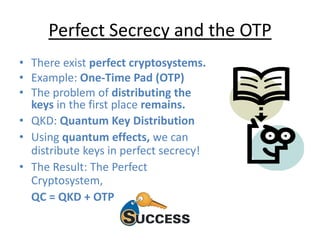
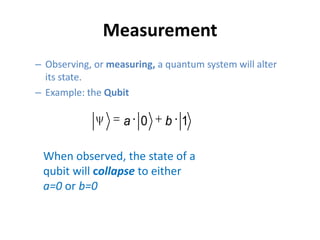
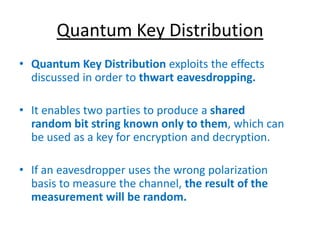
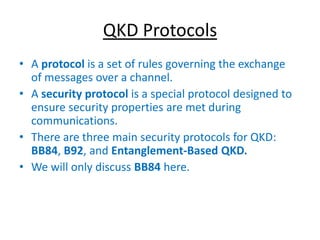
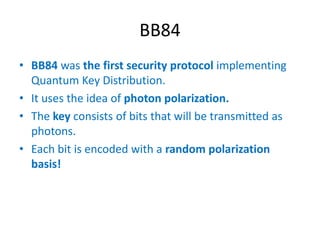
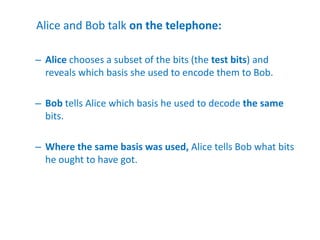
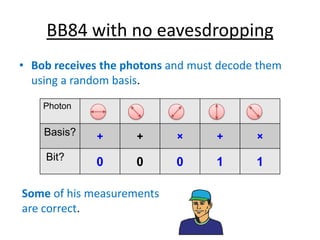
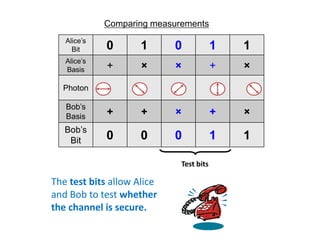
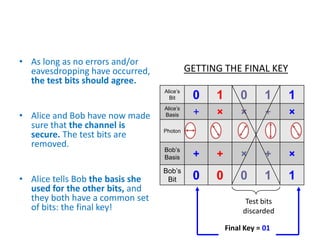
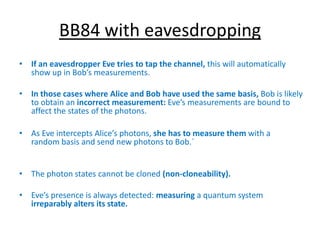
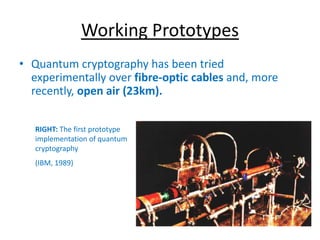
This document provides an overview of quantum cryptography. It introduces key concepts like the Heisenberg uncertainty principle, photon polarization, and the need for quantum cryptography due to potential threats from quantum computers. The document describes how quantum key distribution works using protocols like BB84 to generate and test secure encryption keys between two parties by detecting any eavesdropping. It notes that working prototypes have been implemented over fiber optic cables and open air.
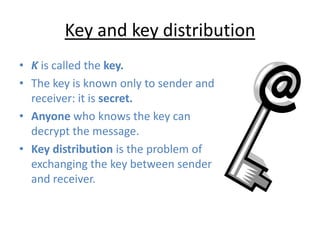
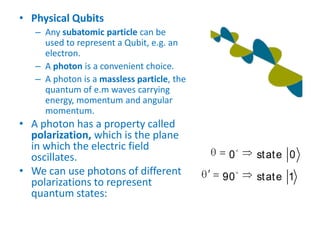
![Basic idea in cryptography
• Cryptography: “the coding
and decoding of secret
messages.”
• The basic idea is to modify
a message so as to make it
unintelligible to anyone but
the intended recipient.
• For message (plaintext) M,
e(M, K)
encryption - ciphertext
d[e(M, K), K] = M
decryption
• Cryptosystem (Cipher
System) – method of
disguising messages so that
only certain people can
read them
• Cryptography – Art of
creating and using
Cryptosystems
• Cryptanalysis – Art of
breaking Cryptosystems
• Cryptography – study of
Cryptography and
Cryptosystems](https://image.slidesharecdn.com/quantumcryptography-130913005611-phpapp01/85/Quantum-cryptography-6-320.jpg)