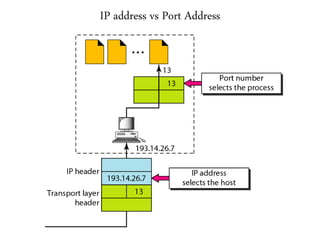
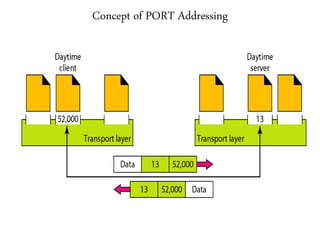
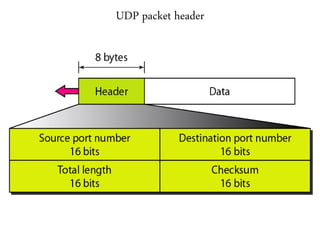
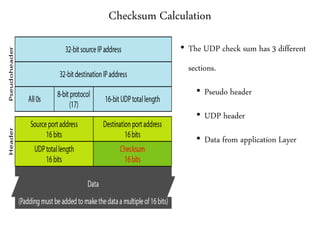
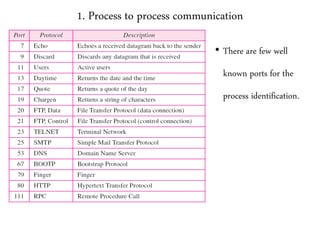
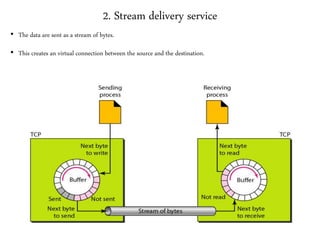
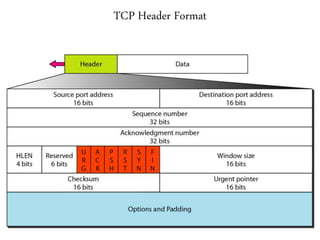
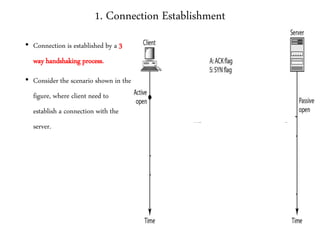
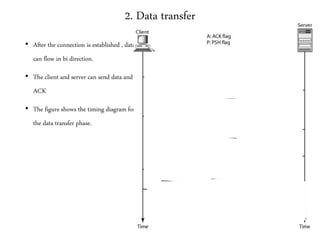
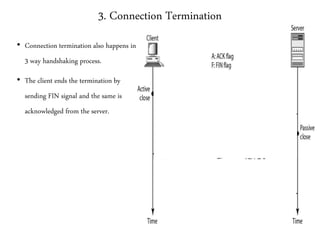
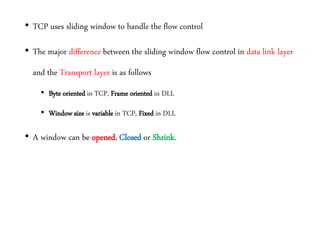
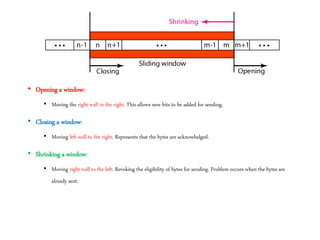
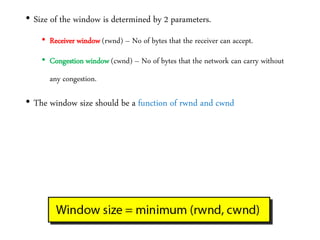
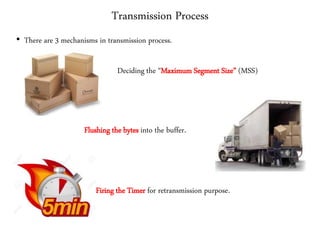
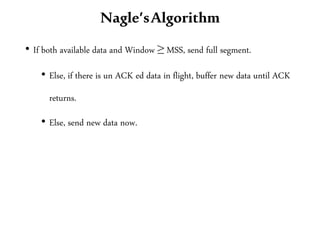
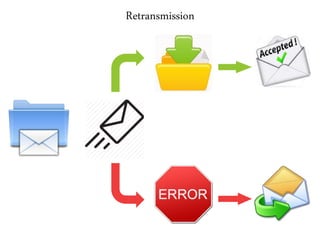
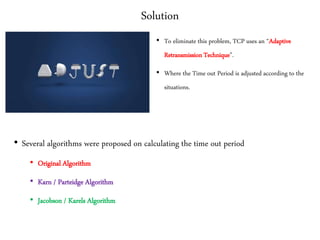
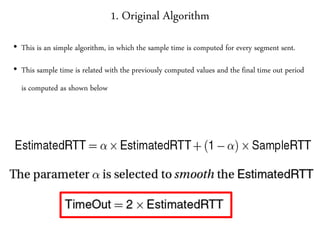
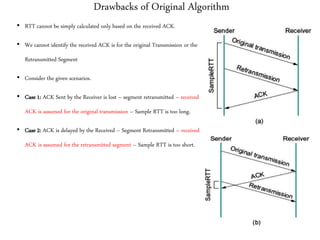
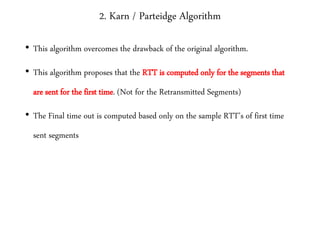
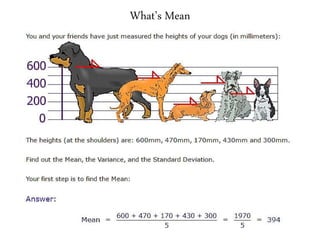
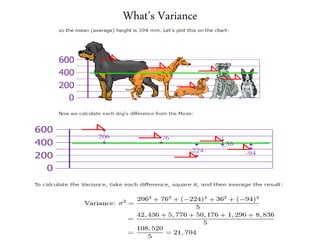
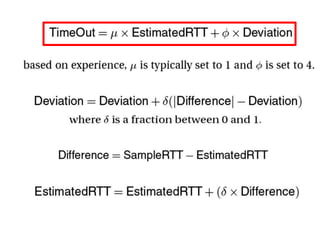
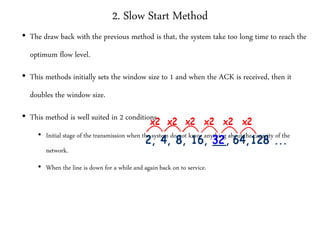
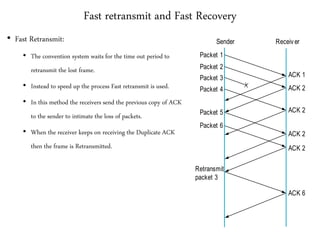
This document provides a summary of the transport layer of computer networks. It discusses key topics like UDP, TCP, connection management, flow control, congestion control, and quality of service. UDP provides a connectionless, unreliable service while TCP provides connection-oriented, reliable byte streaming. TCP uses three-way handshaking for connection establishment and termination. It implements flow control using sliding windows and employs congestion control algorithms like additive increase/multiplicative decrease. The document also covers transport layer concepts like ports, checksums, and retransmission methods in TCP.