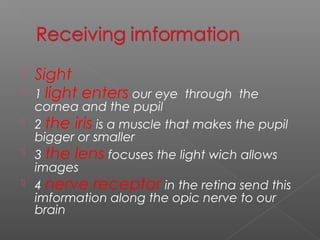
The document summarizes the five basic senses - sight, hearing, smell, taste, and touch. It describes how each sense works, from light entering the eye and sounds entering the ear, to smell receptors detecting chemicals and touch nerves sensing temperature. It also covers the central nervous system, brain parts and their functions, and common diseases including how they are transmitted and prevented.