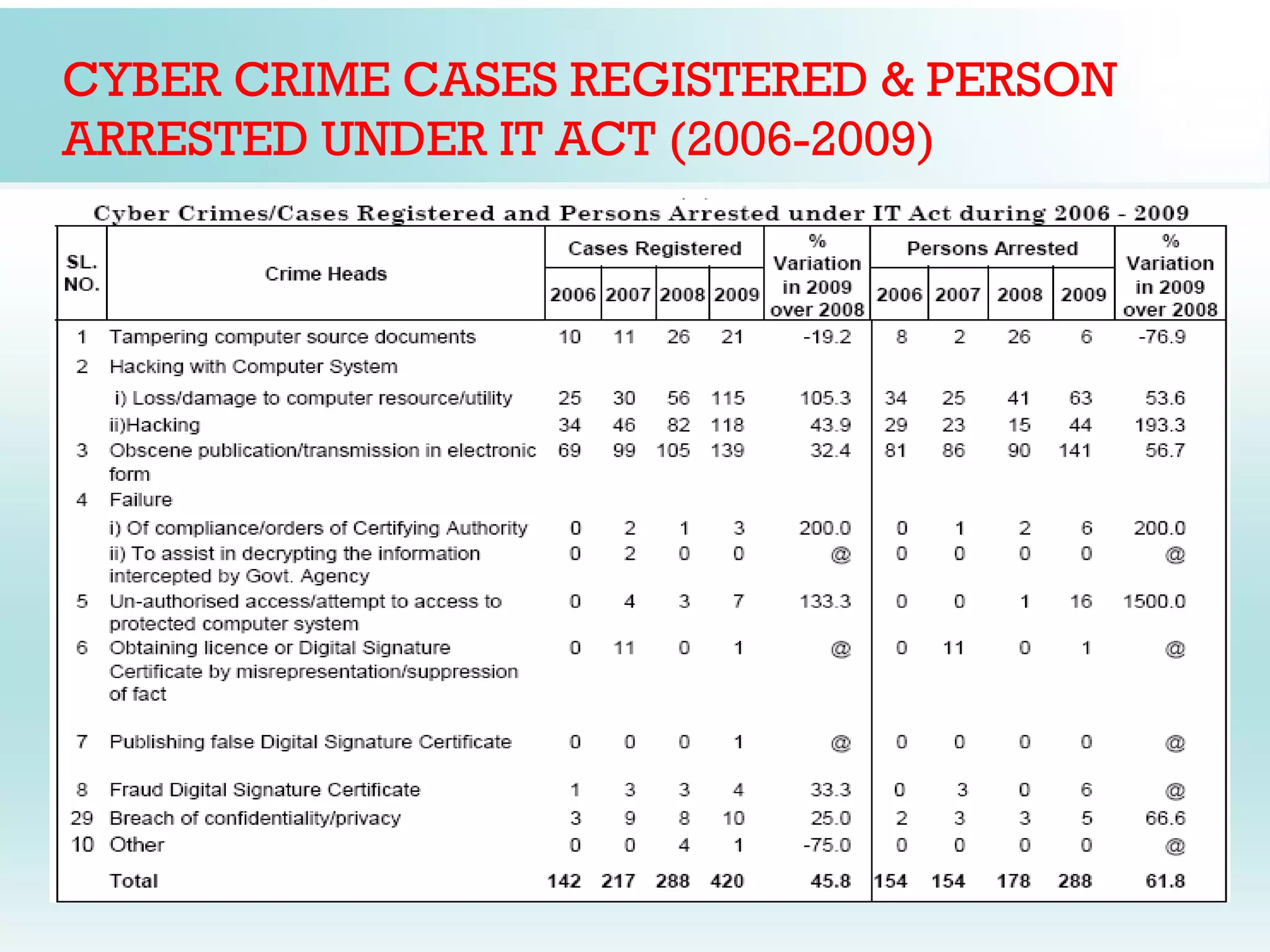
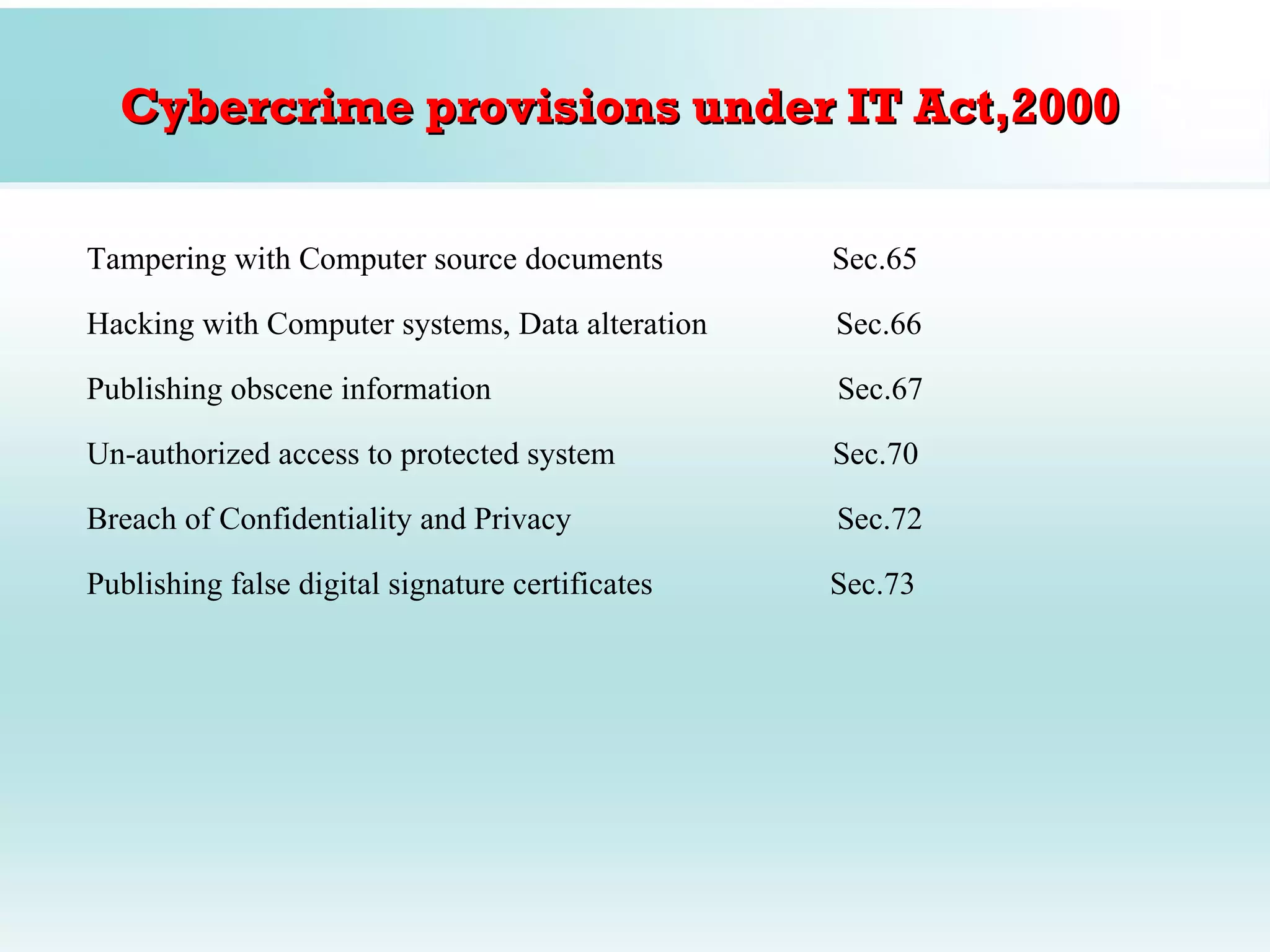
The document discusses India's Information Technology Act and cyber crimes. It provides background on the birth of cyber laws in India and the objectives of the IT Act of 2000. The Act aims to provide legal recognition for electronic transactions and commerce. It also covers key terms, the impact on the banking sector, types of cyber crimes like hacking and cyber terrorism, and statistics on cyber crime cases registered under the IT Act from 2006 to 2009. Amendments to the Act in 2008 are also summarized.