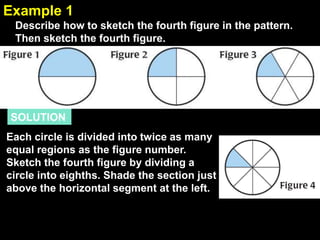
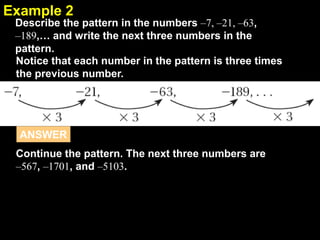
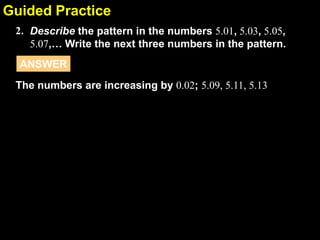
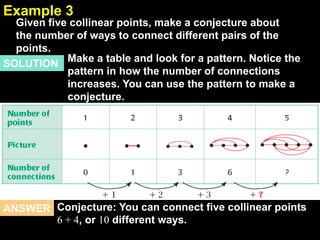
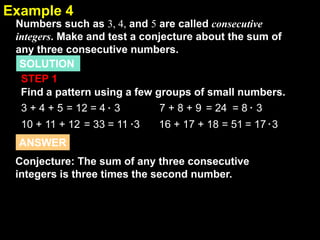
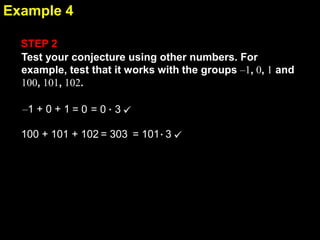
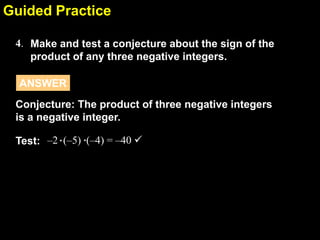
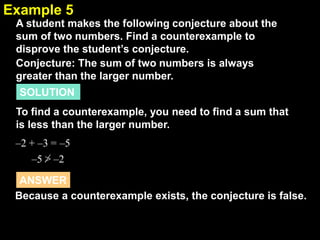
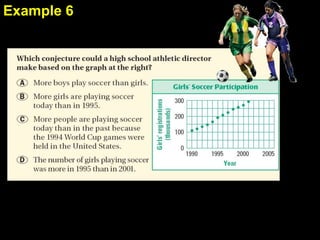
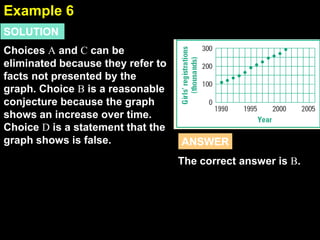
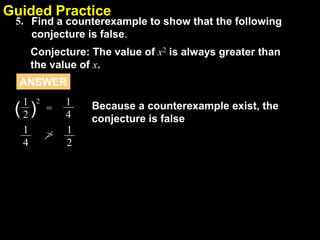
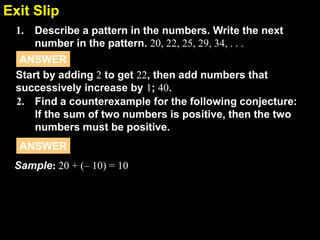
1. The document provides examples and explanations of using inductive reasoning to make and test conjectures based on patterns in numbers, shapes, and graphs. Examples include describing patterns, writing subsequent terms, finding counterexamples, and summarizing relationships between variables.
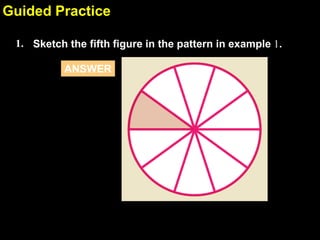
2. Guided practice questions ask students to continue patterns, make conjectures, find counterexamples, and describe relationships based on provided examples.
3. The document aims to teach students how to use inductive reasoning by looking for patterns in examples and testing conjectures. Students practice these skills on guided problems with feedback provided.