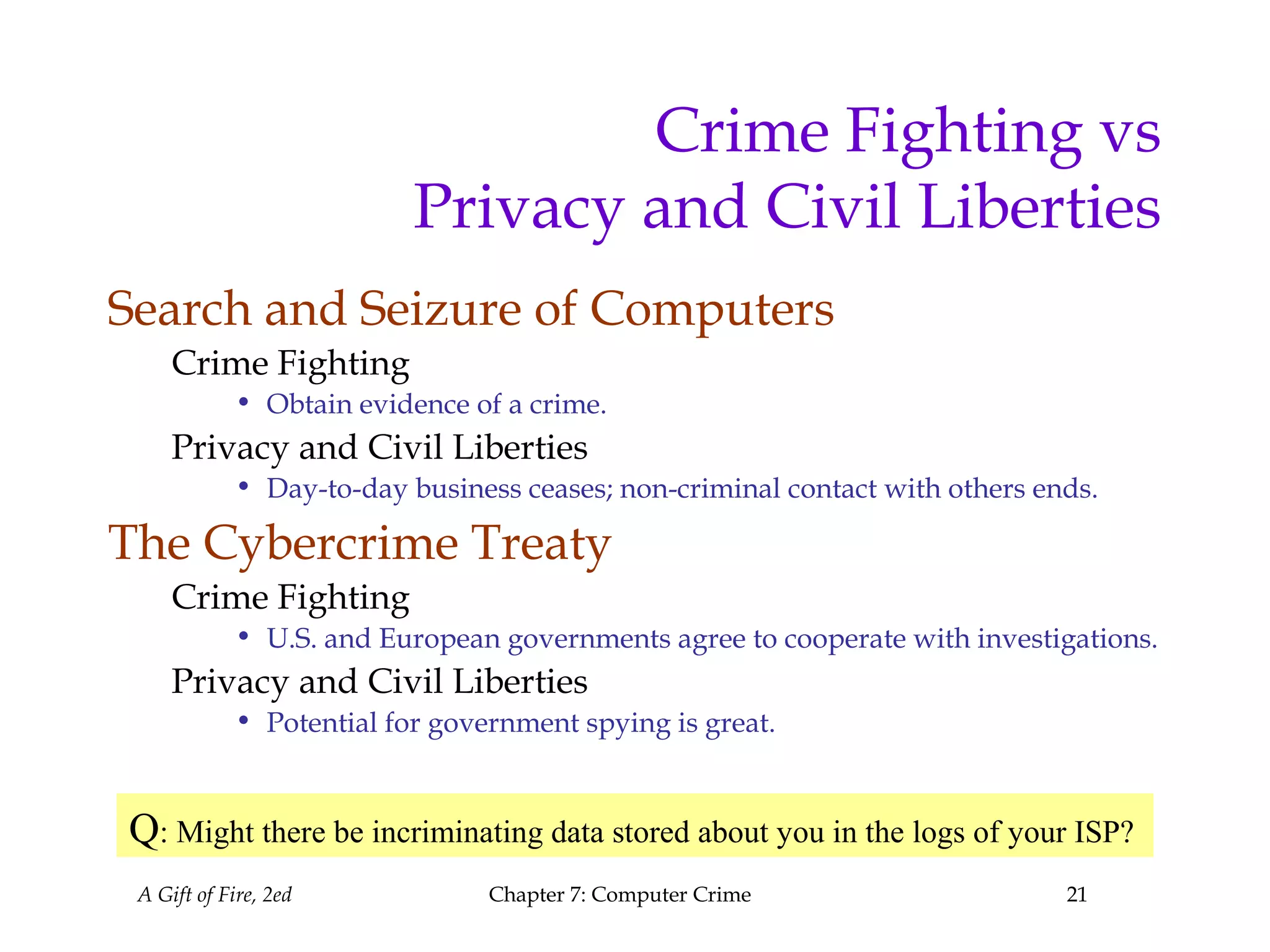
This chapter discusses various types of computer crimes such as hacking, online scams, fraud, embezzlement, sabotage, identity theft, and forgery. It explores the challenges of preventing, detecting, and prosecuting computer crimes while also protecting privacy and civil liberties. Key topics covered include the history and phases of hacking, different types of online scams and fraud, methods used to commit embezzlement and sabotage, causes and defenses related to identity theft and forgery, and the tensions between crime fighting techniques and preserving privacy.