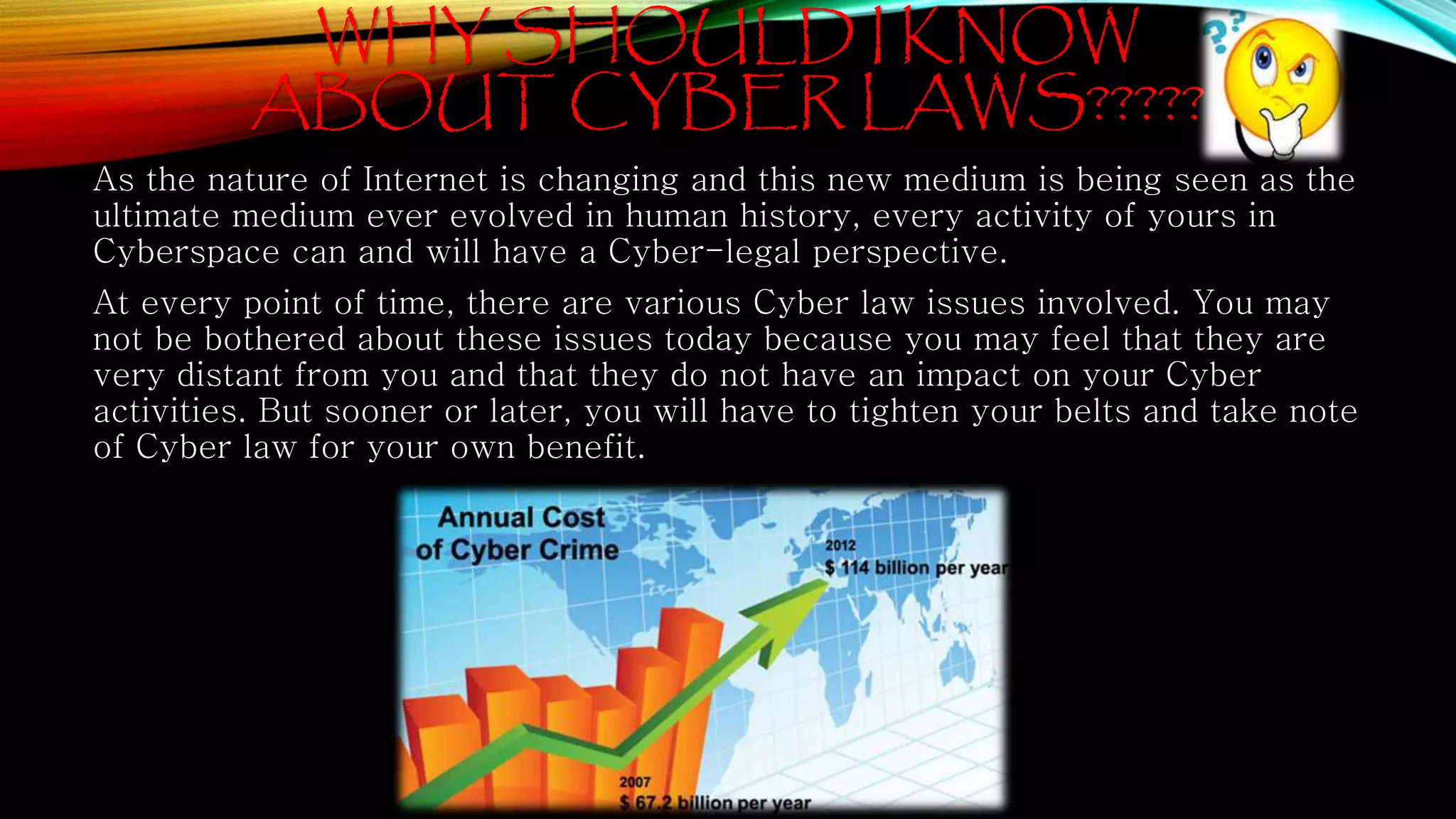
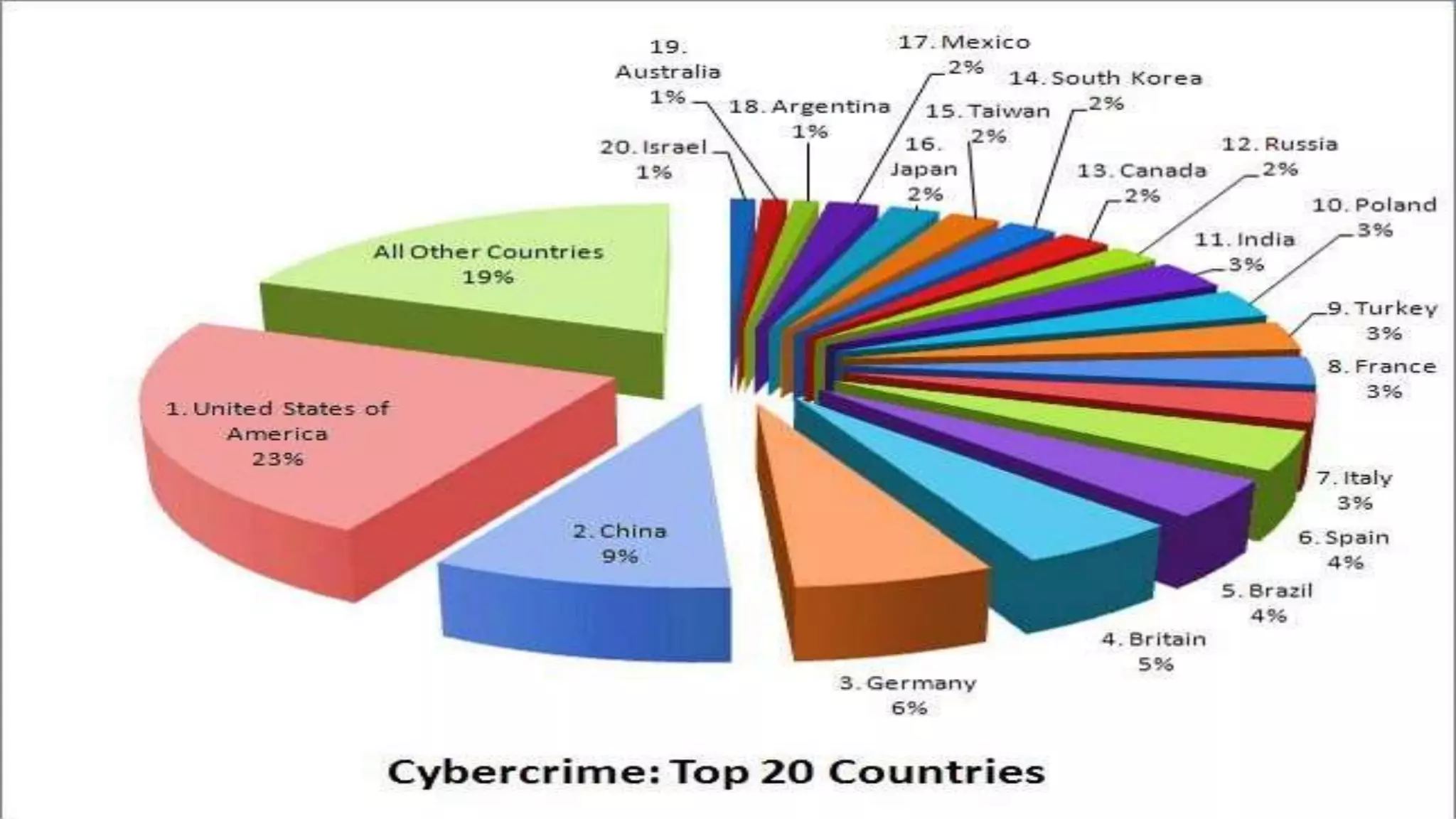
This presentation provides an overview of cyber laws in India. It begins with definitions of cyber crime and classifications of different types of cyber crimes such as those against persons, property, and government. It then discusses the need for cyber laws in India given its growing internet user base. The key cyber laws discussed are the Information Technology Act of 2000 and its 2008 amendment, which created offenses related to hacking, identity theft, cheating, and privacy violations. Statistics on reported cyber crimes in India are also presented. Countermeasures to cyber crimes and the future threats are briefly outlined before a case study is described.



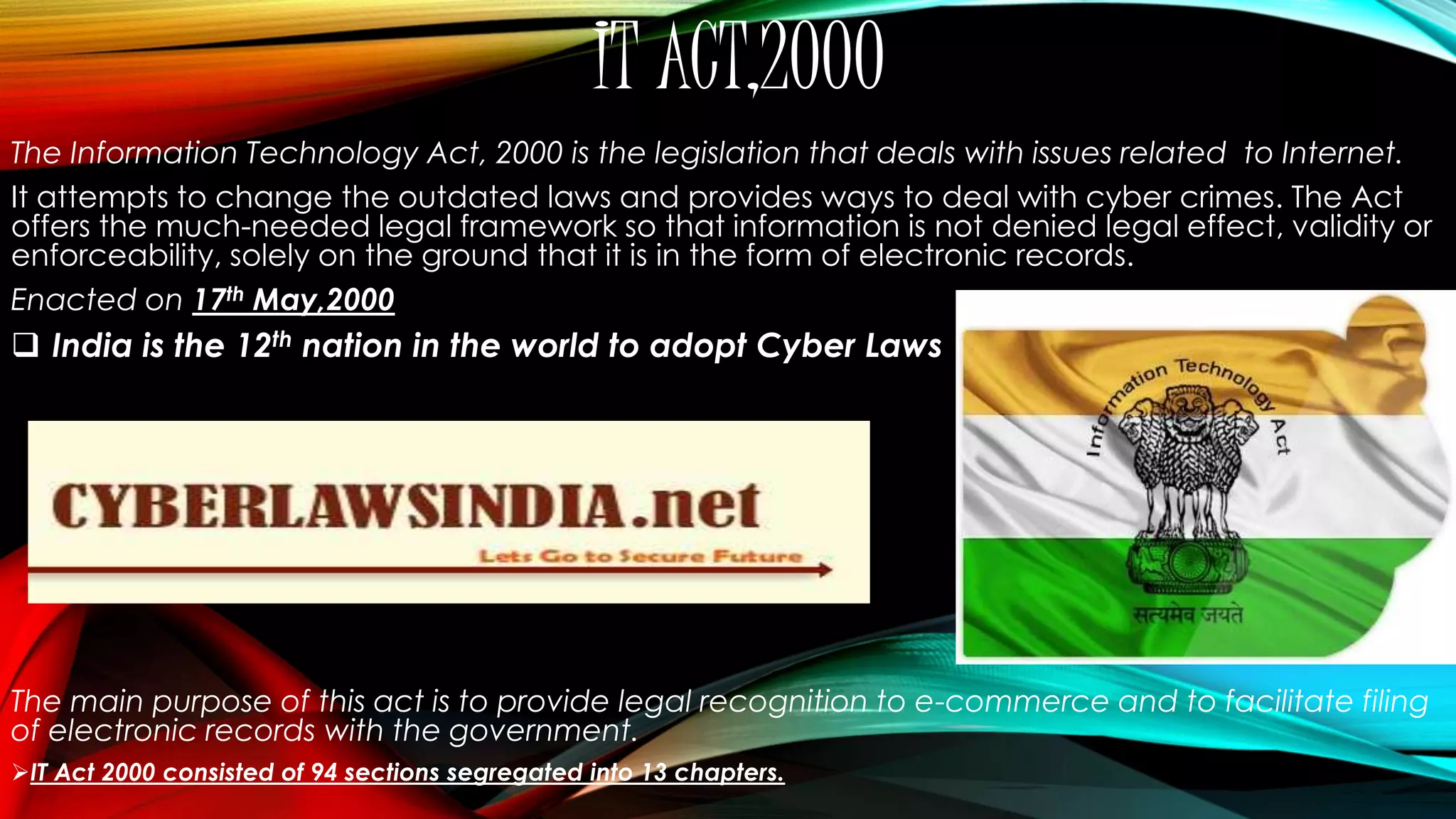
![CHAPTER XI – OFFENCES – 66. Hacking with computer system.
(1)Whoever, intentionally or unintentionally risks the security of a
computer system or network, commits hack.
(2) Whoever commits hacking shall be punished with imprisonment up to three years,
or with fine which may extend up to two lakh rupees, or with both.
Section – 43
Deals with cyber trespassing
“If any person, dishonestly, or fraudulently, does any act referred to in section 43, he shall be punishable with
imprisonment for a term which may extend to three years or with fine which may extend to five lakh rupees
or with both.” [S.66]](https://image.slidesharecdn.com/cyberlaws1-141029085329-conversion-gate01/75/Cyber-laws-in-India-11-2048.jpg)