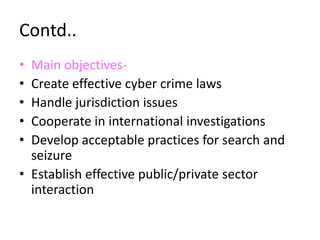
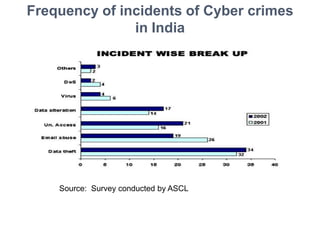
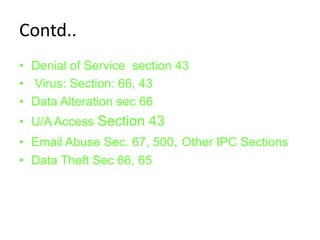
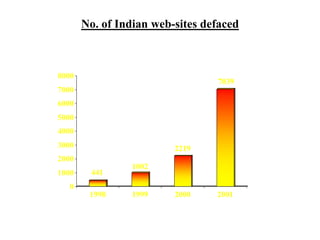
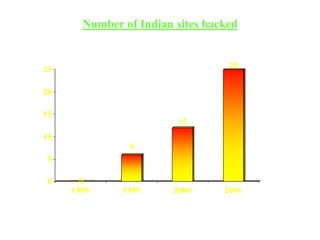
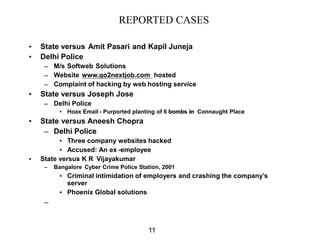
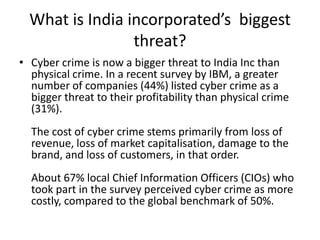
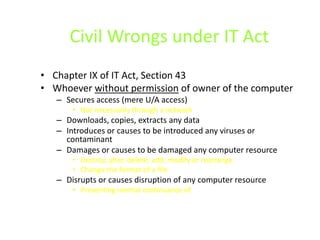
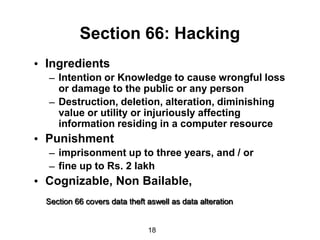
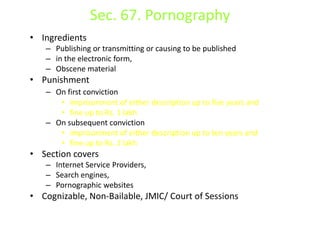
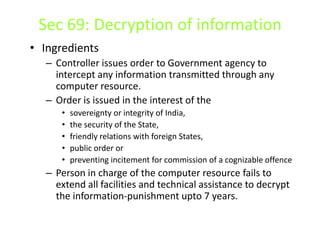
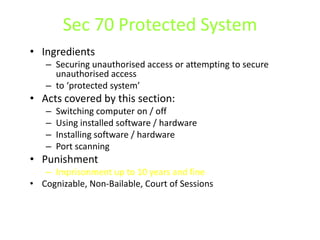
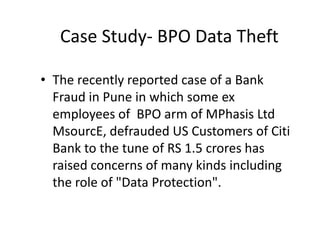
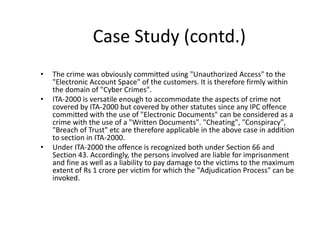
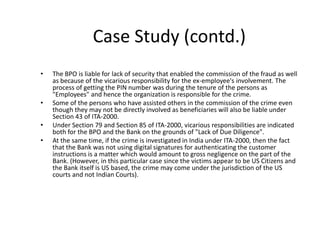
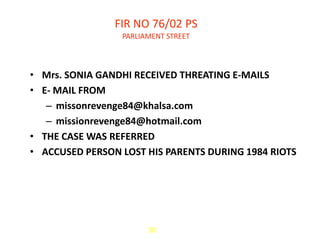
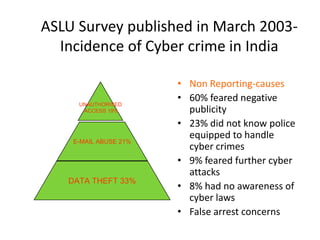
This document provides an introduction to cyber crimes, including definitions and examples. It discusses how computers are vulnerable due to large data storage in small spaces, ease of access, complexity of technology, and human error. It then outlines various types of cyber crimes such as credit card fraud, cyber pornography, intellectual property theft, and cyber stalking. The document also discusses international initiatives to combat cyber crimes and provides examples of cyber crime cases in India. Overall, the document serves as a high-level overview of the topic of cyber crimes.