Embed presentation
Download to read offline


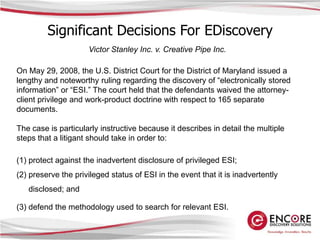
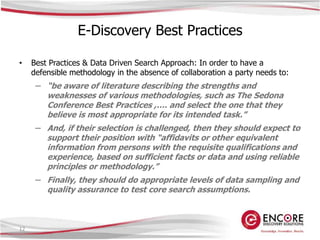
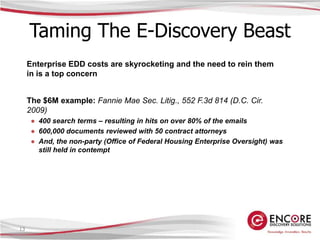
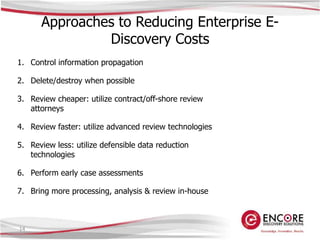
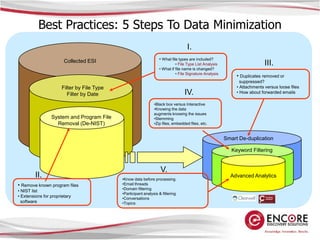
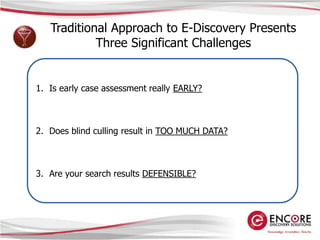
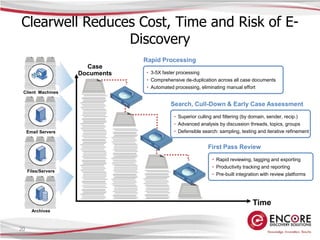
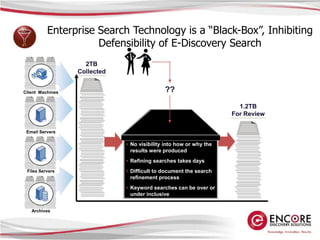
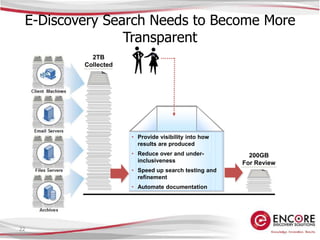

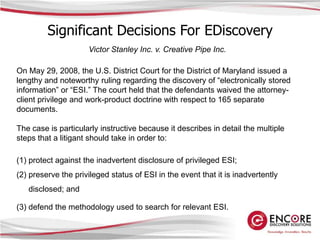
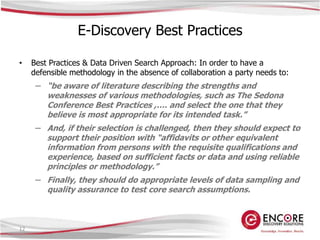
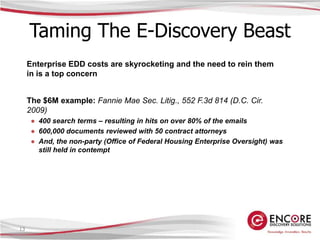
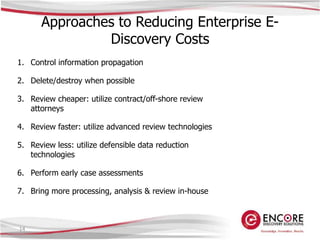
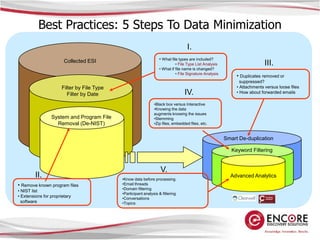
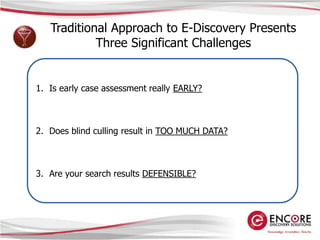
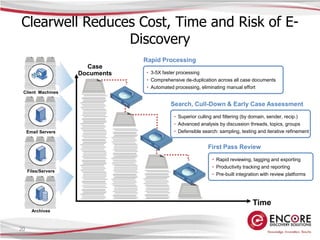
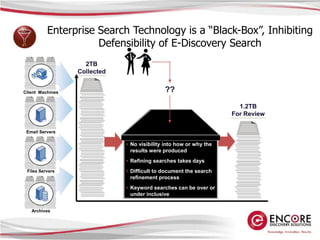
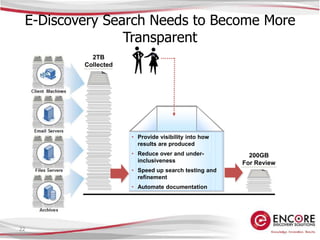
The document discusses data minimization techniques for reducing costs in electronic discovery. It outlines 5 steps to data minimization including filtering by file type and date, removing system/program files, deduplication, keyword filtering, and advanced analytics. The document also notes that utilizing these strategies can reduce collected data volumes by 40-80%, allowing cases to be assessed virtually as soon as data is collected and lowering processing costs. It promotes the use of transparent search technologies to ensure discovery searches are defensible.