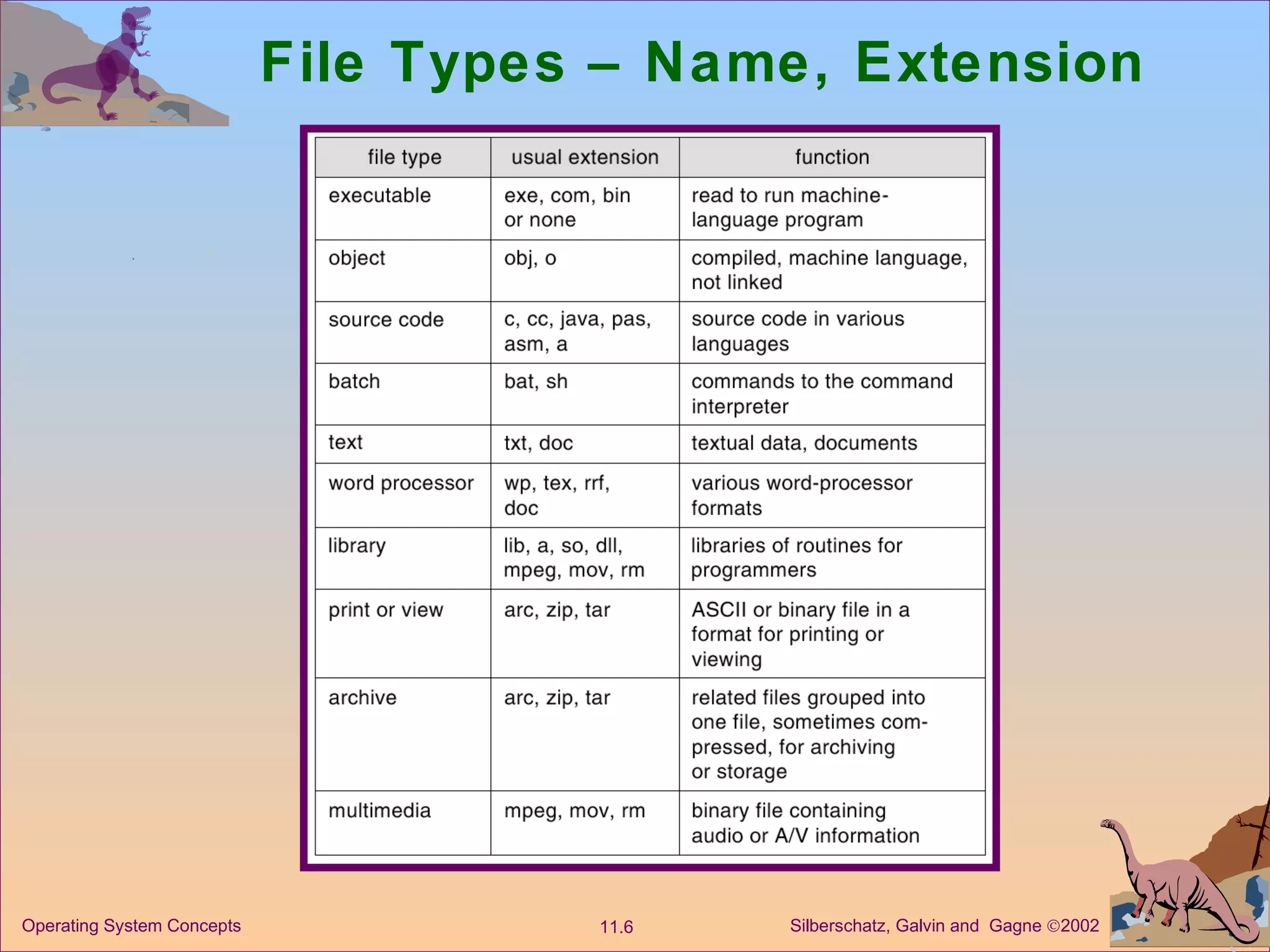
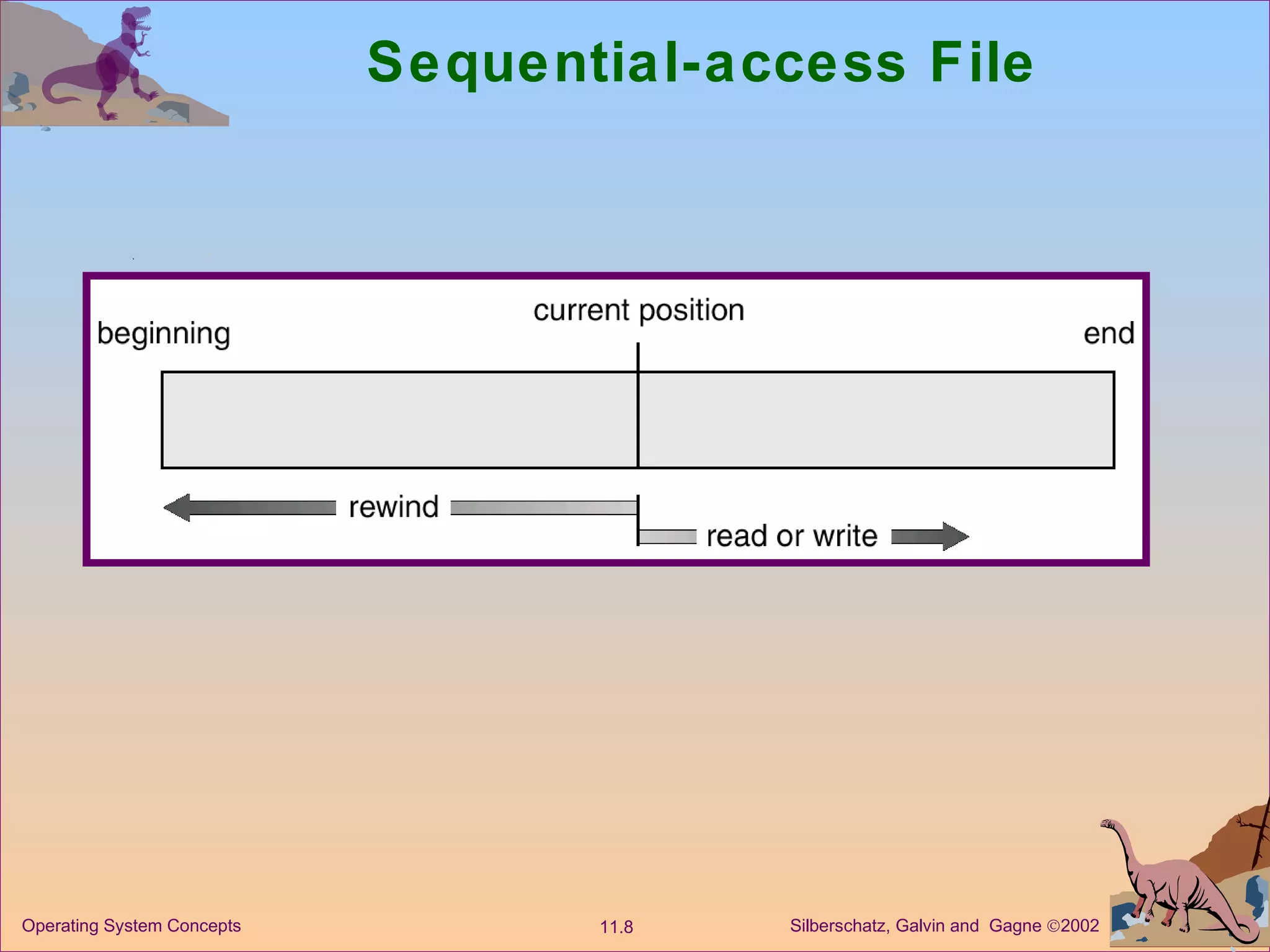
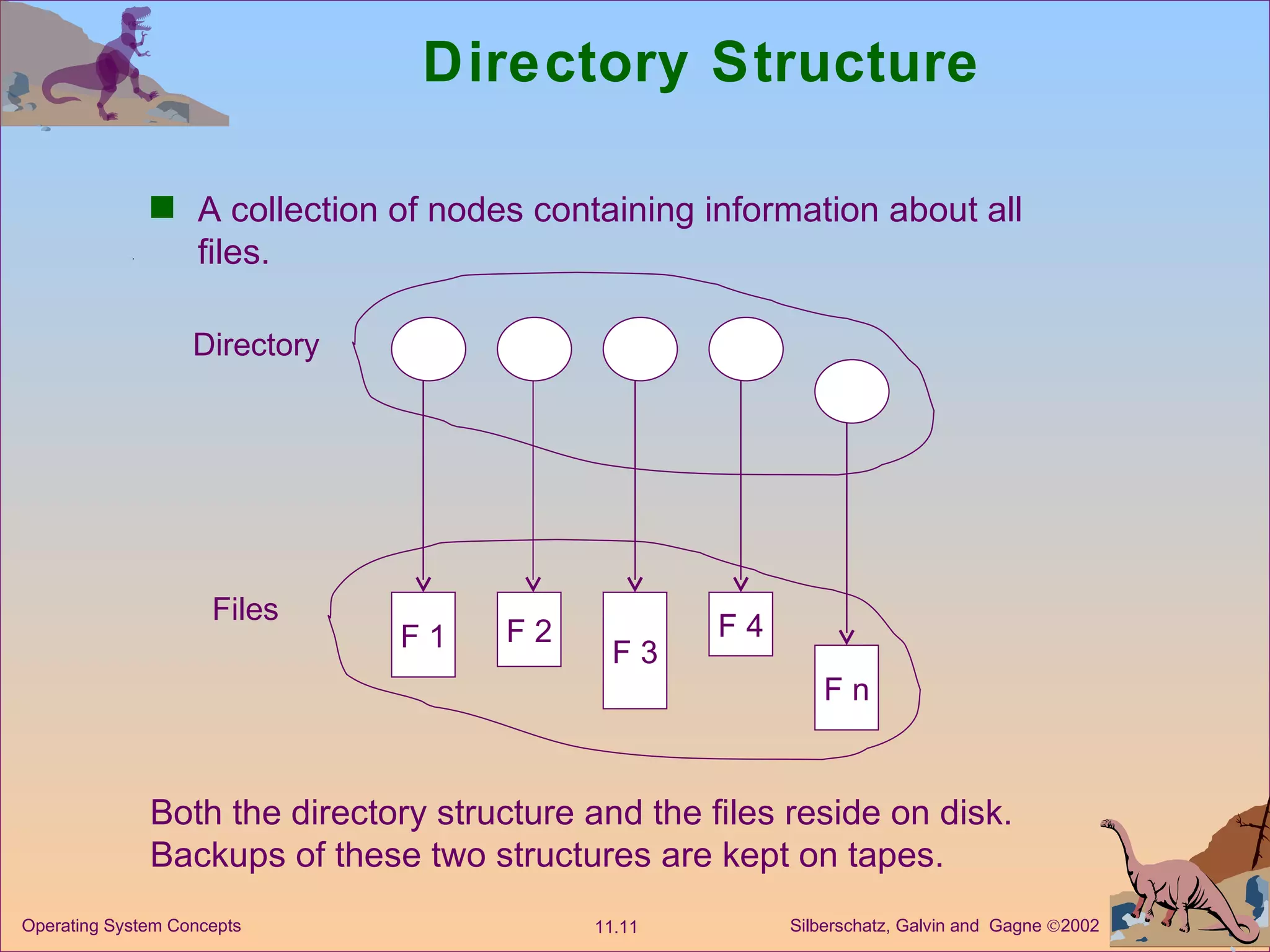
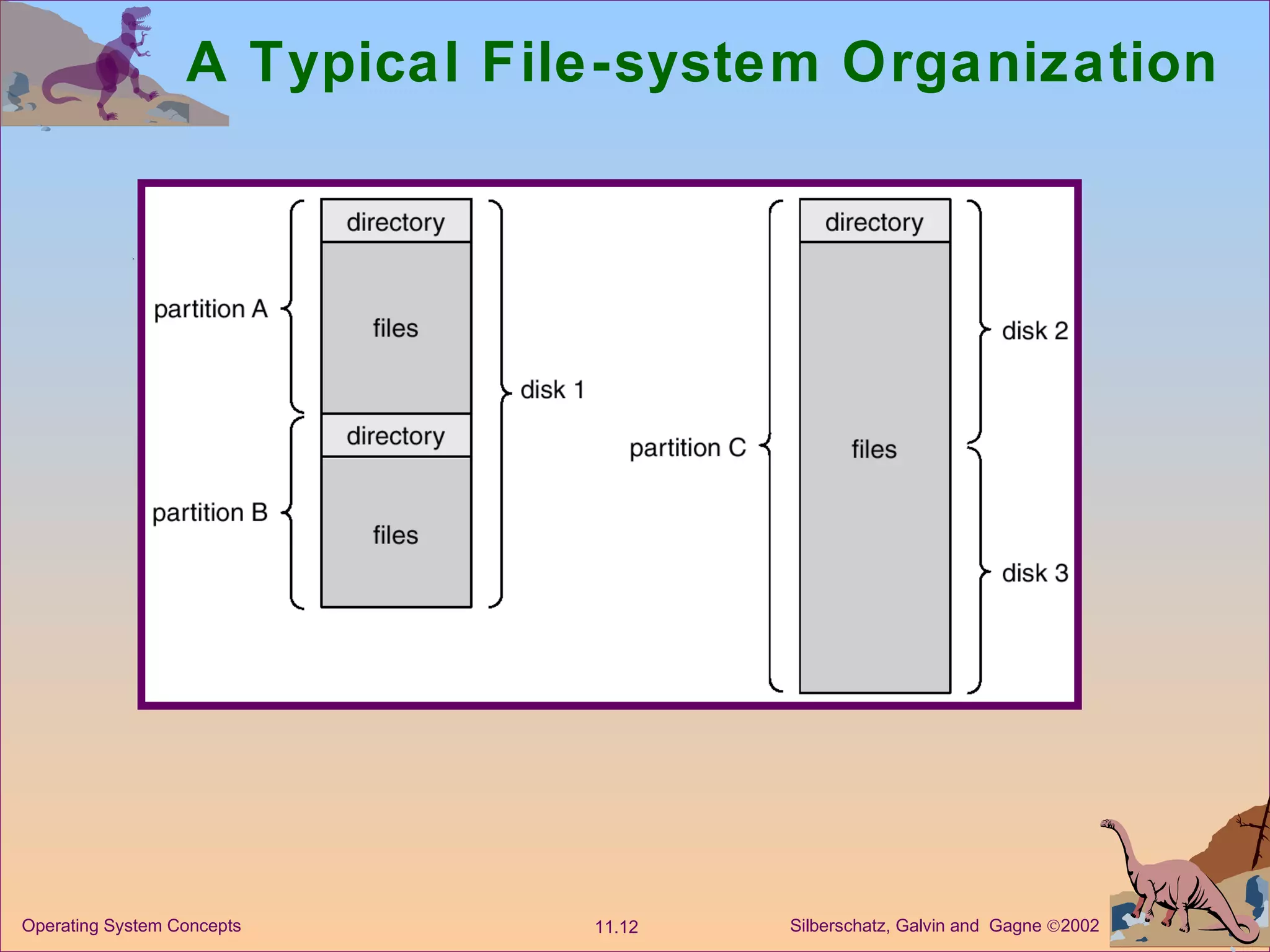
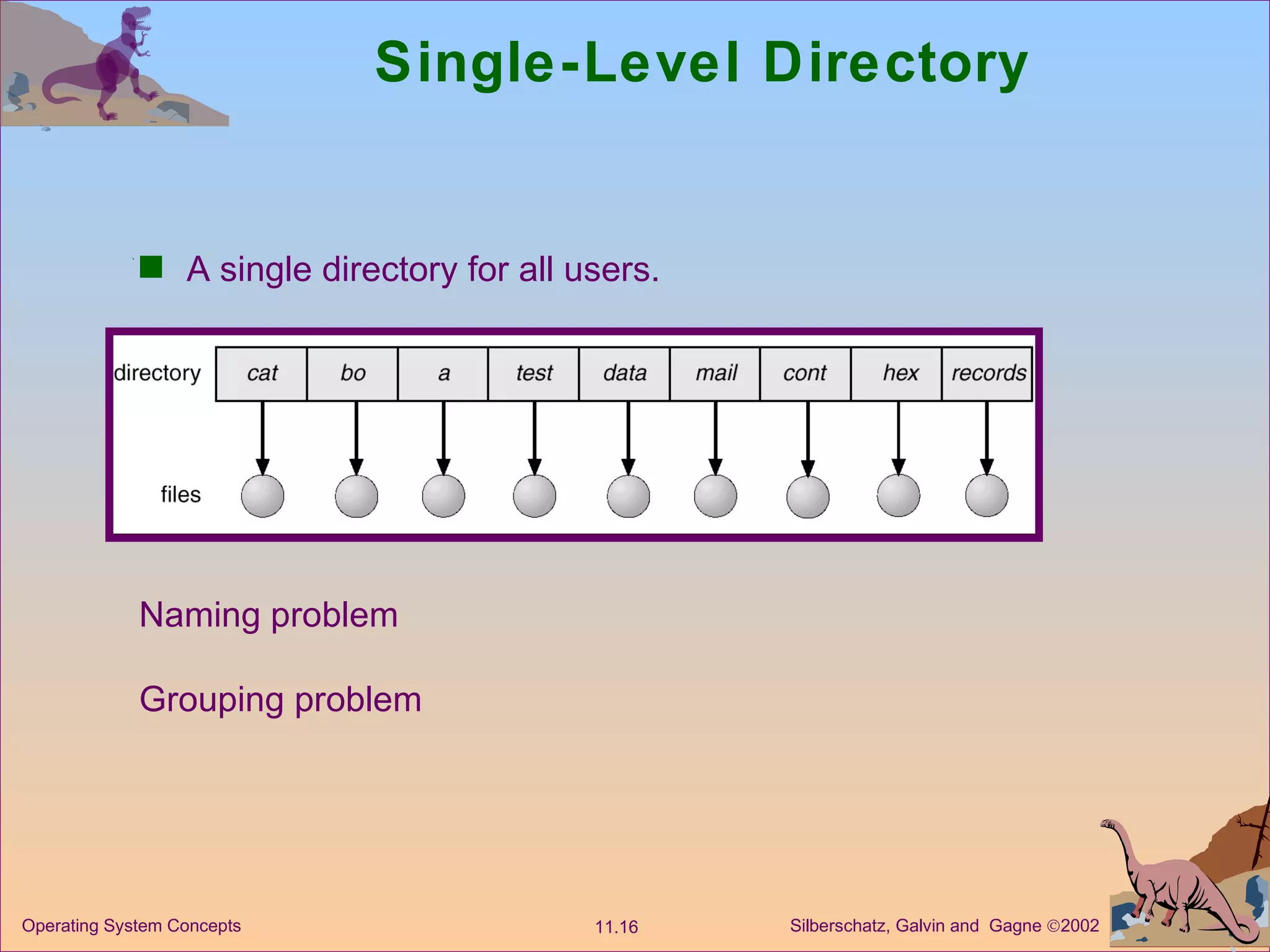
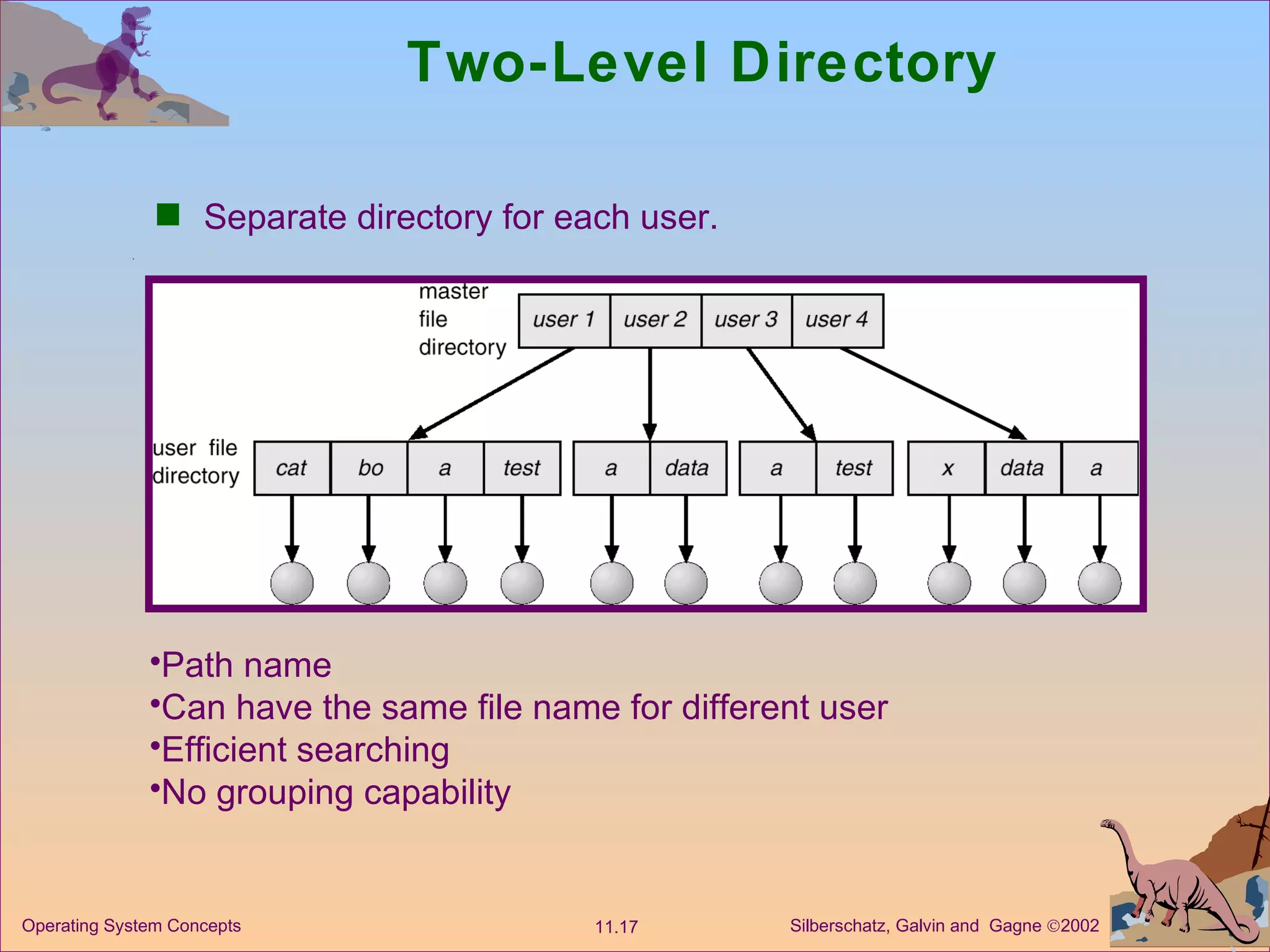
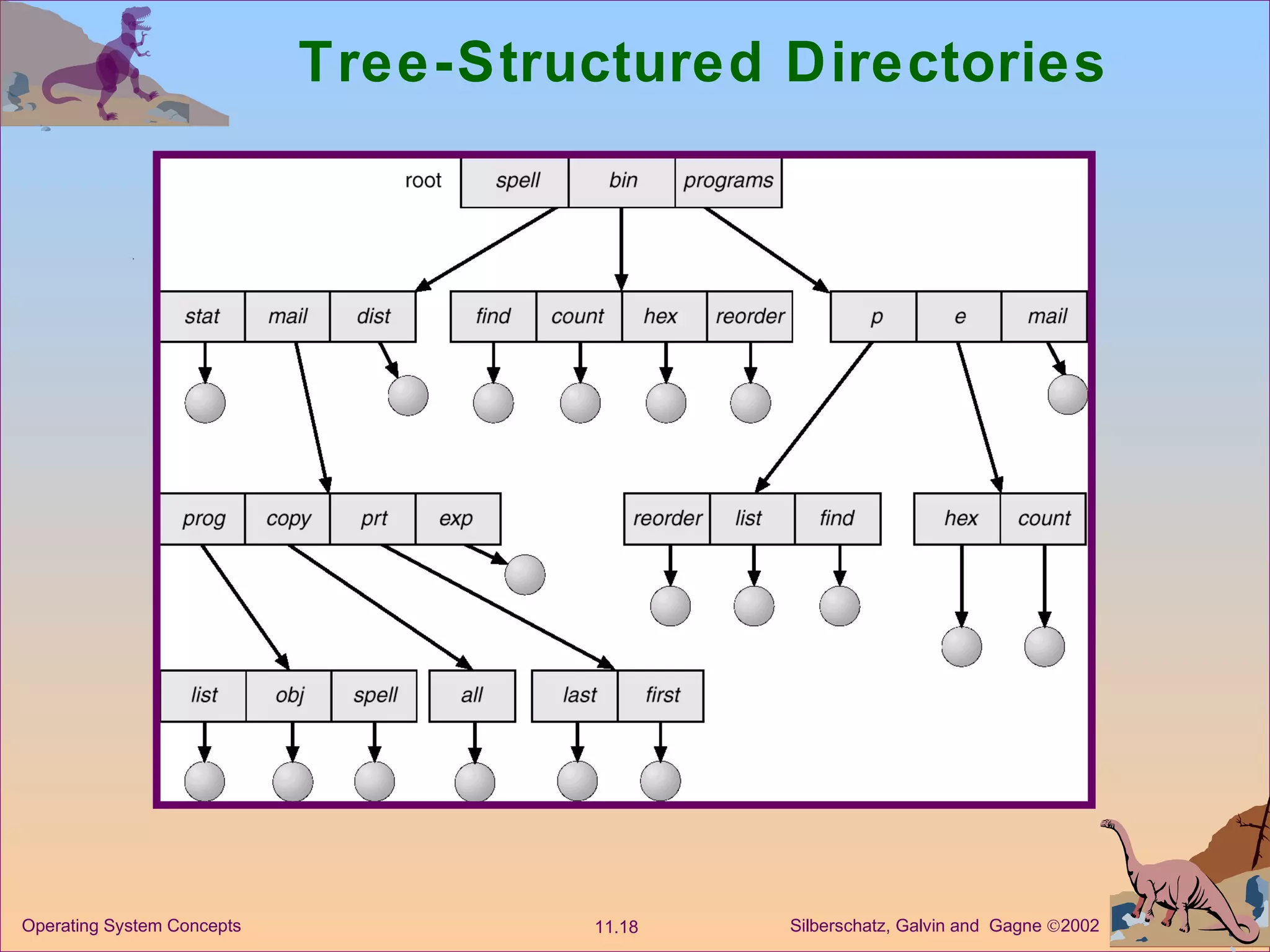
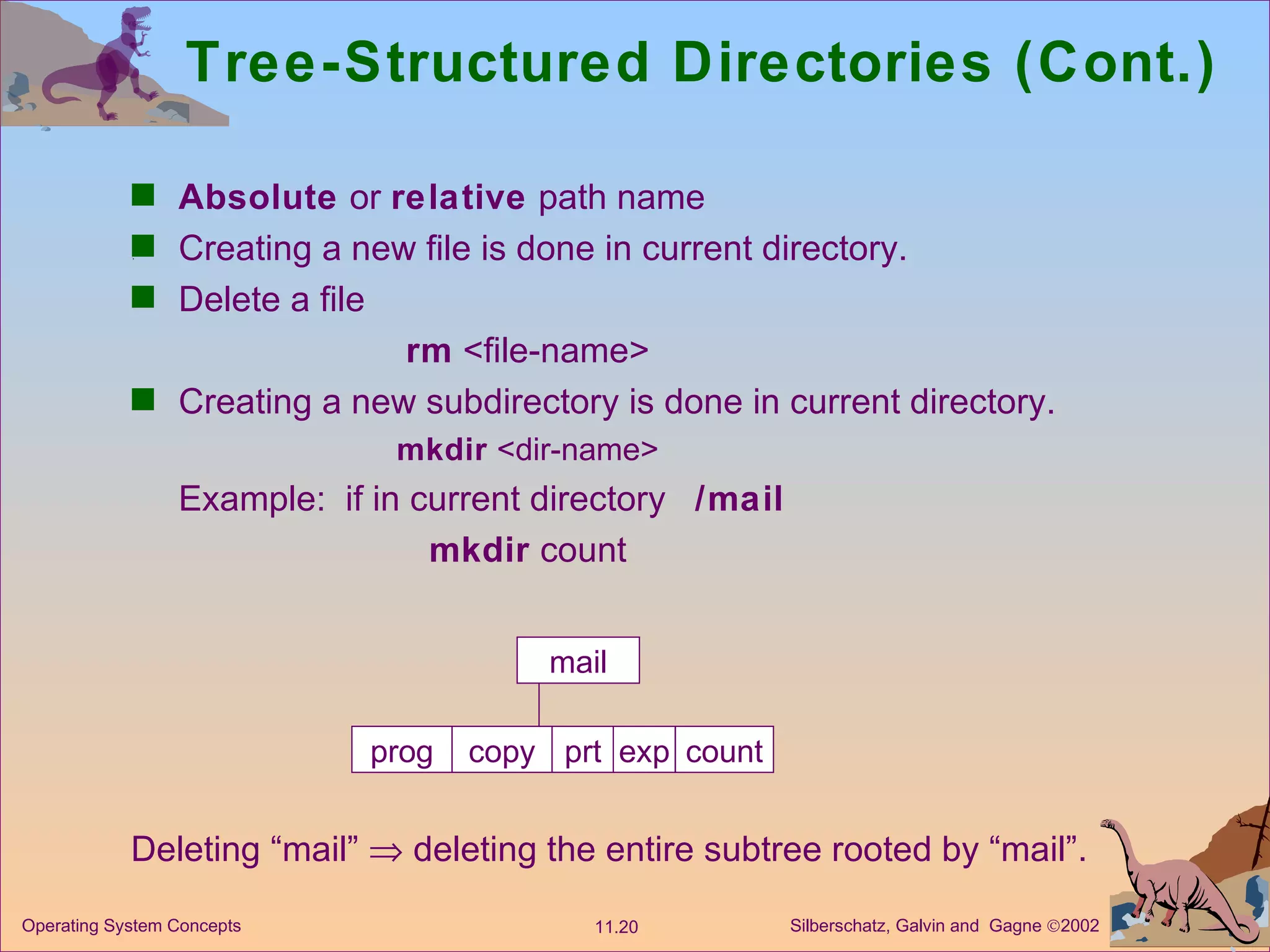
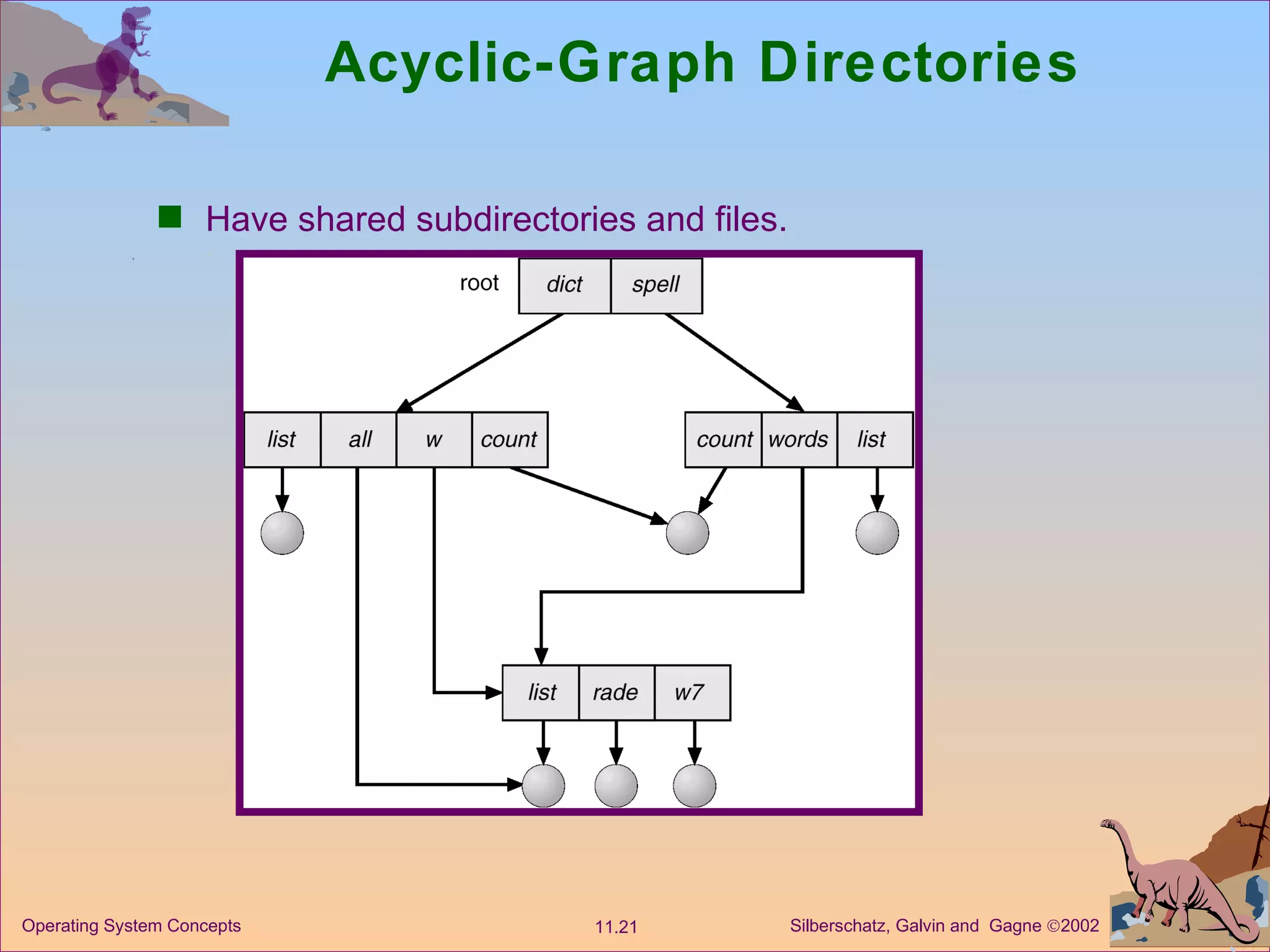
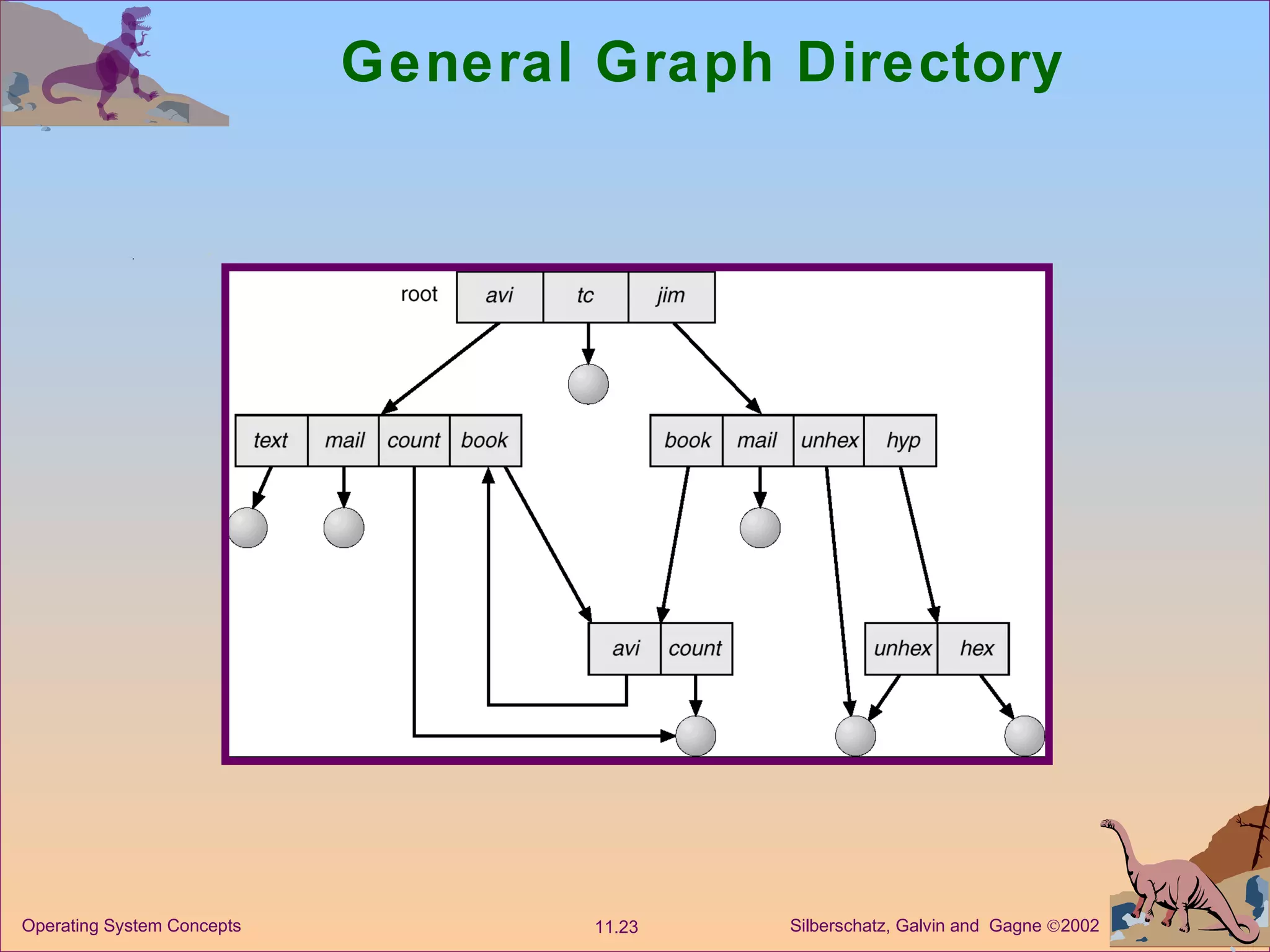
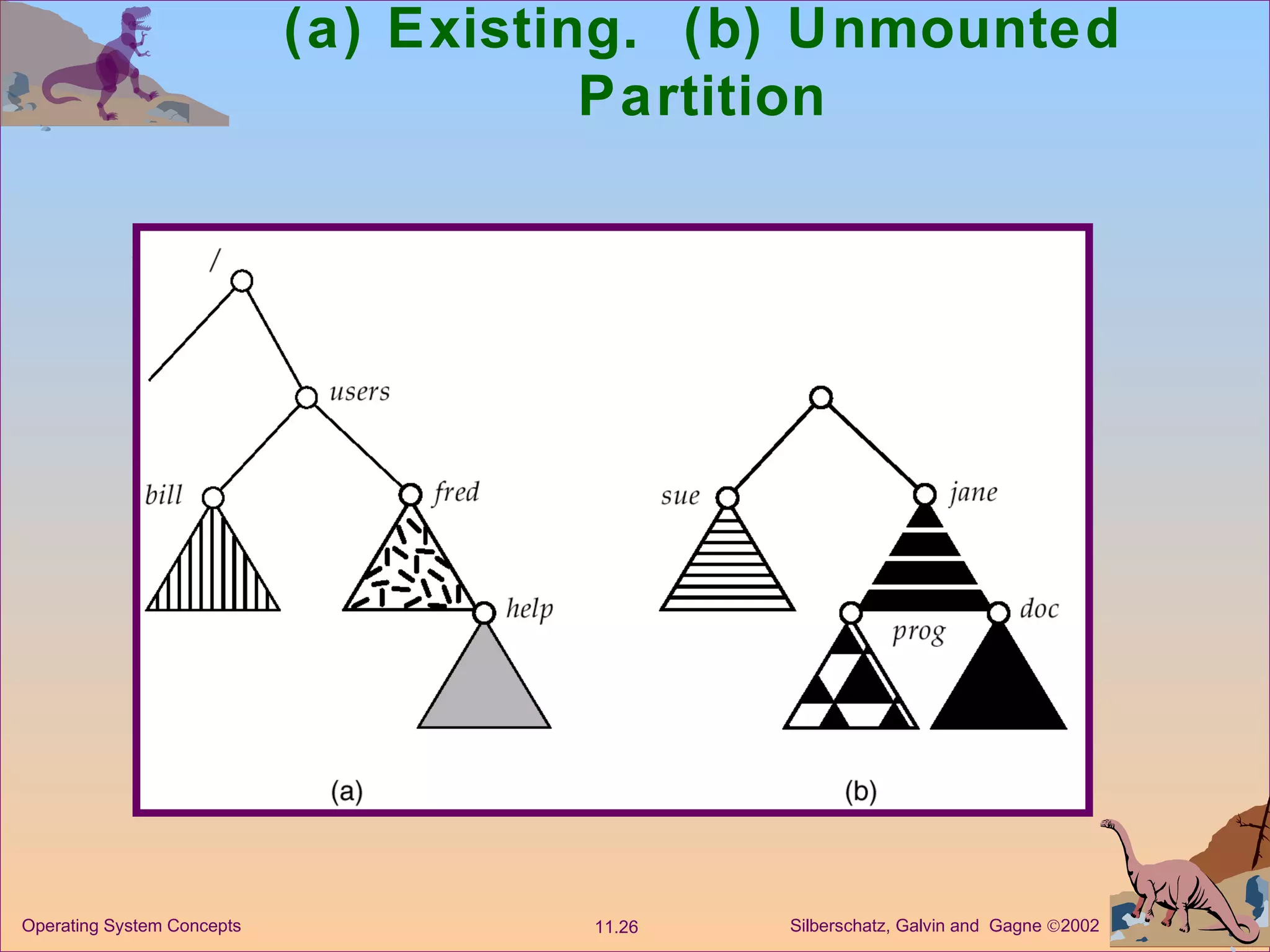
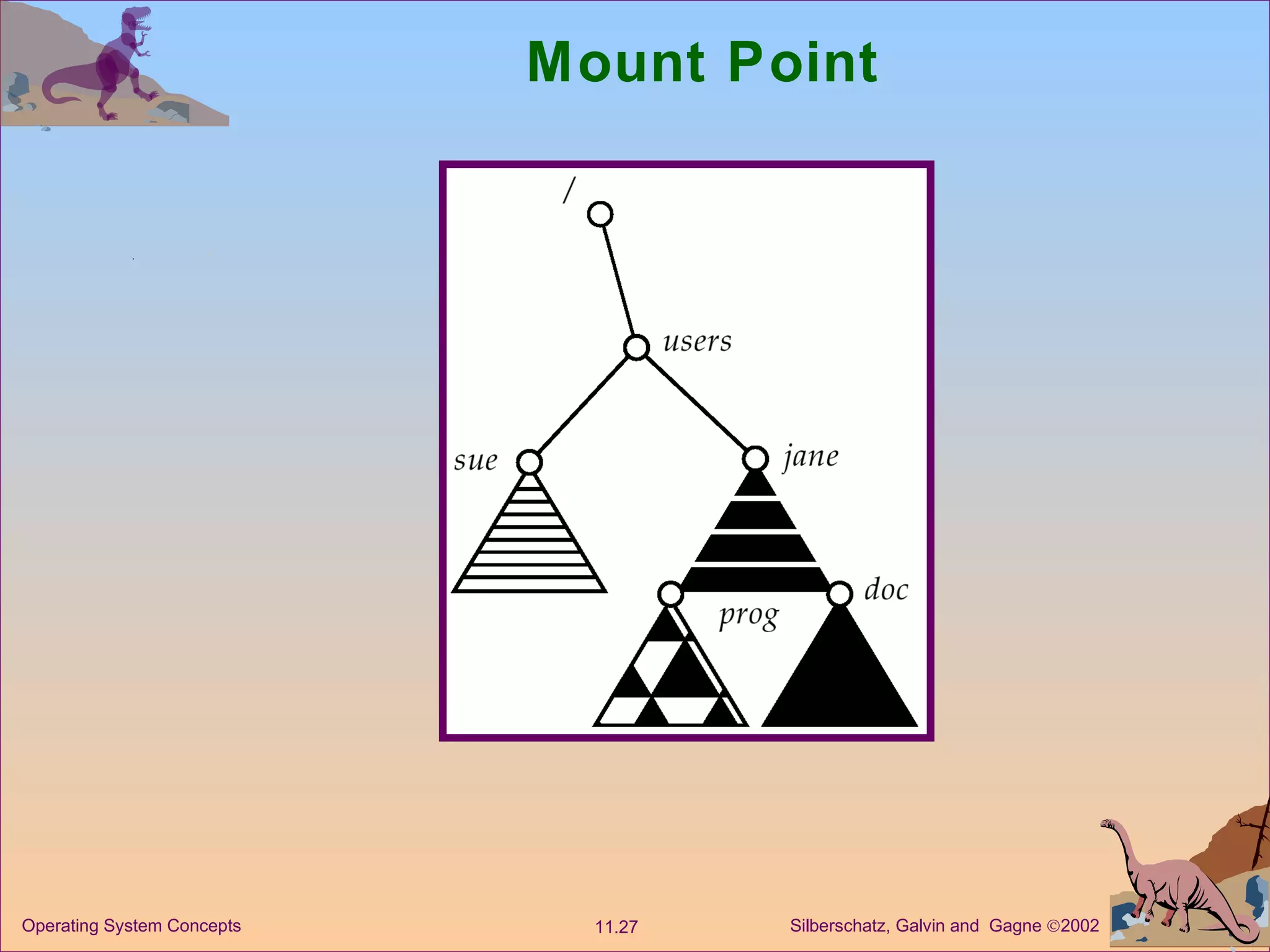
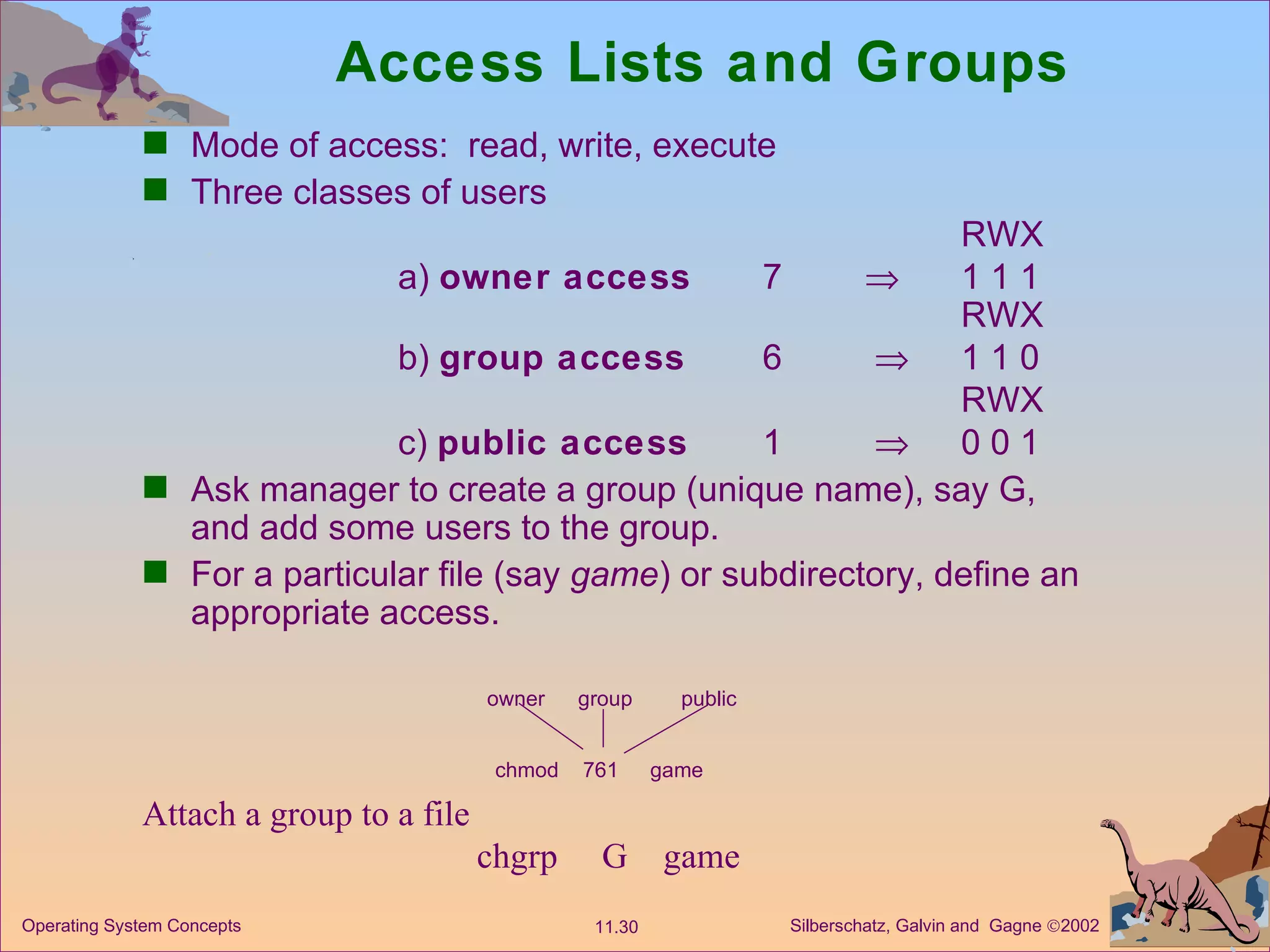
The document discusses various concepts related to file systems including file structure, attributes, operations, access methods, directory structure, mounting, sharing and protection. It describes hierarchical tree-structured directories as the most common organization that allows for efficient searching, grouping of files and use of absolute or relative path names. File sharing across networks can be enabled through various protection schemes and network file systems like NFS.