The document explains the bisection method for finding roots of equations, which involves selecting two initial values that bracket a root and successively halving the interval to locate the root. It outlines the merits of the method, such as guaranteed convergence and simplicity, alongside its demerits, including slow convergence and limitations regarding discontinuity and complex roots. A numerical example and MATLAB code are provided to illustrate the implementation of the bisection method.


![Example Numerical
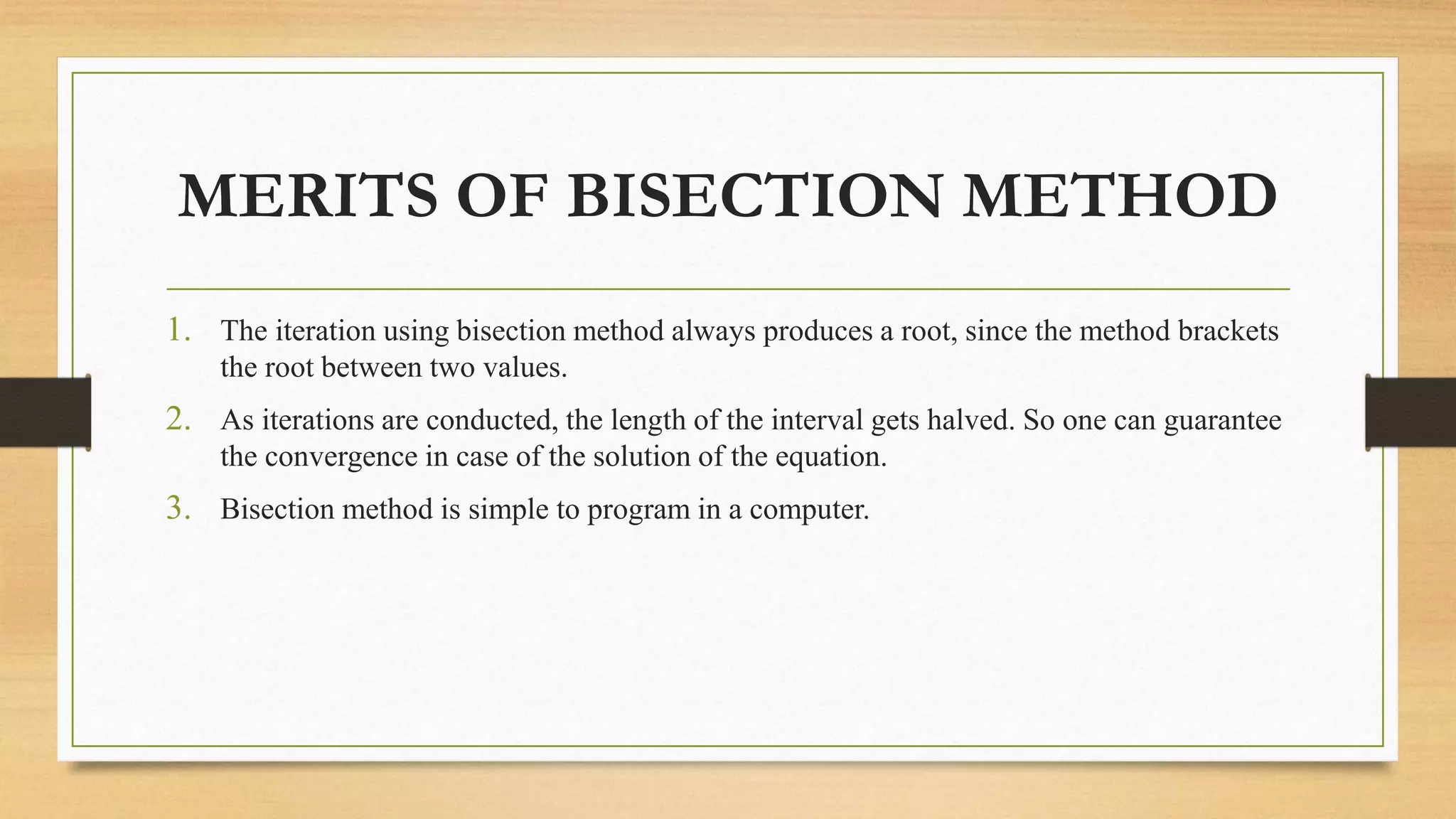
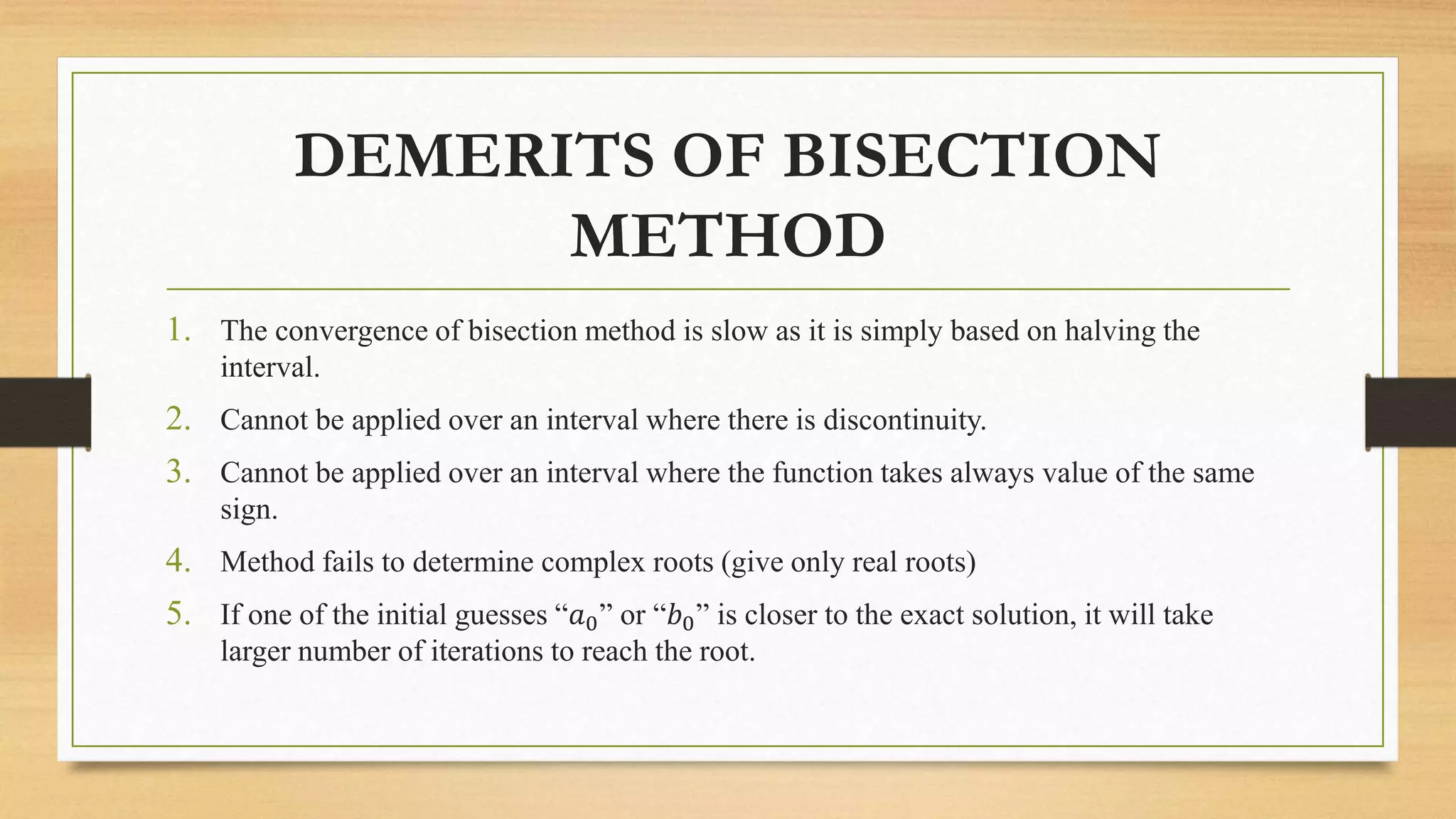
So replace 𝑥1with 𝑥2,
𝐼𝑛𝑡𝑒𝑟𝑣𝑎𝑙 𝑤𝑒 𝑐𝑜𝑛𝑠𝑖𝑑𝑒𝑟 𝑖𝑠
𝑥0 = 1 , 𝑥1 = 1.5 i.e [1,1.5]
𝑥2 =
𝑥0+𝑥1
2
=
1+1.5
2
= 1.25 As f(
1.25)= 2.875 i.e F(1.25)>0
𝑥3 =
𝑥1+𝑥2
2
=
1+1.25
2
= 1.125 As f(
1.125)= -0.2011 i.e F(1.125)<0
𝑥4 =
𝑥2+𝑥3
2
=
1.125+1.25
2
= 1.187500
As f(1.187500)= 0.237061
i.e. F(1.187500)>0
𝑥5 =
𝑥3+𝑥4
2
=
1.125+1.187500
2
= 1.156250
As f(1.156250)= 0.014557
i.e. F(1.156250)>0
X F(x) Up
dat
e
Val
ue
1 -1
2 9
1.5 2.875 𝑥2
1.25 0.703125 𝑥2
1.125 -0.2011 𝑥1
1.187500 0.237061 𝑥2
1.156250 0.014557 𝑥2
1.140625 -0.094143 𝑥1
1.156250 0.040003 𝑥2](https://image.slidesharecdn.com/lecture7bisection-210324100745/75/Bisection-9-2048.jpg)
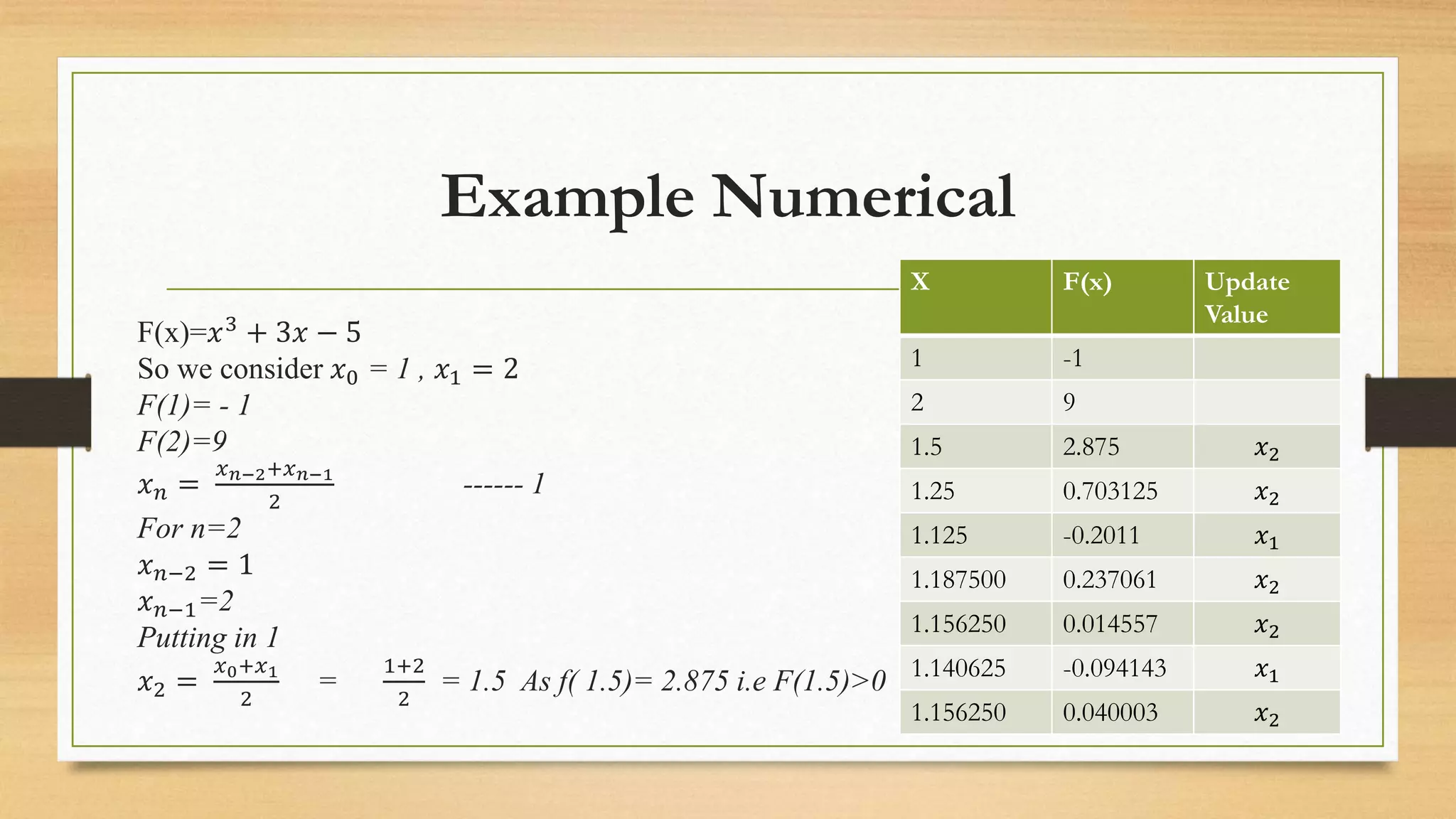
![Matlab Code
function_x=@(x) x.^3+3*x-5;
x1=1;
x2=2;
figure(1)
fplot(function_x,[x1 x2],'b-')
grid on
hold on
x_mid = (x1 + x2)/2;
iterate=1;
%fprintf('%f',abs(- 4))
%while
abs(myfunction(x_mid))>
0.01
while abs(x1 - x2) > 0.01 %or
you can change it to number
of iterations, it can be any
condition
if
(function_x(x2)*function_x(x
_mid))<0
x1=x_mid;
else
x2=x_mid;
end
x_mid = (x1+x2)/2;
%fprintf('The root of data is
%gn' , x_mid);
iterate=iterate+1;
fprintf('%d Approximation
Bracket is [%f,%f] gives
function value %f,%f
respectively and, mid value is
%fn',iterate,
x1,x2,function_x(x1),function
_x(x2),x_mid);
end
plot(x_mid,function_x(x_mid)
,'r')
fprintf('The root of data is
%fn and iteration is %dn' ,
x_mid,iterate);](https://image.slidesharecdn.com/lecture7bisection-210324100745/75/Bisection-10-2048.jpg)
