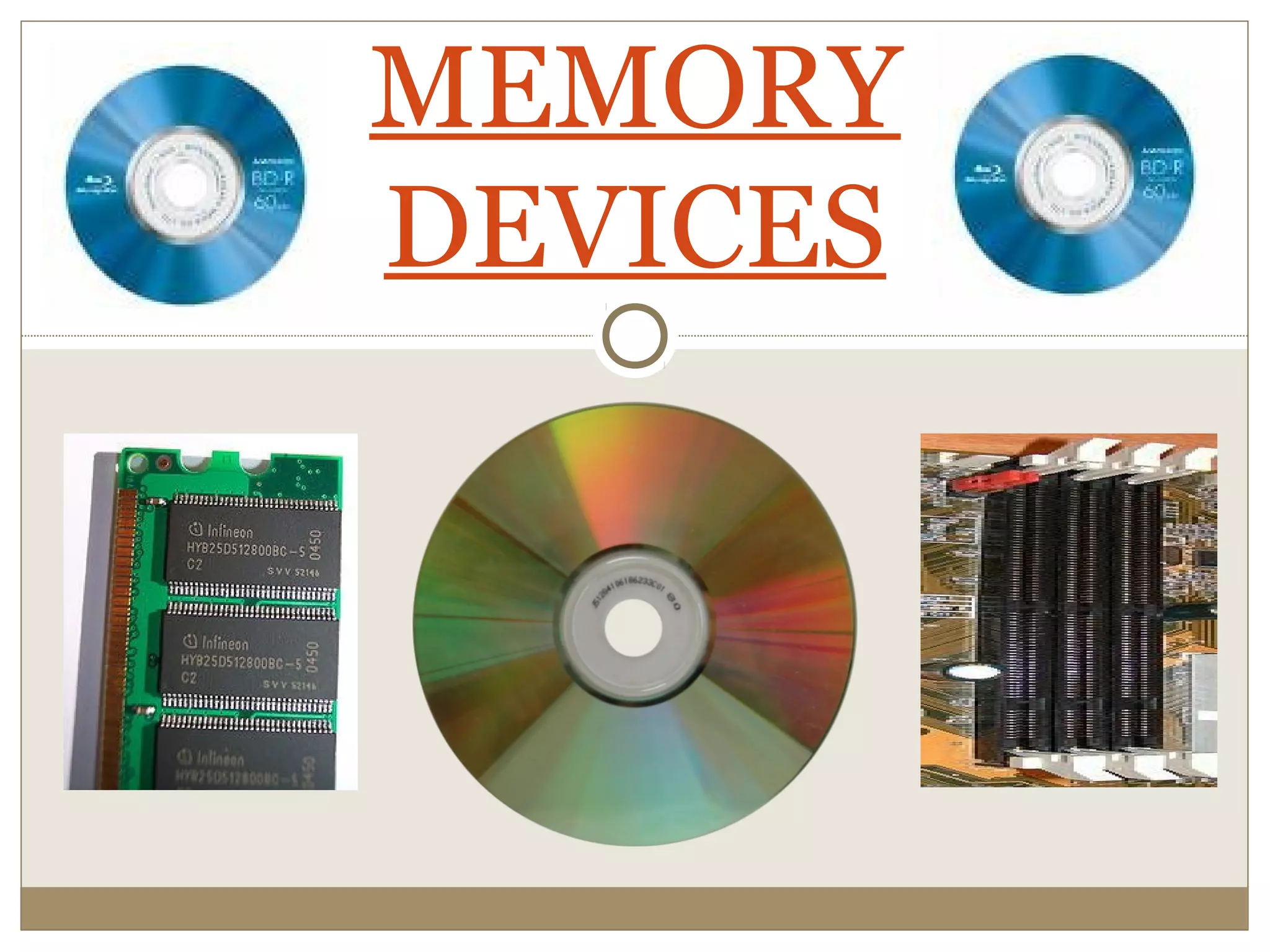
This document provides an overview of different types of computer memory devices. It begins by explaining the importance of memory and then outlines the main types which include main memory (RAM and ROM), cache memory, and secondary storage devices. RAM is further divided into DRAM and SRAM. ROM includes PROM, EPROM, and EEPROM. Secondary storage includes magnetic devices like hard disks and floppy disks, as well as optical devices like CDs and DVDs. Newer memory technologies like flash memory and Blu-ray disks are also mentioned.