This document is a response from EnrollHostel to a request for proposal from Pharmaceutical Research and Manufacturers of America for enterprise risk and audit services. EnrollHostel outlines their audit methodology, which includes assessing compliance, identifying risks, maintaining an audit knowledge repository, creating audit plans and dashboards. Their service delivery approach involves phases such as inception, knowledge transfer, and steady state operations. EnrollHostel also describes their account management structure and technology team to support the audit services.




![EnrollHostel Privileged and Confidential Page 7 of 65
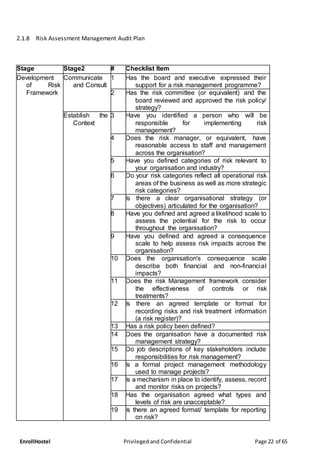
1 PART I – GENERAL INFORMATION
1.1 EXECUTIVE SUMMARY
EnrollHostel is pleased to provide this proposal for Accessing/Auditing Compliance to RISK For School student
from Spain [Europe]. EnrollHostel understands the importance of these services School provides to Students.
EnrollHostel brings to this engagement a significant advantage to Education Sector, in terms of technology
expertise, security, operations architecture, strategy and advisory skills, process maturity and a consistent and
reliable track record providing operational and infrastructure support across multiple technologies.
EnrollHostel also proposes the advantages it brings on board as compared to other MSPs.
1.2 SCOPE OF SERVICES
EnrollHostel understands that School is looking for the following RISK compliance services.
Below is EnrollHostel’s compliance to the scope of services detailed by School in their RFP document:](https://image.slidesharecdn.com/riskmanagementpeelregion-181014230041/85/Risk-management-Consulting-For-Municipality-7-320.jpg)














![4
diverse layers of innovation, the most widely recognized being host-, network-, and application-layer
evaluations.
Directing vulnerability appraisals enable associations to distinguish vulnerabilities in their product and
supporting framework before a bargain can happen. A vulnerability can be characterized in two ways:
• A bug in code or an imperfectioninprogrammingplanthatcan be abusedto cause hurt. Misuse
may happen by means of a verified or unauthenticated aggressor.
• A hole in securitymethodsora shortcomingininteriorcontrolsthat whenmisusedoutcomesin
a security break.
Our dedicated team at EnrollHostel provides Vulnerability evaluations that are intended to yield a
positionedororganizedrundownof aframework'svulnerabilitiesfordifferentsortsof dangers.Usingthis,
we will utilize these evaluations know about security hazards and comprehend they require help
distinguishing and organizing potential issues. By understanding their vulnerabilities, we can plan
arrangements and patches for those vulnerabilities for consolidation with their hazard administration
framework.
The pointof viewof adefenselessnessmayvary,contingentuponthe frameworksurveyed.Forinstance,
a utilityframework,similartopowerand water,may organize vulnerabilitiestothingsthat coulddisturb
administrations or harm offices, similar to cataclysms, altering and psychological oppressor assaults.
Notwithstanding, a data framework (IS), like a site with databases, may require an appraisal of its
powerlessnesstoprogrammersanddifferenttypesof cyberattack.Thenagain,aserverfarmmayrequire
an appraisal of bothphysical andvirtual vulnerabilitiessinceitrequiressecurityforitsphysical office and
digital nearness. This is where we pitch in to provide the best of services and line up the possible cases
and assessments you need.
2.2 EXECUTION PLAN
2.2.1 SERVICE DELIVERY APPROACH
EnrollHostel isof the opinionthatgovernance ismultifacetedwithitsorganizational structure,customer
engagement, relationship models, processes and metrics. When the business and operational
environmentiscomplexthere isagreaterneedforrobustgovernance,aswithoutitthereisincreasedrisk
of shared service and vendor partnership value leakage.
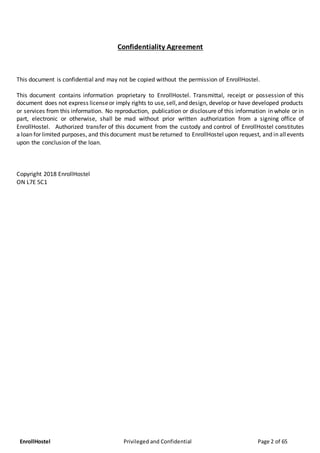
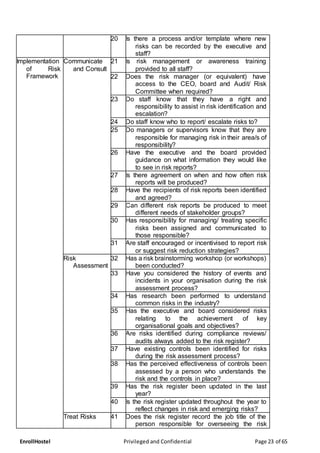
1. Communicate and Consult
2. Establish the context
3. Plan Risk Assessment [Risk identification, Risk Analysis, Risk Evaluation]
4. Risk Treatment
5. Monitor and Review
6. Operate
7. Conform to Standard
BusinesssucceedswhenITrunsbetterandquickerwithreducedcost.OurOperations&SupportServices
is based on ITIL driven Service management framework, coupled with the state of the art tooling and
processes helps IT organizations cut cost, reduce risk and drive down IT Cost. Our mission is to reduce](https://image.slidesharecdn.com/riskmanagementpeelregion-181014230041/85/Risk-management-Consulting-For-Municipality-29-320.jpg)


































![40
4.3.1 USER COUNT AND DEMOGRAPHIC
Approximate 250 users are located at School’s
The followingisahigh-leveloverviewof the on-premiseSchool computingassets:
4.3.1.1 Desktops/Laptops
We are concerned How replaced laptop
4.3.1.2 On-Premise Network/Software hosted
School Network andsoftware hosteddetailsare notknown.
4.3.1.3 Hosted Cloud Environment
It is anticipated that the majority of School’s services will be cloud-based by the end of FY2018. Cloud
details are not known. All software , platform and infrastructure information storing processing or
transmittingRISK informationisnotknown[ Dependingonhow manyapplicationswe needtocheckthe
amount of work may vary]
4.3.1.4 Legacy Business Applications
Details not known.
4.3.1.5 3rd Party Vendors
We wouldneed to understandthe SLAs whichthird party vendorsare on with respect to
handlingof RISK informationbeingprocessed,stored or transmitted.](https://image.slidesharecdn.com/riskmanagementpeelregion-181014230041/85/Risk-management-Consulting-For-Municipality-65-320.jpg)