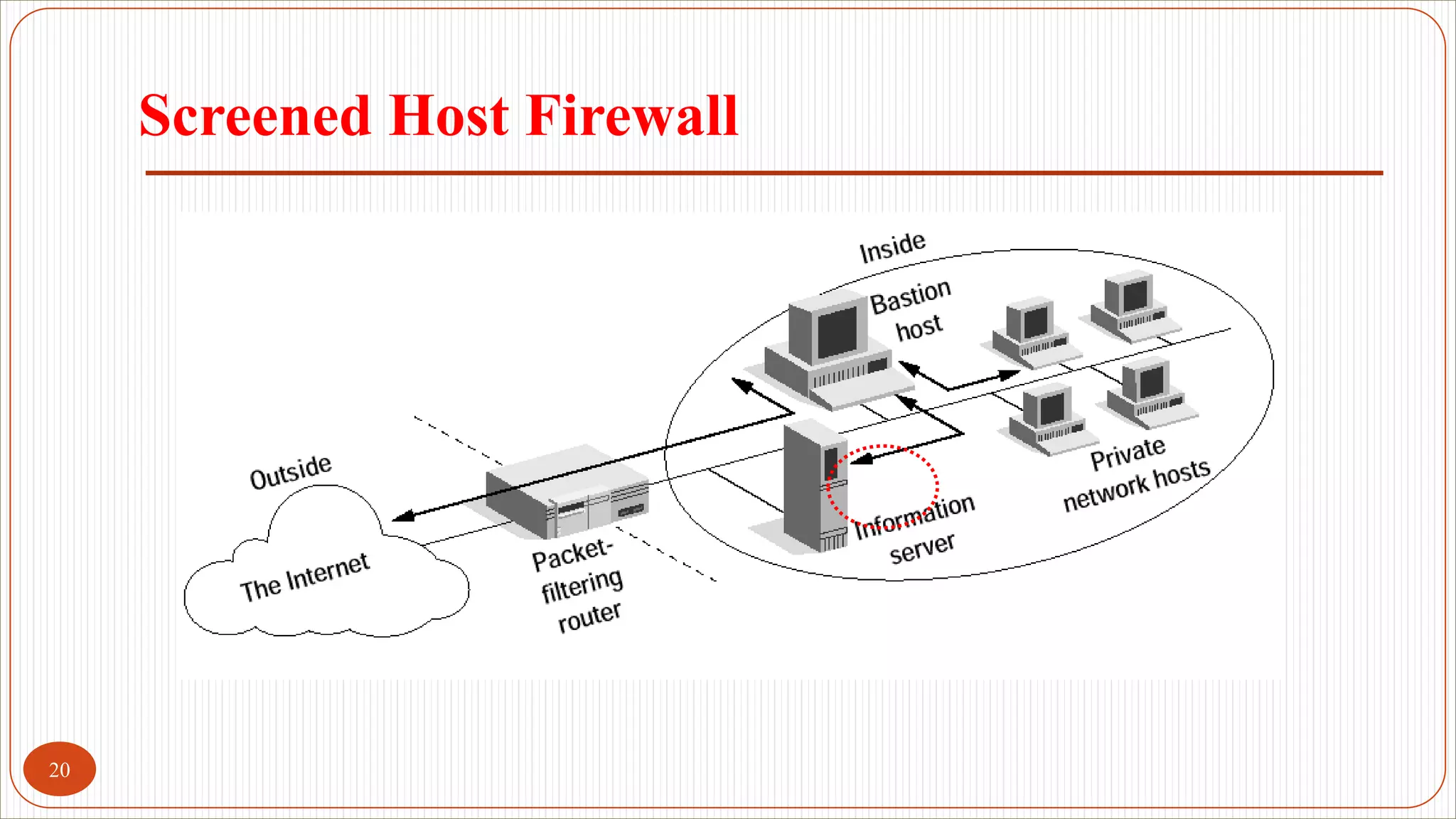
A firewall is a system designed to restrict access between networks and protect private network resources. It imposes a gateway machine between the outside world and private network that software uses to decide whether to allow or reject incoming traffic. Firewalls implement security policies at a single point and monitor security events while providing strong authentication and allowing virtual private networks on a specially hardened operating system. Common types include packet filtering routers, application-level gateways, and circuit-level gateways, with hybrid firewalls combining techniques.




















![[9] Firewall.pdf](https://image.slidesharecdn.com/9firewall-221225213241-c8a89058/75/9-Firewall-pdf-26-2048.jpg)