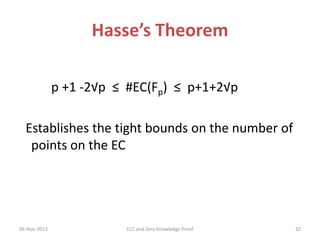
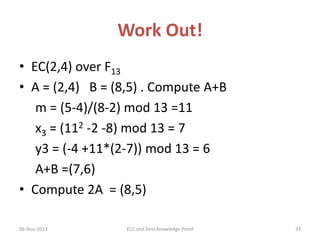
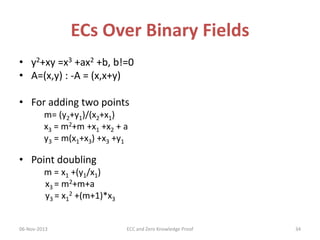
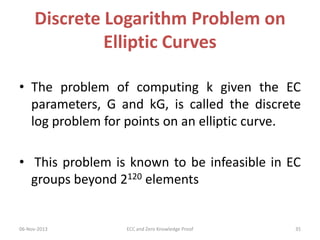
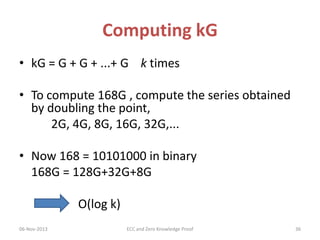
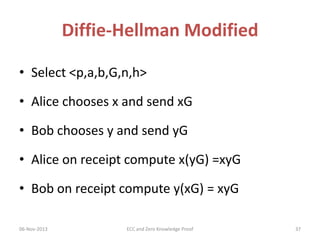
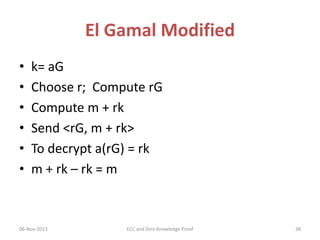
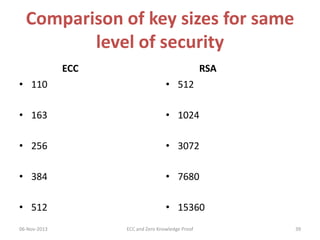
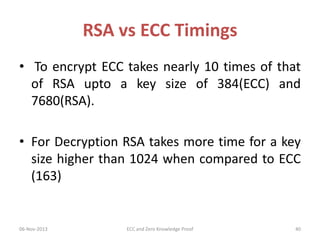
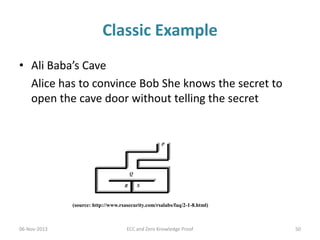
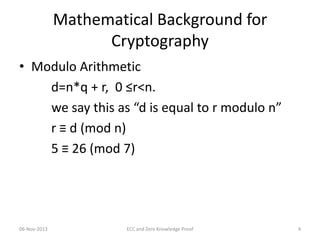
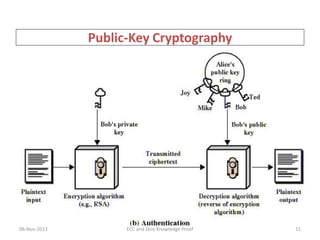
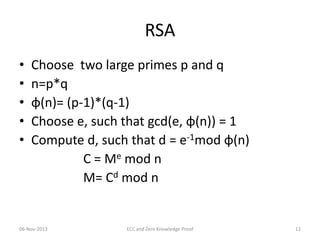
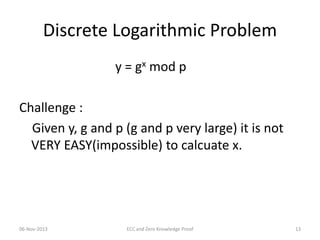
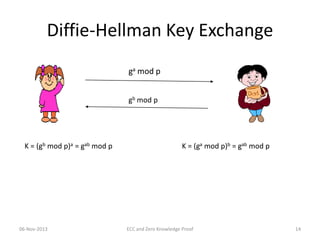
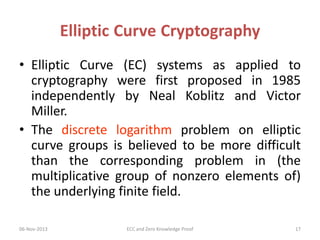
The document covers elliptic curve cryptography (ECC) and zero knowledge proofs (ZKP), exploring their mathematical foundations, applications in public key cryptography, and efficiencies compared to traditional methods like RSA. It introduces key concepts such as group structures, discrete logarithm problems, and the implementation of ECC in various systems. Additionally, it discusses properties, advantages, and real-world applications of zero knowledge proofs, highlighting their role in secure authentication and data integrity.

![What Is Elliptic Curve Cryptography
(ECC)?
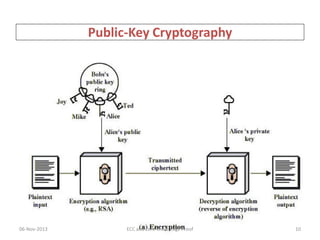
• Elliptic curve cryptography [ECC] is a public-key
cryptosystem just like RSA, Rabin, and El Gamal.
• Every user has a public and a private key.
– Public key is used for encryption/signature verification.
– Private key is used for decryption/signature generation.
• Elliptic curves are used as an extension to other
current cryptosystems.
06-Nov-2013
ECC and Zero Knowledge Proof
18](https://image.slidesharecdn.com/ellipticcurvecryptographyandzeroknowledgeproof-131105012551-phpapp02/85/Elliptic-Curve-Cryptography-and-Zero-Knowledge-Proof-18-320.jpg)