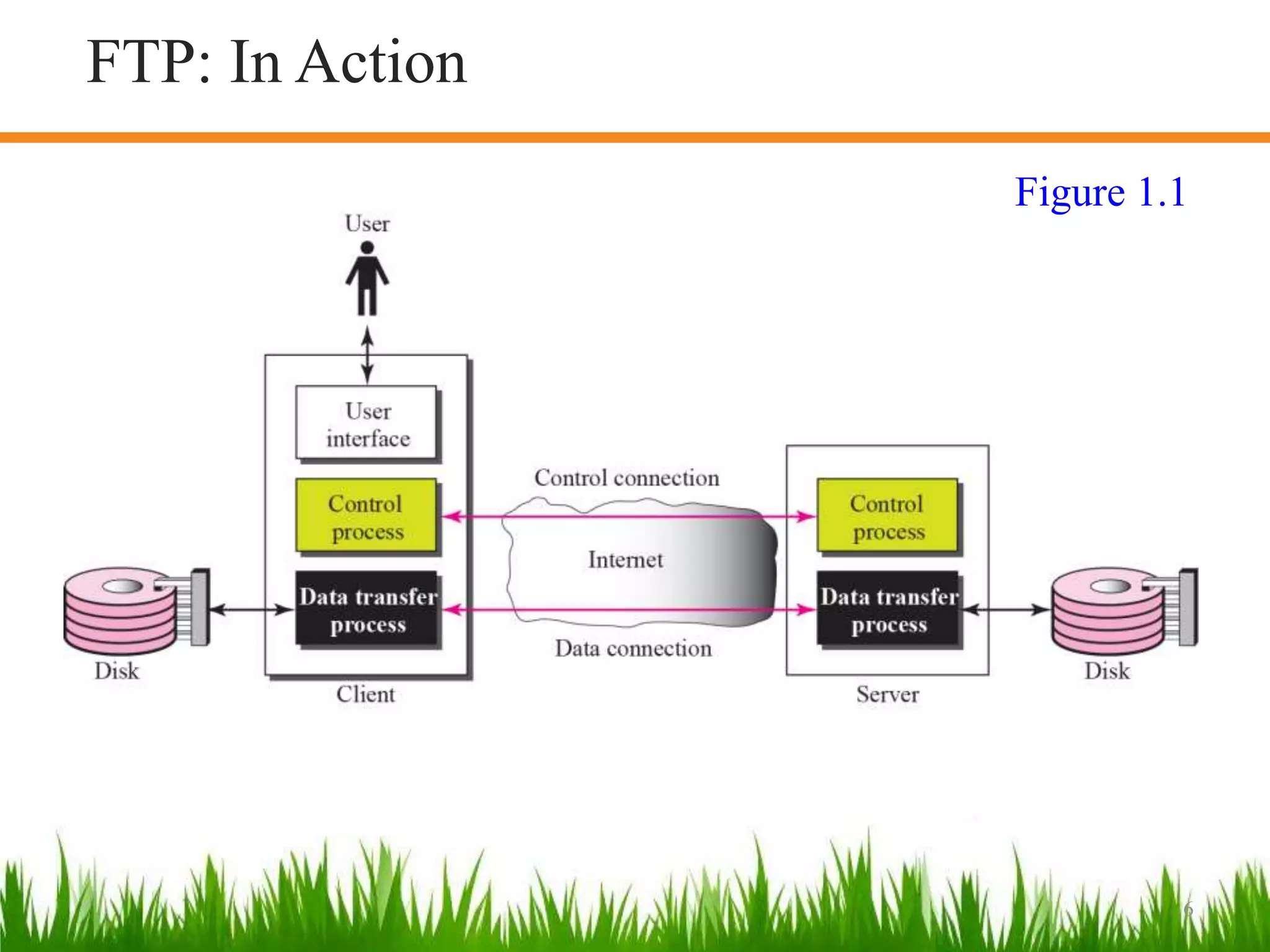
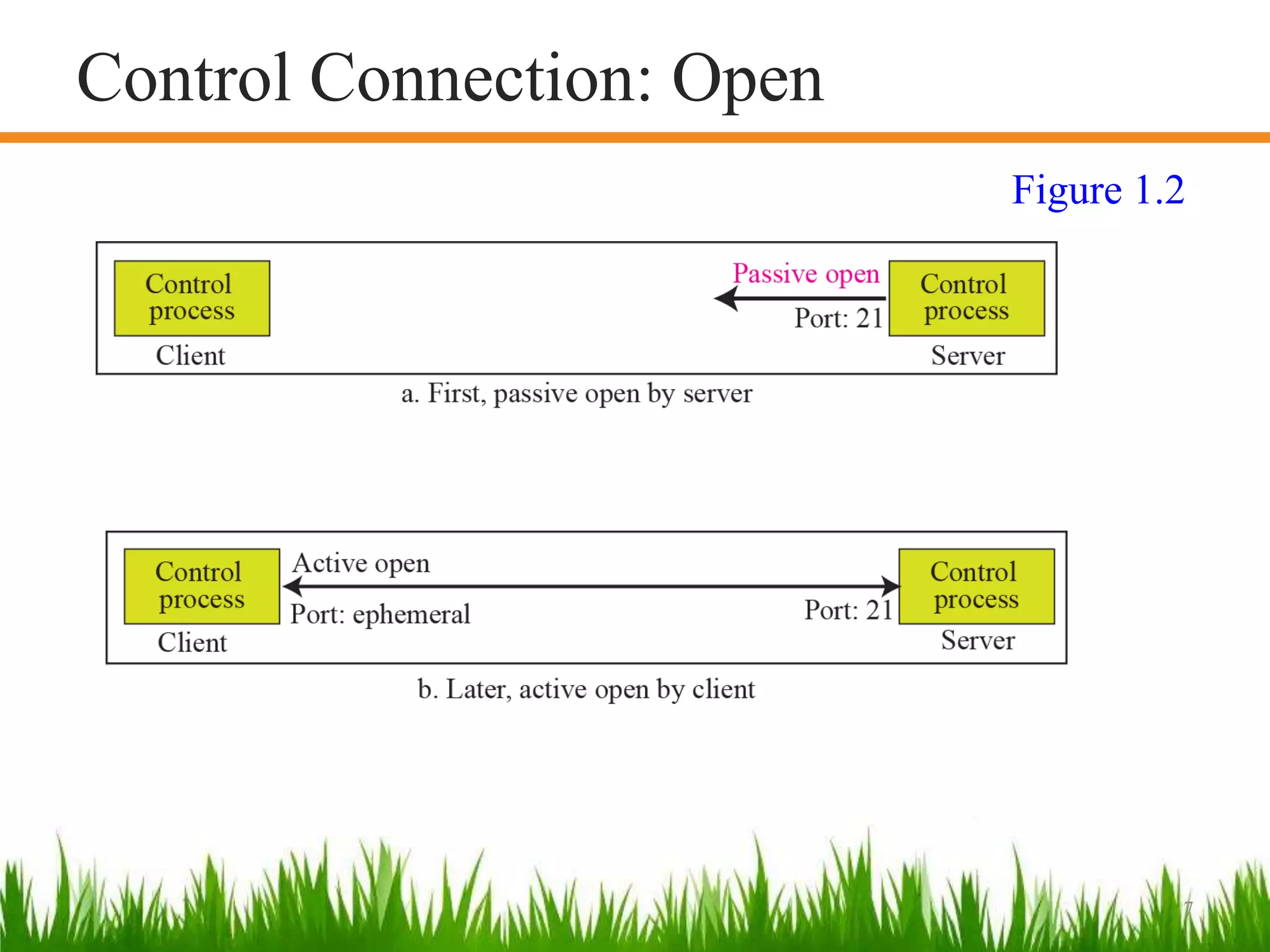
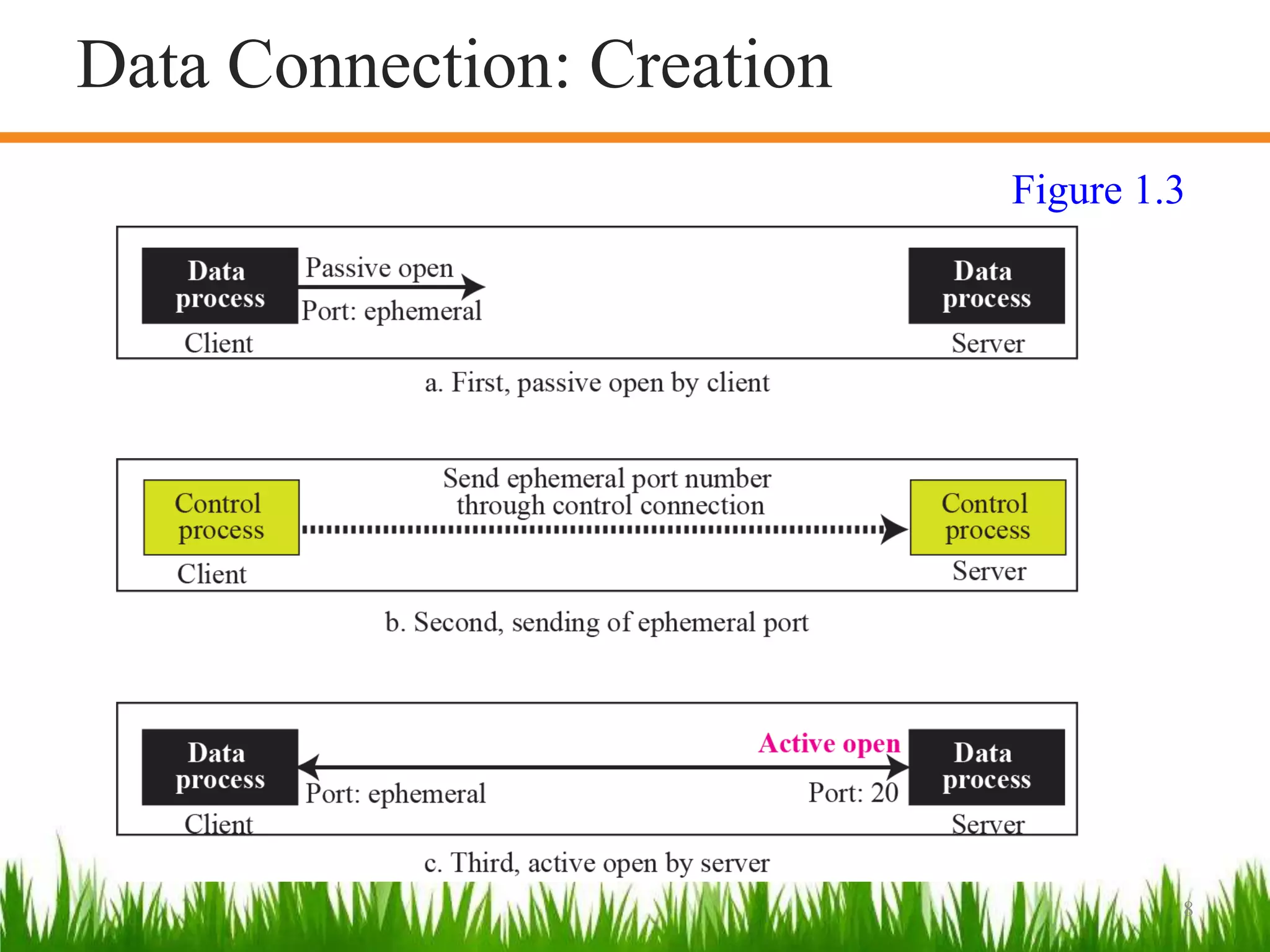
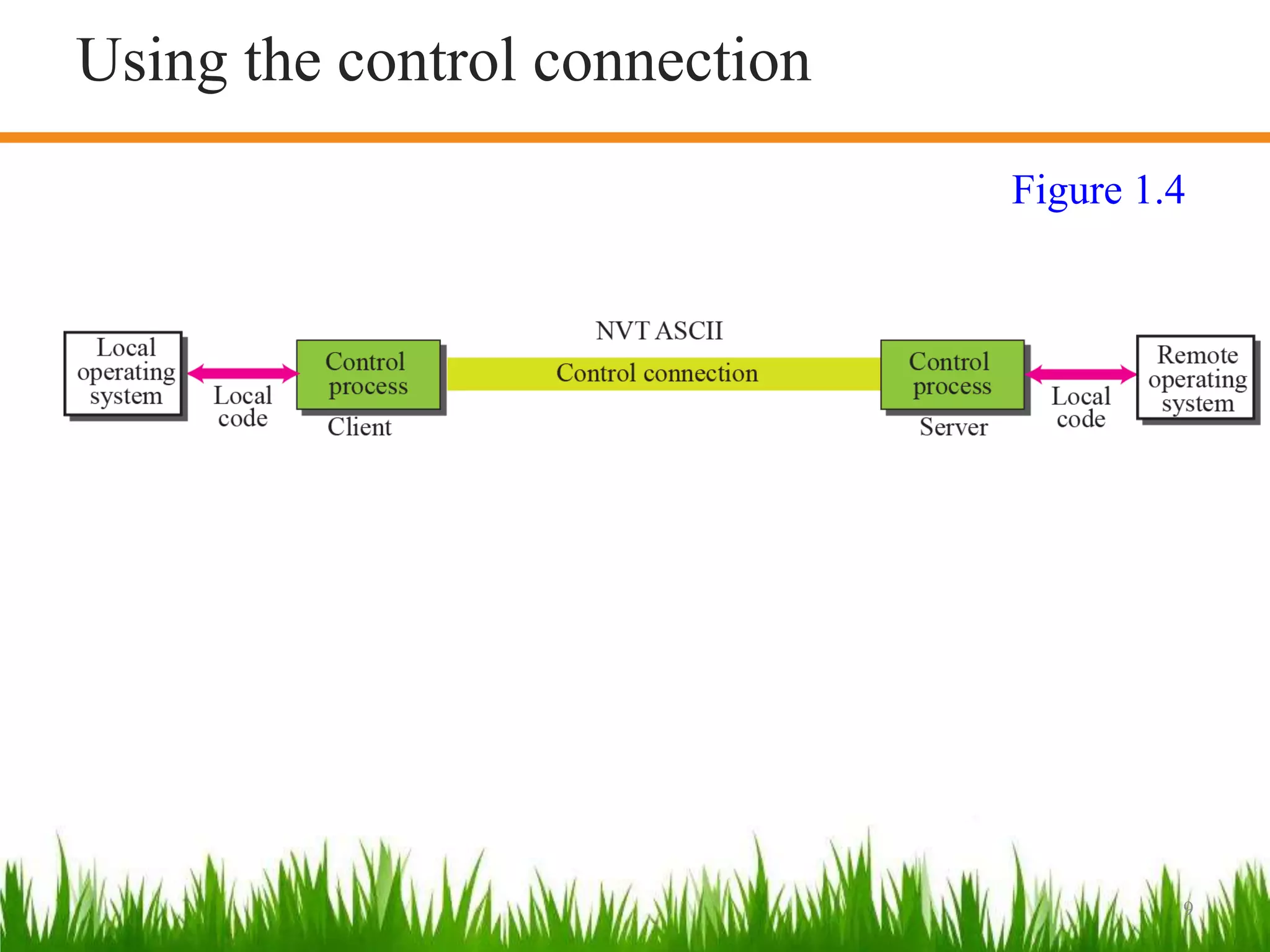
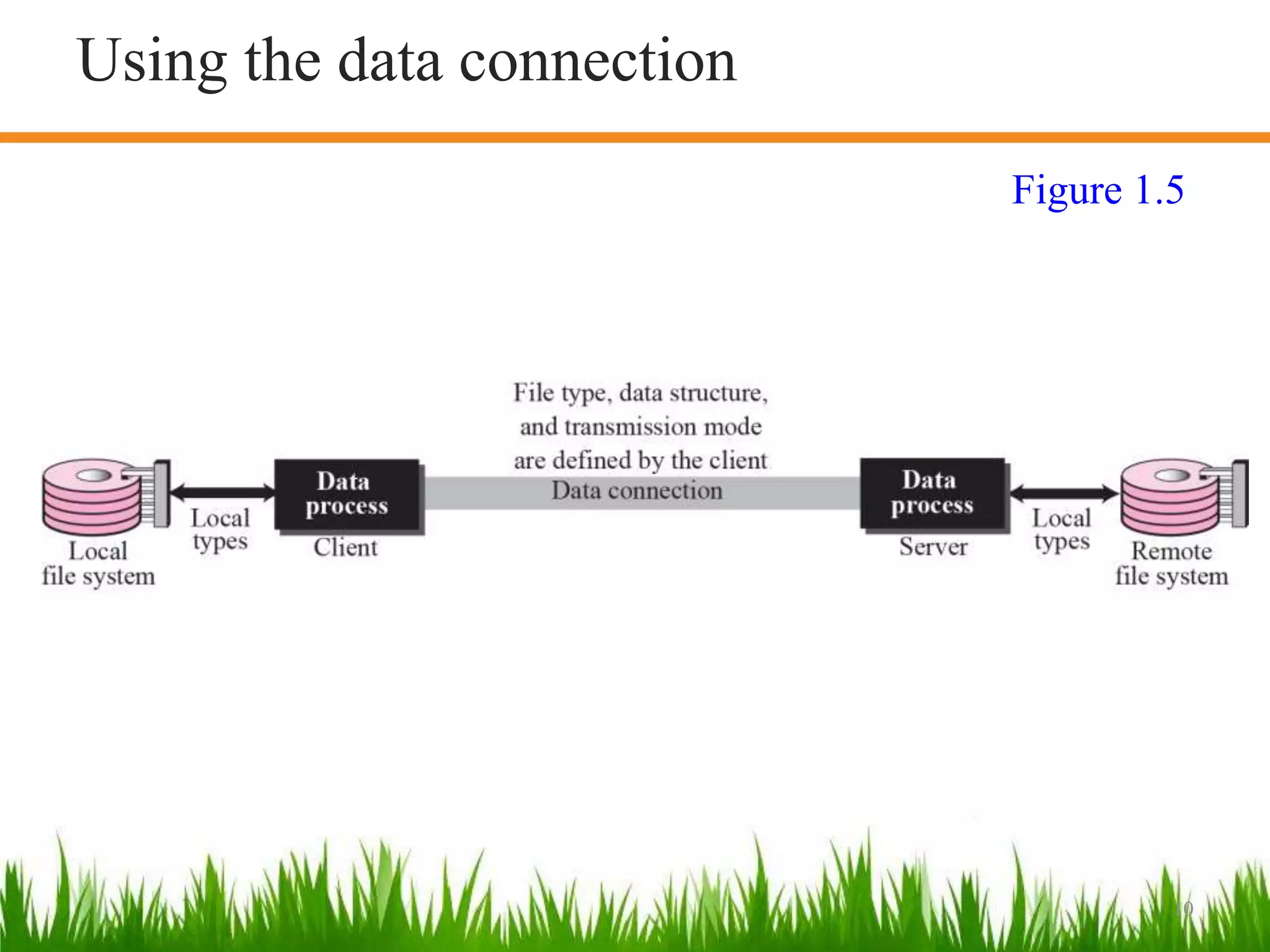
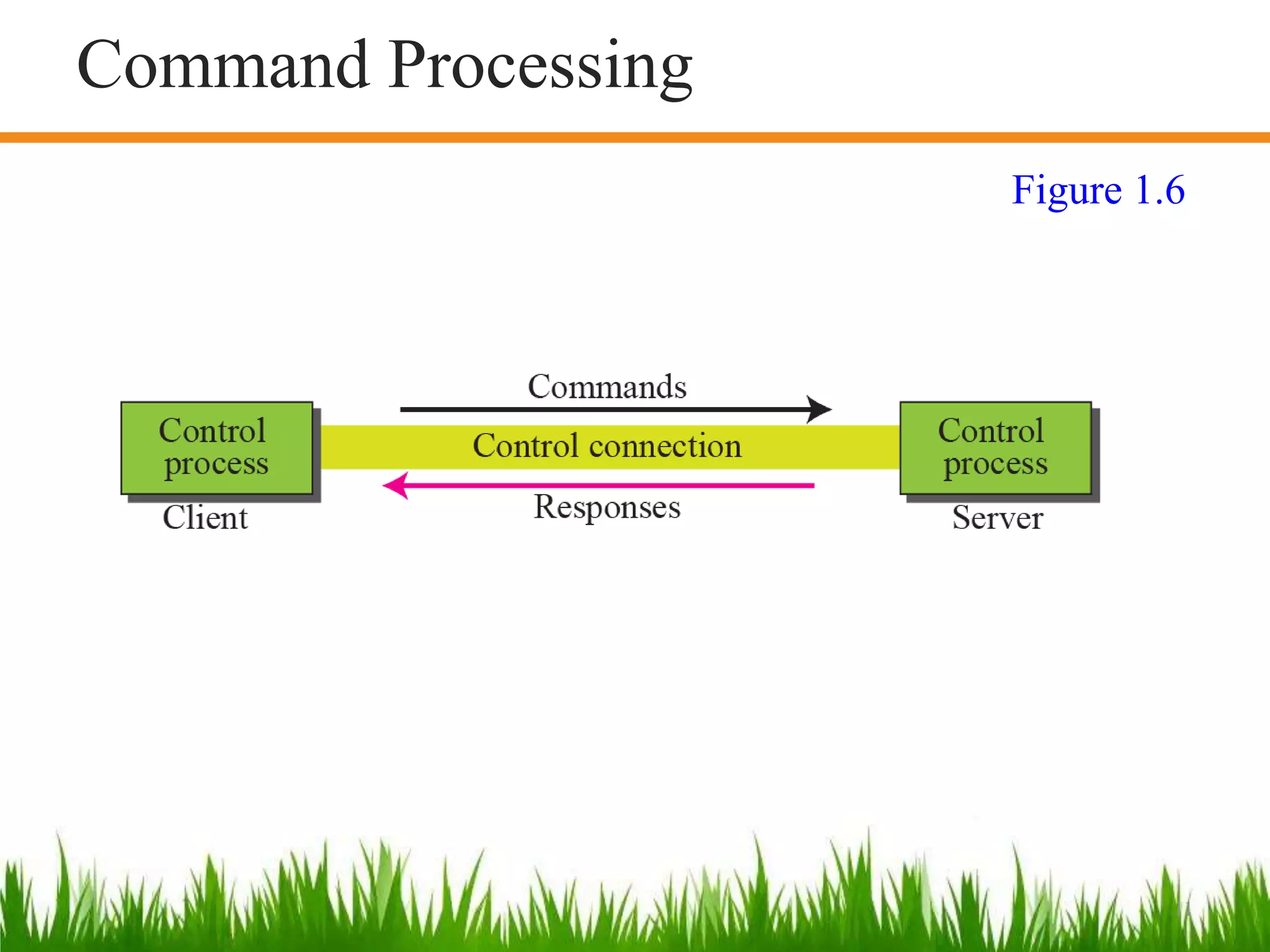
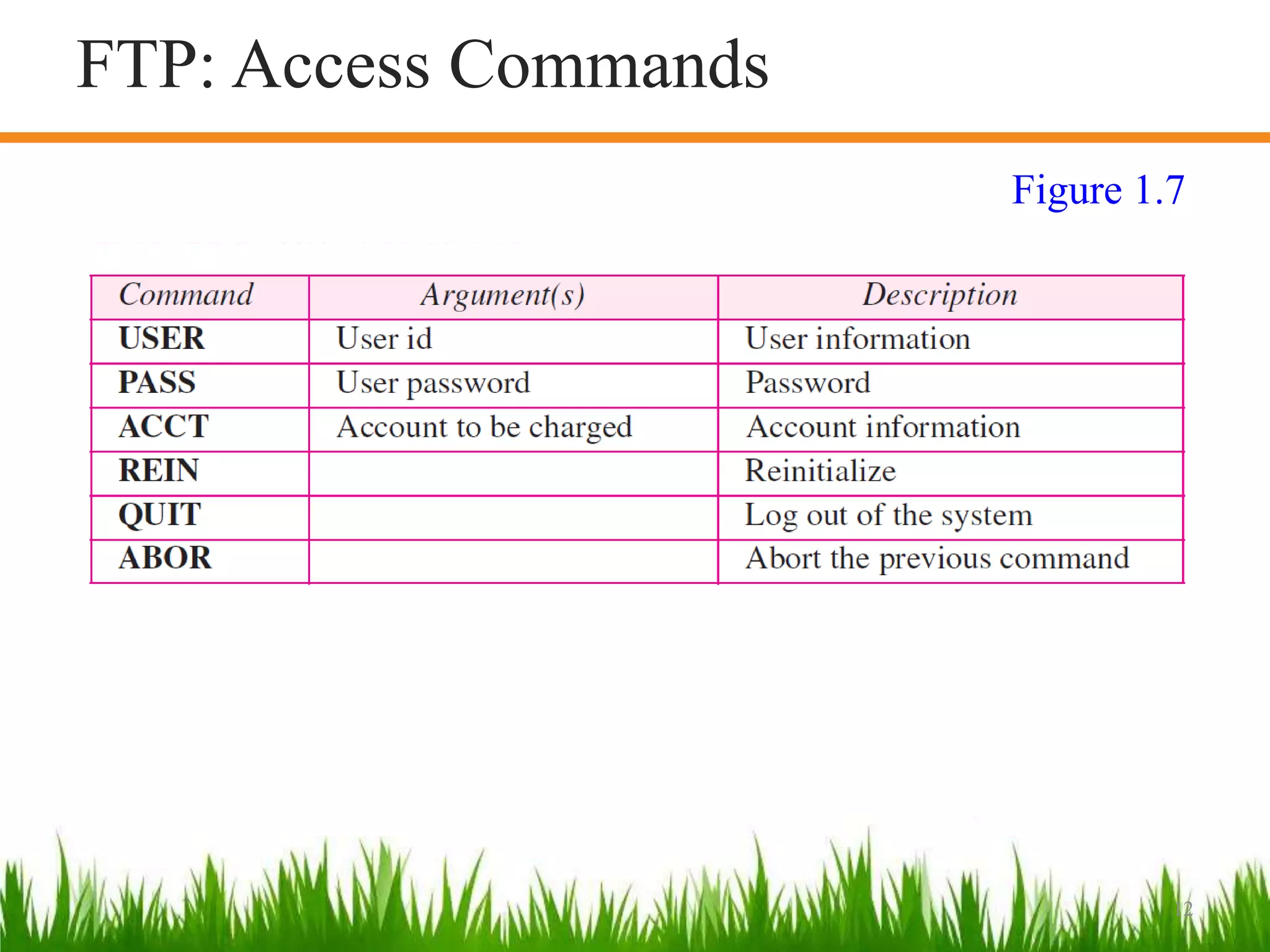
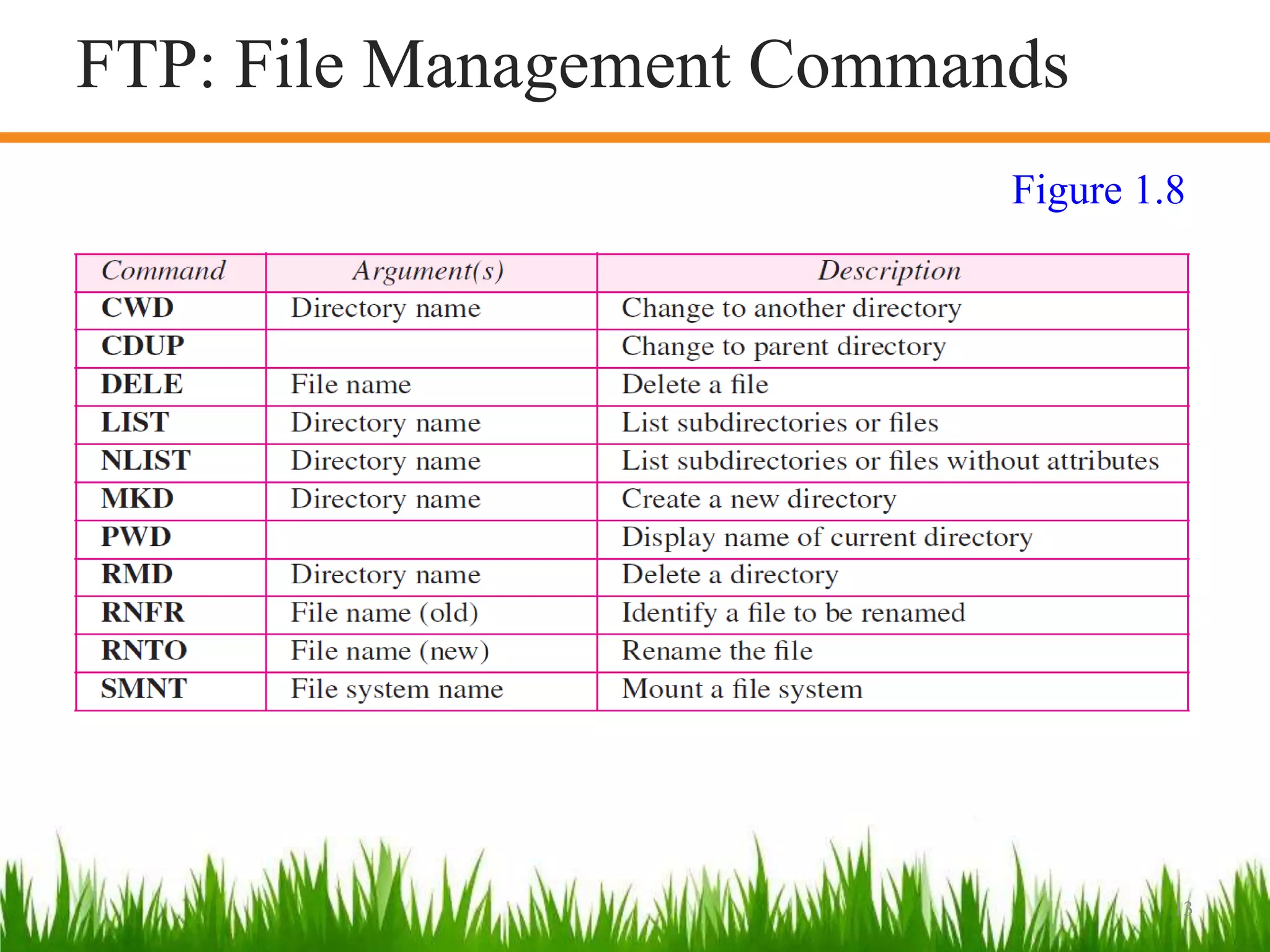
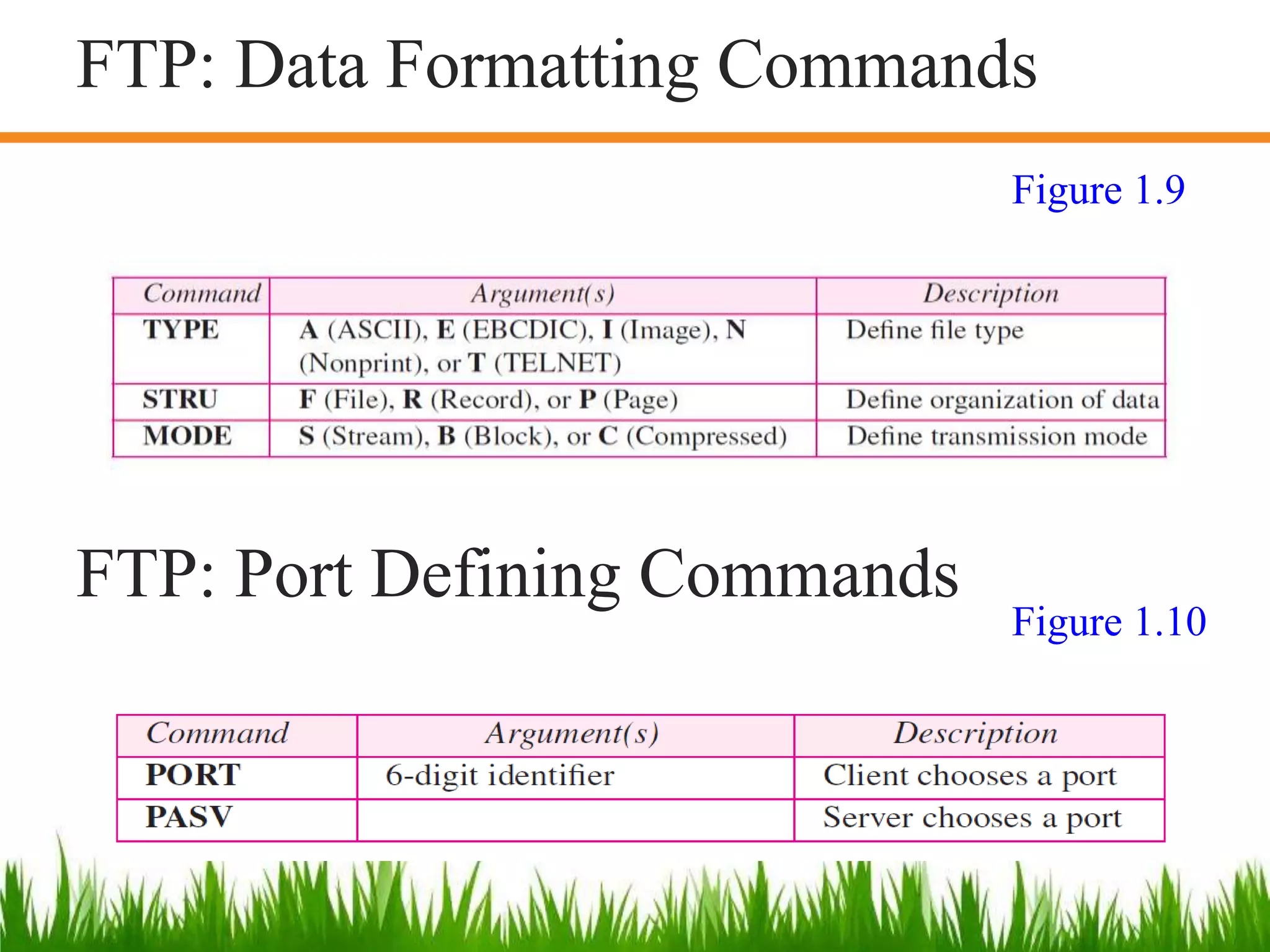
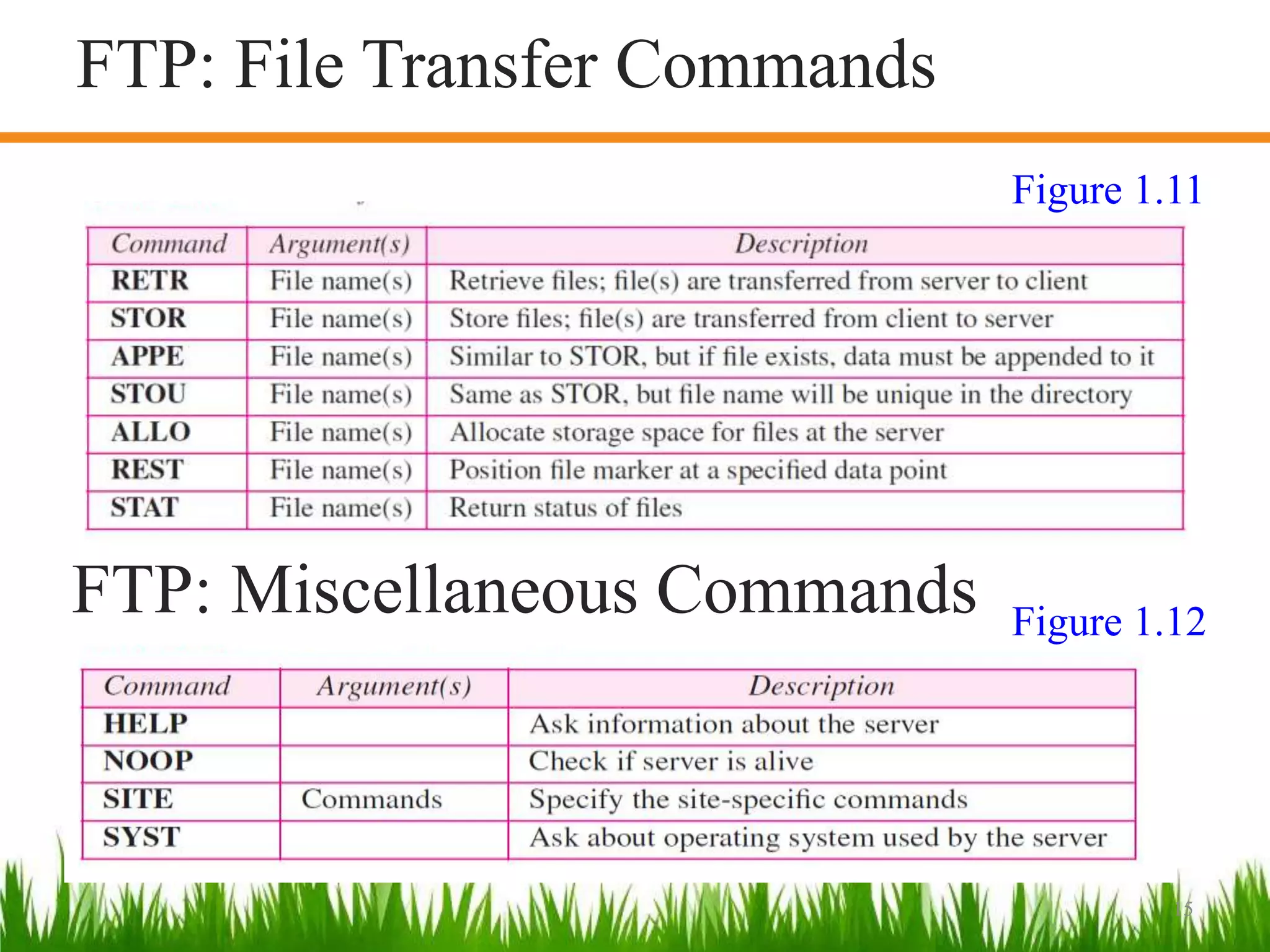
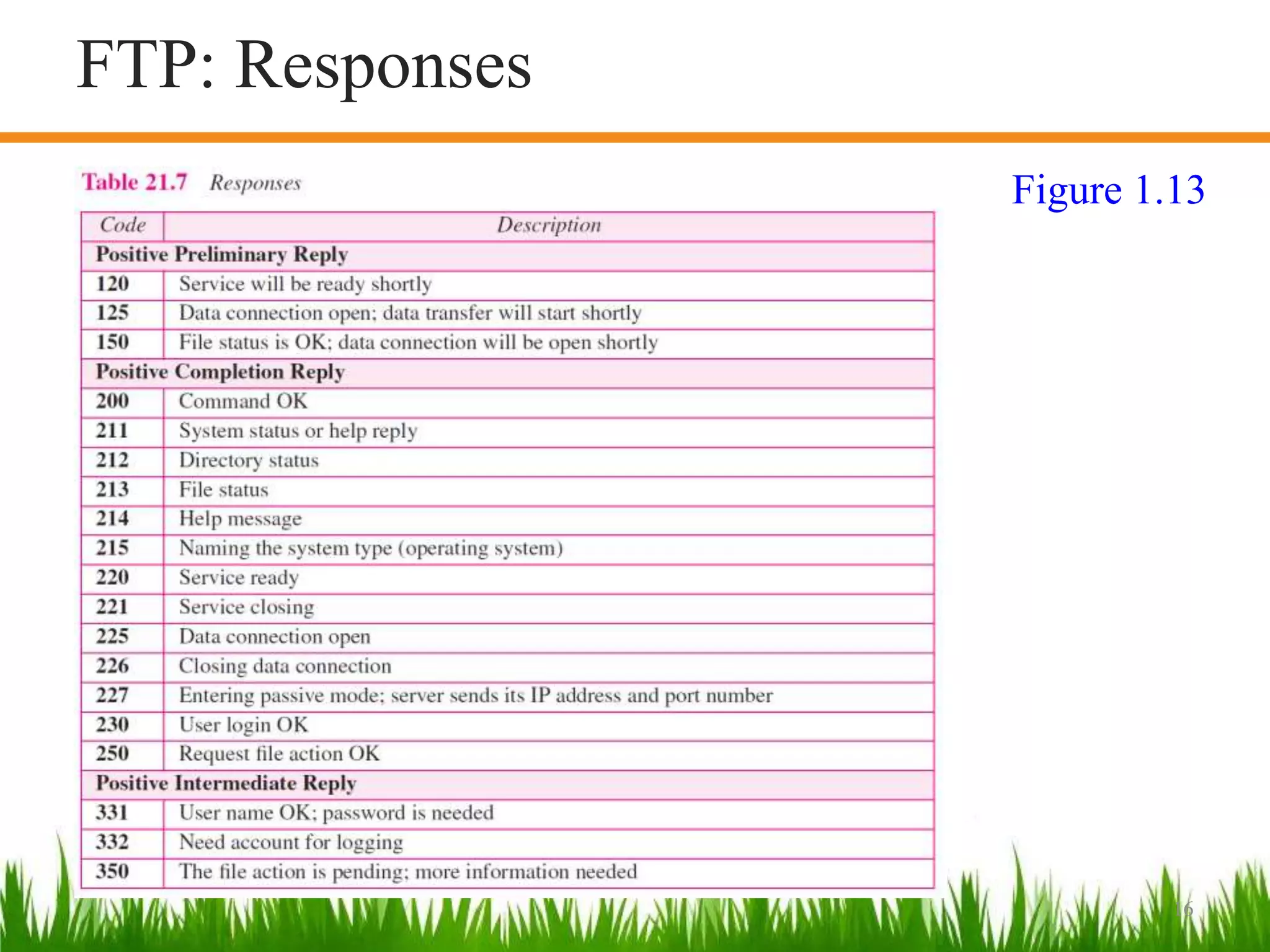
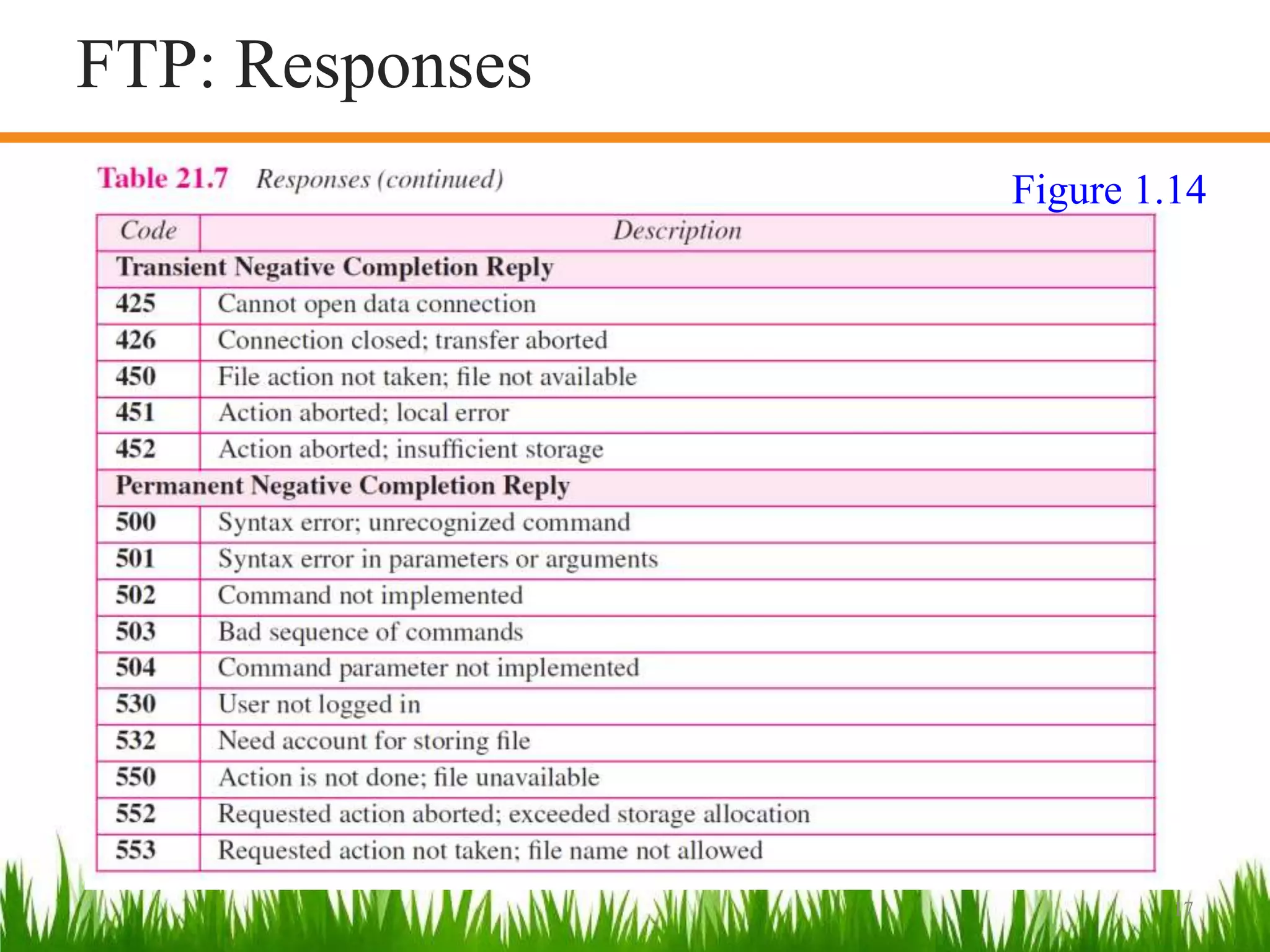
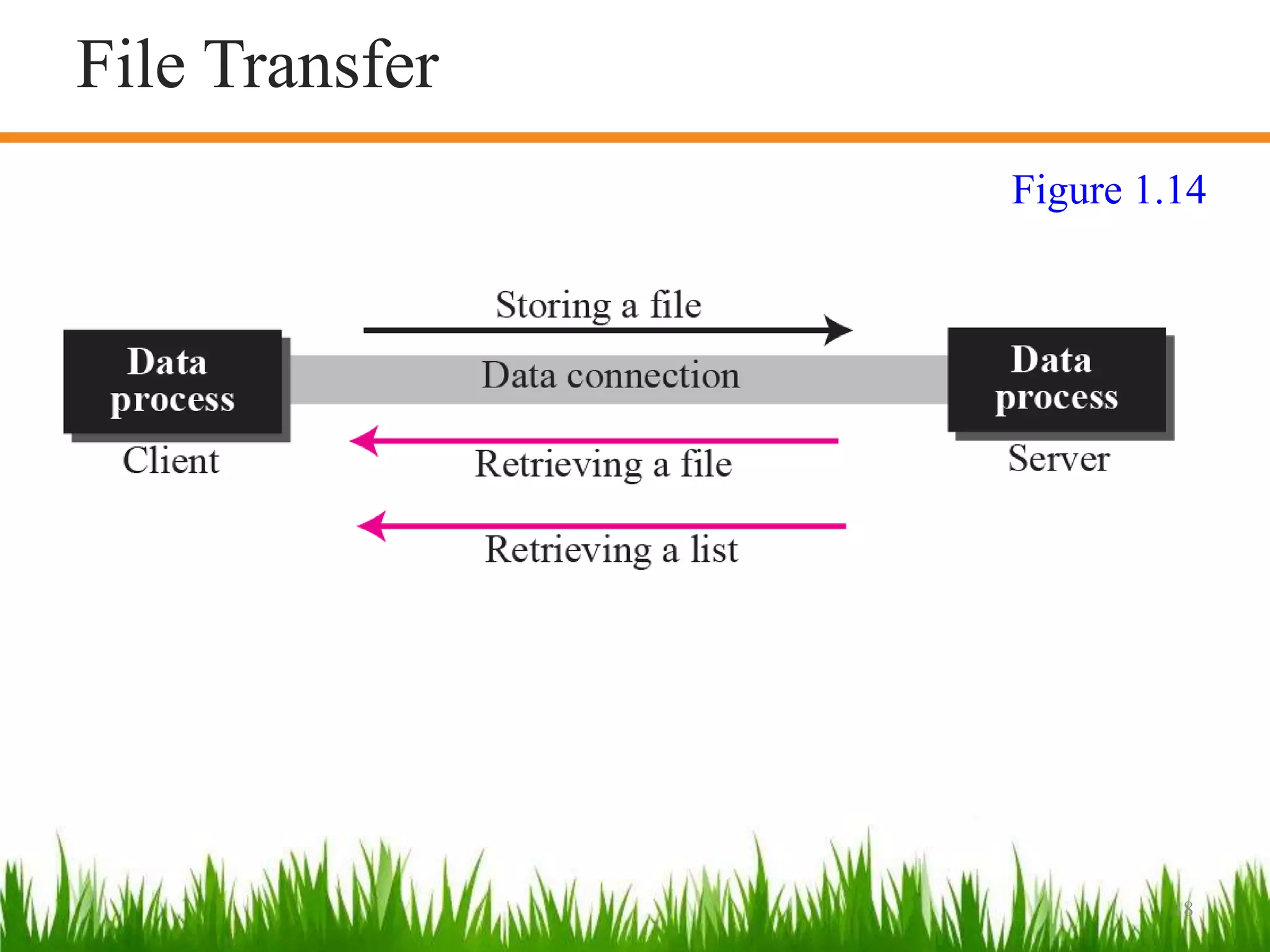
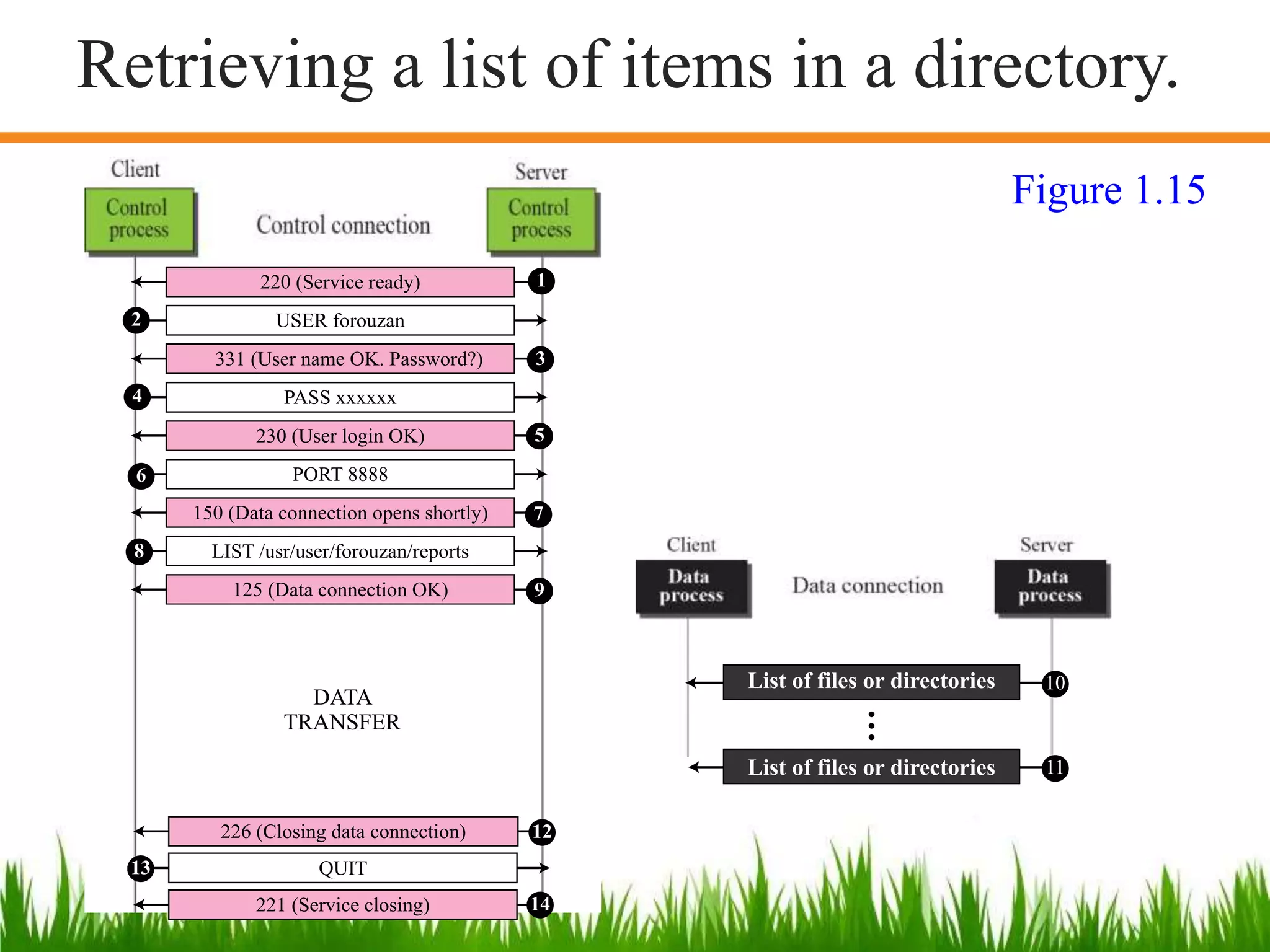
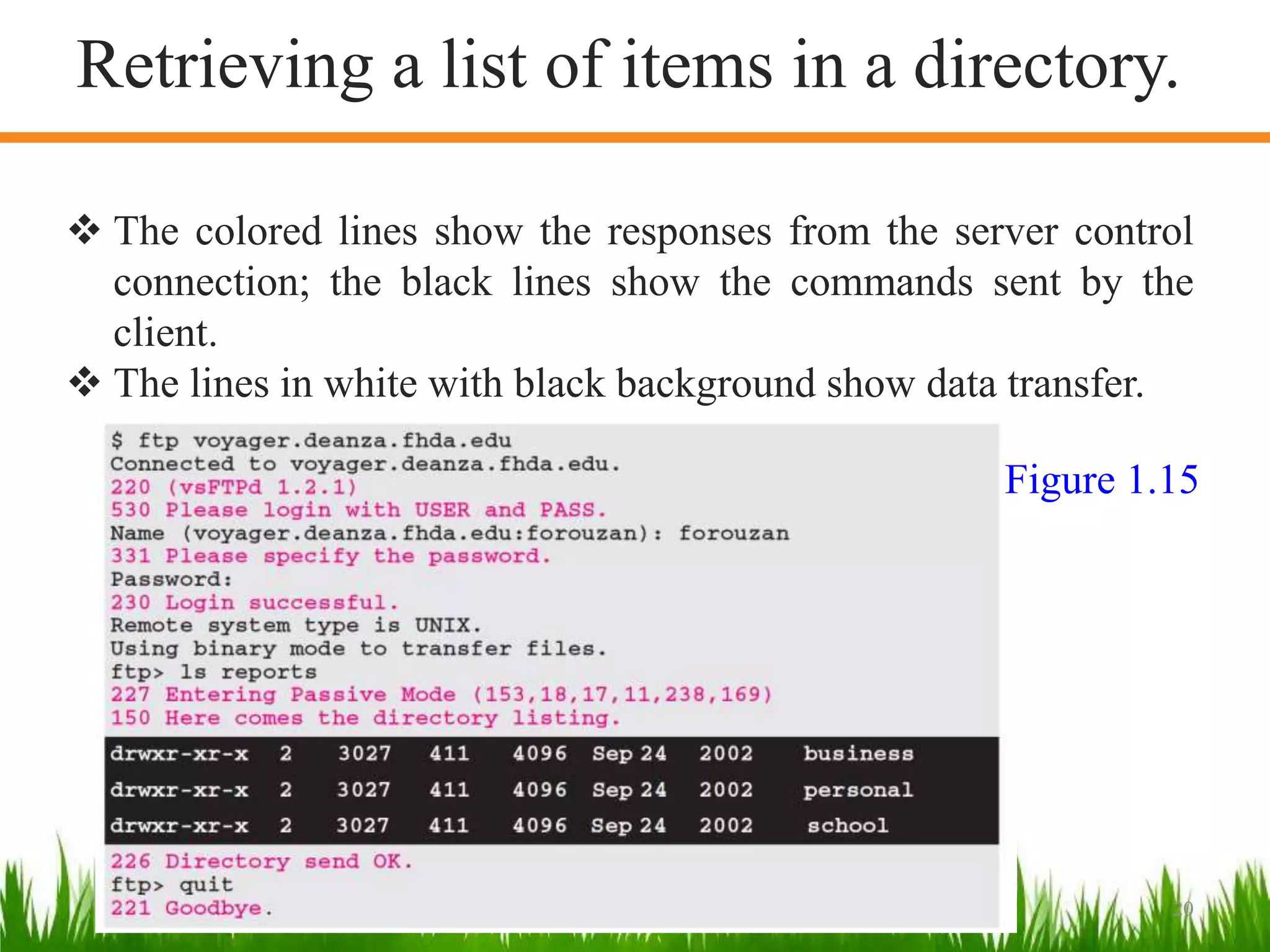
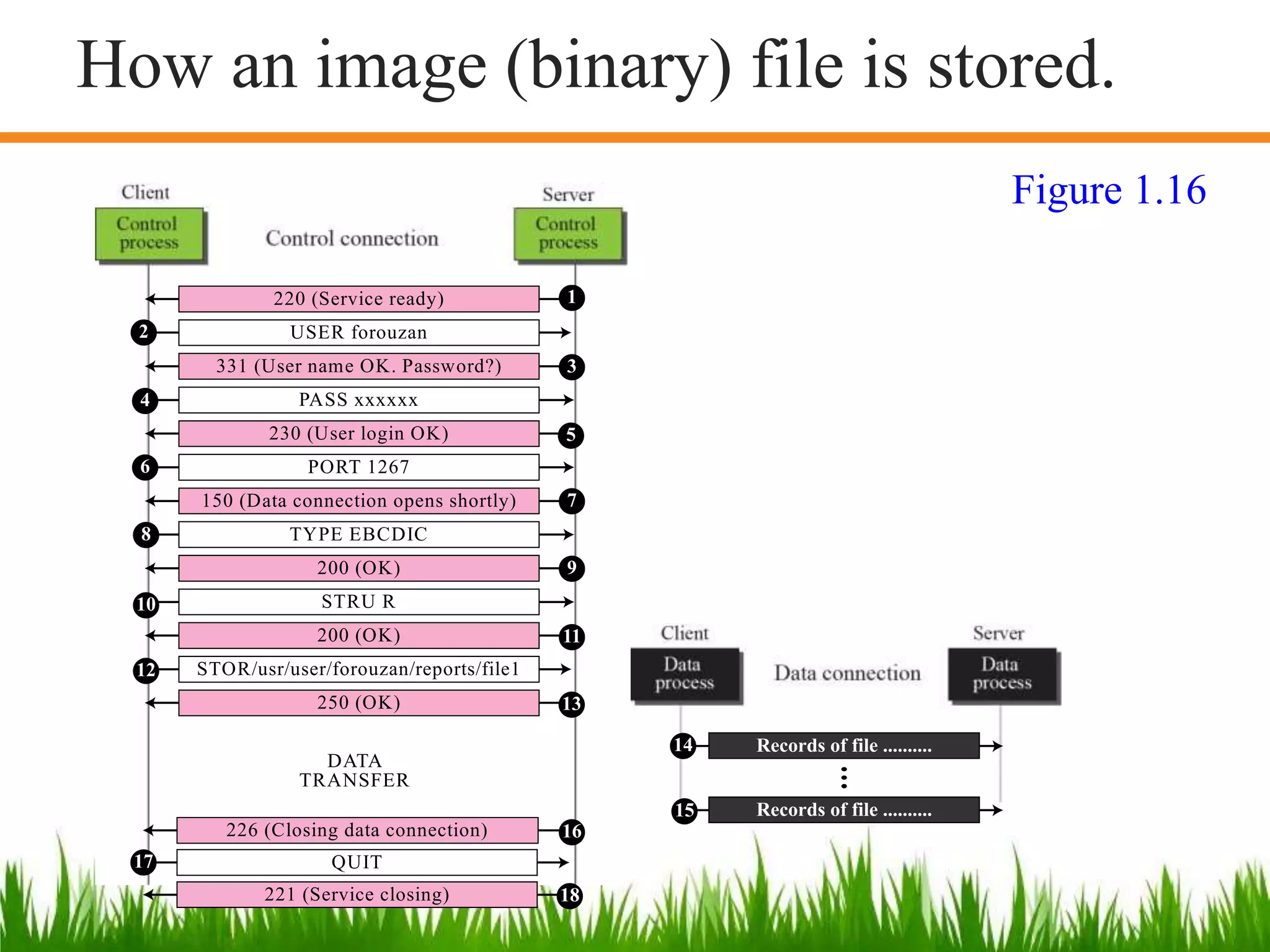
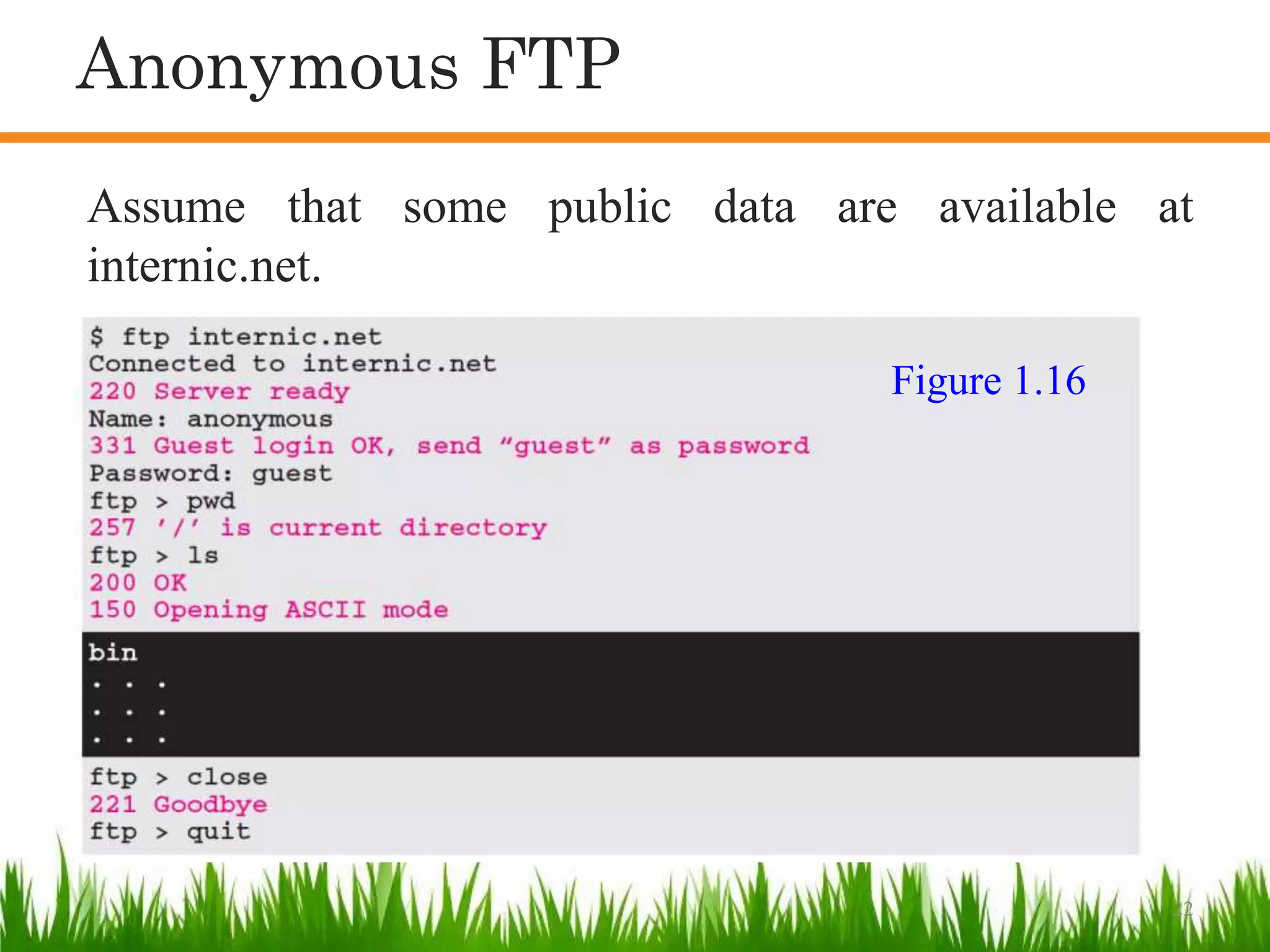
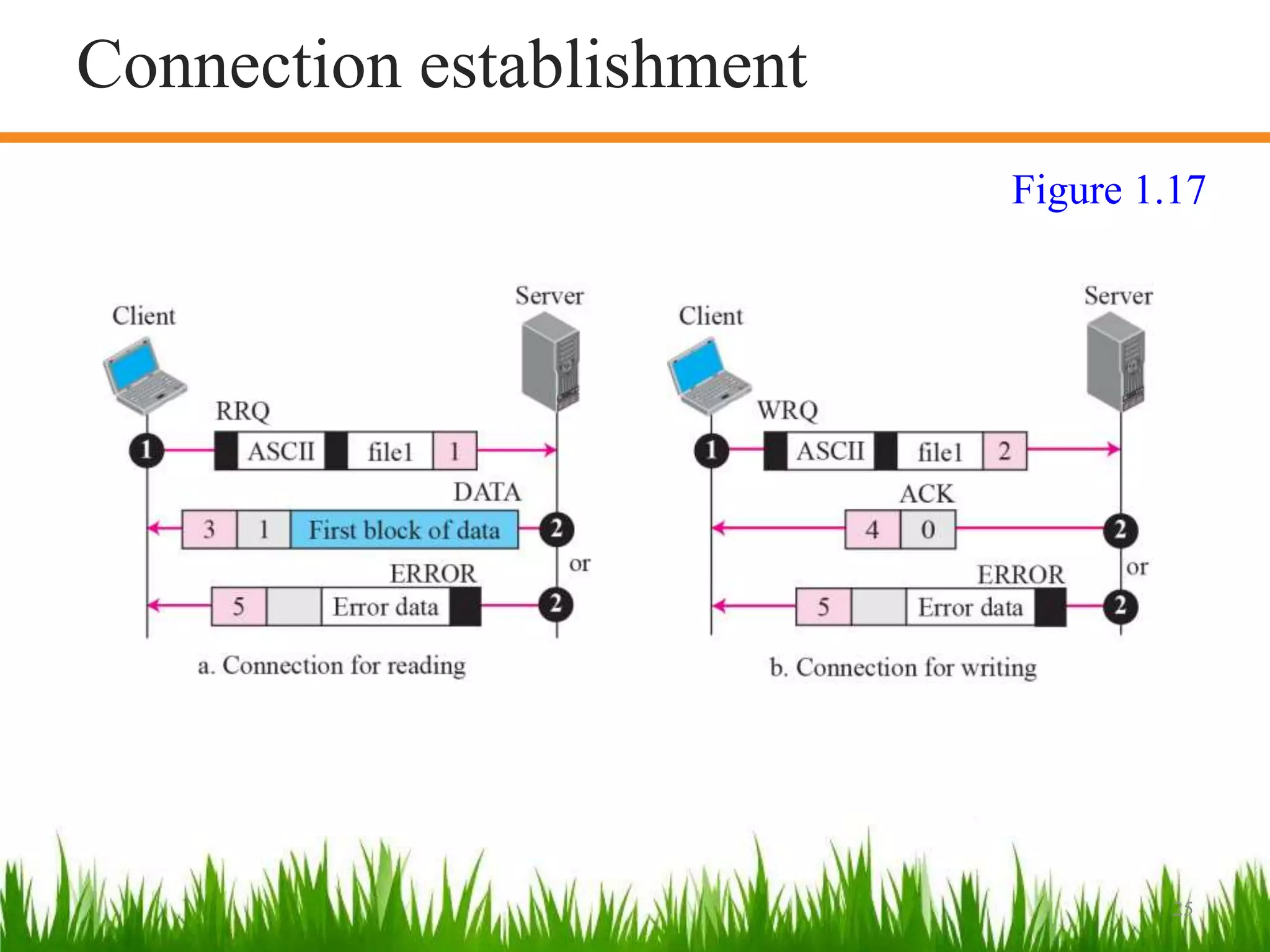
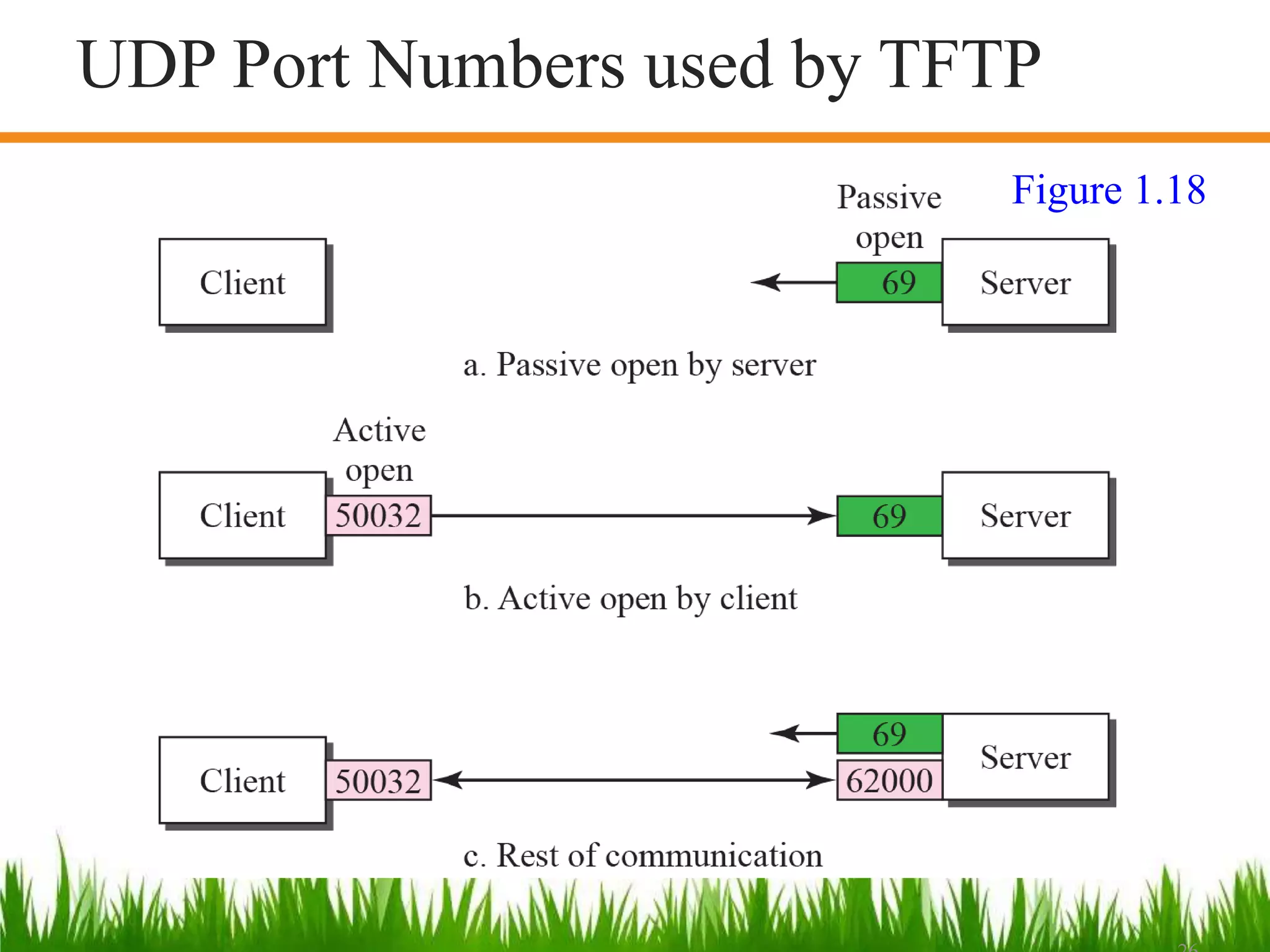
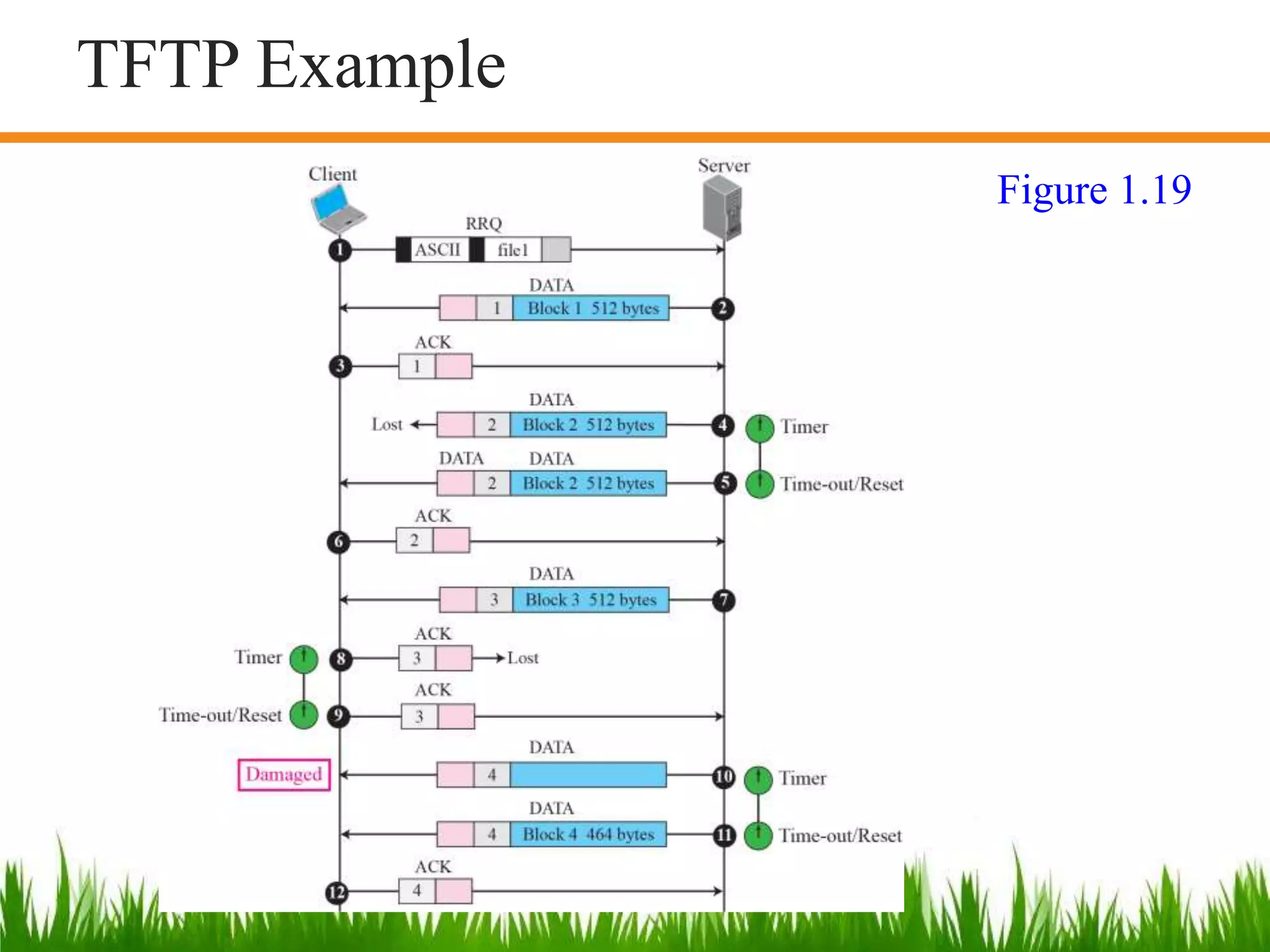
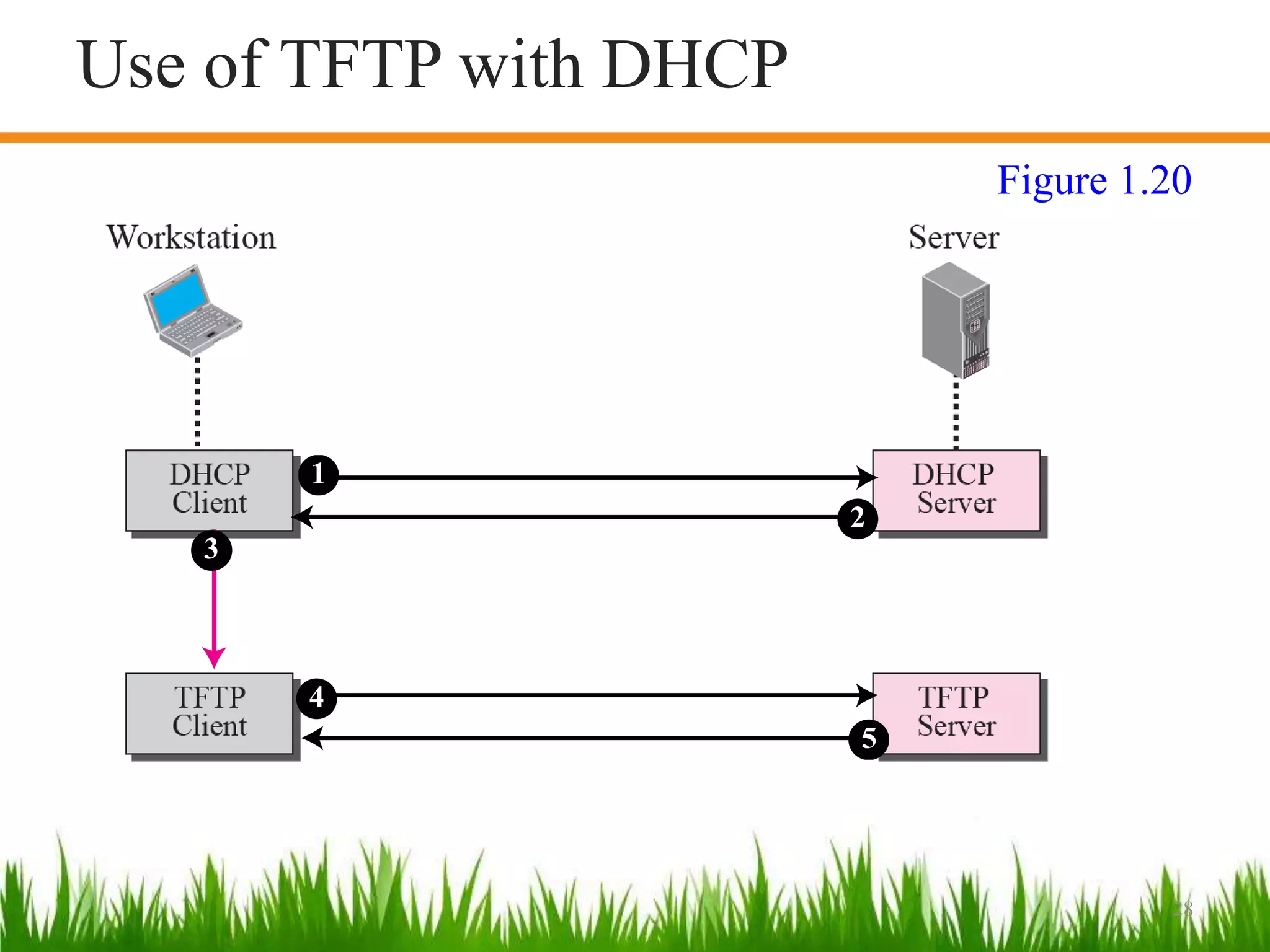
This document discusses two file transfer protocols: FTP and TFTP. FTP uses TCP and requires two connections - one for control and one for data transfer. It addresses issues like different file formats between systems. TFTP is simpler, using UDP instead of TCP. It is used to quickly download small bootstrap and configuration files when systems boot. TFTP uses well-known port 69 while FTP uses ports 20 and 21. The document provides diagrams illustrating the connections and operations of each protocol.