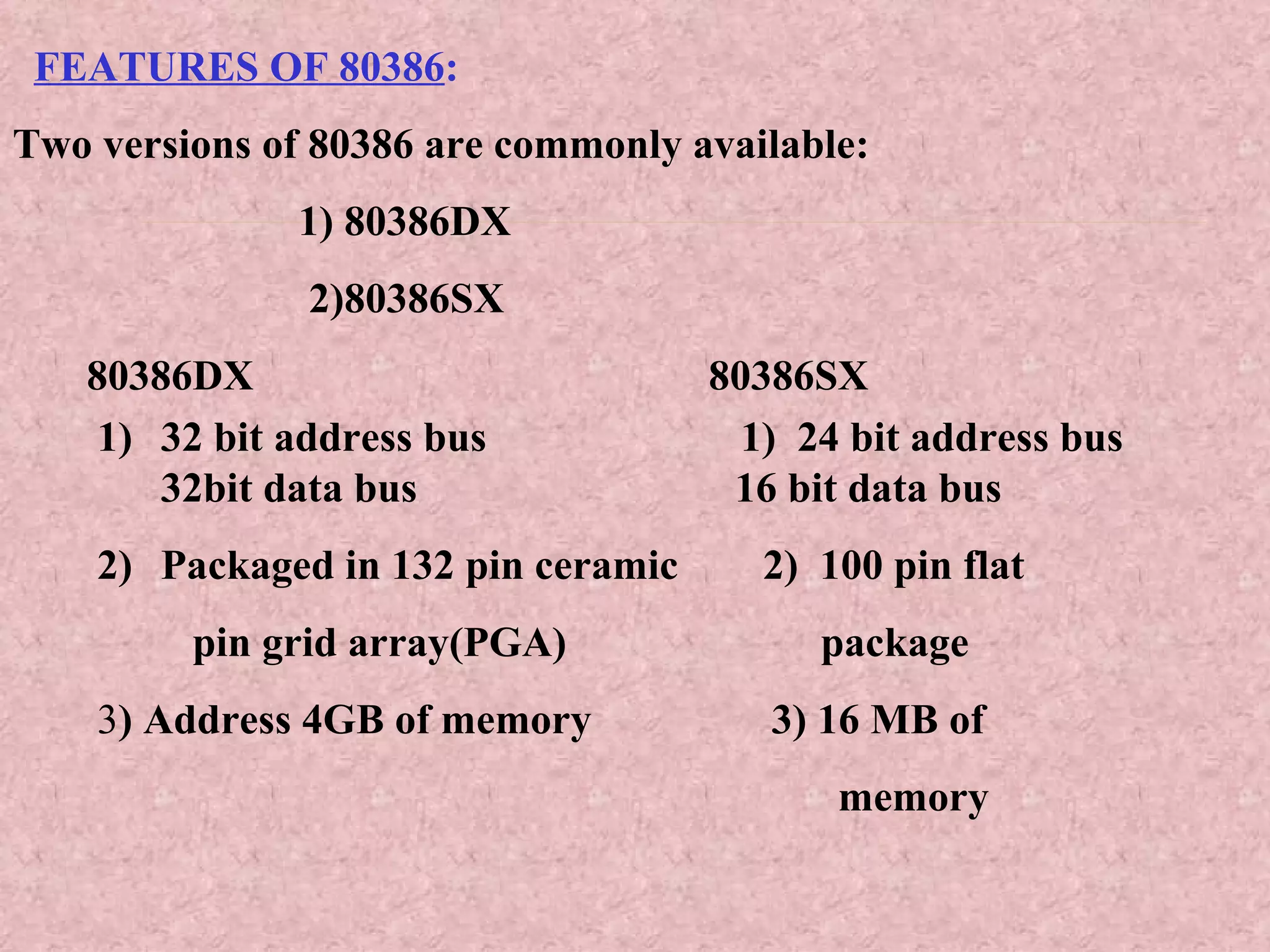
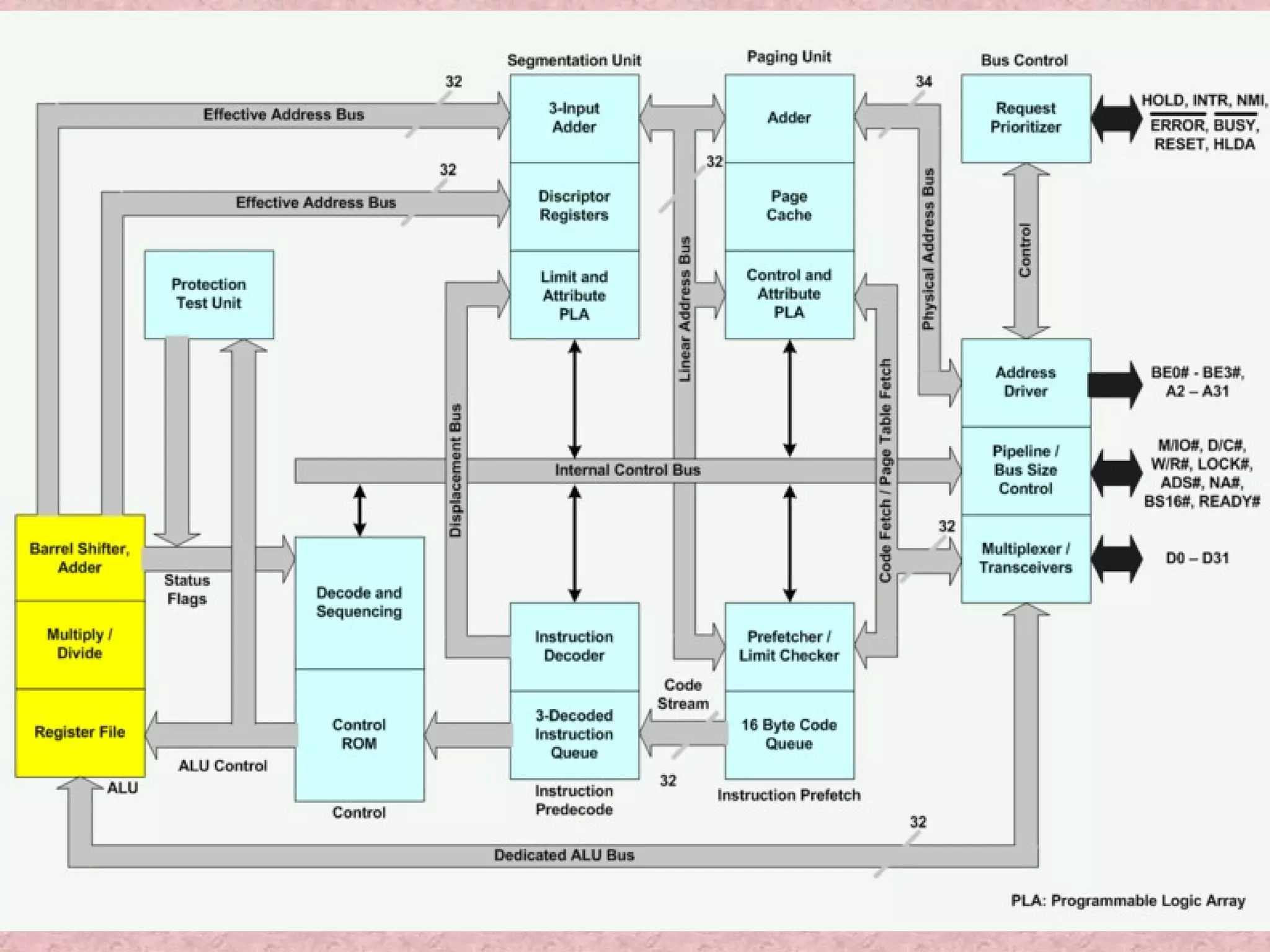
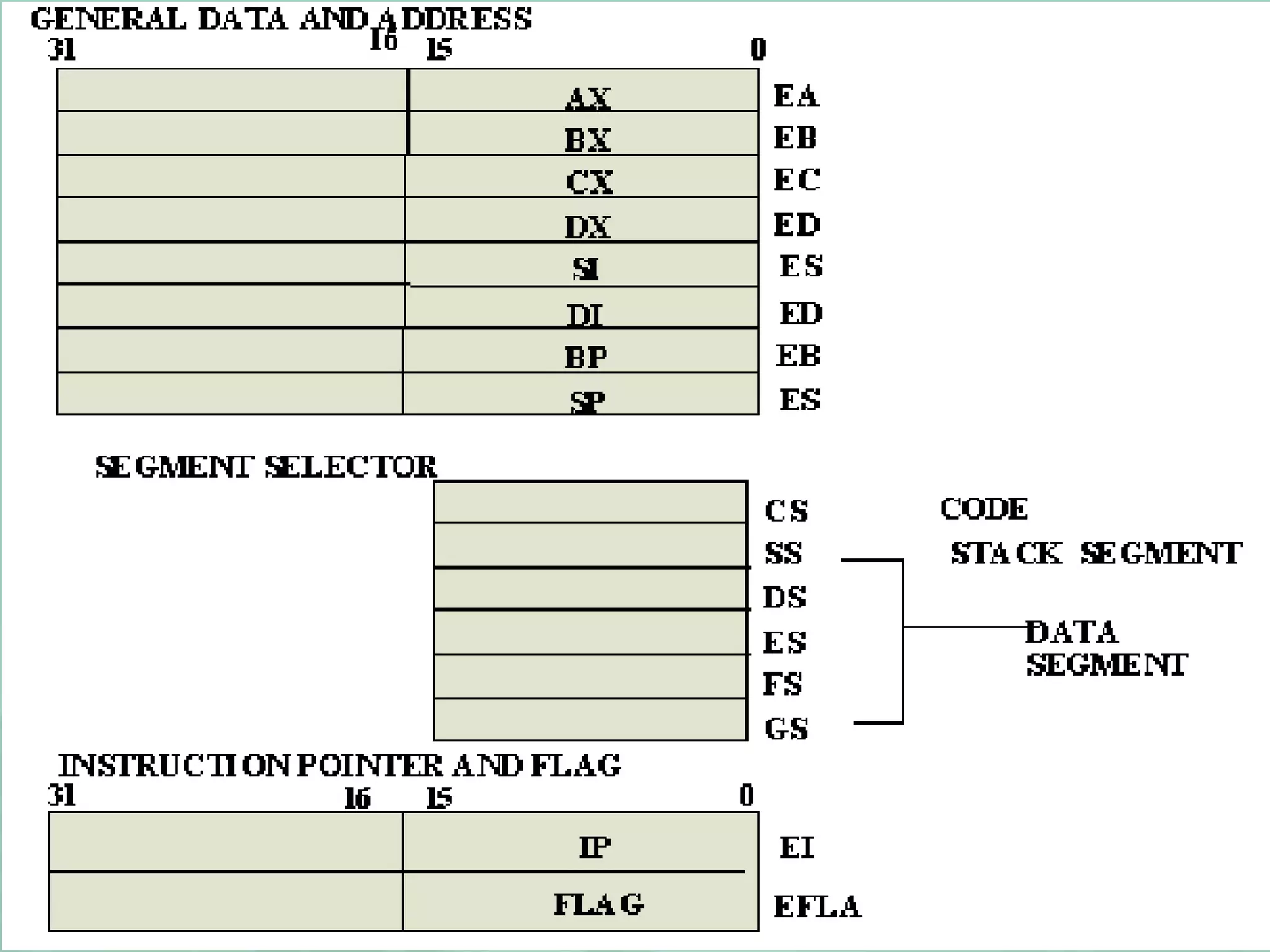
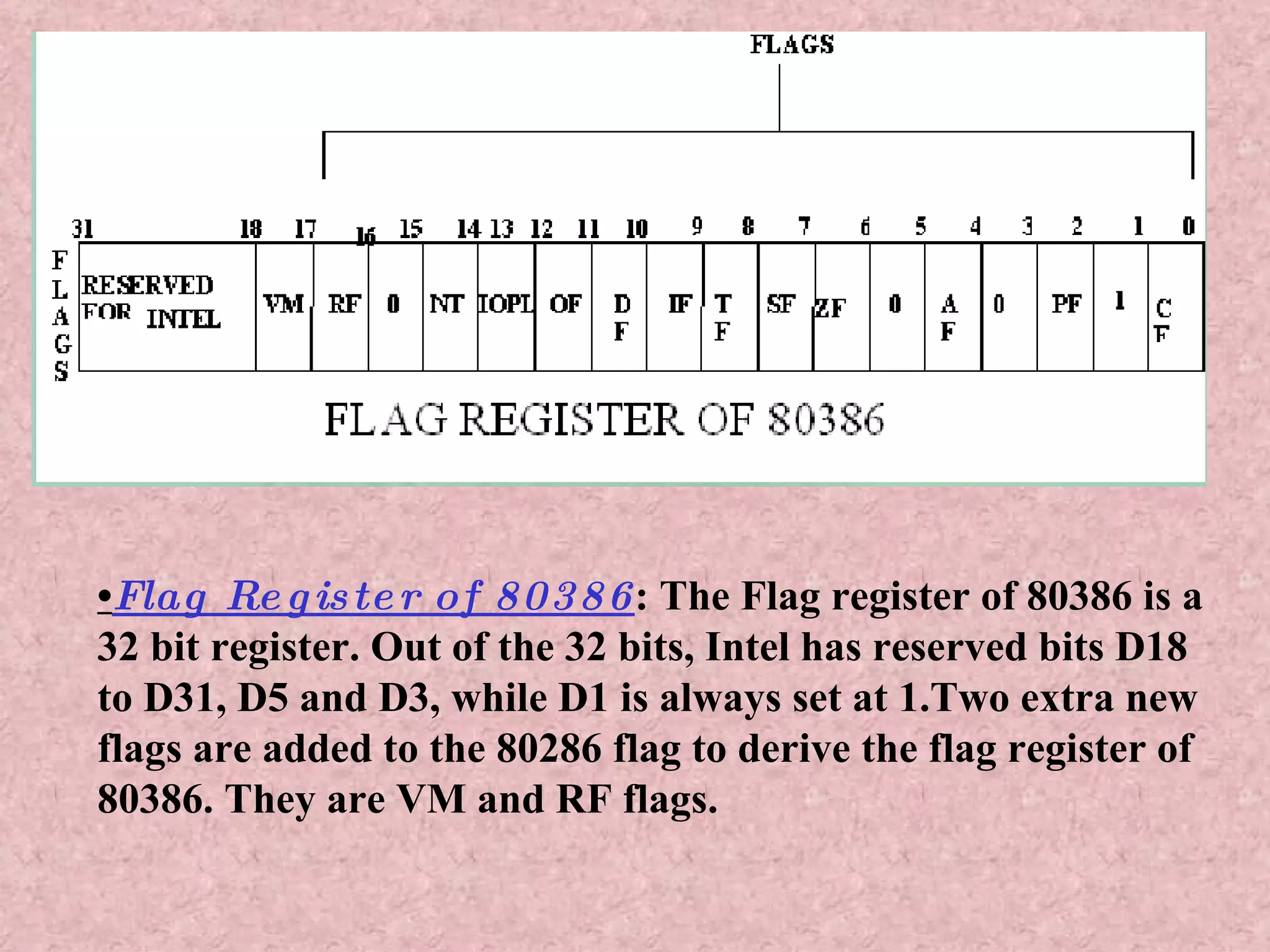
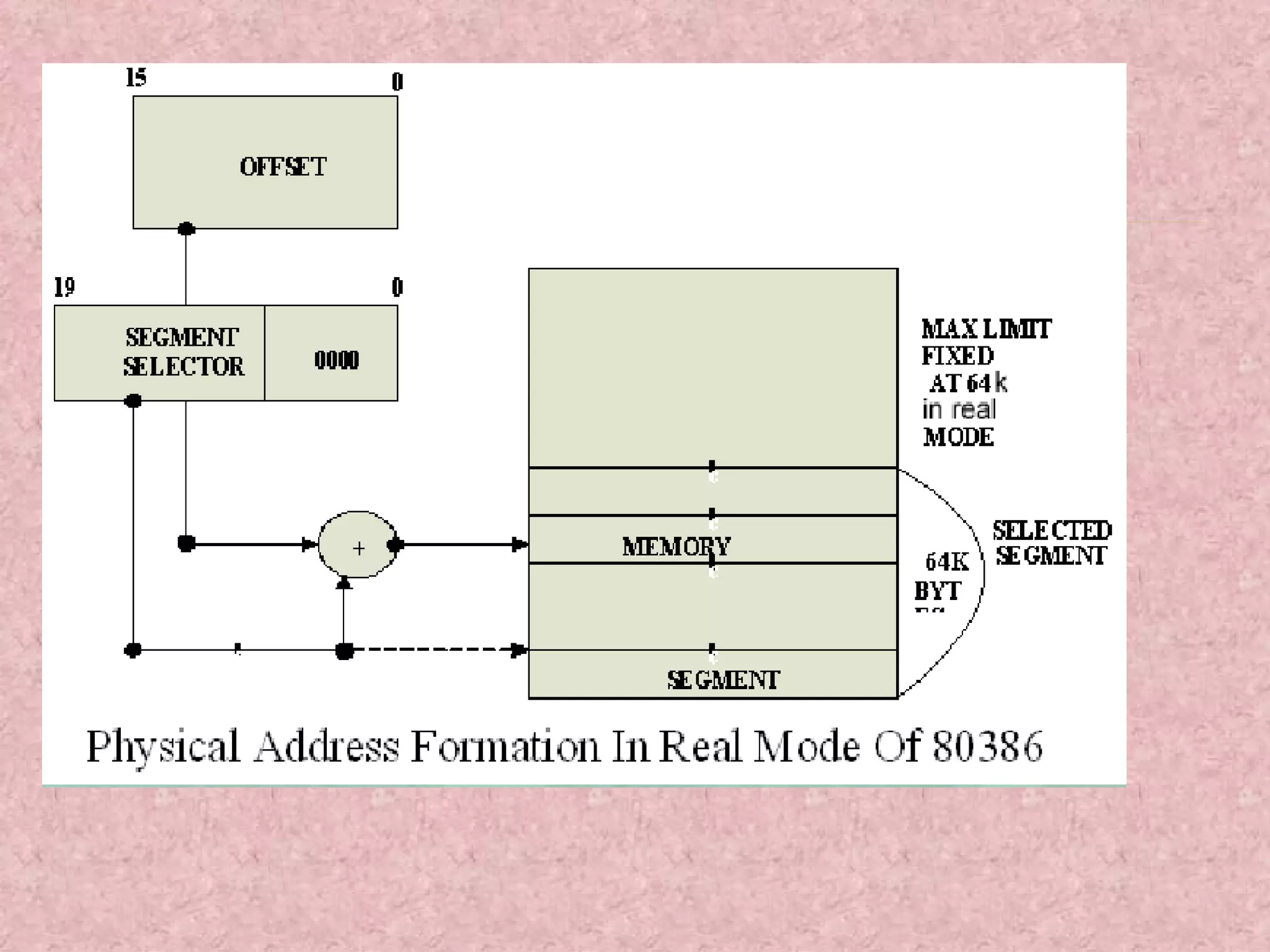
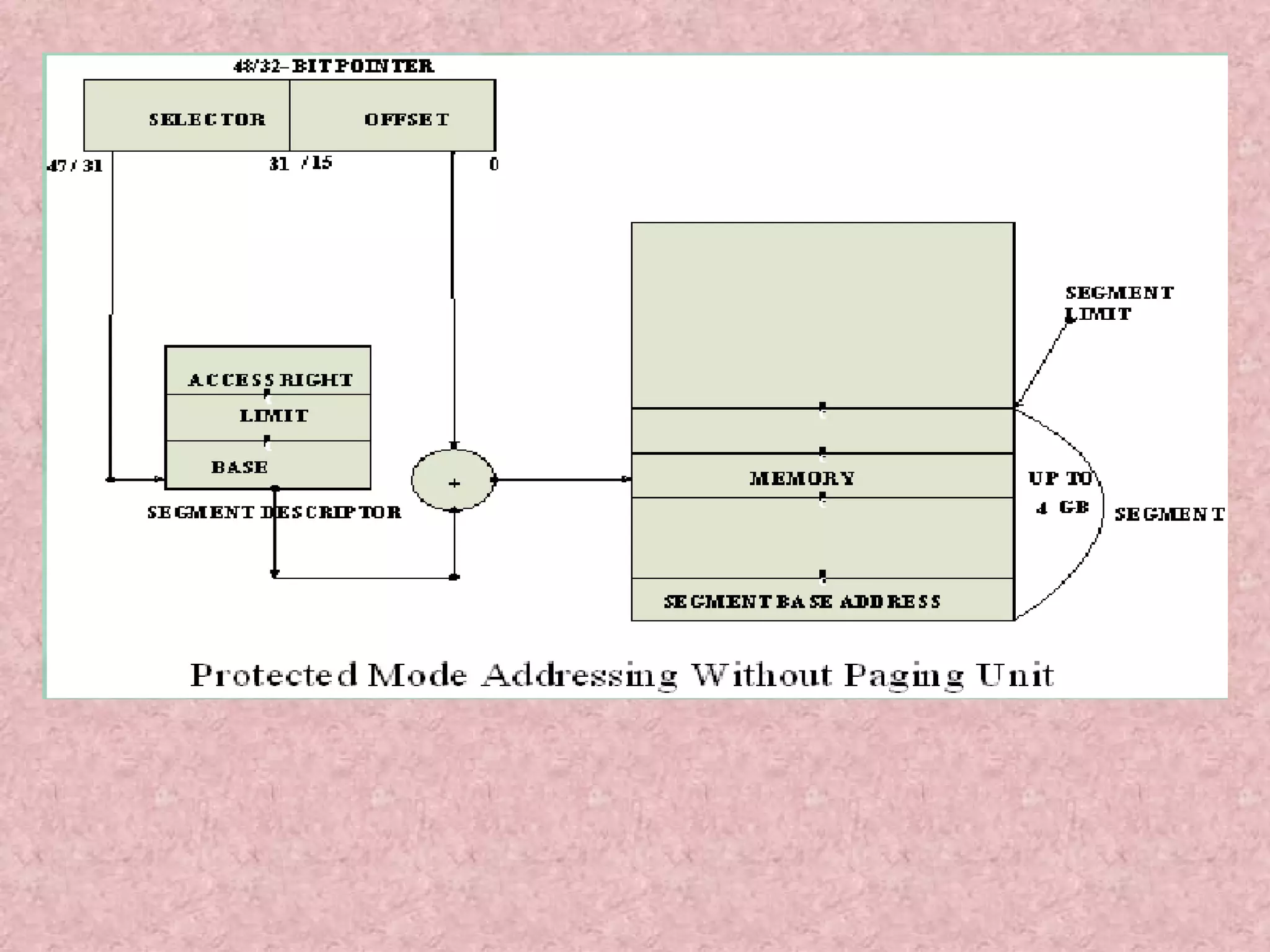
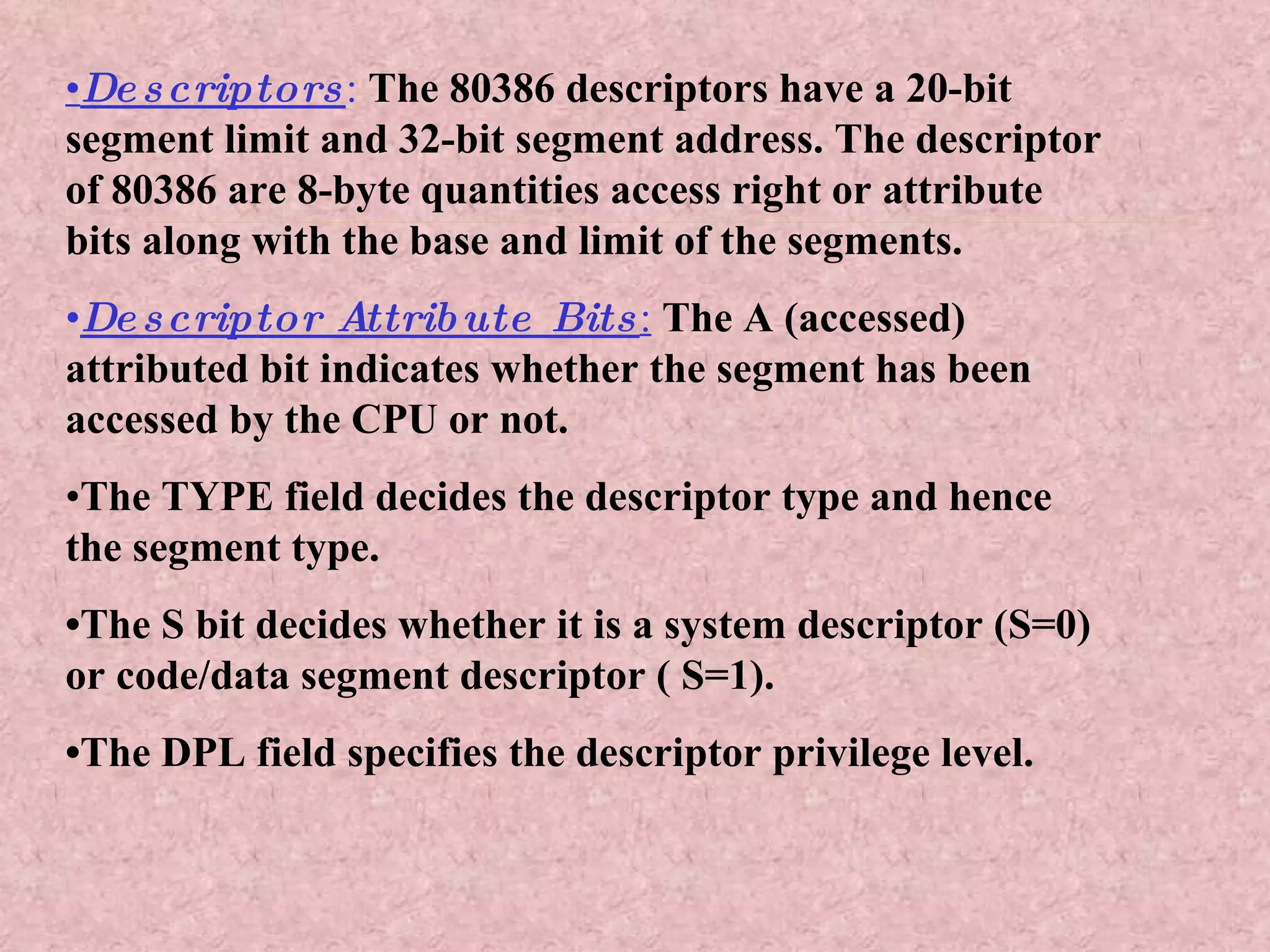
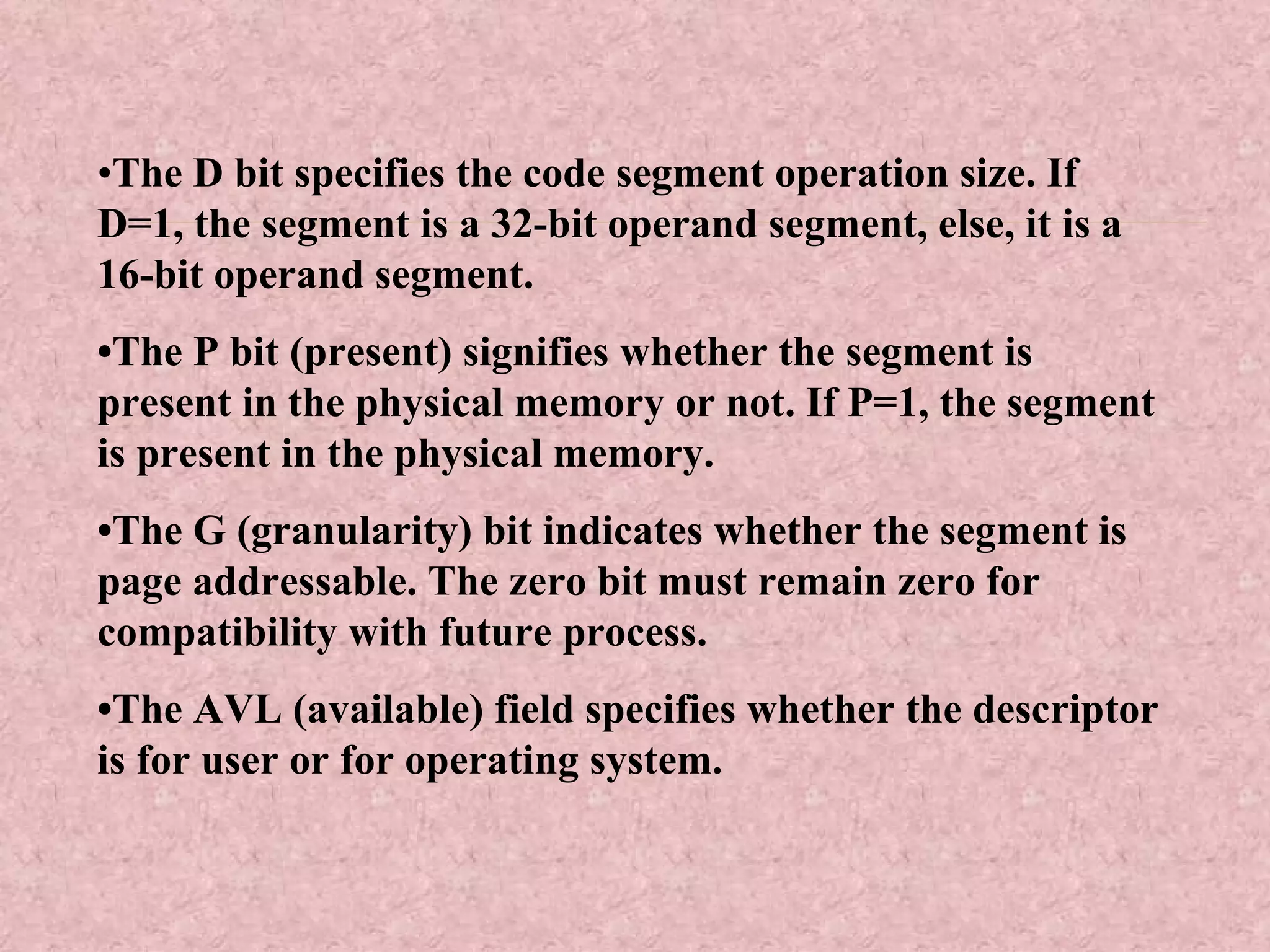
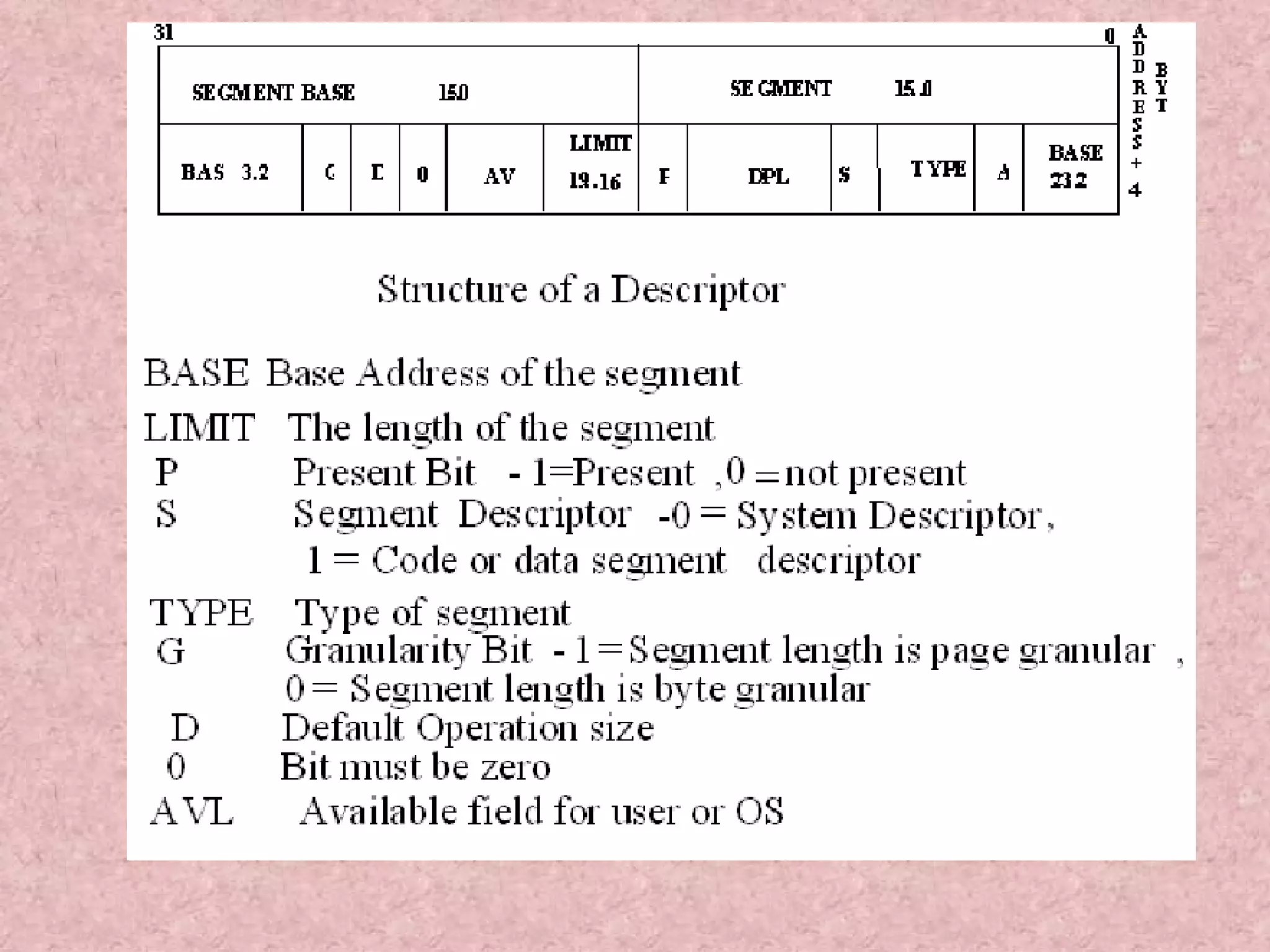
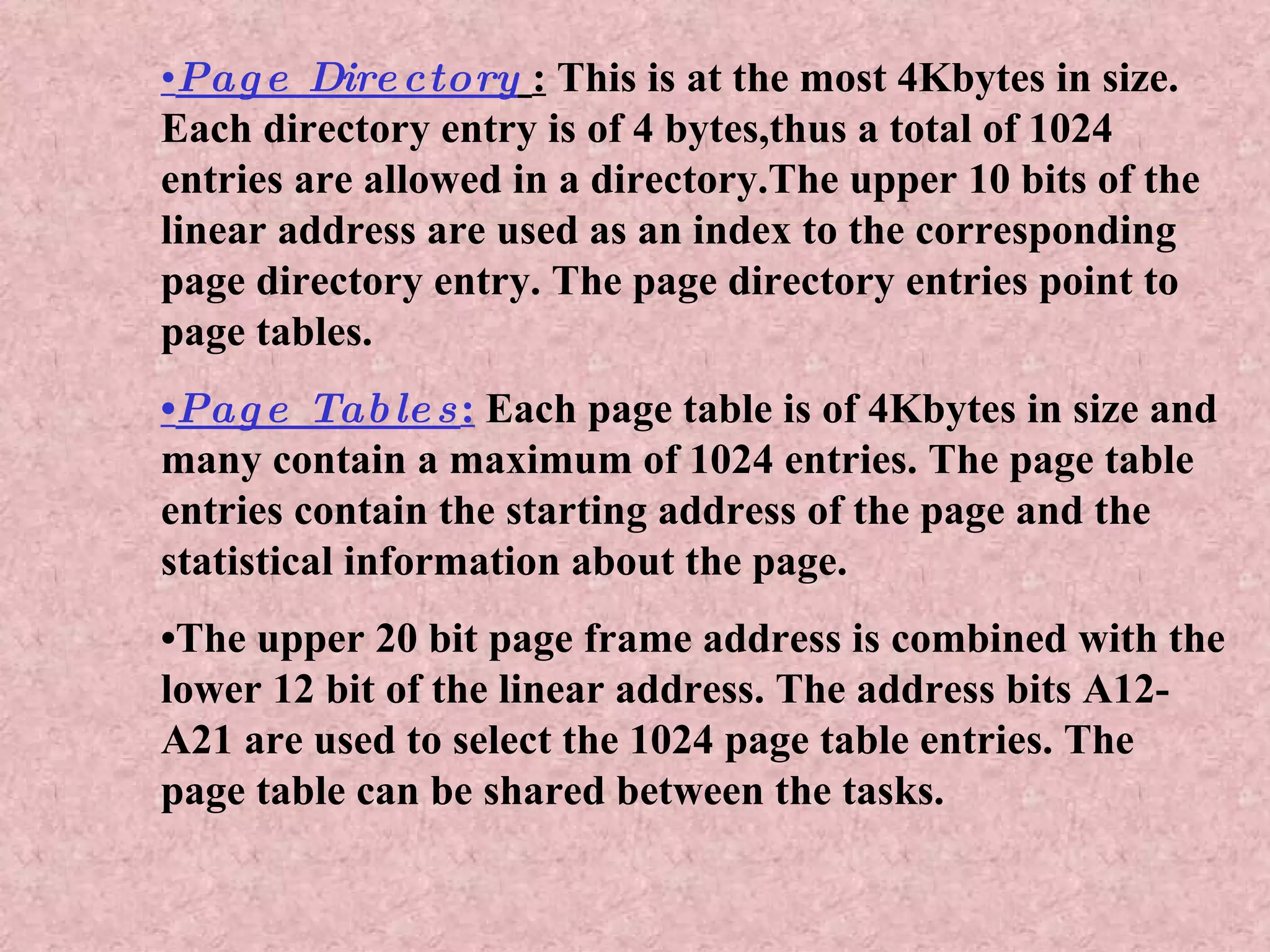
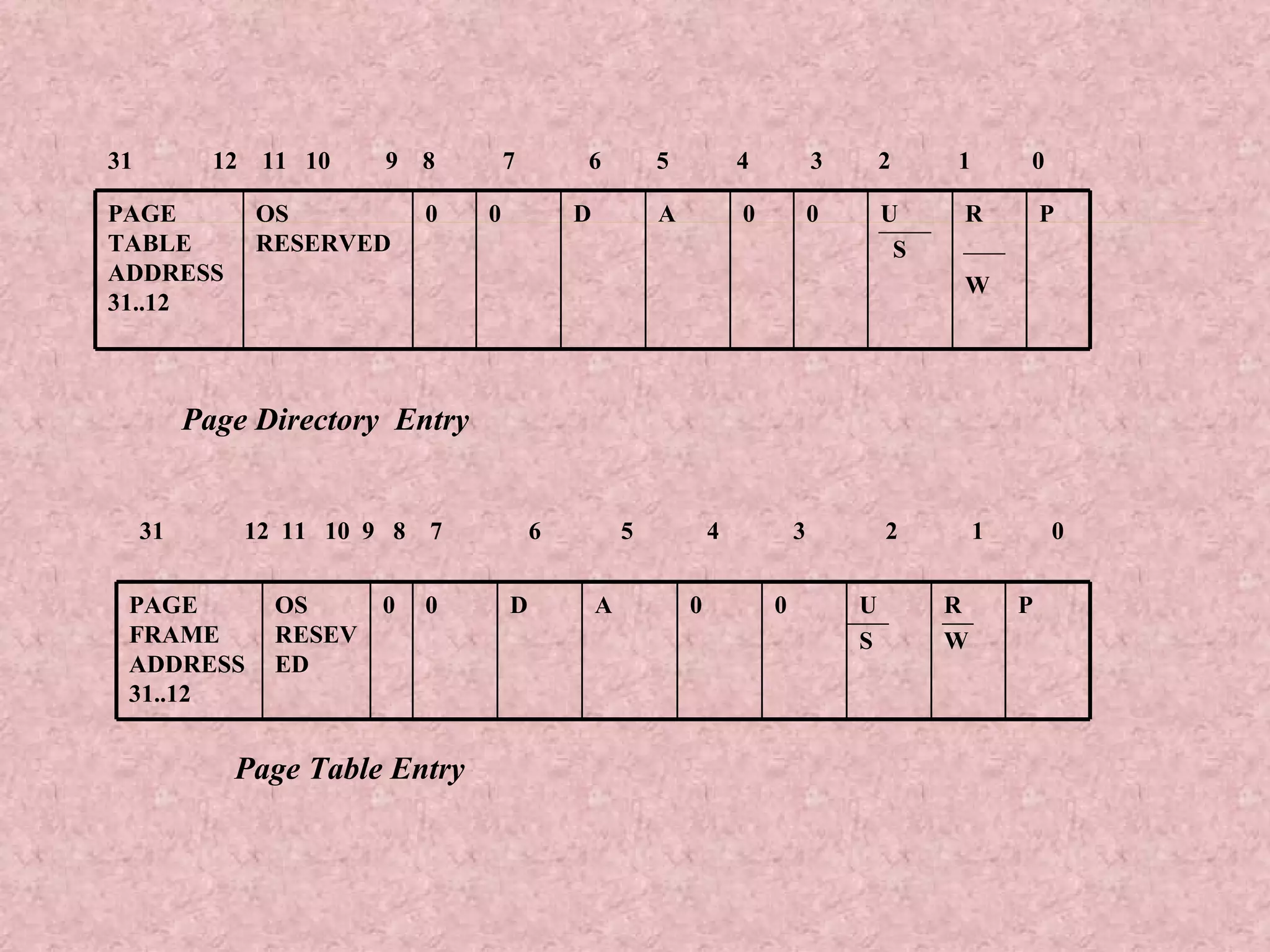
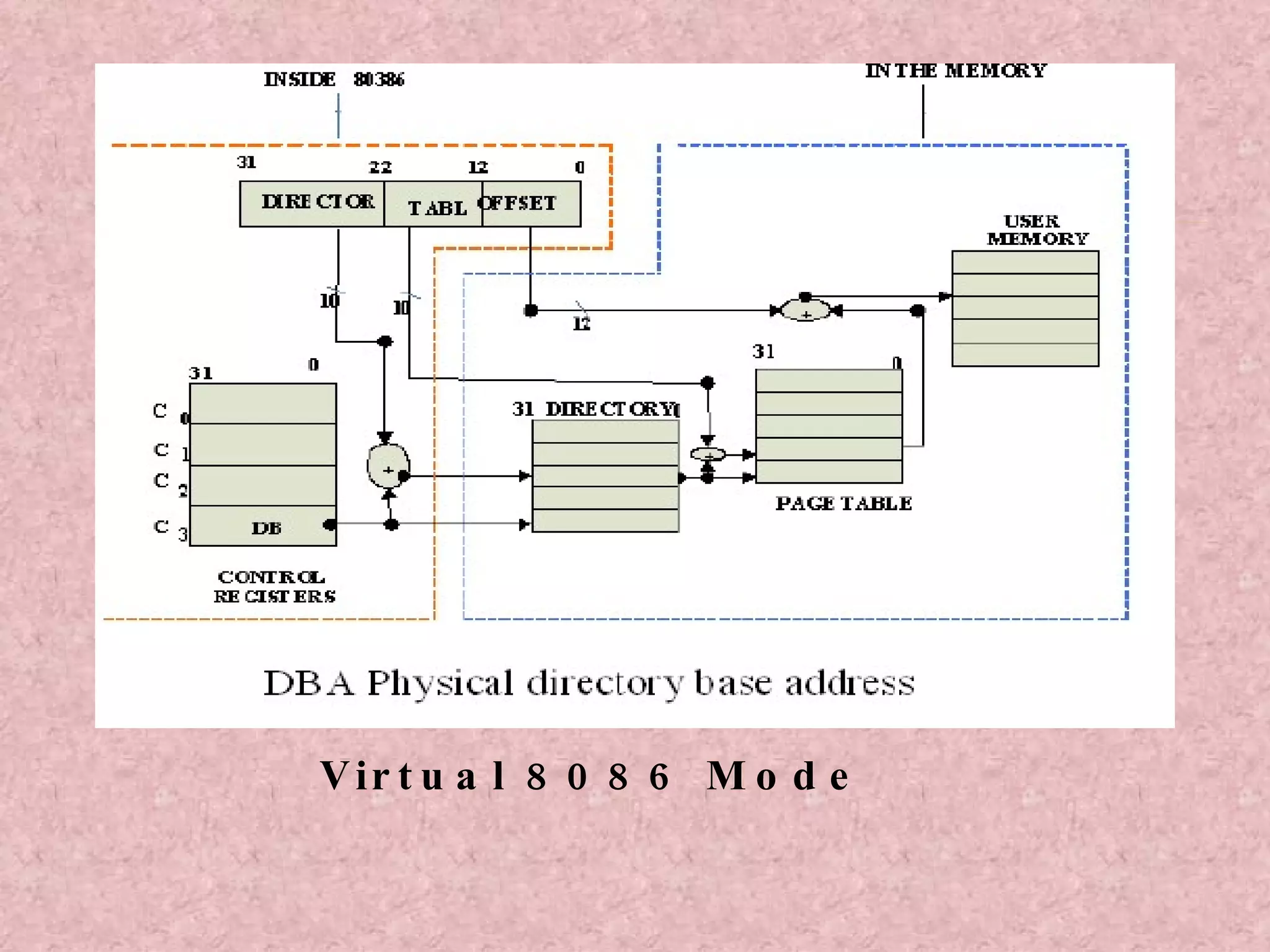
The document summarizes key features of the Intel 80386 microprocessor. It discusses the two main versions - 80386DX and 80386SX, their address buses, data buses, and packaging. It then covers the internal architecture including the central processing unit, memory management unit, and bus interface unit. Finally, it discusses addressing modes and memory management in real and protected modes.