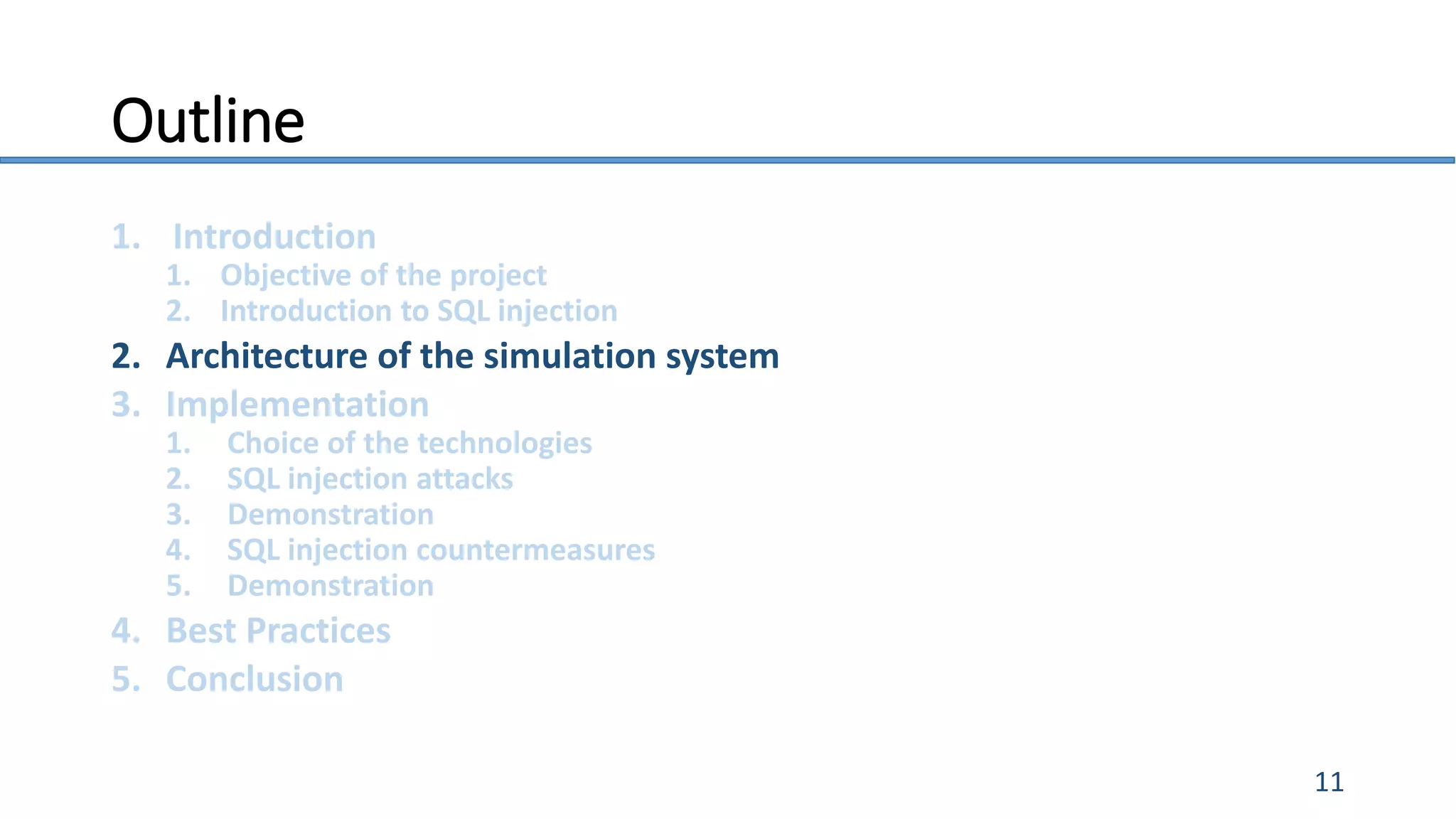
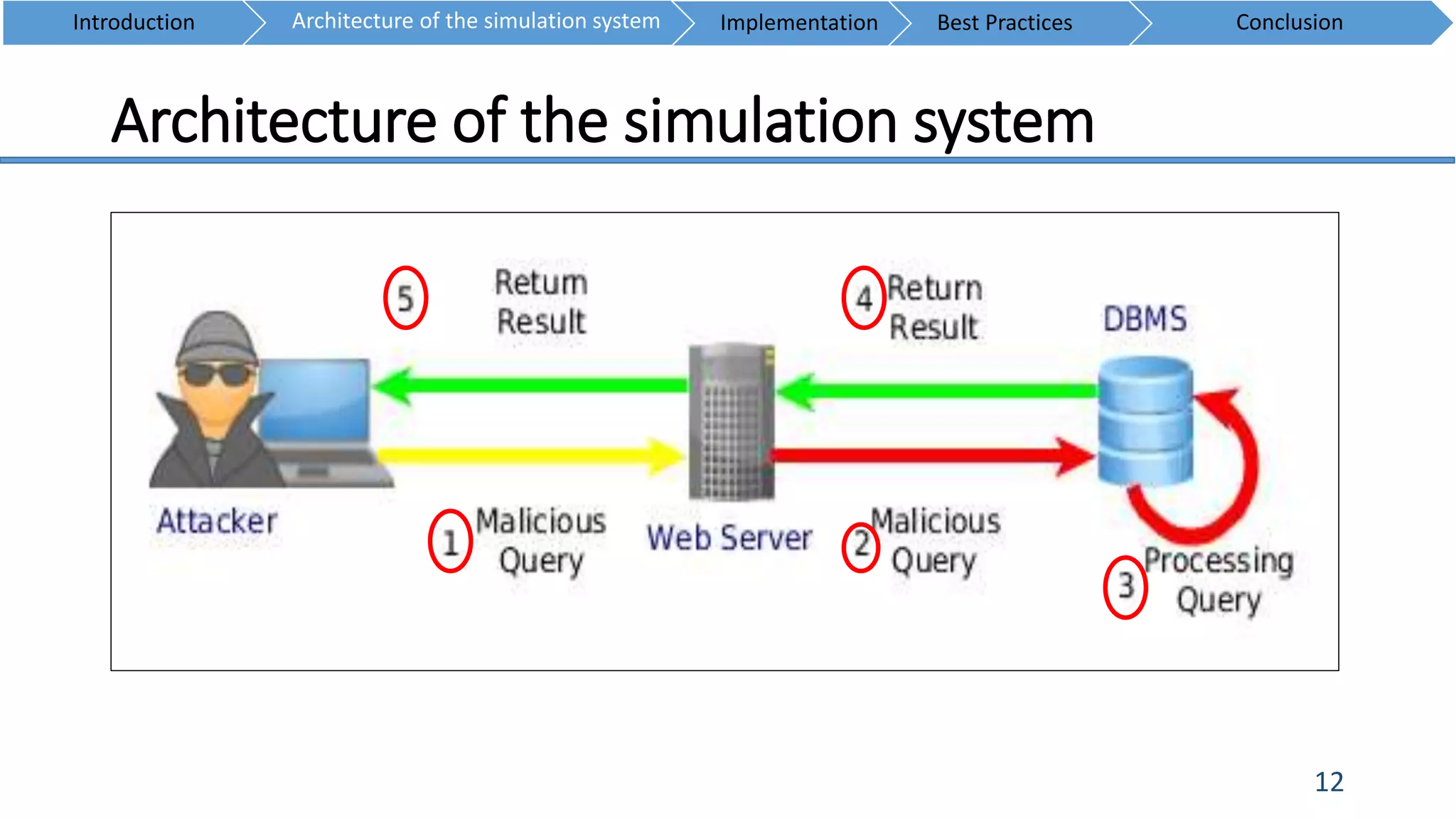
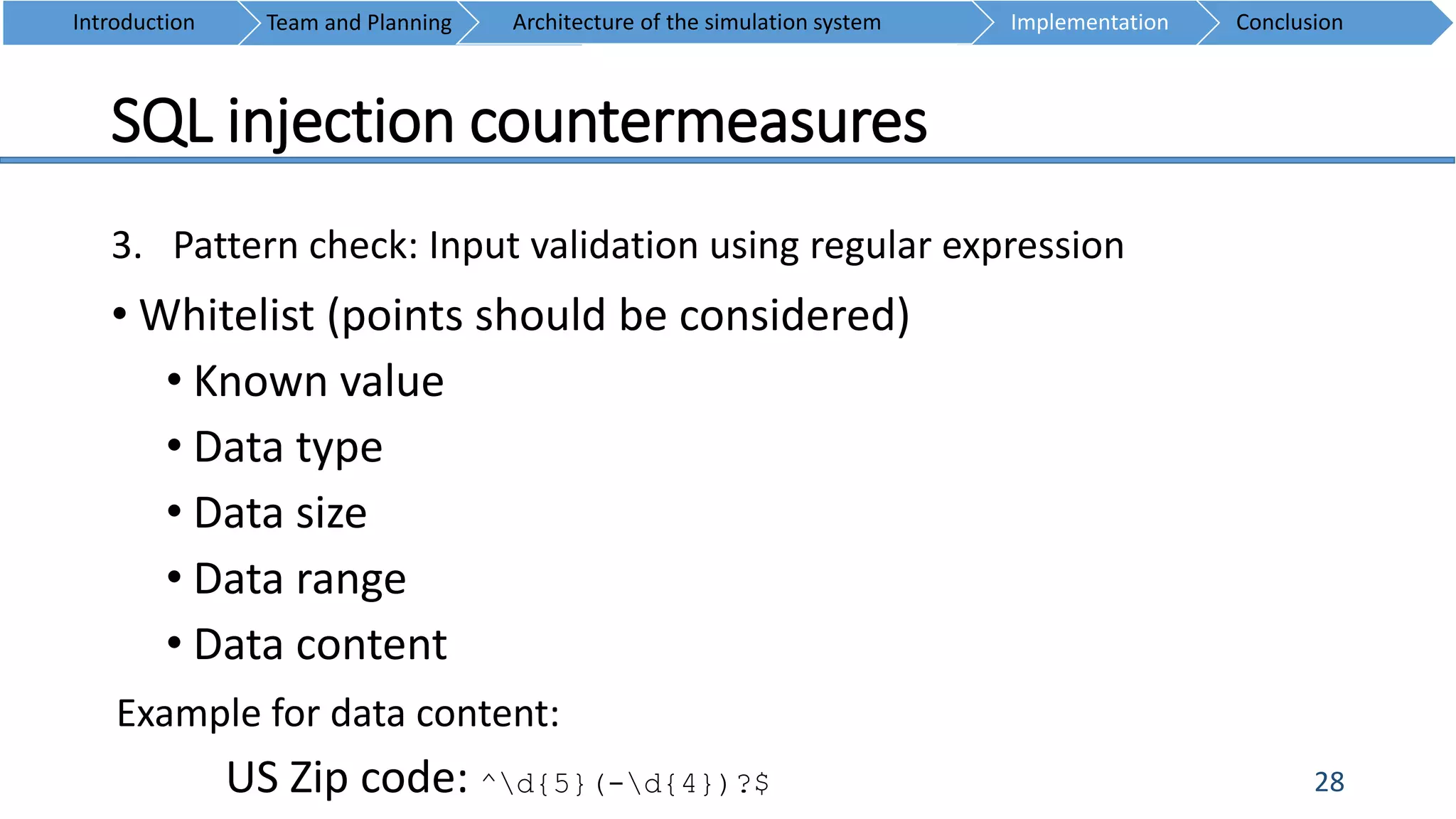
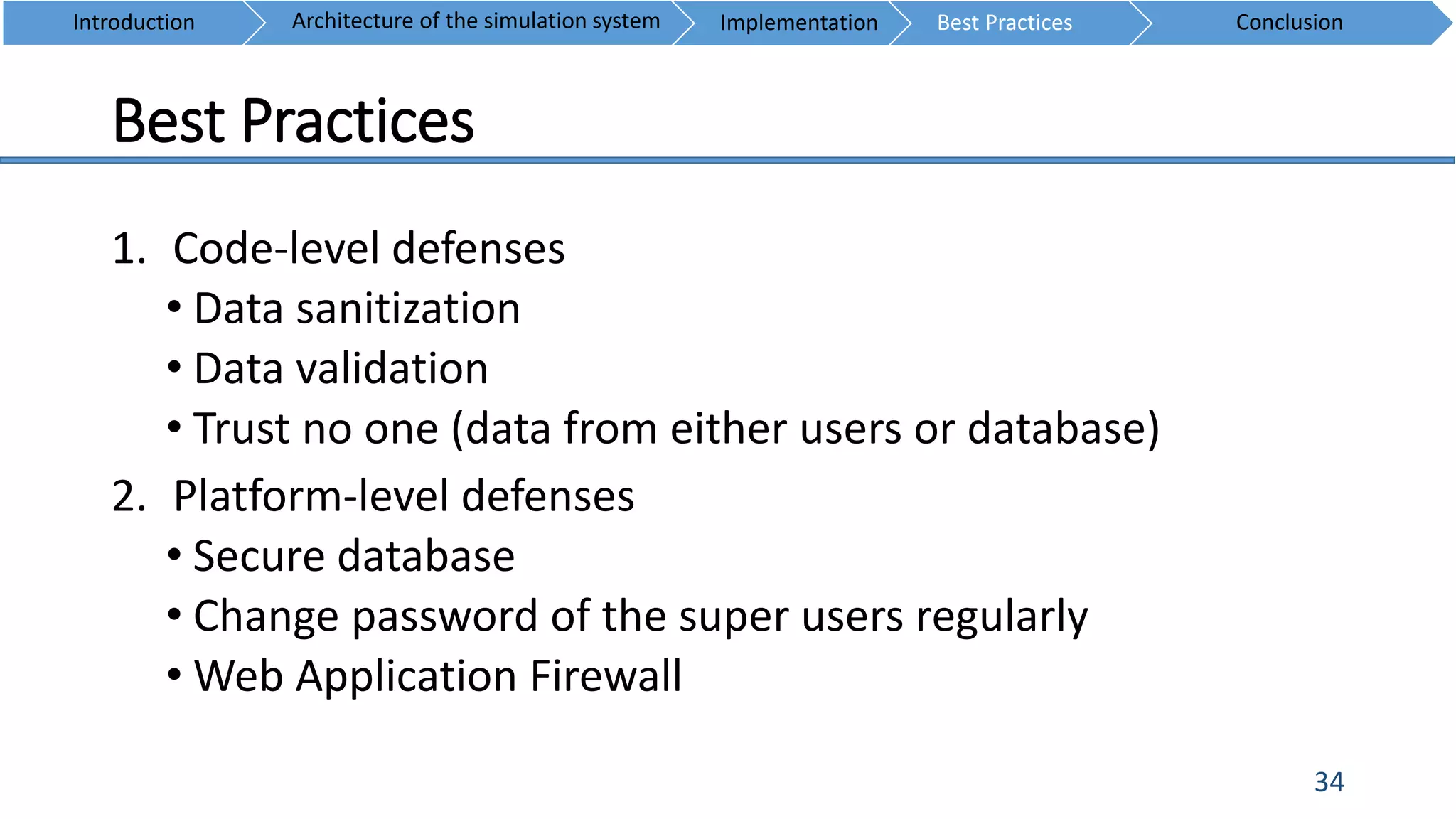
The document provides an overview of SQL injection attacks, discussing their mechanics, common vulnerabilities, and various countermeasures. It outlines the project's objectives, technical implementations, and best practices for securing applications against these threats. The paper also emphasizes the severity of SQL injection vulnerabilities and the importance of effective defenses in application development.
![Introduction to SQL injection
5
• SQL Injection is an attack where the user supplies input in order to
construct SQL request that will retrieve information from Database
[1].
• SQL injection is an attack in which the SQL code is inserted or
appended into application, or user input parameters that are later
passed to a back-end SQL server for parsing and execution [2].
• SQL injection is a code injection technique, used to attack data-driven
applications, in which malicious SQL statements are inserted into an
entry field for execution [3].
Introduction ConclusionArchitecture of the simulation system Implementation Best Practices](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-5-2048.jpg)
![Introduction to SQL injection
6
SQL Injection attack illustrate [4]
3
Attacker sends data containing SQL fragments
Attacker enters SQL
fragments into a web page
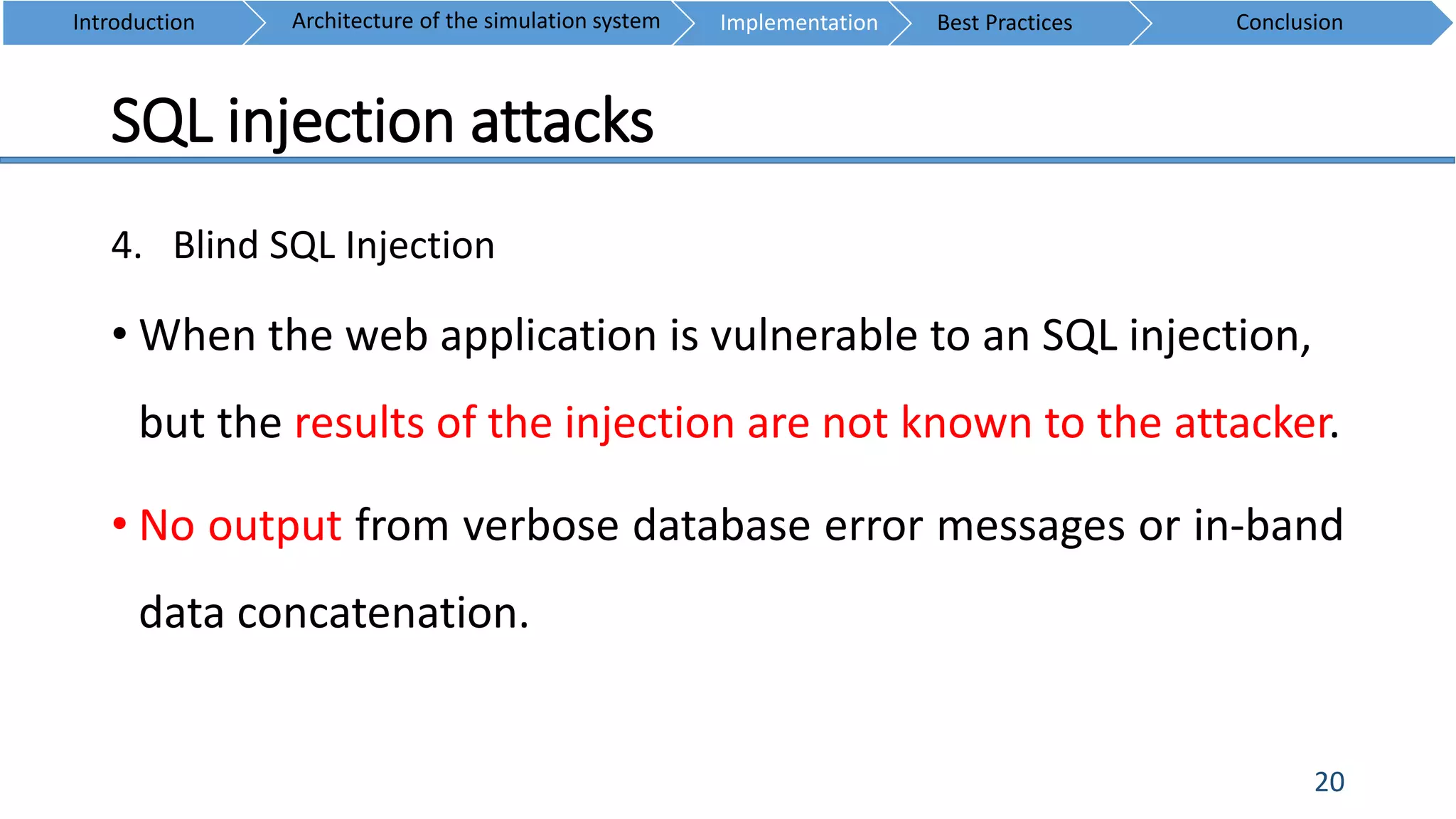
that uses input in a query
1
Attacker views unauthorized data
Custom Code
Accounts
Finance
Administration
Transactions
Communication
Knowledge
Mgmt
E-Commerce
Bus.Functions
Database
2 Application sends
modified query to
database, which
executes it
Introduction ConclusionArchitecture of the simulation system Implementation Best Practices](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-6-2048.jpg)
![Introduction to SQL injection
7
• Vulnerability detection on web application
• Everything between the <FORM> and </FORM> have
potential parameters that might be useful [5].
• Try to look especially for URL that takes parameters, like:
GET method, i.e.: http://test/index.php?id=10 [2].
Introduction ConclusionArchitecture of the simulation system Implementation Best Practices](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-7-2048.jpg)
![Introduction to SQL injection
8
• Vulnerability detection on web application (Cont’)
• POST parameters can be injected using a traffic
manipulation tool or web browser plug-in [2].
• Using blind SQL injection to inject and analyse the error
message from database if any.
Introduction ConclusionArchitecture of the simulation system Implementation Best Practices](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-8-2048.jpg)
![Introduction to SQL injection
9
Introduction ConclusionArchitecture of the simulation system Implementation Best Practices
Consequences [6]
Confidentiality SQL databases generally contains sensitive data, so loss of
confidentiality is a big problem.
Authentication If poor SQL commands are used to check user names and
passwords, authentication can be compromised.
Authorization If authorization information is held in a SQL database, it can
be exploited.
Integrity SQL Injection attack can change or delete data.](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-9-2048.jpg)
![Introduction to SQL injection
10
• Examples [7]
COMPANY DATE RESULTS
Mapp.nl (Online store) 2015 157,000 email addresses and passwords
were stolen
US Federal (Army, NASA, ...) 2013 More than 100,000 user information
Yahoo 2012 450,000 plain text passwords
Ingenicard 2012 estimated financial fraud losses $9 million
Global Payments 2011 950,000 card numbers stolen estimated loss
$92.7 million
Introduction ConclusionArchitecture of the simulation system Implementation Best Practices](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-10-2048.jpg)
![SELECT id FROM users WHERE username = ‘$_GET[usrname]’ AND
password = ‘$_GET[psw]’;
SELECT id FROM users WHERE username = ‘’OR ‘1’ = ‘1’ AND
password = ‘’OR ‘1’ = ‘1’;
SQL injection attacks
17
1. Incorrectly filtered escape characters
• When the user input is not filter for escape characters
Example:
SQL Injection
SQL Injection
Introduction ConclusionArchitecture of the simulation system Implementation Best Practices](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-17-2048.jpg)
![SQL injection attacks
18
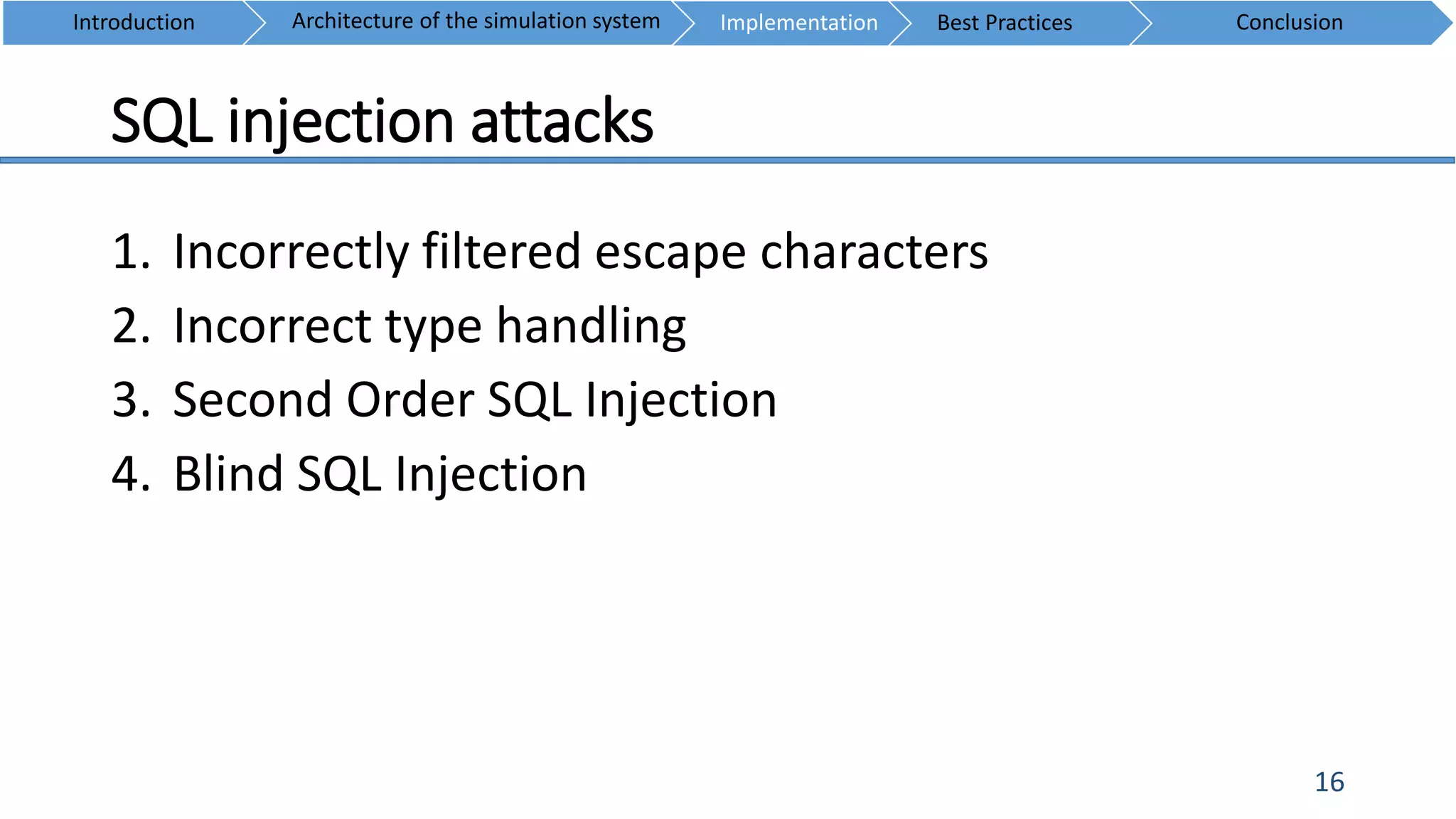
2. Incorrect type handling
• When an input is not appropriately typed or is not checked for type constraints.
Example:
Query:
“SELECT * FROM usersInfo WHERE id= ”.$_GET[“var_number_id”].“;”
SQL Injection:
1;DROP TABLE users
Interpreted query:
SELECT * FROM usersInfo WHERE id=1;DROP TABLE users;
SQL Injection
Introduction ConclusionArchitecture of the simulation system Implementation Best Practices](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-18-2048.jpg)
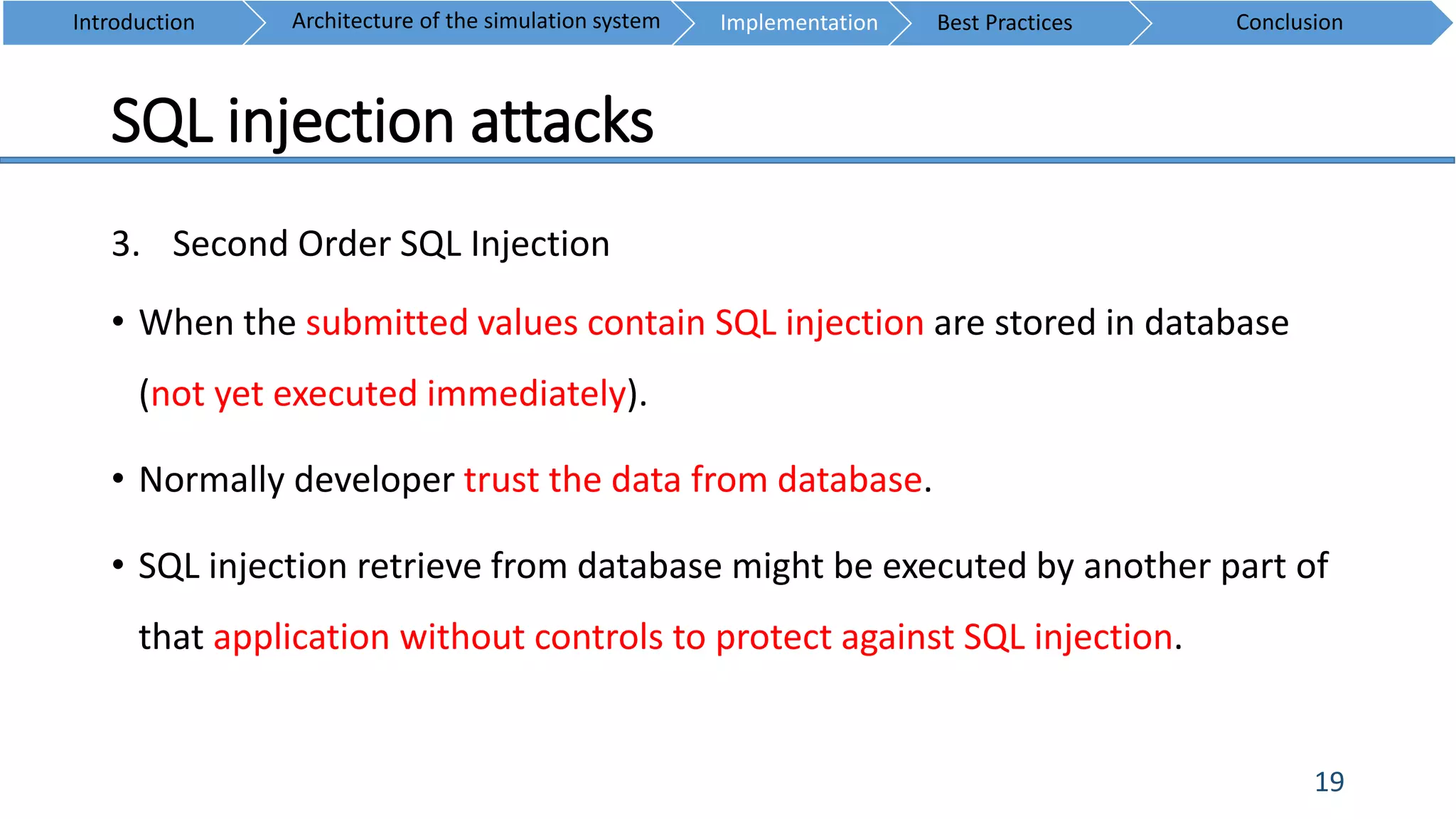
![SQL injection attacks
22
3. Blind SQL Injection (Cont’)
• SQLMap is an open source testing tool
• Automates the process of detecting and exploiting SQL injection flaws
• Taking over of database servers
Introduction ConclusionArchitecture of the simulation system Implementation Best Practices
SQLMap tool [8]](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-22-2048.jpg)
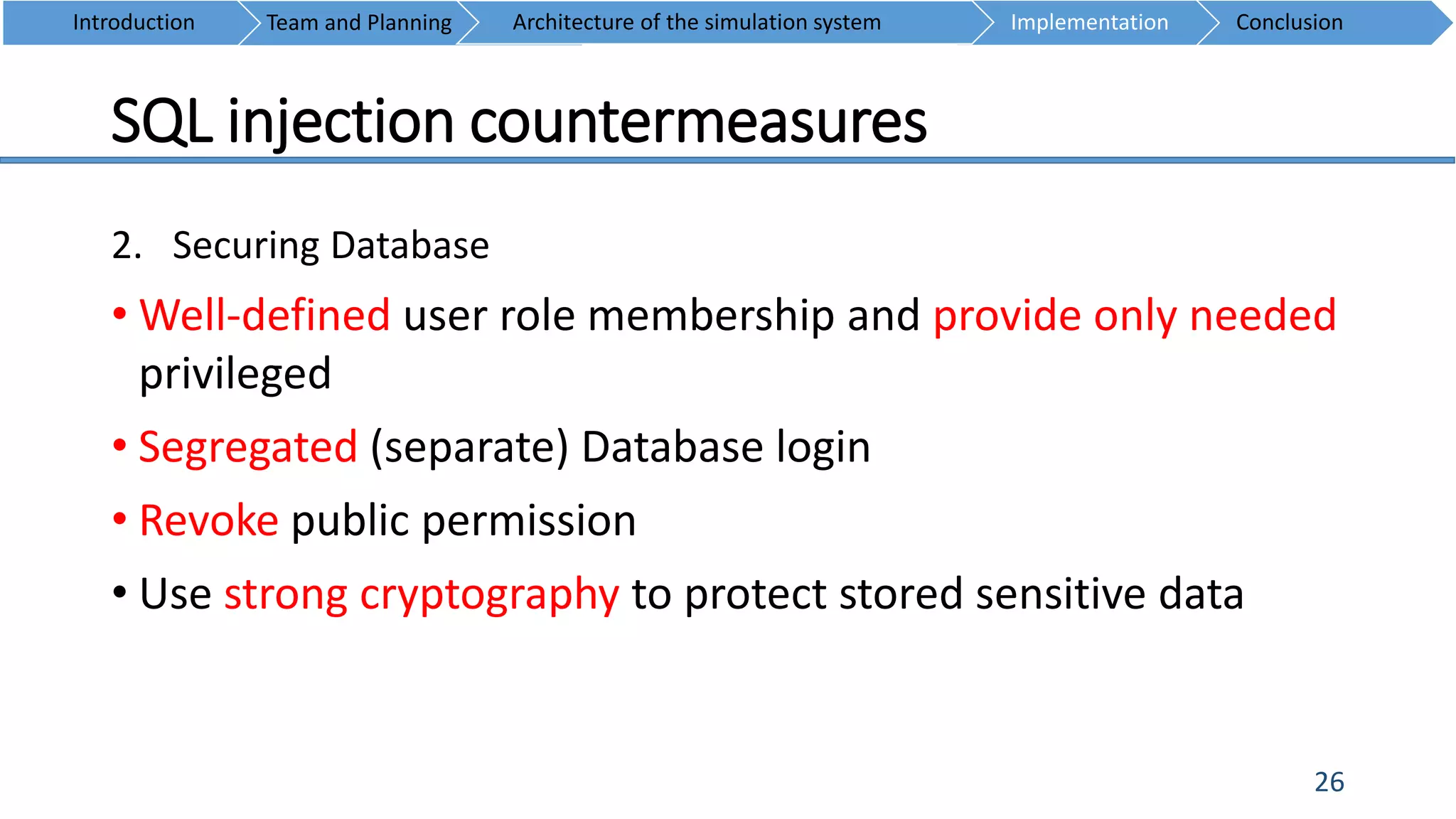
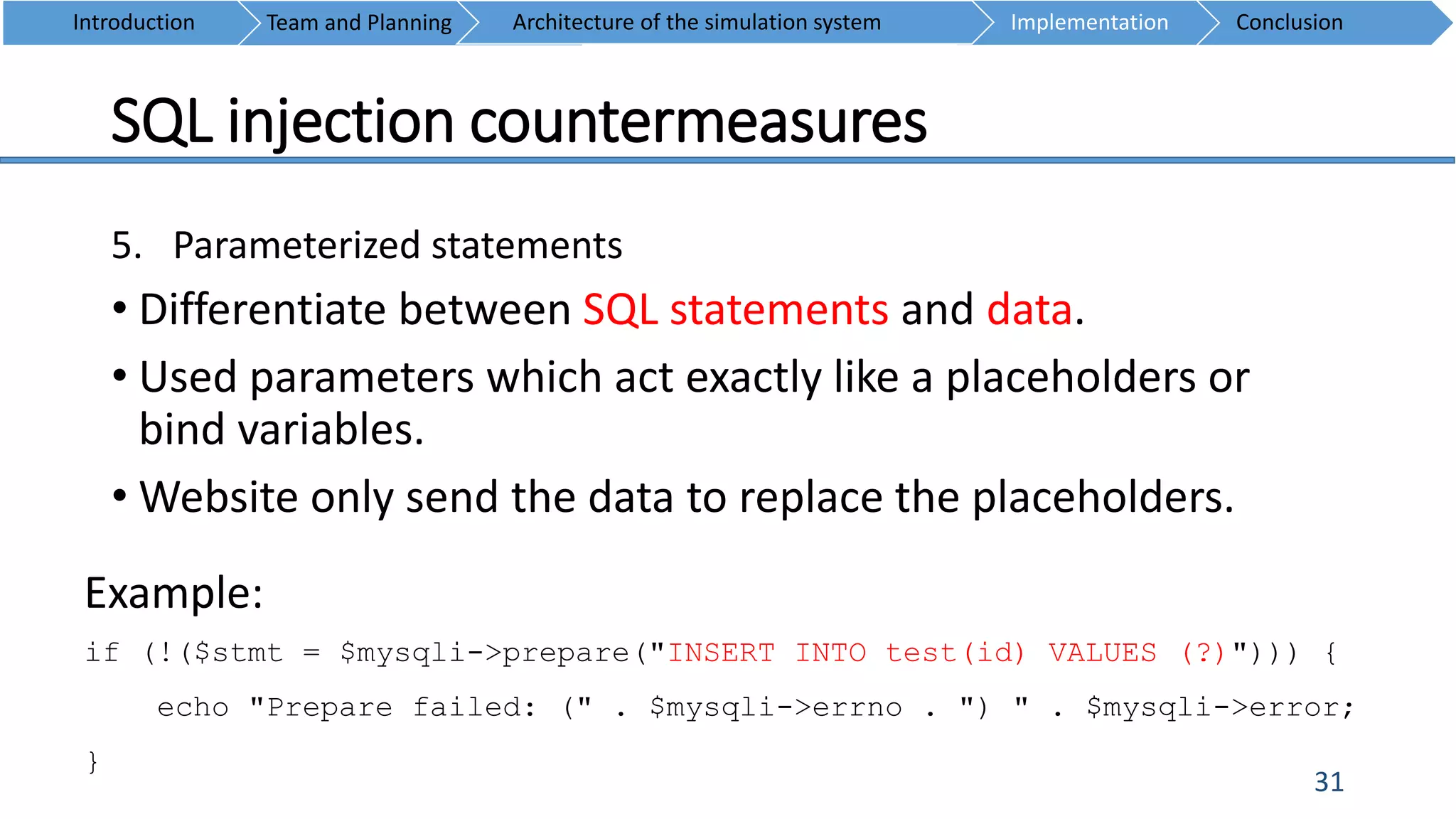
![SQL injection countermeasures
25
1. Hexadecimal Conversion
PHP Functions:
• DECHEX — Decimal to hexadecimal [9].
• BIN2HEX — Convert any other type of variable into hex [9].
MySQL Function:
• UNHEX — Return a string containing hex representation of a number [10].
Introduction Team and Planning ConclusionImplementationArchitecture of the simulation system
Example
"SELECT * FROM user WHERE `usrname`= UNHEX(".bin2hex($userInput).")";](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-25-2048.jpg)
![SQL injection countermeasures
29
3. Pattern check: Input validation using regular expression
• Blacklisting
Reject input that contains malicious content
Introduction Team and Planning ConclusionImplementationArchitecture of the simulation system
Example of known bad character, string or pattern:
[(' OR)|('(''|[^'])*')|(;)|((ALTER|CREATE|DELETE|DROP|EXEC(UTE){0,1}|INSERT(
+INTO){0,1}|MERGE|SELECT|UPDATE|UNION( +ALL){0,1}))]](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-29-2048.jpg)
![REFERENCES
37
[1] William Stalling, Computer Security Principles and Practice. United
State of America: Pearson Education, 2012, 364.
[2] Justin Clarke, SQL Injection Attacks and Defense. United State of
America: Elsevier, 2012, 22.
[3] [online] 2000, http://en.wikipedia.org/wiki/SQL_injection (Accessed:
15 April 2015).
[4] M. Morana, “OWASP Top And Insecure Software Root Causes,"
[online] 2008, http://fr.slideshare.net/marco_morana/owasp-top-10-
and-insecure-software-root-causes-presentation (Accessed: 20 April
2015).](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-37-2048.jpg)
![REFERENCES
38
[5] [online]
2002, http://www.securiteam.com/securityreviews/5DP0N1P76E.h
tml (Accessed: 20 April 2015).
[6] [online] 2014, https://www.owasp.org/index.php/SQL_Injection
(Accessed: 14 April 2015).
[7] Ranger78, “SQL INJECTION HALL OF SHAME" [online],
http://codecurmudgeon.com/wp/sql-injection-hall-of-shame/
(Accessed: 20 April 2015).](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-38-2048.jpg)
![REFERENCES
39
[8] [online] 2006-2015, http://sqlmap.org/ (Accessed: 20 April 2015).
[9] [online] 2001-2015, http://php.net/manual/en/index.php
(Accessed: 20 April 2015).
[10] [online] 2015, https://dev.mysql.com/doc/refman/5.0/en/string-
functions.html (Accessed: 20 April 2015).](https://image.slidesharecdn.com/powerpointpresentation1-150422143006-conversion-gate01/75/Web-Security-SQL-Injection-39-2048.jpg)