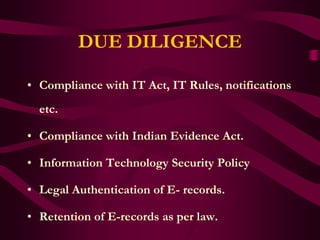
Pavan Duggal gave a presentation on cybercrimes and due diligence. He discussed several high profile cybercrime cases in India and noted that cybercrimes are severely underreported. The key cybercrime categories are crimes against persons, property, and the government. The Information Technology Act 2000 defines and punishes offenses such as hacking and publishing obscene material online. New forms of cybercrime are constantly emerging. Companies need to conduct due diligence audits to limit their legal liability and comply with data security laws.