Io
•
0 likes•1,494 views
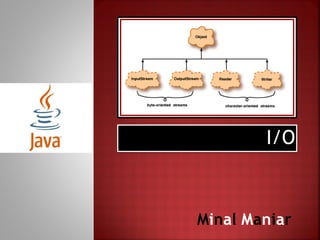
This document discusses I/O streams in Java, which allow reading and writing of data from sources and to destinations. It describes input and output streams, character and byte streams, and the Unicode standard for representing written languages internationally. Unicode was developed to solve the problems with different encodings for languages in various standards, and assigns a unique code value to each character. The document also mentions the File class, which contains methods for obtaining file properties and renaming/deleting files, and BufferedReader and BufferedWriter which improve I/O performance.
Report
Share
Report
Share
Download to read offline
Recommended
Unicode Fundamentals 

You will get all the basic informations about Unicode from this one slide InShaAllah (if Allah, the lord of the worlds wishes).
Internationalisation And Globalisation

This is a very old presentation but if you gloss over the usage of VB6 there is plenty of value. I presented this to the VBUG Annual Conference in 2003.
PDT DC015 Chapter 2 Computer System 2017/2018 (e)

Chapter 2 : 2.3 Information Coding Schemes 2017/2018
Faizah Ma'arof
Recommended
Unicode Fundamentals 

You will get all the basic informations about Unicode from this one slide InShaAllah (if Allah, the lord of the worlds wishes).
Internationalisation And Globalisation

This is a very old presentation but if you gloss over the usage of VB6 there is plenty of value. I presented this to the VBUG Annual Conference in 2003.
PDT DC015 Chapter 2 Computer System 2017/2018 (e)

Chapter 2 : 2.3 Information Coding Schemes 2017/2018
Faizah Ma'arof
The Good, the Bad, and the Ugly: What Happened to Unicode and PHP 6

n the halcyon days of early 2005, a project was launched to bring long overdue native Unicode and internationalization support to PHP. It was deemed so far reaching and important that PHP needed to have a version bump. After more than 4 years of development, the project (and PHP 6 for now) was shelved. This talk will introduce Unicode and i18n concepts, explain why Web needs Unicode, why PHP needs Unicode, how we tried to solve it (with examples), and what eventually happened. No sordid details will be left uncovered.
Towards a mnemonic classification of software languages

Slides of a lightning talk by Mikhail Barash at Fifth International Workshop on Open and Original Problems in Software Language Engineering (https://oopsle.github.io/2020/).
Lecture 4 system programming-data representation

This Lecture gives a brief overview and concept of Data Representation, a Part of System Programming, Number System, and ICT. it is for the BSCS Students, there may be Errors and mistakes, so therefore corrections and suggestions are warmly welcome..
Comment your Suggestions and corrections.
Understanding Names with Neural Networks - May 2020

Matching names across languages and writing systems is a critical issue in a variety of consumer and governmental domains. Historically, computers have attempted to solve this problem with ad-hoc methods such as edit distance, sound indexing, and Hidden Markov Models, but these have a variety of practical limitations in this problem space, which we will explore. To address these issues, we present our research and development team’s work on doing English/Japanese name matching using deep neural networks, which provides a substantial boost in accuracy.
KFIR BAR, PHILIP BLAIR, CARMEL ELIAV
Basis Technology
Type हिन्दी in Java

This tutorial is about how we can write in Hindi in java language.
After watching this, you can try this with other languages too, like Punjabi, Chinese etc
Type हिन्दी in Java

This tutorial is about how we can write in Hindi in java.
After reading this you can try this with other languages too.
More Related Content
What's hot
The Good, the Bad, and the Ugly: What Happened to Unicode and PHP 6

n the halcyon days of early 2005, a project was launched to bring long overdue native Unicode and internationalization support to PHP. It was deemed so far reaching and important that PHP needed to have a version bump. After more than 4 years of development, the project (and PHP 6 for now) was shelved. This talk will introduce Unicode and i18n concepts, explain why Web needs Unicode, why PHP needs Unicode, how we tried to solve it (with examples), and what eventually happened. No sordid details will be left uncovered.
Towards a mnemonic classification of software languages

Slides of a lightning talk by Mikhail Barash at Fifth International Workshop on Open and Original Problems in Software Language Engineering (https://oopsle.github.io/2020/).
Lecture 4 system programming-data representation

This Lecture gives a brief overview and concept of Data Representation, a Part of System Programming, Number System, and ICT. it is for the BSCS Students, there may be Errors and mistakes, so therefore corrections and suggestions are warmly welcome..
Comment your Suggestions and corrections.
Understanding Names with Neural Networks - May 2020

Matching names across languages and writing systems is a critical issue in a variety of consumer and governmental domains. Historically, computers have attempted to solve this problem with ad-hoc methods such as edit distance, sound indexing, and Hidden Markov Models, but these have a variety of practical limitations in this problem space, which we will explore. To address these issues, we present our research and development team’s work on doing English/Japanese name matching using deep neural networks, which provides a substantial boost in accuracy.
KFIR BAR, PHILIP BLAIR, CARMEL ELIAV
Basis Technology
What's hot (10)
The Good, the Bad, and the Ugly: What Happened to Unicode and PHP 6

The Good, the Bad, and the Ugly: What Happened to Unicode and PHP 6
Towards a mnemonic classification of software languages

Towards a mnemonic classification of software languages
Understanding Names with Neural Networks - May 2020

Understanding Names with Neural Networks - May 2020
Viewers also liked
Viewers also liked (9)
Similar to Io
Type हिन्दी in Java

This tutorial is about how we can write in Hindi in java language.
After watching this, you can try this with other languages too, like Punjabi, Chinese etc
Type हिन्दी in Java

This tutorial is about how we can write in Hindi in java.
After reading this you can try this with other languages too.
Data encryption and tokenization for international unicode

Unicode is an information technology standard for the consistent encoding, representation, and handling of text expressed in most of the world's writing systems. The standard is maintained by the Unicode Consortium, and as of March 2020, it has a total of 143,859 characters, with Unicode 13.0 (these characters consist of 143,696 graphic characters and 163 format characters) covering 154 modern and historic scripts, as well as multiple symbol sets and emoji. The character repertoire of the Unicode Standard is synchronized with ISO/IEC 10646, each being code-for-code identical with the other.
The Unicode Standard consists of a set of code charts for visual reference, an encoding method and set of standard character encodings, a set of reference data files, and a number of related items, such as character properties, rules for normalization, decomposition, collation, rendering, and bidirectional text display order (for the correct display of text containing both right-to-left scripts, such as Arabic and Hebrew, and left-to-right scripts). Unicode's success at unifying character sets has led to its widespread and predominant use in the internationalization and localization of computer software. The standard has been implemented in many recent technologies, including modern operating systems, XML, Java (and other programming languages), and the .NET Framework.
Unicode can be implemented by different character encodings. The Unicode standard defines Unicode Transformation Formats (UTF) UTF-8, UTF-16, and UTF-32, and several other encodings. The most commonly used encodings are UTF-8, UTF-16, and UCS-2 (a precursor of UTF-16 without full support for Unicode)
Encoding Nightmares (and how to avoid them)

Have you ever encountered problems displaying foreign characters on your app or website, or been confused by the appearance of strange question marks like this: ���? These are the result of character encoding mismatches. If you encounter these in the course of software localization, it can develop into an encoding nightmare!
Encoding nightmares can over-run product deadlines and spark frustration for your clients. If a website or app has an international future, a little knowledge up front can save you hours and even days of debugging.
Unicode 101

Learn the bare minimum to avoid corrupting Unicode text in your programs.
Many examples are given in the Python language.
Character encoding and unicode format

This presentation gives a deep understanding of character encoding format's and character set's.
Jun 29 new privacy technologies for unicode and international data standards ...

Protecting the increasing use International Unicode characters is required by a growing number of Privacy Laws in many countries and general Privacy Concerns with private data. Current approaches to protect International Unicode characters will increase the size and change the data formats. This will break many applications and slow down business operations. The current approach is also randomly returning data in new and unexpected languages. New approach with significantly higher performance and a memory footprint can be customizable and fit on small IoT devices.
We will discuss new approaches to achieve portability, security, performance, small memory footprint and language preservation for privacy protecting of Unicode data. These new approaches provide granular protection for all Unicode languages and customizable alphabets and byte length preserving protection of privacy protected characters.
Old Approaches
Major Issues
Protecting the increasing use International Unicode characters is required by a growing number of Privacy Laws in many countries and general Privacy Concerns with private data.
Old approaches to protect International Unicode characters will typically increase the size and change the data formats.
This will break many applications and slow down business operations. This is an example of an old approach that is also randomly returning data in new and unexpected languages
Software Internationalization Crash Course

Crash course in software internationalization and localization. Based on Java, but most of the information applicable for all web development.
What character is that

Character sets and collations are am important part of the database setup. In this presentation I show you the history of character sets and how they are used today, how UTF-8 works and how MySQL handles all this.
How To Build And Launch A Successful Globalized App From Day One Or All The ...

Significant compromises are often made taking a product to market that cause downstream pain—success can mean endless hours re-architecting and retrofitting to go global, get past 508 compliance at universities or integrate partners. The good news is there are freely available technologies and strategies to avoid the pain. Learn from Zimbra’s experiences with ZCS and Zimbra Desktop (an offline-capable AJAX email application) including a checklist of do’s and don’ts and a deep dive into: i18n and l10n, 508 compliance (Americans with Disabilities Act), skinning, templates, time-date formatting and more.
From http://en.oreilly.com/oscon2008/public/schedule/detail/4834
Similar to Io (20)
Data encryption and tokenization for international unicode

Data encryption and tokenization for international unicode
Jun 29 new privacy technologies for unicode and international data standards ...

Jun 29 new privacy technologies for unicode and international data standards ...
How To Build And Launch A Successful Globalized App From Day One Or All The ...

How To Build And Launch A Successful Globalized App From Day One Or All The ...
More from Minal Maniar
More from Minal Maniar (6)
Recently uploaded
Standard Reomte Control Interface - Neometrix

About
Indigenized remote control interface card suitable for MAFI system CCR equipment. Compatible for IDM8000 CCR. Backplane mounted serial and TCP/Ethernet communication module for CCR remote access. IDM 8000 CCR remote control on serial and TCP protocol.
• Remote control: Parallel or serial interface.
• Compatible with MAFI CCR system.
• Compatible with IDM8000 CCR.
• Compatible with Backplane mount serial communication.
• Compatible with commercial and Defence aviation CCR system.
• Remote control system for accessing CCR and allied system over serial or TCP.
• Indigenized local Support/presence in India.
• Easy in configuration using DIP switches.
Technical Specifications
Indigenized remote control interface card suitable for MAFI system CCR equipment. Compatible for IDM8000 CCR. Backplane mounted serial and TCP/Ethernet communication module for CCR remote access. IDM 8000 CCR remote control on serial and TCP protocol.
Key Features
Indigenized remote control interface card suitable for MAFI system CCR equipment. Compatible for IDM8000 CCR. Backplane mounted serial and TCP/Ethernet communication module for CCR remote access. IDM 8000 CCR remote control on serial and TCP protocol.
• Remote control: Parallel or serial interface
• Compatible with MAFI CCR system
• Copatiable with IDM8000 CCR
• Compatible with Backplane mount serial communication.
• Compatible with commercial and Defence aviation CCR system.
• Remote control system for accessing CCR and allied system over serial or TCP.
• Indigenized local Support/presence in India.
Application
• Remote control: Parallel or serial interface.
• Compatible with MAFI CCR system.
• Compatible with IDM8000 CCR.
• Compatible with Backplane mount serial communication.
• Compatible with commercial and Defence aviation CCR system.
• Remote control system for accessing CCR and allied system over serial or TCP.
• Indigenized local Support/presence in India.
• Easy in configuration using DIP switches.
AKS UNIVERSITY Satna Final Year Project By OM Hardaha.pdf

AKS UNIVERSITY Satna Final Year Project By OM Hardaha.
Thank me later.
samsarthak31@gmail.com
Industrial Training at Shahjalal Fertilizer Company Limited (SFCL)

This presentation is about the working procedure of Shahjalal Fertilizer Company Limited (SFCL). A Govt. owned Company of Bangladesh Chemical Industries Corporation under Ministry of Industries.
Immunizing Image Classifiers Against Localized Adversary Attacks

This paper addresses the vulnerability of deep learning models, particularly convolutional neural networks
(CNN)s, to adversarial attacks and presents a proactive training technique designed to counter them. We
introduce a novel volumization algorithm, which transforms 2D images into 3D volumetric representations.
When combined with 3D convolution and deep curriculum learning optimization (CLO), itsignificantly improves
the immunity of models against localized universal attacks by up to 40%. We evaluate our proposed approach
using contemporary CNN architectures and the modified Canadian Institute for Advanced Research (CIFAR-10
and CIFAR-100) and ImageNet Large Scale Visual Recognition Challenge (ILSVRC12) datasets, showcasing
accuracy improvements over previous techniques. The results indicate that the combination of the volumetric
input and curriculum learning holds significant promise for mitigating adversarial attacks without necessitating
adversary training.
Sachpazis:Terzaghi Bearing Capacity Estimation in simple terms with Calculati...

Terzaghi's soil bearing capacity theory, developed by Karl Terzaghi, is a fundamental principle in geotechnical engineering used to determine the bearing capacity of shallow foundations. This theory provides a method to calculate the ultimate bearing capacity of soil, which is the maximum load per unit area that the soil can support without undergoing shear failure. The Calculation HTML Code included.
在线办理(ANU毕业证书)澳洲国立大学毕业证录取通知书一模一样

学校原件一模一样【微信:741003700 】《(ANU毕业证书)澳洲国立大学毕业证》【微信:741003700 】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
【主营项目】
一.毕业证【q微741003700】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【q/微741003700】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
HYDROPOWER - Hydroelectric power generation

Overview of the fundamental roles in Hydropower generation and the components involved in wider Electrical Engineering.
This paper presents the design and construction of hydroelectric dams from the hydrologist’s survey of the valley before construction, all aspects and involved disciplines, fluid dynamics, structural engineering, generation and mains frequency regulation to the very transmission of power through the network in the United Kingdom.
Author: Robbie Edward Sayers
Collaborators and co editors: Charlie Sims and Connor Healey.
(C) 2024 Robbie E. Sayers
WATER CRISIS and its solutions-pptx 1234

Water scarcity is the lack of fresh water resources to meet the standard water demand. There are two type of water scarcity. One is physical. The other is economic water scarcity.
Architectural Portfolio Sean Lockwood

This portfolio contains selected projects I completed during my undergraduate studies. 2018 - 2023
The Benefits and Techniques of Trenchless Pipe Repair.pdf

Explore the innovative world of trenchless pipe repair with our comprehensive guide, "The Benefits and Techniques of Trenchless Pipe Repair." This document delves into the modern methods of repairing underground pipes without the need for extensive excavation, highlighting the numerous advantages and the latest techniques used in the industry.
Learn about the cost savings, reduced environmental impact, and minimal disruption associated with trenchless technology. Discover detailed explanations of popular techniques such as pipe bursting, cured-in-place pipe (CIPP) lining, and directional drilling. Understand how these methods can be applied to various types of infrastructure, from residential plumbing to large-scale municipal systems.
Ideal for homeowners, contractors, engineers, and anyone interested in modern plumbing solutions, this guide provides valuable insights into why trenchless pipe repair is becoming the preferred choice for pipe rehabilitation. Stay informed about the latest advancements and best practices in the field.
Final project report on grocery store management system..pdf

In today’s fast-changing business environment, it’s extremely important to be able to respond to client needs in the most effective and timely manner. If your customers wish to see your business online and have instant access to your products or services.
Online Grocery Store is an e-commerce website, which retails various grocery products. This project allows viewing various products available enables registered users to purchase desired products instantly using Paytm, UPI payment processor (Instant Pay) and also can place order by using Cash on Delivery (Pay Later) option. This project provides an easy access to Administrators and Managers to view orders placed using Pay Later and Instant Pay options.
In order to develop an e-commerce website, a number of Technologies must be studied and understood. These include multi-tiered architecture, server and client-side scripting techniques, implementation technologies, programming language (such as PHP, HTML, CSS, JavaScript) and MySQL relational databases. This is a project with the objective to develop a basic website where a consumer is provided with a shopping cart website and also to know about the technologies used to develop such a website.
This document will discuss each of the underlying technologies to create and implement an e- commerce website.
Recently uploaded (20)
AKS UNIVERSITY Satna Final Year Project By OM Hardaha.pdf

AKS UNIVERSITY Satna Final Year Project By OM Hardaha.pdf
Industrial Training at Shahjalal Fertilizer Company Limited (SFCL)

Industrial Training at Shahjalal Fertilizer Company Limited (SFCL)
Planning Of Procurement o different goods and services

Planning Of Procurement o different goods and services
Immunizing Image Classifiers Against Localized Adversary Attacks

Immunizing Image Classifiers Against Localized Adversary Attacks
Sachpazis:Terzaghi Bearing Capacity Estimation in simple terms with Calculati...

Sachpazis:Terzaghi Bearing Capacity Estimation in simple terms with Calculati...
block diagram and signal flow graph representation

block diagram and signal flow graph representation
The Benefits and Techniques of Trenchless Pipe Repair.pdf

The Benefits and Techniques of Trenchless Pipe Repair.pdf
Final project report on grocery store management system..pdf

Final project report on grocery store management system..pdf
MCQ Soil mechanics questions (Soil shear strength).pdf

MCQ Soil mechanics questions (Soil shear strength).pdf
Io
- 2. Automatically I/O package Stream: A sequence of data. Input Stream: reads data from source. Output Stream: writes data to destination.
- 3. Automatically I/O methods Character Streams Byte Streams
- 5. Automatically Unicode is a universal international standard character encoding that is capable of representing most of the world's written languages. Before Unicode, there were many language standards: ASCII (American Standard Code for Information Interchange) for the United States. ISO 8859-1 for Western European Language. KOI-8 for Russian. GB18030 and BIG-5 for Chinese.
- 6. Automatically Problem A particular code value corresponds to different letters in the various language standards. The encodings for languages with large character sets have variable length. Some common characters are encoded as single bytes, other require two or more byte. Solution To solve these problems, a new language standard was developed i.e. Unicode System. In unicode, character holds 2 byte, so java also uses 2 byte for characters. lowest value:u0000 highest value:uFFFF
- 9. Automatically The File class contains the methods for obtaining the properties of a file/directory and for renaming and deleting a file/directory. The File class is intended to provide an abstraction that deals with most of the machine dependent complexities of files and path names in a machine-independent fashion. The File class contains the methods for obtaining file and directory properties and for renaming and deleting files and directories
- 10. Automatically
- 11. Automatically BufferedReader & BufferedWriter
- 12. Automatically Introduction to Java Programming, Comprehensive Version (10th Edition), Y. Daniel Liang Java The Complete Reference (9th Edition), Herbert Schildt
