Embed presentation
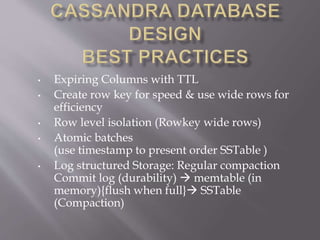
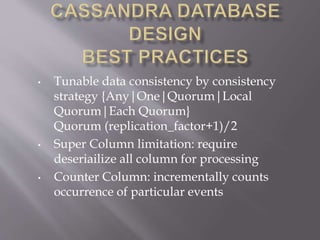
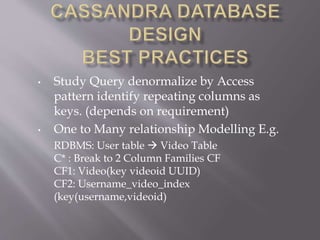
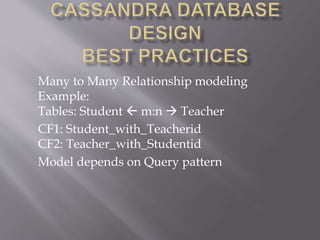
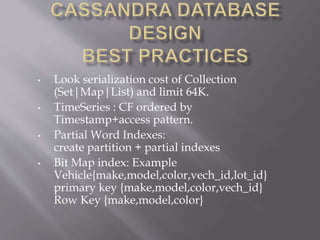
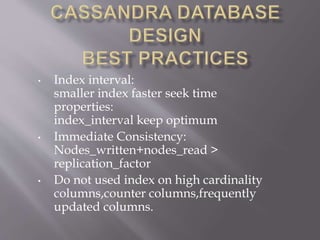
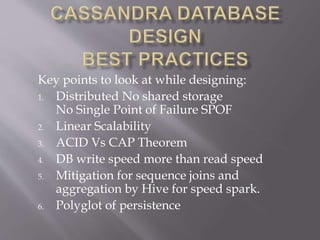
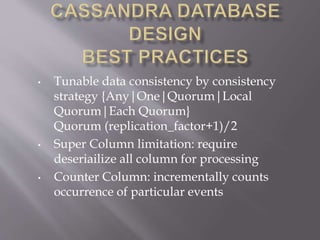
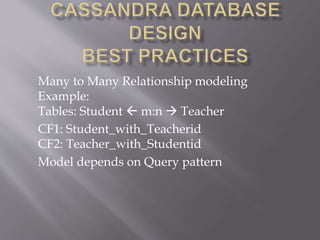
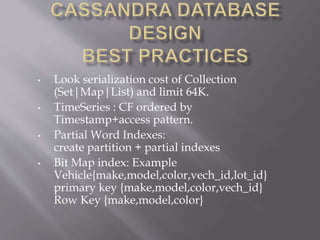
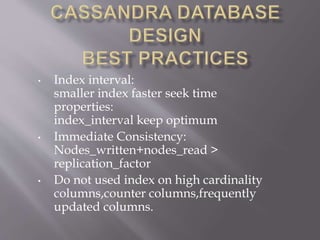
1. Key considerations for Cassandra database design include distributing storage without a single point of failure, linear scalability, and understanding the tradeoffs of consistency models. 2. The document provides tips such as using time-to-live columns, wide rows for efficiency, tunable consistency levels, modeling one-to-many and many-to-many relationships, and indexing strategies. 3. Best practices are outlined like limiting collection sizes, modeling time series data, and avoiding indexes on high-cardinality or frequently updated columns.