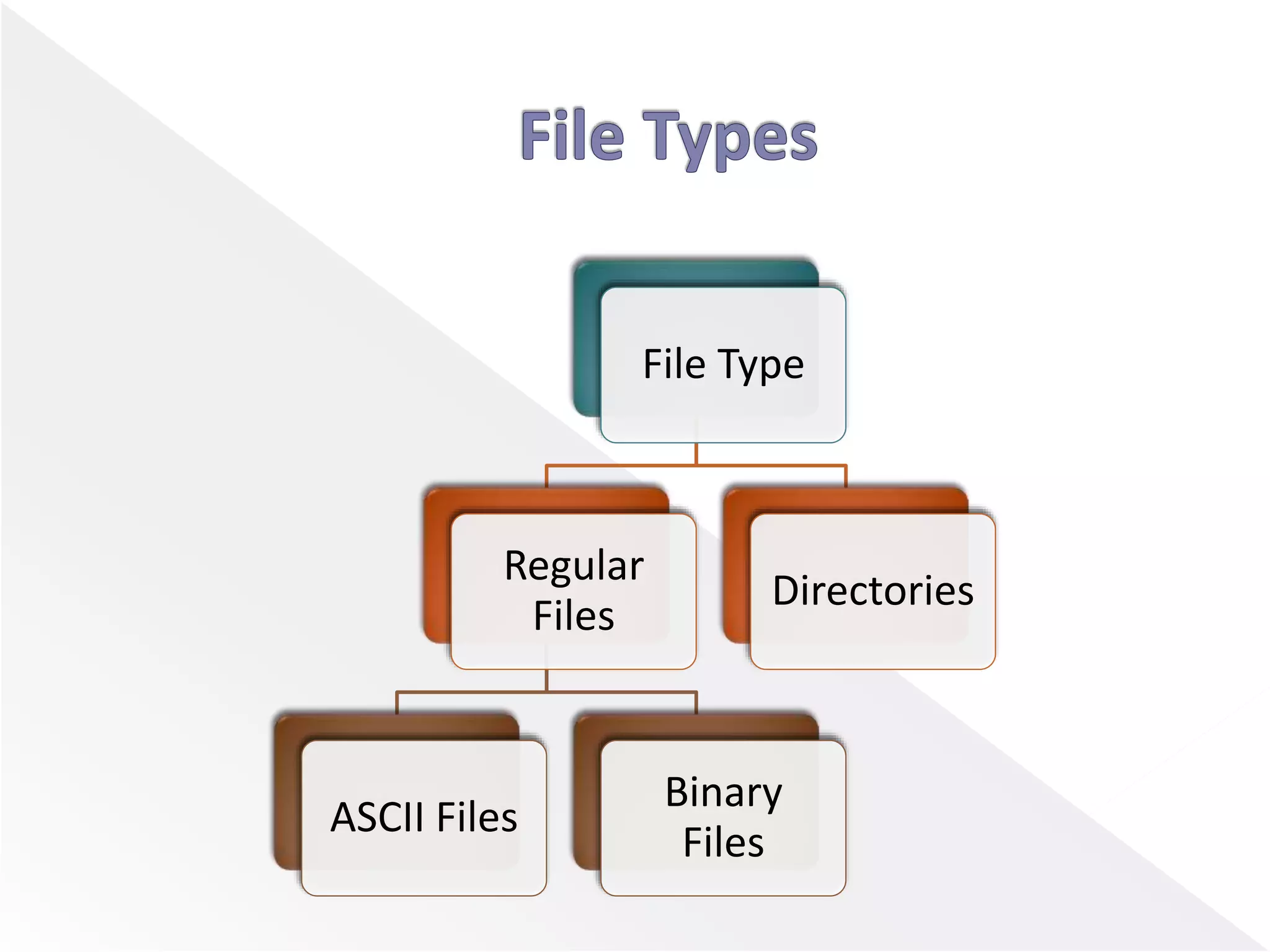
El documento presenta conceptos sobre la gestión de archivos, incluyendo métodos de acceso, tipos de archivos y operaciones de archivos. Se diferencian entre el acceso secuencial y aleatorio, destacando que los archivos de acceso aleatorio son esenciales para aplicaciones como sistemas de bases de datos. También se explican los tipos de archivos, como archivos ASCII y binarios, y las operaciones comunes en la gestión de archivos, como crear, abrir, leer y eliminar archivos.