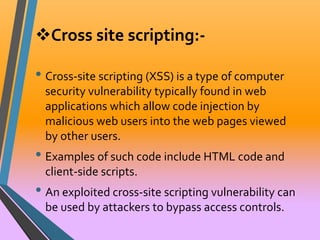
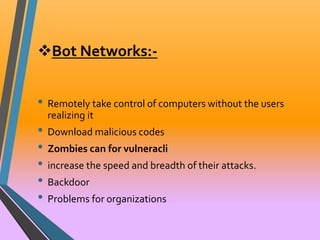
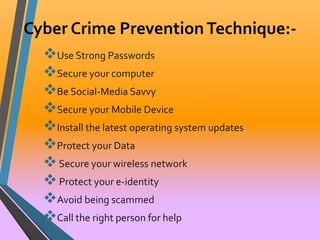
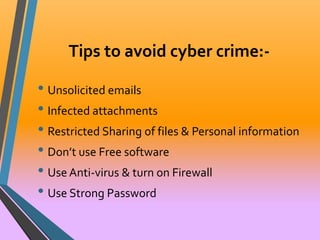
The document provides a comprehensive overview of various types of cyber crimes, including fraud, harassment, drug trafficking, and cyber terrorism, highlighting their definitions and implications. It outlines prevention techniques and emphasizes the need for increased awareness and security measures in an evolving digital landscape. The conclusion touches on the future of cyber crime and the challenges posed by advanced technology.