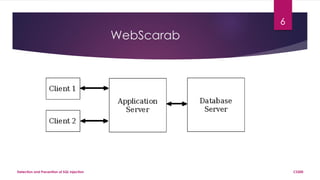
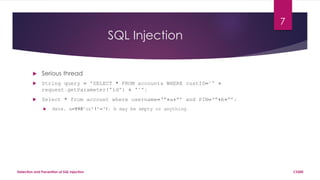
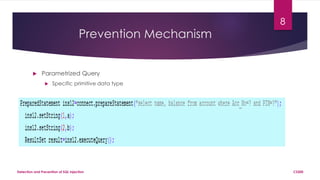
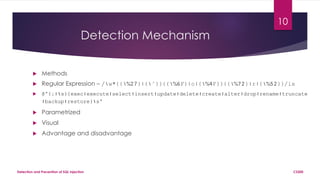
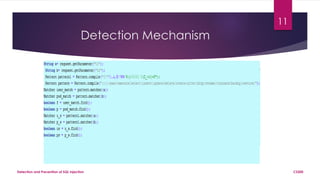
The document presents a project on detecting and preventing SQL injection, detailing methods, mechanisms, and tools like WebGoat and WebScarab. It discusses the nature of SQL injection attacks and their impacts, as well as prevention techniques such as parameterized queries and indirect SQL queries. The conclusion emphasizes the necessity of advanced scanning structures and hashing of user credentials for improved security.