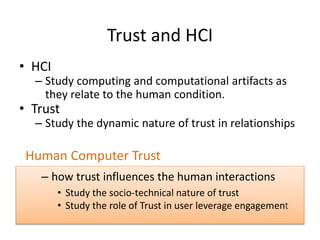
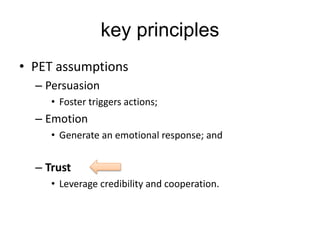
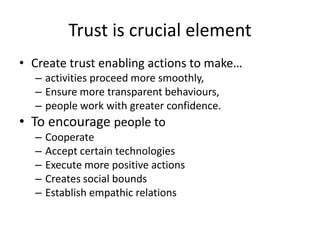
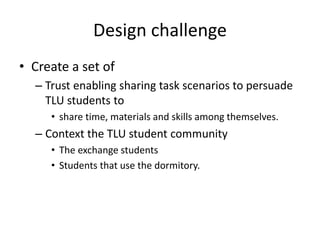
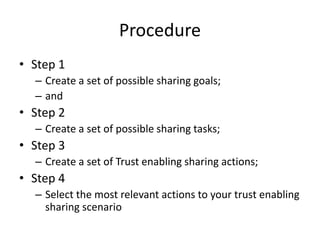
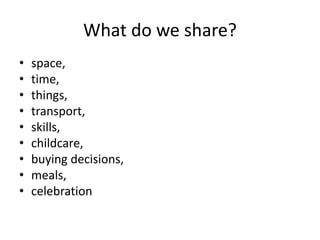
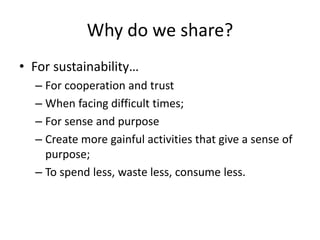
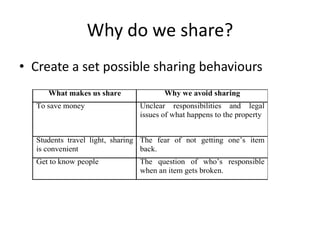
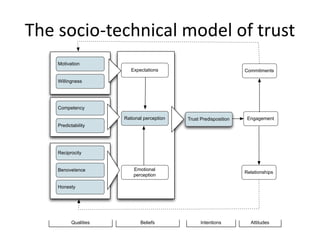
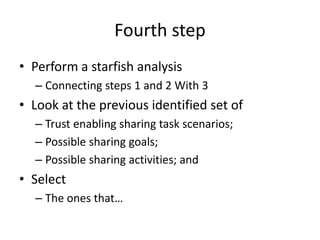
The document discusses the importance of trust in human-computer interaction (HCI) and emphasizes the need for design methodologies that incorporate persuasion, emotion, and trust to enhance user engagement. It highlights the socio-technical nature of trust, the dynamic factors that influence it, and how trust enables smoother interactions and cooperation in sharing practices. Additionally, it outlines a design challenge aimed at creating trust-enabling scenarios for students to encourage sharing of resources and skills within a community.








![Resources
• Sousa et al. (2014). A design space for trust
enabling interaction design. In Proceedings of the
International Conference on Multimedia,
Interaction, Design and Innovation MIDI 2014.
ACM.
• Sousa et al. (2015). Value creation through trust
in technologically-mediated social participation.
Technology, Innovation and Education, 1 - 9.
[forthcoming]
• https://humancomputertrust.wordpress.com](https://image.slidesharecdn.com/trust-introduction-150330012852-conversion-gate01/85/Trust-from-a-Human-Computer-Interaction-perspective-44-320.jpg)