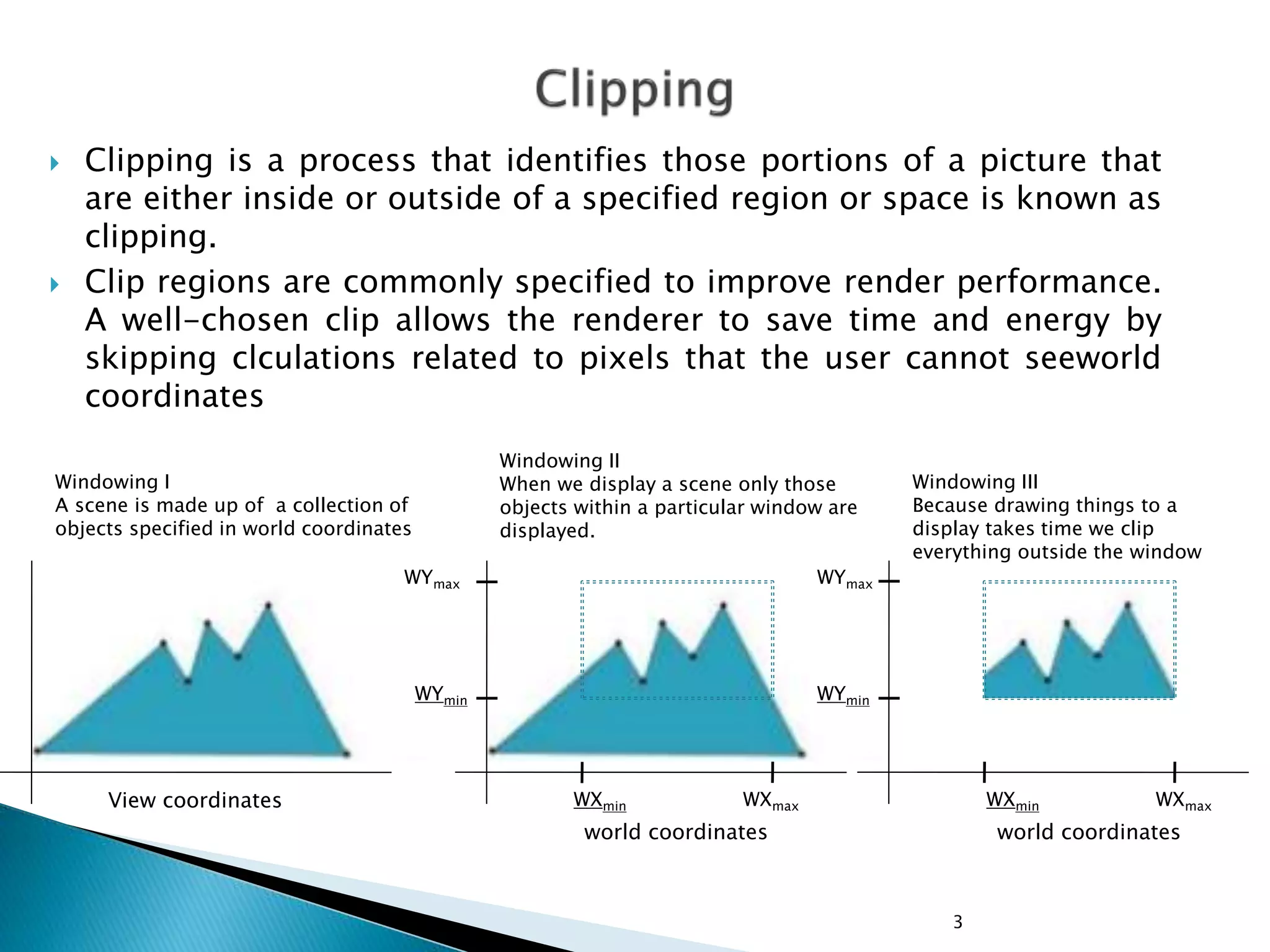
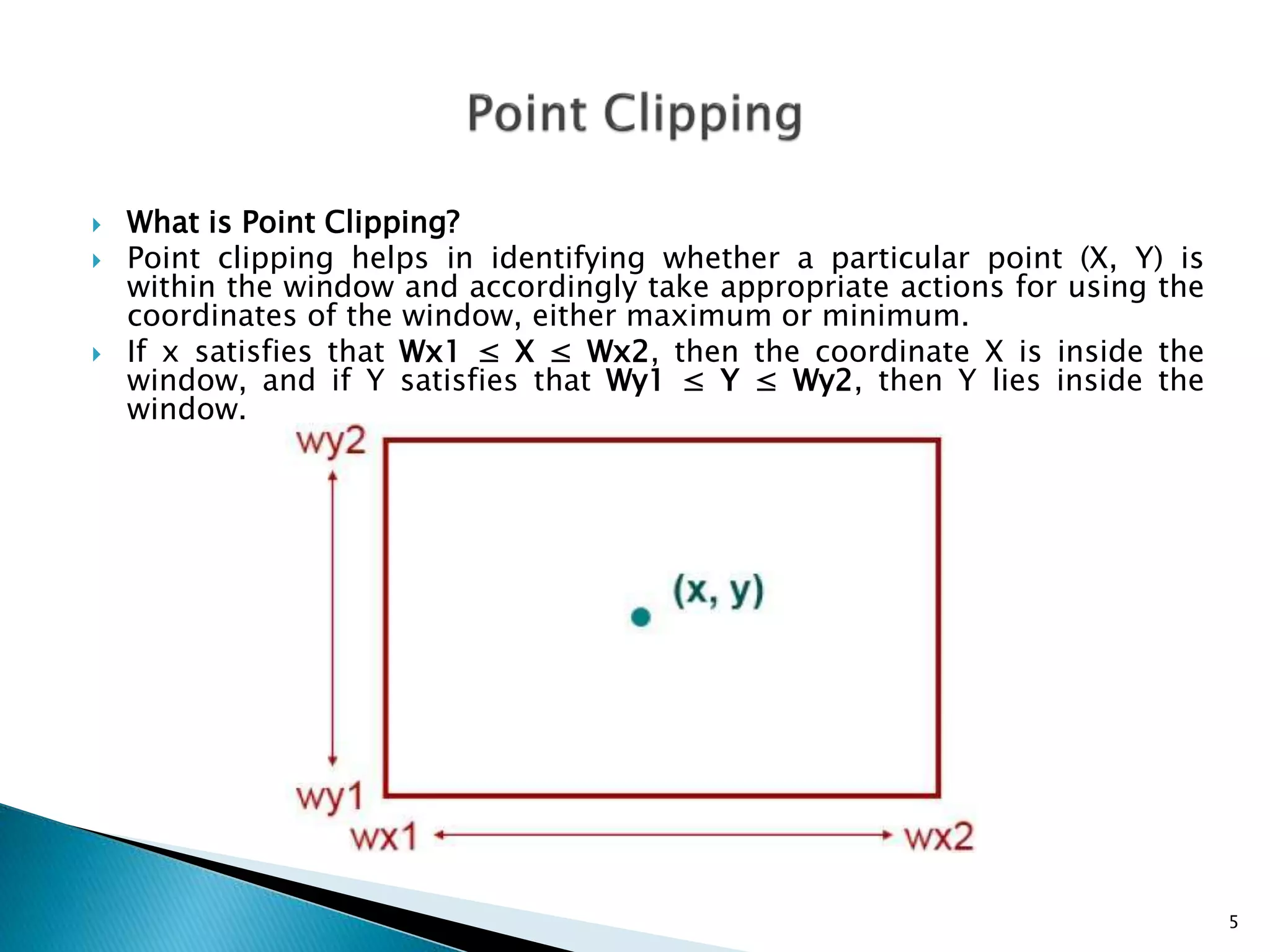
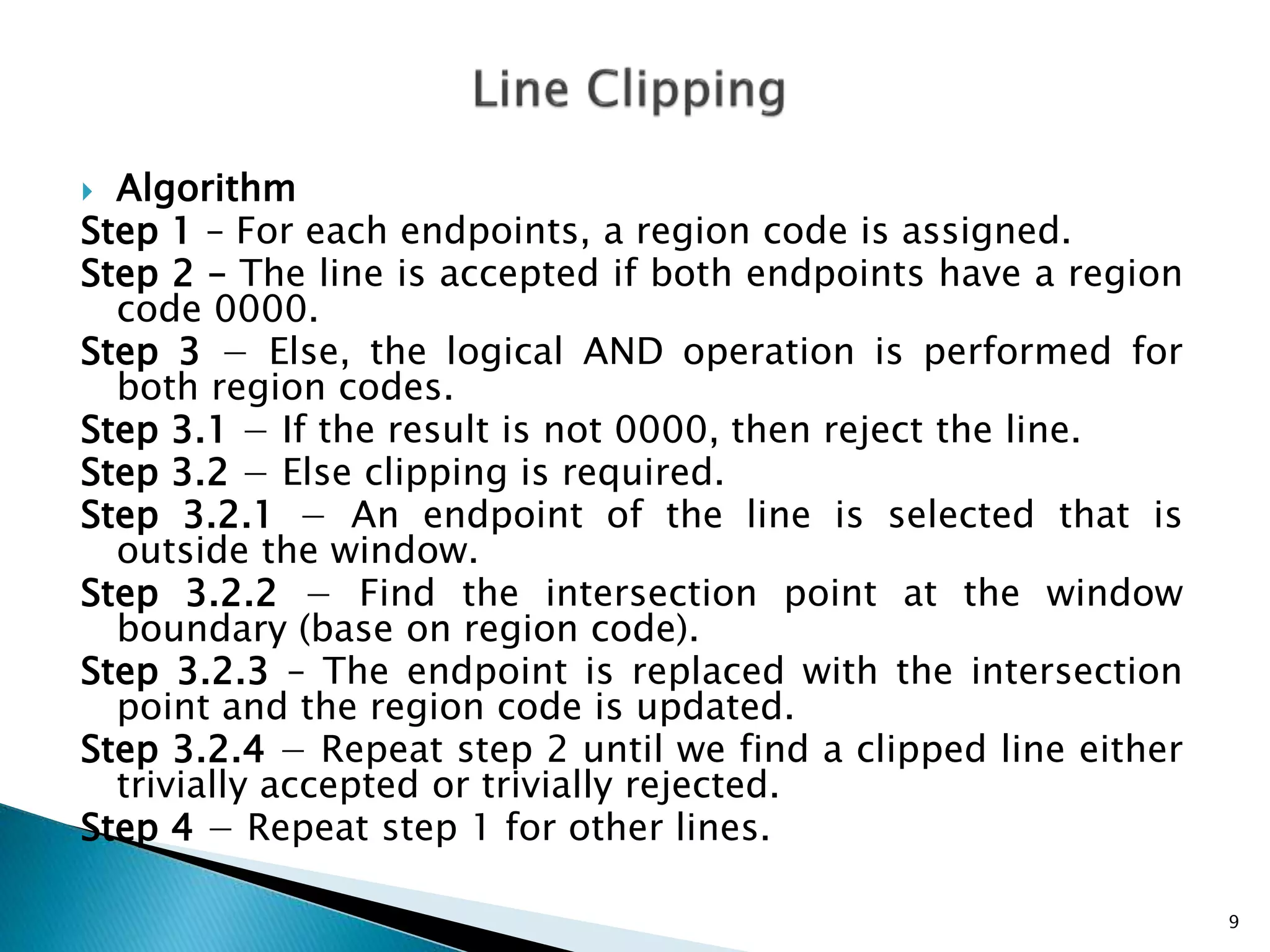
The document discusses the clipping process in computer graphics, which identifies portions of images inside or outside specified regions to improve rendering performance. It covers techniques like Cohen-Sutherland line clipping, Sutherland-Hodgman polygon clipping, and text clipping, explaining the algorithms and scenarios for each method. Key details include how points, lines, and polygons are evaluated based on their positions relative to the clipping window, and the impact of these methods on rendering efficiency.