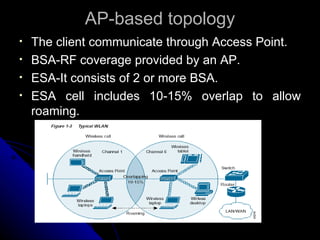
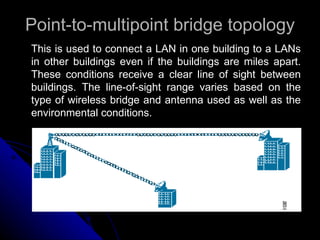
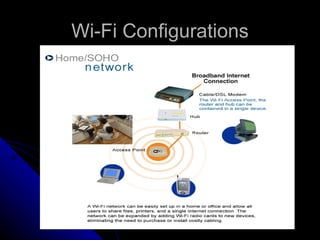
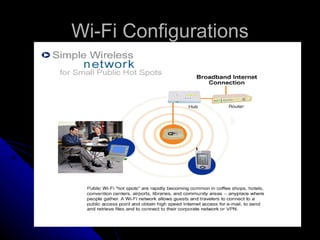
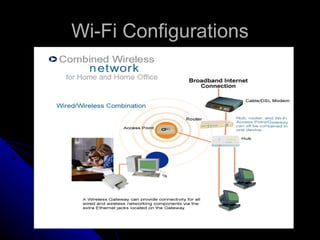
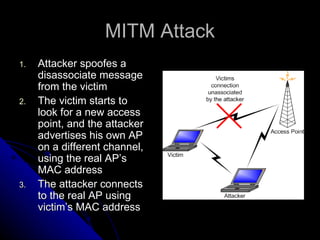
This document provides an overview of Wi-Fi technology, including its standards, network elements, configurations, applications, security threats and advantages/disadvantages. It discusses the IEEE 802.11b, 802.11a and 802.11g wireless standards and how they operate at different speeds and frequencies. It describes the basic components of a Wi-Fi network including access points and Wi-Fi cards. It also summarizes different Wi-Fi network topologies and security threats like eavesdropping, man-in-the-middle attacks and denial-of-service.