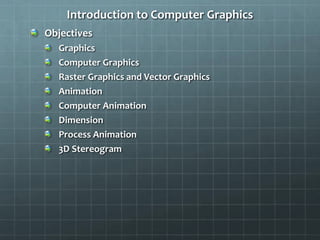
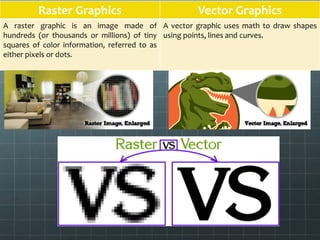
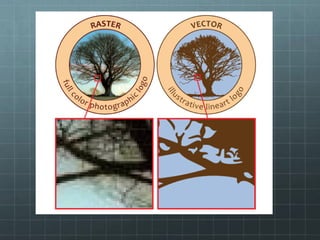
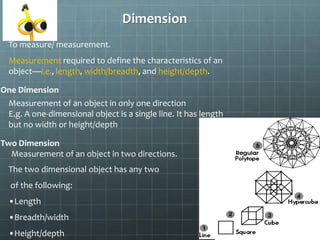
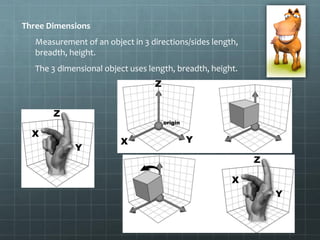
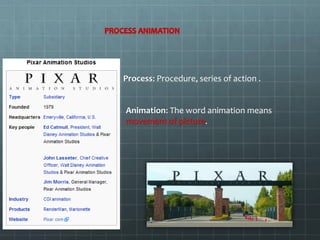
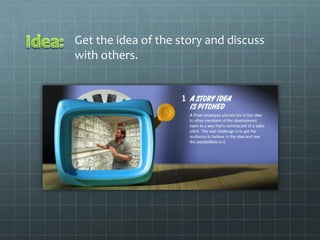
This document provides an introduction to computer graphics. It discusses graphics and computer graphics, including raster graphics and vector graphics. It also discusses animation and computer animation. Dimensions including one, two, and three dimensions are defined. The objectives of the introduction to computer graphics class are explained, which will include 3DS Max modeling, activities in Photoshop and InDesign, and an introduction to computer animation. The document provides definitions and examples of key graphics and animation terms.