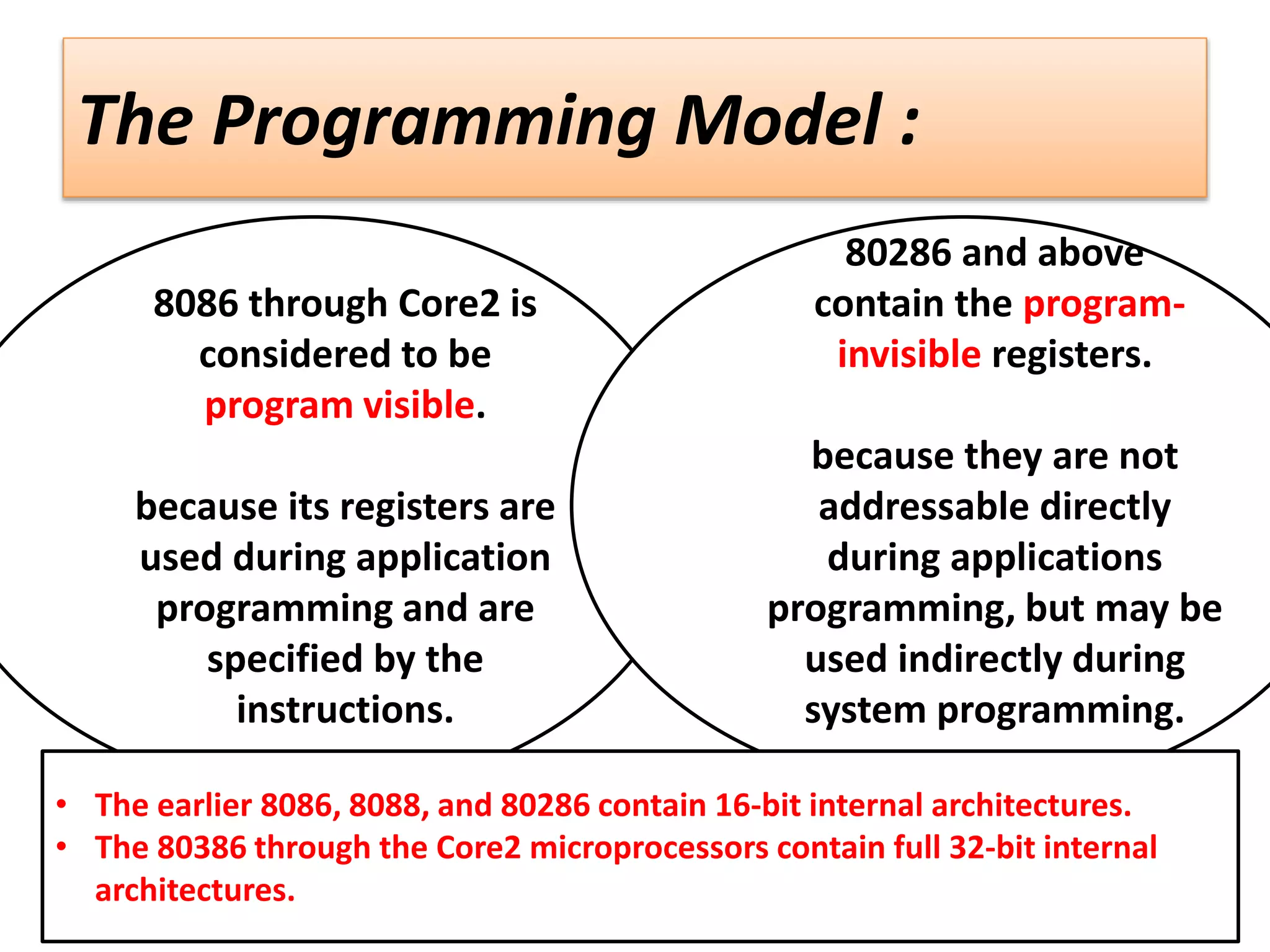
The document describes various aspects of memory addressing in Intel microprocessors from 8086 to Core2. It discusses register types, including general purpose, segment, special purpose and flag registers. It details real mode, protected mode and flat 64-bit memory addressing techniques. Real mode uses segment and offset registers to access the first 1MB of memory. Protected mode allows access above 1MB using segment selectors and 32-bit offsets. The 64-bit flat mode uses a single 64-bit address space.